Understanding the Importance of Cloud Network Security
As we delve into the digital age, the importance of cloud network security cannot be overstated. The cloud has transformed how we store and manage data, offering flexibility, scalability, and cost-effectiveness. However, these benefits come with their own set of challenges, particularly in terms of data protection.
Understanding network security in the cloud is crucial for businesses and individuals alike. When you move your data to the cloud, you're entrusting a third-party provider with sensitive information. This could range from personal details to financial records, intellectual property, or proprietary business data. If this data falls into the wrong hands, the consequences can be devastating.

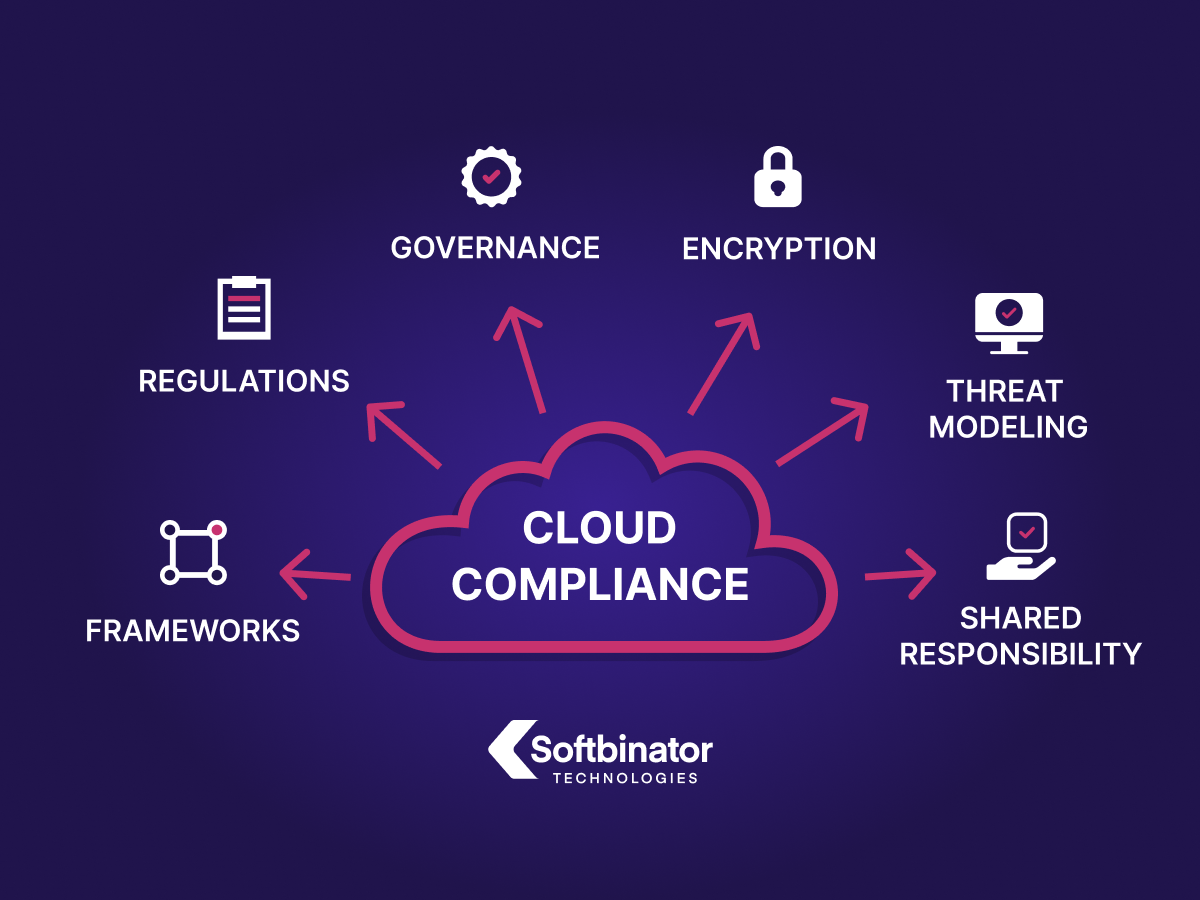
Cloud network security is all about implementing measures to safeguard this data. It involves a combination of policies, controls, procedures, and technologies that work together to protect your cloud-based systems. This is where concepts like penetration testing for cloud come into play, helping to identify vulnerabilities that could be exploited by malicious entities.
