What is External Penetration Testing?
Let's dive into the heart of the matter: What is External Penetration Testing? In the simplest terms, external penetration testing is a cybersecurity testing technique that simulates a real-world attack on a company's network. This simulation is conducted from outside the organization's network infrastructure to identify potential vulnerabilities and weaknesses.
Imagine your network as a fortress. The external penetration testing is like a friendly knight who checks the fortress's defenses. The knight tries to breach the walls, not to conquer, but to find any weak spots that enemies might exploit. In the digital world, these 'enemies' are cybercriminals who are always on the lookout for any chink in your armor.

External penetration testing is a crucial part of cybersecurity best practices. It involves a series of penetration testing steps designed to assess the security of your digital networks. These steps include reconnaissance, scanning, gaining access, maintaining access, and covering tracks.
By simulating attacks, this form of network security testing helps organizations understand their security posture from an attacker's perspective. It's a proactive measure that allows you to fix vulnerabilities before they can be exploited, thereby securing your digital networks and reinforcing your defenses in the digital world.
Remember, in the realm of cybersecurity, knowledge is power. The more you know about your vulnerabilities, the better prepared you are to defend against cyber threats. That's why it's important to continuously conduct penetration testing and why security testing is so important.
The Importance of External Penetration Testing
Stepping into the spotlight, let's delve into The Importance of External Penetration Testing. In the grand scheme of cybersecurity, external penetration testing serves as a critical line of defense. It's like a health check-up for your network, a necessary measure to ensure the well-being of your digital fortress.
Imagine a world where cyber threats are invisible predators lurking in the shadows of the digital world. In such a scenario, external penetration testing is your ever-vigilant sentinel, tirelessly scanning the horizon for potential threats. It's not just about finding vulnerabilities; it's about understanding them, learning how they can be exploited, and most importantly, figuring out how to fix them.

External penetration testing is a proactive approach to cybersecurity. It's not waiting for an attack to happen, but rather anticipating it. This is the essence of cybersecurity best practices. It's about being one step ahead, always. It's about turning the tables on cybercriminals, using their own tactics against them to strengthen your defenses.
Why is network security testing important, you ask? It's simple. In a world where digital threats are constantly evolving, staying static is not an option. You need to evolve too, adapt, and improve. That's where external penetration testing comes in. It's a continuous process, a cycle of testing, learning, and improving.
So, why is it important to continuously conduct penetration testing? Because in the ever-changing landscape of the digital world, what worked yesterday might not work today. New vulnerabilities can appear overnight, and old ones can evolve. Regular testing ensures that you're always on top of your game, ready to face whatever the digital world throws at you.
Remember, in cybersecurity, complacency is the enemy. External penetration testing keeps you alert, vigilant, and prepared. It's not just a testing technique; it's a mindset, a commitment to securing your digital networks and safeguarding your digital world.
Steps Involved in External Penetration Testing
Now that we've established the importance of external penetration testing, let's delve into the Steps Involved in External Penetration Testing. This process is a meticulous journey through your network's defenses, a deep dive into the hidden recesses of your digital fortress. It's a journey that requires precision, expertise, and a keen understanding of cybersecurity testing techniques.
Firstly, we begin with Planning and Reconnaissance. This is the stage where we define the scope and goals of the test. We gather intelligence about the target system - its network, IP addresses, domain names, mail servers, and more. This step sets the stage for the rest of the process. 
Next, we move to Scanning. Here, we use automated tools to understand how the target application will respond to different intrusion attempts. This helps us identify potential vulnerabilities. 
Then comes the Gaining Access phase. This is where the real action begins. We simulate cyber-attacks to exploit the identified vulnerabilities, aiming to understand the extent of potential damage. 
Once we've gained access, we move to Maintaining Access. Here, we try to remain inside the system for as long as possible, mimicking the actions of potential attackers. This helps us understand how well the system can withstand persistent threats. 
Finally, we arrive at the Analysis stage. Here, we compile a comprehensive report detailing our findings - the vulnerabilities discovered, data breaches, and the time we remained in the system. This report serves as a roadmap for improving network security. 
External penetration testing is a crucial component of cybersecurity best practices. It's a journey that takes us through the heart of a network, revealing its strengths and weaknesses. It's a journey that helps us secure our digital world, one step at a time.
Understanding External Penetration Testing
Let's dive into the fascinating world of External Penetration Testing. In the simplest terms, it's a cybersecurity best practice that involves simulating cyber attacks on your network from the outside. This method is a crucial part of network security testing, designed to expose any weaknesses before they can be exploited by malicious hackers.