Moreover, with the advent of regulations like the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA), businesses are now legally obligated to protect their customers' data. Non-compliance can result in hefty fines, not to mention damage to brand reputation.
So, whether you're using AWS, Google Cloud Platform, or any other cloud service, understanding and implementing robust cloud network security measures is not just a good practice—it's a necessity in our increasingly digital world.
The Basics of Cloud Network Security
Let's dive into the basics of cloud network security. At its core, cloud network security is about safeguarding your data in the cloud. It's a complex field, encompassing a range of strategies and tools designed to protect data, applications, and the associated infrastructure of cloud computing.
One of the fundamental aspects of cloud security is access control. This ensures that only authorized individuals can access your data. It's typically managed through a combination of usernames, passwords, and two-factor authentication. 
Another crucial element is encryption. Encryption transforms your data into a code that can only be deciphered with a specific key. This means that even if a hacker manages to access your data, they won't be able to understand it without the decryption key. 
Then there's firewalls. Just like the firewalls in your home network, cloud firewalls are designed to block unauthorized access to your cloud-based data. They monitor and control incoming and outgoing network traffic based on predetermined security rules. 
Finally, we have intrusion detection systems (IDS) and intrusion prevention systems (IPS). These systems monitor your network for malicious activities or policy violations and report them to the system or network administrator. In some cases, they can also prevent or block these activities. 
These are just a few examples of the tools and strategies used in cloud network security. Each plays a vital role in creating a secure digital world with cloud. However, it's important to remember that cloud security is a shared responsibility. While your cloud provider will have their own security measures in place, it's up to you to ensure your data is as secure as possible.
Penetration Testing for Cloud Networks
Now that we've covered the basics of cloud network security, let's delve into the world of penetration testing for cloud networks. Penetration testing, often referred to as pen testing, is a simulated cyber attack against your system to check for exploitable vulnerabilities. In the context of cloud security, it's akin to a digital 'stress test' for your cloud-based data protection measures.
Penetration testing is a critical aspect of data protection in cloud. It helps you identify weak spots in your security before a real attacker does. Think of it as a safety drill, preparing you for any potential cybersecurity threats that might come your way in the digital world.
There are several types of penetration tests, each designed to analyze different aspects of your cloud network security. For instance, AWS penetration tests focus specifically on the security measures in place on Amazon Web Services. Similarly, cloud penetration tests are designed to evaluate the robustness of your cloud-based systems.
During a penetration test, the tester might try to exploit vulnerabilities in your system, attempt to gain unauthorized access to sensitive data, or even disrupt your services. The goal is not to cause harm, but to identify areas where your security can be improved.
By regularly conducting penetration tests, you can stay one step ahead of cybercriminals. It's an essential part of maintaining a secure digital world with cloud. Remember, the more you understand about your network security in the cloud, the better you can protect your data.

Cybersecurity Best Practices for Cloud Networks
Having understood the importance of penetration testing in ensuring a robust cloud network security, let's now focus on the Cybersecurity Best Practices for Cloud Networks. These are the measures that you can put in place to ensure that your data is protected in the cloud and you maintain a secure digital world.
Firstly, encryption is a must-have for any cloud network. Encryption converts your data into a code that can only be deciphered with a decryption key. This means that even if an attacker manages to access your data, they won't be able to understand it. 
Secondly, multi-factor authentication (MFA) is a simple yet effective way to add an extra layer of security. MFA requires users to provide two or more verification factors to gain access to a resource such as an application, online account, or a VPN. 
Thirdly, regular security updates are crucial. Cloud providers often release security updates to fix vulnerabilities in their systems. It's essential to apply these updates as soon as they're available to prevent cybercriminals from exploiting these vulnerabilities. 
Lastly, access control is a fundamental aspect of cloud network security. This involves defining who has access to what data and what they can do with it. It's crucial to limit access to sensitive data to only those who need it for their job roles. 
These are just a few examples of the best practices for cybersecurity in cloud networks. By implementing these measures, you can significantly enhance your data protection in the cloud and maintain a secure digital world.
Securing Your Data on AWS
As we delve into the realm of Securing Your Data on AWS, it's crucial to understand that Amazon Web Services (AWS) is a leading player in the cloud network security landscape. AWS offers a robust and flexible framework for data protection in the cloud, but it's up to you to leverage these tools effectively.
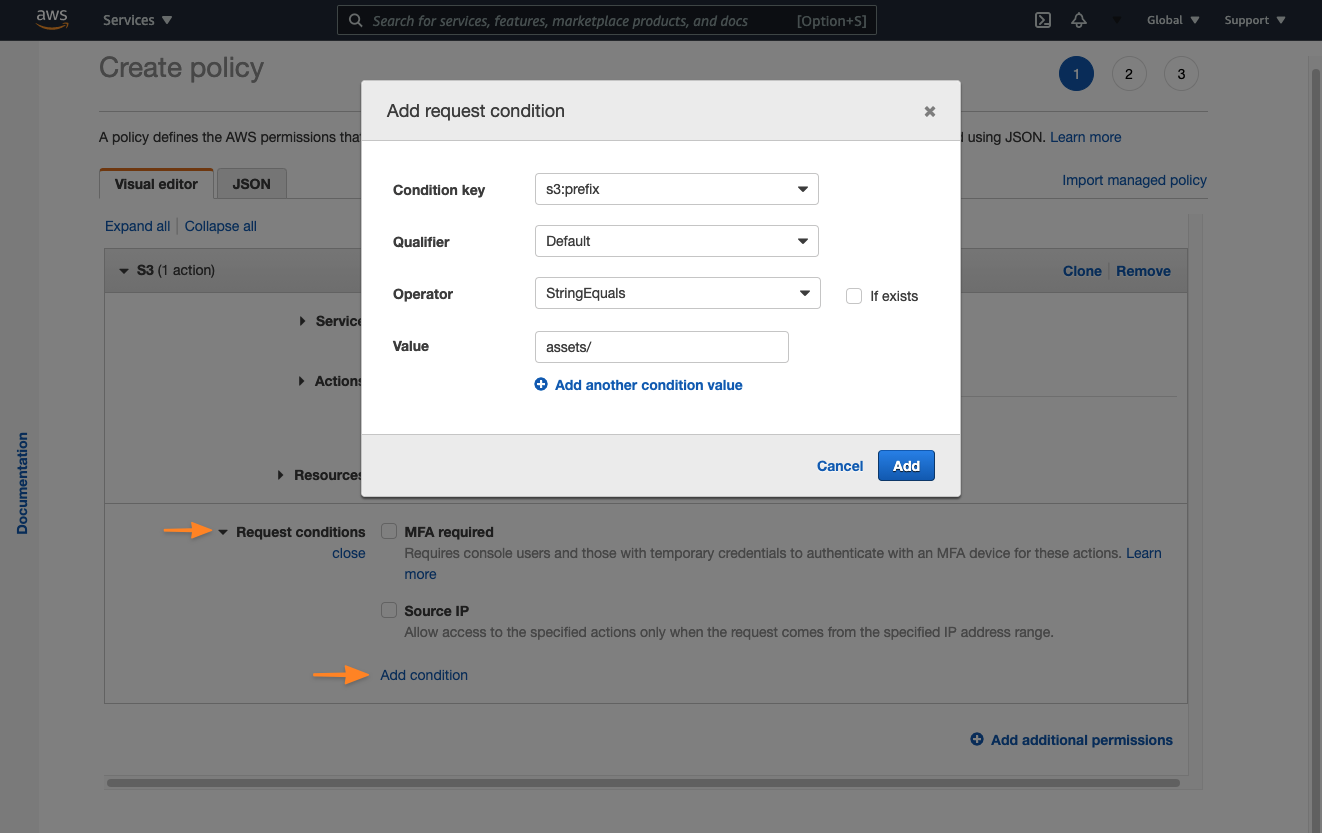
Firstly, let's talk about AWS Identity and Access Management (IAM). This service allows you to manage access to your AWS resources. You can create and manage AWS users and groups, and use permissions to allow and deny their access to AWS resources. It's a fundamental step towards securing your data on AWS.