Think of external penetration testing as a health check-up for your digital security measures. Just as you'd visit a doctor to identify any potential health issues, you conduct penetration testing to find vulnerabilities in your network. This proactive approach is a vital part of securing digital networks, ensuring that your defenses are robust and ready to fend off any cyber threats.
External penetration testing follows a systematic process. It starts with the identification of the target system, followed by a thorough analysis of potential entry points. The next step involves attempting to breach the system using various cybersecurity testing techniques. The final stage is to document the findings and make recommendations for improvements.

So, why is it important to continuously conduct penetration testing? The digital world is ever-evolving, with new threats emerging every day. Regular testing ensures that your network security measures are up-to-date and capable of combating the latest cyber threats. Remember, in the realm of cybersecurity, complacency can be costly.
External Penetration Testing is not just a one-time event, but an ongoing commitment to maintaining the integrity and security of your digital networks. It's an essential part of your cybersecurity toolkit, helping you stay one step ahead in the digital world.
Effective Cybersecurity Testing Techniques
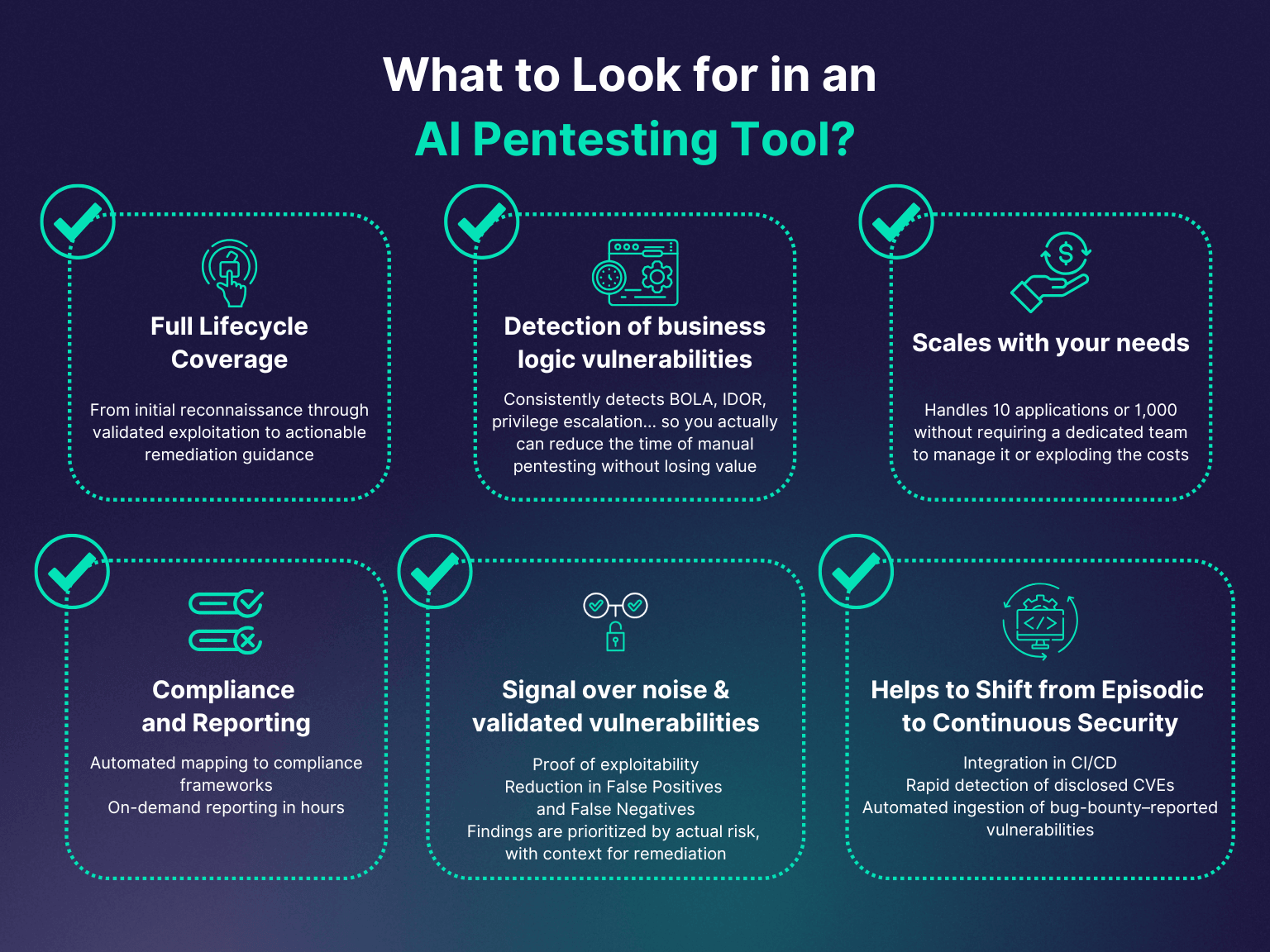
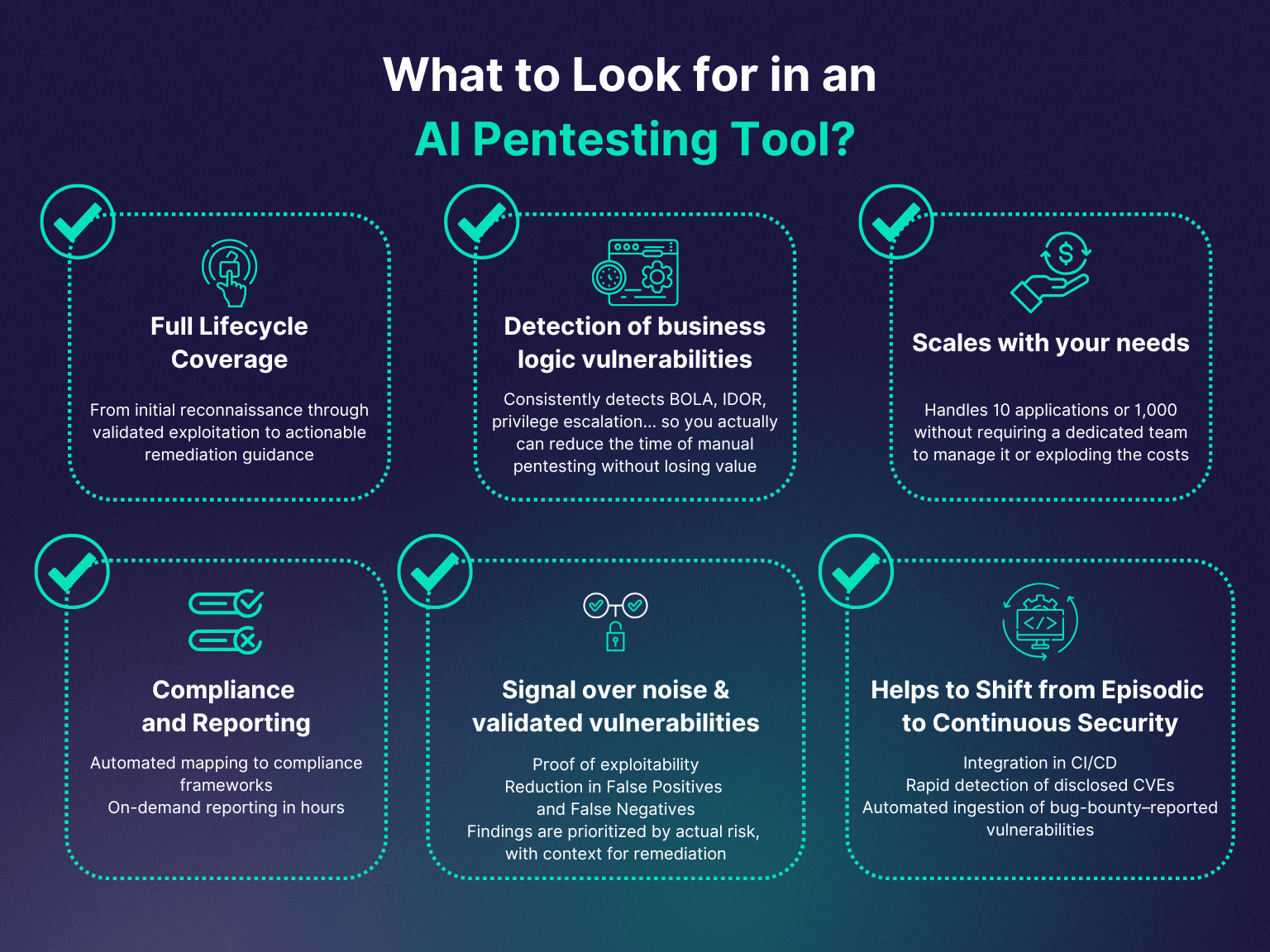
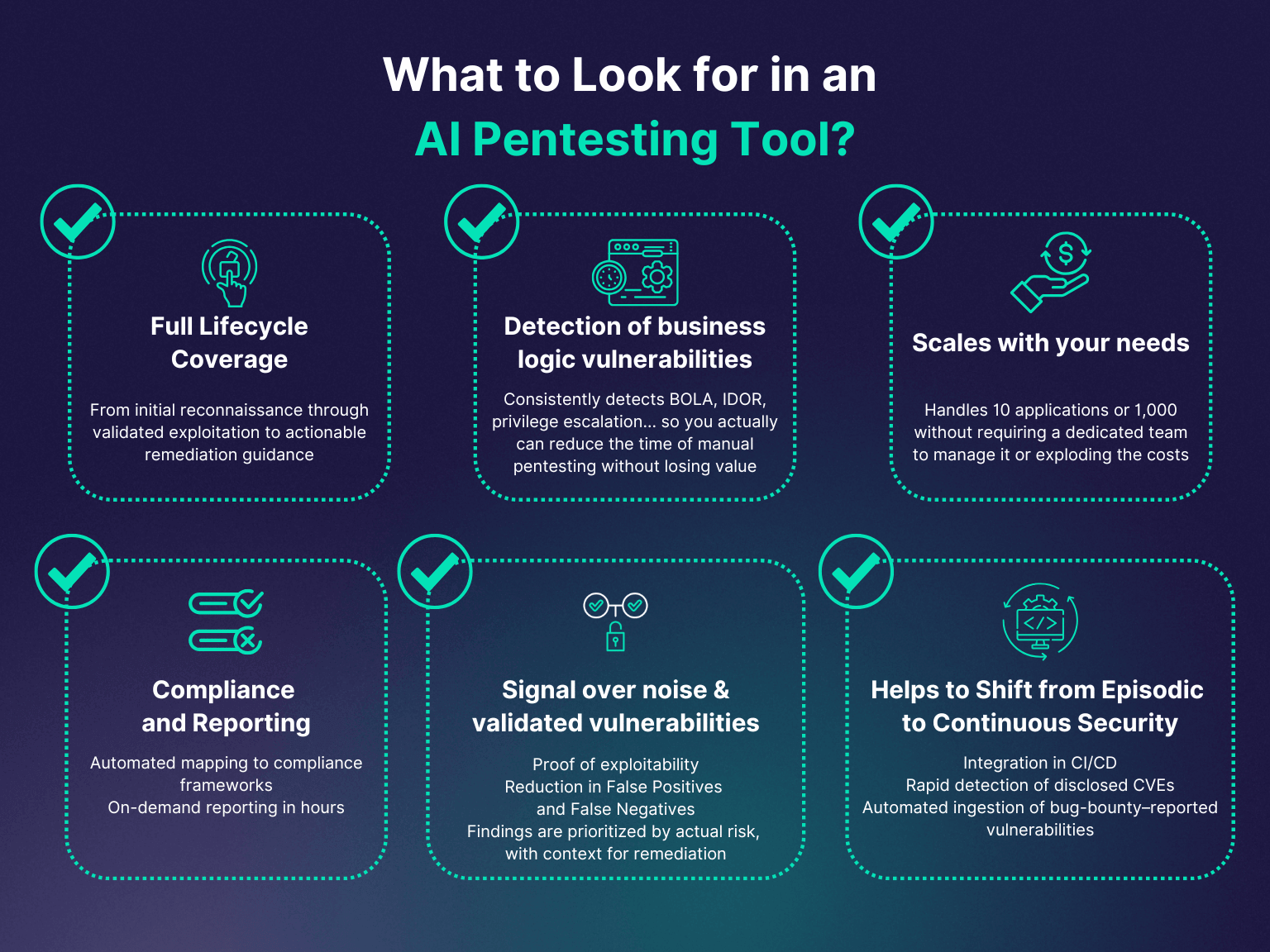
When it comes to fortifying your digital fortress, a variety of Effective Cybersecurity Testing Techniques come into play. These techniques not only help identify potential vulnerabilities but also provide insights into how to patch them up effectively.
One of the most widely adopted techniques is White Box Testing. This method involves a thorough examination of internal structures or workings of an application. It's like having a blueprint of the building you're trying to secure. 
Next up is Black Box Testing. This technique tests the functionality of an application without peering into its internal structures or workings. It's like testing the locks on the doors without knowing the layout of the building. 
Another powerful technique is Grey Box Testing. This is a blend of both white and black box testing. It's like having a partial blueprint of the building while still testing the locks on the doors. 
Lastly, Penetration Testing is a cybersecurity best practice that simulates a cyber attack on your system to identify vulnerabilities. It's like hiring a friendly burglar to try and break into your building to see how secure it really is. 
These techniques, when used in conjunction, provide a comprehensive overview of your network security, making them essential components of any external penetration testing guide. Remember, the digital world is ever-evolving, and so are the threats that come with it. Therefore, continuous testing and updating of security measures is the key to securing digital networks.
Continuous Penetration Testing: Why It Matters
In the ever-evolving landscape of the digital world, Continuous Penetration Testing stands as a pivotal element in maintaining robust cybersecurity. But why does it matter so much? Let's delve into the reasons.
Imagine your network security as a fortress. You've built strong walls (firewalls), stationed guards (antivirus software), and installed advanced surveillance systems (intrusion detection systems). But, how do you ensure that these defenses are truly impenetrable? That's where penetration testing comes into play. It's like a friendly siege on your fortress to identify any weak spots.
However, the digital world is not static. New threats emerge, and old ones evolve. Hence, a one-time test is not enough. Continuous Penetration Testing is akin to regularly checking the integrity of your fortress, making sure it's ready to withstand any attack, anytime. It's one of the cybersecurity best practices that cannot be overlooked.
With continuous penetration testing, you can detect vulnerabilities before attackers do. It's a proactive approach to securing digital networks, allowing you to patch up weaknesses and fortify your defenses. It's not just about finding flaws; it's about continuous improvement and adaptation to the ever-changing digital threats.
So, the importance of continuous penetration testing lies in its ability to keep your cybersecurity measures up-to-date and effective. It's about staying one step ahead in the game of network security.

Remember, the digital world doesn't sleep, and neither should your cybersecurity efforts. Embrace continuous penetration testing, and make your digital fortress unbreachable.
The Significance of Network Security Testing
Now that we've established the importance of continuous penetration testing, let's shift our focus to the broader concept of network security testing. In the grand scheme of cybersecurity best practices, network security testing holds a position of paramount importance. It's not just a single step, but a comprehensive process that encompasses various cybersecurity testing techniques, including penetration testing.
Why is network security testing important? The answer lies in the very nature of our digital world. With the increasing reliance on digital networks for everything from communication to commerce, the stakes have never been higher. A breach in network security can lead to devastating consequences, including data theft, financial loss, and damage to reputation.
Network security testing acts as a preventive measure. It's like a health check-up for your network, identifying potential issues before they turn into full-blown problems. It's about ensuring the integrity and availability of your network, while safeguarding the confidentiality of the data it carries.
External penetration testing is a crucial part of network security testing. It's like a mock drill, simulating real-world attacks to evaluate your network's resilience. This external penetration testing guide can help you understand the penetration testing steps and their significance.
So, the significance of network security testing lies in its proactive approach to cybersecurity. It's about identifying vulnerabilities, assessing risks, and implementing appropriate security measures. It's about ensuring that your digital fortress is not just strong, but also adaptable and resilient.
In the end, network security testing is not just a best practice; it's a necessity in our digital world. It's about staying vigilant and prepared in the face of ever-evolving cyber threats. Remember, in the realm of cybersecurity, offense is the best defense.

Why Security Testing is Crucial in the Digital World
Stepping into the digital world without security testing is akin to venturing into a storm without an umbrella. The digital landscape is teeming with potential threats, and security testing is our shield against these invisible enemies. It's not just an option, but an absolute necessity in our increasingly interconnected world. So, why is security testing so crucial in the digital world?
Firstly, security testing is the cornerstone of cybersecurity best practices. It's the mechanism that helps us identify vulnerabilities in our digital infrastructure, allowing us to patch them before they can be exploited. In essence, it's our first line of defense against cyber threats. 
Secondly, security testing, including penetration testing, is vital for maintaining the integrity of our digital networks. It's the process that ensures our networks are not just secure, but also resilient and adaptable in the face of evolving threats. 
Lastly, continuous security testing is important because it helps us stay ahead of the curve. Cyber threats are not static; they evolve and adapt, becoming more sophisticated with each passing day. By continuously conducting penetration testing and other security tests, we can stay one step ahead of these threats, ensuring our digital networks remain secure. 
In conclusion, security testing is not just a crucial step in cybersecurity; it's the bedrock upon which our digital security rests. Without it, our digital world would be a much more dangerous place. So, let's embrace security testing and make our digital world a safer place for all. 
Key Steps in External Penetration Testing
Now that we've established the importance of external penetration testing, let's explore the Key Steps in External Penetration Testing. This guide will help you understand the process and the cybersecurity testing techniques involved.