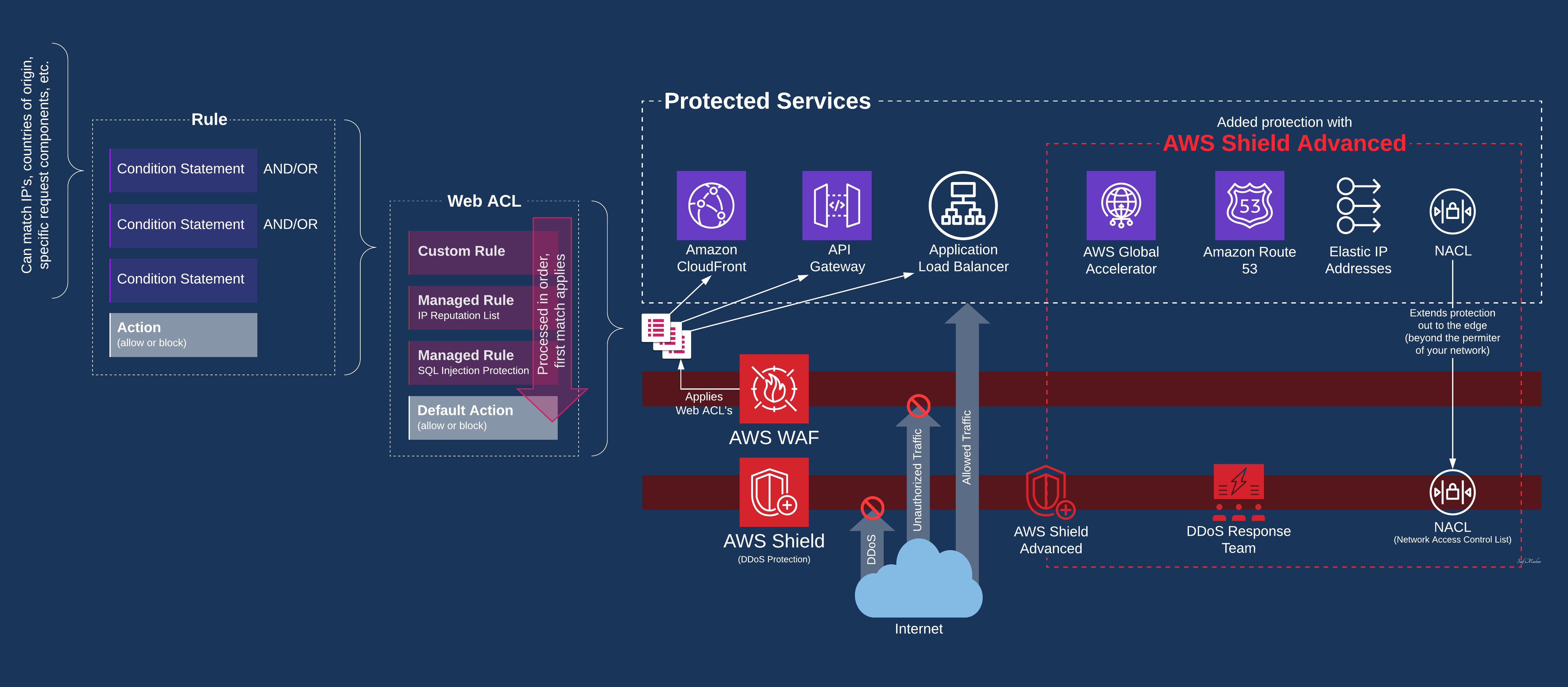
Another significant aspect of AWS security is the AWS Shield, a managed Distributed Denial of Service (DDoS) protection service that safeguards applications running on AWS. AWS Shield provides automatic protections that minimize application downtime and latency, so your application remains available and performant.
For those interested in penetration testing for cloud, AWS also supports this. AWS penetration tests are a way to identify potential vulnerabilities in your system. However, it's important to note that these tests must comply with AWS's testing policies.
Lastly, don't forget about the importance of regular cloud security updates. AWS frequently releases security bulletins detailing any vulnerabilities and the necessary actions to mitigate them. Staying updated with these bulletins can help you maintain a secure digital world with cloud.
In conclusion, understanding network security in cloud, particularly on platforms like AWS, is a vital part of data protection. By leveraging the tools and services provided by AWS, you can ensure that your data remains secure and accessible.
Enhancing Security on Google Cloud Platform
Shifting our focus to the Google Cloud Platform (GCP), let's explore how to enhance your cloud network security on this popular platform. Google Cloud Platform, much like AWS, provides a comprehensive suite of tools and services designed to bolster your data protection in the cloud. However, the key to a secure digital world with cloud lies in understanding how to effectively utilize these resources.
One of the most critical components of GCP's security is the Google Cloud Identity and Access Management (IAM). Similar to AWS IAM, Google Cloud IAM allows you to manage who has what access to your GCP resources. You can define roles and assign them to users, groups, or service accounts, controlling who can take action on specific resources. This granular control over resource access is a cornerstone of cloud network security.

When it comes to penetration testing for cloud, Google Cloud Platform is no exception. Google encourages users to conduct penetration testing on their GCP environments to identify and address vulnerabilities. However, it's important to remember that Google has specific policies regarding penetration testing, and it's essential to abide by these rules.
Another crucial aspect of GCP security is staying updated with Google Cloud Platform security bulletins. These bulletins provide timely information about security issues that might affect your GCP environment. Regularly reviewing these bulletins and implementing the recommended actions can significantly enhance your cloud network security.

Finally, Google Cloud Security Command Center is a powerful tool that provides insights into your GCP security health. It helps identify and manage threats, making it easier for you to stay secure in the cloud.
To sum up, the Google Cloud Platform offers a robust set of tools and services to enhance your cloud network security. By understanding and effectively utilizing these resources, you can ensure a secure digital world with cloud.
Understanding Cloud Network Security
When we talk about the digital world, one term that often comes to the forefront is cloud network security. But what exactly does it mean? Let's delve into the basics of understanding network security in the cloud.
Cloud network security is a sub-domain of cybersecurity that focuses specifically on securing data stored in the cloud. It's all about protecting your data from threats like unauthorized access, data breaches, and other cyber-attacks. With the increasing reliance on cloud-based services, understanding and implementing robust cloud network security measures has become paramount.
Imagine your data as a treasure chest. In the old days, you'd store this chest in a physical vault. But in today's digital age, this vault is the cloud. The security of this vault, i.e., the cloud, is what we refer to as cloud network security.

Cloud network security involves several strategies and tools. These include firewalls, intrusion detection systems, and encryption, among others. It also involves regular penetration testing for cloud networks to identify potential vulnerabilities. Companies like Amazon Web Services (AWS) and Google Cloud Platform offer their own security measures and updates to ensure your data remains secure.
So, whether you're a small business owner storing customer data or an individual storing personal files, understanding cloud network security is crucial in this digital age. It's not just about protecting your data; it's about ensuring a secure digital world with cloud.
Cybersecurity for Cloud Networks
Stepping into the realm of Cybersecurity for Cloud Networks, we find ourselves in a complex labyrinth of protocols, firewalls, and encryption. This is where the real battle against cyber threats takes place. In this digital fortress, every piece of data is guarded like a precious gem, and every communication is encrypted to ensure its safe passage.
When we talk about cybersecurity for cloud networks, we're referring to a set of strategies and practices designed to protect your data and applications that reside in the cloud. It's about creating a secure digital world with cloud, where your data can live and move freely, without fear of being intercepted or tampered with.
One of the key elements of cloud network security is encryption. Encryption is like a secret language that only your system understands. When data is encrypted, it's transformed into a code that can only be read with the right key. This means that even if a hacker manages to intercept your data, they won't be able to understand it without the key. 
Another critical aspect of cybersecurity for cloud networks is access control. This involves setting up strict rules about who can access your data and what they can do with it. For example, you might allow certain users to view your data, but not modify it. Or, you might restrict access to sensitive data to a select few individuals. 