Firstly, Planning and Reconnaissance is the initial step. This involves defining the scope and goals of the test, gathering intelligence on the target system to understand its potential vulnerabilities. 
Next comes the Scanning phase, where the tester uses technical tools to understand how the target application or system responds to various intrusion attempts. 
The third step is Gaining Access. Here, the tester attempts to exploit the vulnerabilities identified in the previous step, trying to penetrate the system. 
Once access is gained, the tester moves to the Maintaining Access stage. The goal here is to see if the system is susceptible to a persistent presence, mimicking advanced persistent threats. 
The final step is Analysis and Reporting. The tester documents the vulnerabilities found, the steps taken during the test, the success of each step, and provides recommendations for remediation. 
Remember, each of these steps is crucial in the penetration testing process. They provide a comprehensive view of your network's security posture, helping you understand where you stand in the digital world security measures. External penetration testing is not a one-time event, but a continuous cycle of testing, learning, and improving. It's a key part of cybersecurity best practices, ensuring that your digital networks remain secure in the face of evolving threats.
Continuous Penetration Testing for Network Security
Stepping into the realm of Continuous Penetration Testing for Network Security, we delve deeper into the importance of regular, ongoing scrutiny of your digital defenses. In the dynamic landscape of the digital world, threats evolve at an alarming pace. This necessitates a proactive approach to network security, rather than a reactive one.
Continuous penetration testing is akin to having a dedicated security guard who is always on the lookout for potential threats. This guard doesn't just patrol once and then call it a day. Instead, they are constantly vigilant, ensuring that your digital fortress remains impregnable.

Why is it important to continuously conduct penetration testing? The answer lies in the ever-changing nature of cybersecurity threats. New vulnerabilities can emerge overnight, and old ones can mutate into more dangerous forms. Continuous penetration testing allows you to stay one step ahead of these threats, identifying and patching vulnerabilities before they can be exploited.
Moreover, continuous penetration testing is a key component of cybersecurity best practices. It provides a real-time snapshot of your network's security posture, allowing you to make informed decisions about resource allocation and risk management.
Remember, in the digital world, complacency can be costly. Continuous penetration testing is not just a luxury—it's a necessity for securing digital networks. So, keep your guard up, stay vigilant, and ensure that your network security is always up to the mark.

As we move forward in our external penetration testing guide, we will explore more about how to secure digital networks in the digital world. Stay tuned to learn more about the penetration testing steps and why security testing is so important.
Securing Digital Networks in the Digital World
As we delve into the realm of Securing Digital Networks in the Digital World, it's crucial to remember that the digital world is a vast, interconnected ecosystem. In this ecosystem, network security testing is not just a protective measure—it's an essential survival strategy.
Why is network security testing important? Imagine your digital network as a sprawling city. This city is constantly under threat from cybercriminals—akin to burglars and vandals—who are always looking for weak points to exploit. Network security testing is like a city-wide inspection, identifying these weak points and reinforcing them before they can be exploited.

But securing digital networks goes beyond just identifying and patching vulnerabilities. It also involves implementing cybersecurity best practices and educating your team about them. This is because the human element is often the weakest link in any security chain. By ensuring that everyone in your organization understands the importance of cybersecurity and follows best practices, you can significantly strengthen your digital defenses.
External penetration testing plays a crucial role in this process. It provides a comprehensive assessment of your network's security posture from an outsider's perspective. This can reveal vulnerabilities that internal testing might miss, making it an invaluable tool in your cybersecurity arsenal.
So, why is security testing important? In the digital world, the stakes are high. A single security breach can result in massive data loss, financial damage, and reputational harm. By conducting regular security testing, you can protect your digital assets and ensure that your network remains secure in the face of evolving threats.
Remember, in the digital world, security is not a destination—it's a journey. And on this journey, penetration testing is your trusted guide, helping you navigate the complex landscape of cybersecurity threats and secure your digital networks.

The Role of External Penetration Testing in Cybersecurity
Stepping into the role of External Penetration Testing in Cybersecurity, we find ourselves in the shoes of a potential attacker. This is a critical perspective to adopt in our quest to fortify our digital citadels. The essence of external penetration testing lies in its ability to mimic the tactics, techniques, and procedures (TTPs) of real-world cybercriminals. It's like hiring a skilled locksmith to test the strength of your locks. 
External penetration testing is an essential part of cybersecurity best practices. It provides a fresh, unbiased perspective on your network's security. This 'outsider view' can uncover blind spots that may have been overlooked during internal testing. These blind spots are often the very loopholes that cybercriminals exploit. 
Moreover, external penetration testing is not a one-time event. It's a continuous process that needs to be integrated into your cybersecurity strategy. The digital landscape is ever-evolving, with new threats emerging daily. By continuously conducting penetration testing, you stay one step ahead of these threats, ensuring your network's security is always up to date. 
So, why is external penetration testing so important? It's simple. It gives you the upper hand in the digital world. It empowers you to anticipate and prepare for potential attacks, rather than reacting to them. In the grand chessboard of cybersecurity, external penetration testing is your knight, providing the strategic insight needed to safeguard your digital kingdom. 
The Importance of Network Security Testing
Now that we've established a basic understanding of external penetration testing, let's delve deeper into the importance of network security testing. Network security testing is akin to the immune system of the digital world. It's the first line of defense against cyber threats, much like our immune system protects us from diseases. Without it, your digital networks are left vulnerable to a myriad of cyber attacks.
Network security testing is a critical component of cybersecurity best practices. It's not just about identifying vulnerabilities; it's also about understanding how these vulnerabilities can be exploited and the potential consequences of such breaches. This knowledge is crucial in developing effective countermeasures and securing digital networks.

One of the key benefits of network security testing is that it provides a real-world perspective on your network's security posture. It simulates the tactics, techniques, and procedures (TTPs) that hackers use, providing valuable insights into how your defenses might hold up under a real attack. This is why security testing is important - it helps you stay one step ahead of the attackers.
Regular network security testing is also essential because the threat landscape is constantly evolving. New vulnerabilities are discovered every day, and hackers are always coming up with new ways to exploit them. By continuously conducting penetration testing, you ensure that your network security measures are always up-to-date and capable of defending against the latest threats.
In summary, network security testing is a critical component of any cybersecurity strategy. It helps identify vulnerabilities, understand potential attack paths, and develop effective countermeasures. It's an essential tool in the fight against cyber threats, helping to keep your digital networks secure and your data safe.
Steps to Conduct External Penetration Testing
Embarking on the journey of external penetration testing is a critical step in fortifying your cybersecurity defenses. This process can be broken down into several key steps, each of which plays a vital role in ensuring the robustness of your network security.
The first step is planning and reconnaissance. This involves defining the scope of the test, identifying the systems to be tested, and gathering as much information as possible about the target. This step is crucial in setting the stage for the entire testing process. 
Next, you move on to scanning. This involves using automated tools to identify potential vulnerabilities in the system. It's akin to a doctor using a stethoscope to listen for any irregularities in a patient's heartbeat. 
Once potential vulnerabilities have been identified, the next step is gaining access. This involves exploiting the identified vulnerabilities to break into the system. It's a critical step in understanding how a real attacker might breach your defenses. 
The fourth step is maintaining access. This involves trying to remain within the system undetected, mimicking the actions of a real attacker who would want to maintain long-term access to the network. 
Finally, the last step is analysis and reporting. This involves documenting the vulnerabilities discovered, the successful exploits, and the data accessed. This report is crucial in understanding the security flaws in your system and devising strategies to fix them. 
Each of these steps is crucial in the external penetration testing guide, helping you to understand and implement the best cybersecurity testing techniques. Remember, the goal is not just to find vulnerabilities, but to understand how they can be exploited and how to prevent such breaches in the future.
Best Practices for Cybersecurity Testing
Stepping into the realm of Best Practices for Cybersecurity Testing, it's essential to grasp the significance of adopting a proactive approach. Remember, cybersecurity isn't a one-time event, but a continuous process that requires regular updates and improvements. Here are some of the best practices to enhance your cybersecurity testing techniques.
Firstly, adopt a risk-based approach. Prioritize your assets based on their importance and vulnerability to attacks. This will help you focus your efforts where they are needed the most. 
Secondly, automate where possible. Automation can help you identify vulnerabilities faster and more accurately. However, it's important to remember that automation is not a replacement for human judgment. Manual testing is still necessary for complex vulnerabilities that automated tools might miss. 
Thirdly, keep your testing tools up-to-date. Cyber threats are constantly evolving, and so should your tools. Regularly updating your tools ensures that you are equipped to deal with the latest threats. 
Fourthly, foster a culture of security within your organization. Everyone in the organization should understand the importance of cybersecurity and their role in maintaining it. Regular training and awareness programs can help achieve this. 
Lastly, learn from your mistakes. Every penetration test is a learning opportunity. Use the insights gained from each test to improve your security measures and testing techniques. 