Finally, let's not forget about the importance of regular cloud security updates. These updates often contain patches for known vulnerabilities, making them a crucial part of your defense strategy. By staying updated with cloud security, you're essentially reinforcing your digital fortress, making it harder for cybercriminals to break in. 
In the end, understanding network security in the cloud is all about knowing how to protect your data. It's about being proactive, staying updated, and always being one step ahead of the cybercriminals. Remember, in the digital world, knowledge is your best weapon.
AWS Penetration Testing: Ensuring Security in the Cloud
AWS Penetration Testing: Ensuring Security in the Cloud
When it comes to data protection in the cloud, AWS penetration testing is a crucial tool. It's a proactive approach to safeguarding your data, allowing you to identify vulnerabilities before they can be exploited. AWS penetration testing is a simulated cyber attack on your AWS environment, aimed at uncovering weak spots in your cloud network security.
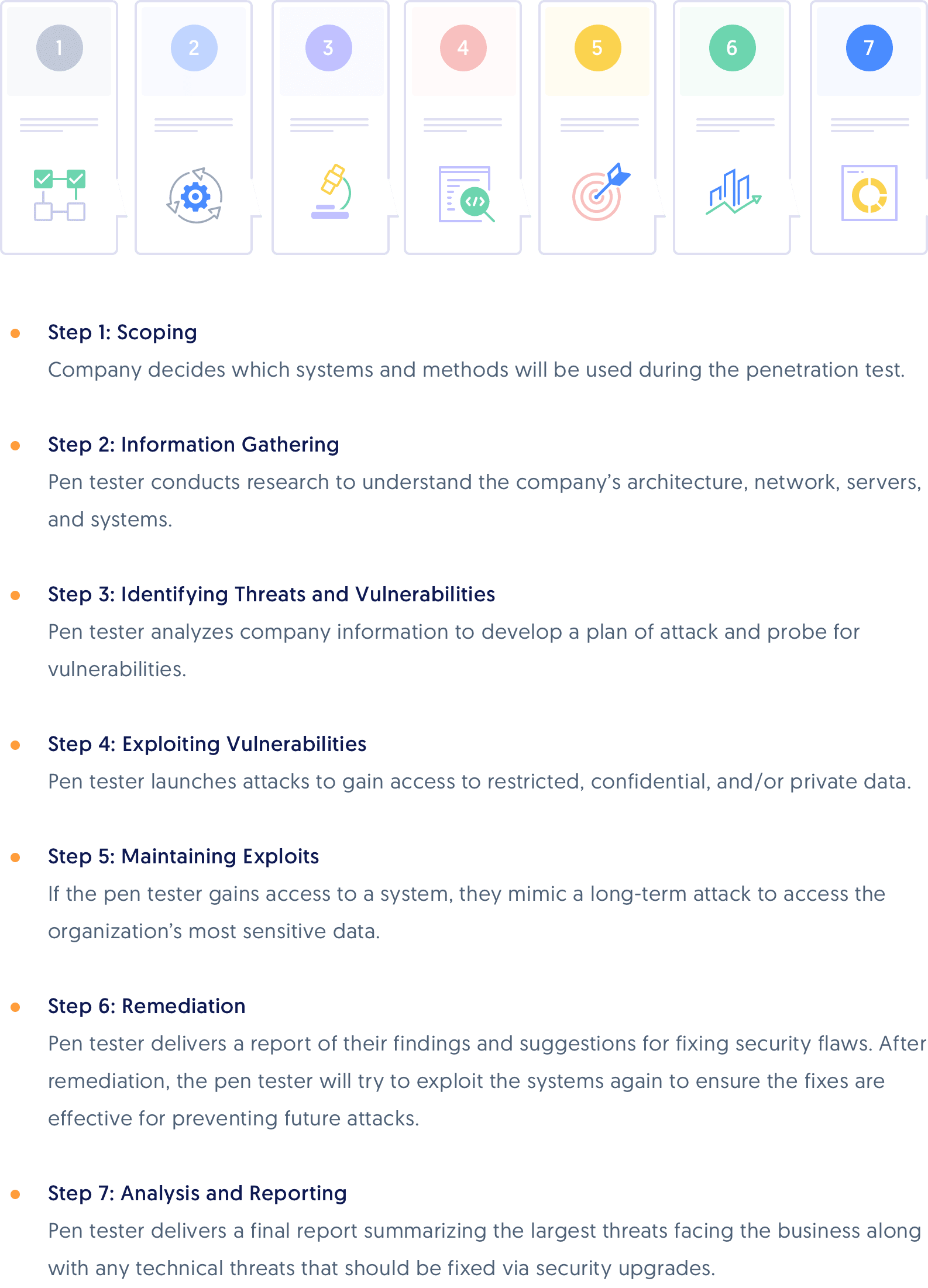
Penetration tests are performed under controlled conditions, with the primary objective of understanding network security in the cloud. They provide a comprehensive view of your cloud security posture, helping you to prioritize security updates and fortify your defenses.
But how does AWS penetration testing work? The process begins with the identification of potential vulnerabilities in your AWS environment. This could be anything from misconfigured security groups to weak encryption protocols. Once these vulnerabilities are identified, the next step is to attempt to exploit them, mimicking the actions of a potential attacker.

Finally, a detailed report is generated, outlining the vulnerabilities discovered and providing recommendations for remediation. This report serves as a roadmap for enhancing your cloud network security, ensuring a secure digital world with cloud.
Remember, AWS penetration tests are not a one-time activity. They should be conducted regularly to keep up with the ever-evolving threat landscape. With AWS penetration testing, you can stay one step ahead of the cybercriminals, ensuring the security of your data in the cloud.
Google Cloud Platform Security Bulletins
Google Cloud Platform Security Bulletins: Your Guide to a Safer Cloud Environment
As we delve deeper into the realm of cloud network security, it's essential to stay updated with the latest security bulletins. One of the most reliable sources for such updates is the Google Cloud Platform Security Bulletins. These bulletins provide timely information about the latest vulnerabilities and threats, helping you to maintain a secure digital world with cloud.
Google Cloud Platform Security Bulletins are comprehensive reports that detail the latest security vulnerabilities discovered in Google Cloud services. They provide a clear understanding of network security in the cloud, offering insights into potential risks and how they can be mitigated. Each bulletin includes a description of the vulnerability, its severity rating, potential impact, and recommended actions for remediation.
For instance, if a vulnerability is discovered in Google's data storage service, the bulletin will provide details about the issue, its potential impact on data protection in the cloud, and steps to address it. This way, you can take immediate action to safeguard your data and maintain the integrity of your cloud environment.
Staying updated with Google Cloud Platform Security Bulletins is a proactive approach to cloud network security. It allows you to stay ahead of potential threats and ensure the safety of your data in the cloud. Remember, cybersecurity for cloud networks is not a passive task; it requires constant vigilance and timely action.
Google Cloud Platform Security Bulletins are an excellent resource for anyone interested in cloud security. They offer a wealth of information that can help you understand the basics of cloud network security, making them an essential part of your cybersecurity toolkit.
So, whether you're conducting penetration testing for cloud or simply looking to enhance your cloud security posture, make sure to keep an eye on Google Cloud Platform Security Bulletins. They're your guide to a safer, more secure cloud environment.

Introduction to Cloud Network Security
Welcome to the world of cloud network security. As we venture into the digital realm, the need for data protection in the cloud has never been more critical. This is your introduction to cloud security, a guide designed to help you navigate the complexities of this essential field.
Cloud network security is a sub-discipline of cybersecurity that focuses on the protection of data, applications, and infrastructures involved in cloud computing. It's about creating a secure digital world with cloud technology. As more businesses migrate to the cloud, understanding network security in the cloud becomes a necessity, not a luxury.
Imagine the cloud as a fortress. The data you store on the cloud is the treasure within, and cloud network security is the robust wall that protects this treasure from cyber threats. From the smallest startups to the largest corporations, everyone is a potential target.
But fear not! With the right knowledge and tools, you can fortify your cloud fortress. This includes staying updated with cloud security updates, conducting regular penetration testing for cloud networks, and understanding the unique security features of different cloud platforms like AWS and Google Cloud Platform.
So, let's embark on this journey together, to understand, implement, and maintain a secure cloud network.