Following these best practices will not only enhance your cybersecurity testing techniques but also strengthen your overall network security. Remember, in the digital world, security is not a destination, but a journey.
The Role of Penetration Testing in the Digital World
As we navigate the vast expanse of the digital world, the role of penetration testing becomes increasingly pivotal. It's like a compass guiding us through the labyrinth of cybersecurity threats, pointing out vulnerabilities and helping us fortify our defenses.
Penetration testing, or pen testing, is a simulated cyber attack against your system to check for exploitable vulnerabilities. It's the digital equivalent of a fire drill, preparing us for real-life cyber threats. In the digital world, where data is the new gold, penetration testing is the knight in shining armor, safeguarding our precious assets.

Imagine your network as a castle. The castle is surrounded by high walls and deep moats, but is it really secure? Penetration testing is like a friendly siege, testing the castle's defenses to ensure no enemy can breach them. It's a proactive approach to network security testing, identifying weak spots before they can be exploited.
But why is it important to continuously conduct penetration testing? The digital world is ever-evolving, and so are the threats it harbors. New vulnerabilities can emerge overnight, turning what was once a secure system into a potential target. Continuous penetration testing keeps us one step ahead of cybercriminals, ensuring our defenses are always up to date.
So, in essence, penetration testing is not just a part of cybersecurity best practices, it's the heart of it. It's the key to securing digital networks, making the digital world a safer place for us all.
The Role of Penetration Testing in Cybersecurity
Stepping into the spotlight, let's explore The Role of Penetration Testing in Cybersecurity. Penetration testing, often fondly referred to as 'pen testing', is the unsung hero in the narrative of cybersecurity. It's the secret agent that infiltrates your system, not with malicious intent, but to uncover potential weaknesses before the real villains do.
Imagine pen testing as a friendly ghost, invisible yet present, slipping through your digital walls to find cracks and crevices.  It's a proactive approach, a pre-emptive strike against potential cyber threats. This is why it's a cornerstone in cybersecurity best practices.
It's a proactive approach, a pre-emptive strike against potential cyber threats. This is why it's a cornerstone in cybersecurity best practices.
But what makes pen testing so vital? It's simple. It provides a real-world perspective on your network's security. By simulating cyber-attacks, pen testing can reveal how an actual attack might occur, the potential damage it could cause, and how well your defenses would hold up.
Penetration testing steps are like a treasure map, guiding you to hidden vulnerabilities in your network.  It's an external penetration testing guide, offering a fresh, unbiased view of your network's security.
It's an external penetration testing guide, offering a fresh, unbiased view of your network's security.
But remember, pen testing is not a one-time event. The digital world is ever-evolving, and so are the threats it harbors. This is why it is important to continuously conduct penetration testing. Regular pen testing ensures that your network remains secure, even as new vulnerabilities emerge and old ones evolve.
So, in the grand scheme of cybersecurity, pen testing is not just a tool—it's a lifeline. It's the key to securing digital networks and staying one step ahead in the dynamic digital world.
Benefits of External Penetration Testing
Now that we've delved into the role and importance of penetration testing, let's shift our focus onto the Benefits of External Penetration Testing. The advantages of this cybersecurity testing technique are manifold, and they play a crucial role in fortifying your digital defenses.
Firstly, external penetration testing provides a realistic assessment of your network's security posture. It's akin to a health check-up for your digital infrastructure, providing a comprehensive diagnosis of your network's vulnerabilities. 
Secondly, external penetration testing is a proactive measure against cyber threats. It's the digital equivalent of a fire drill, preparing you for potential cyber-attacks and helping you understand how to respond effectively. This is why network security testing is so important—it's not just about identifying weaknesses, but also about learning how to mitigate them.
Thirdly, external penetration testing is a valuable tool for compliance. Many industries require regular penetration testing as part of their regulatory standards. By conducting these tests, you're not just securing your network—you're also ensuring that your organization stays on the right side of the law. 
Finally, external penetration testing helps build trust with your clients and stakeholders. By demonstrating that you take cybersecurity seriously and are committed to protecting your network, you're showing that you value their data and privacy. In the digital world, where data breaches are all too common, this can be a significant competitive advantage. 
In essence, external penetration testing is a critical step in cybersecurity. It's a proactive, comprehensive, and legally compliant approach to securing digital networks. It's not just about protecting your network—it's about safeguarding your reputation, your compliance status, and your relationships with clients. That's the true power of penetration testing.



No comments yet. Be the first to share your thoughts!