Whether you're a seasoned IT professional or a curious beginner, this guide will provide you with the basics of cloud network security and help you take the first steps towards a more secure digital world.
Understanding the Basics of Cloud Security
As we delve into the realm of cloud network security, it's crucial to understand the basics. Cloud security is not a single entity but a collection of protocols, strategies, and tools designed to safeguard data, applications, and infrastructure in the cloud. It's about creating a secure digital world with cloud technology.
At the heart of cloud security are three core principles: confidentiality, integrity, and availability, often referred to as the CIA triad. Confidentiality ensures that your data is accessible only to authorized individuals. Integrity guarantees that your data remains accurate and consistent over its entire lifecycle. And availability ensures that your data is always accessible when needed. 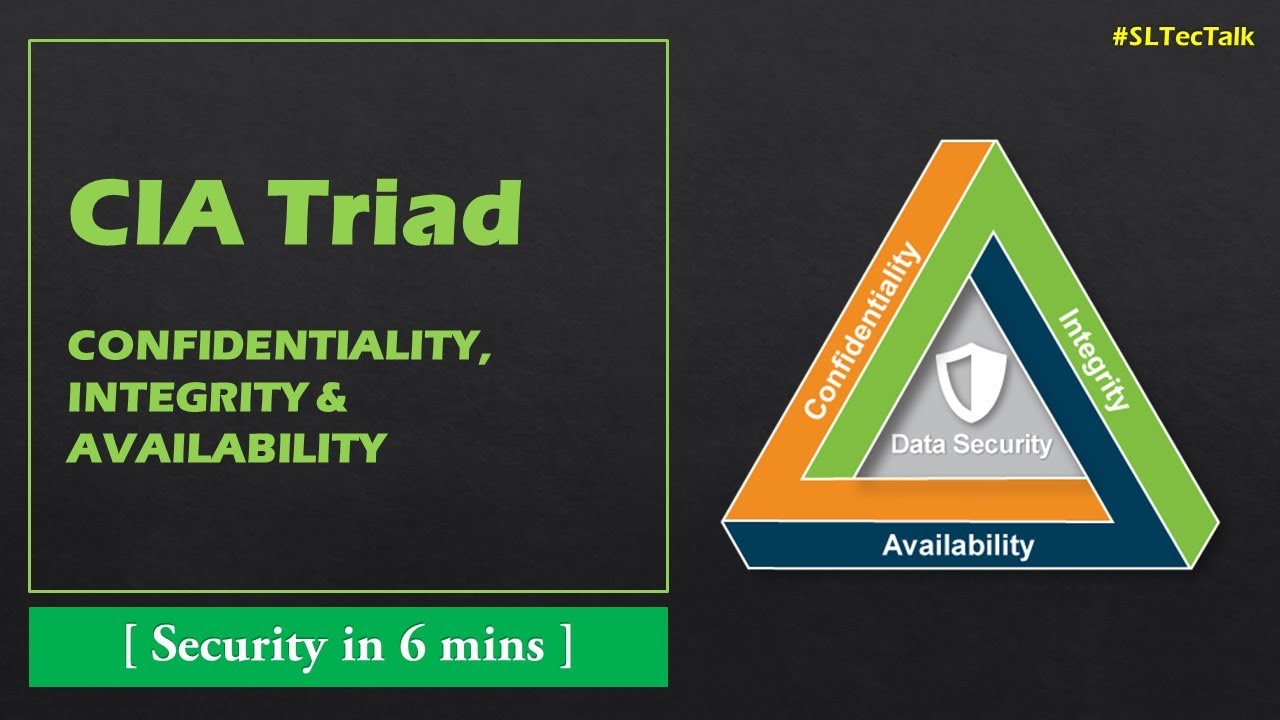
Another essential aspect of cloud security is access control. This involves defining who can access your data and what they can do with it. Access control mechanisms can be as simple as username/password combinations or as complex as multi-factor authentication systems. 
Cloud security also involves encryption, a method of converting data into a code to prevent unauthorized access. When your data is in the cloud, it's often in a shared environment. Encryption ensures that even if someone can access the environment, they can't make sense of your data without the decryption key. 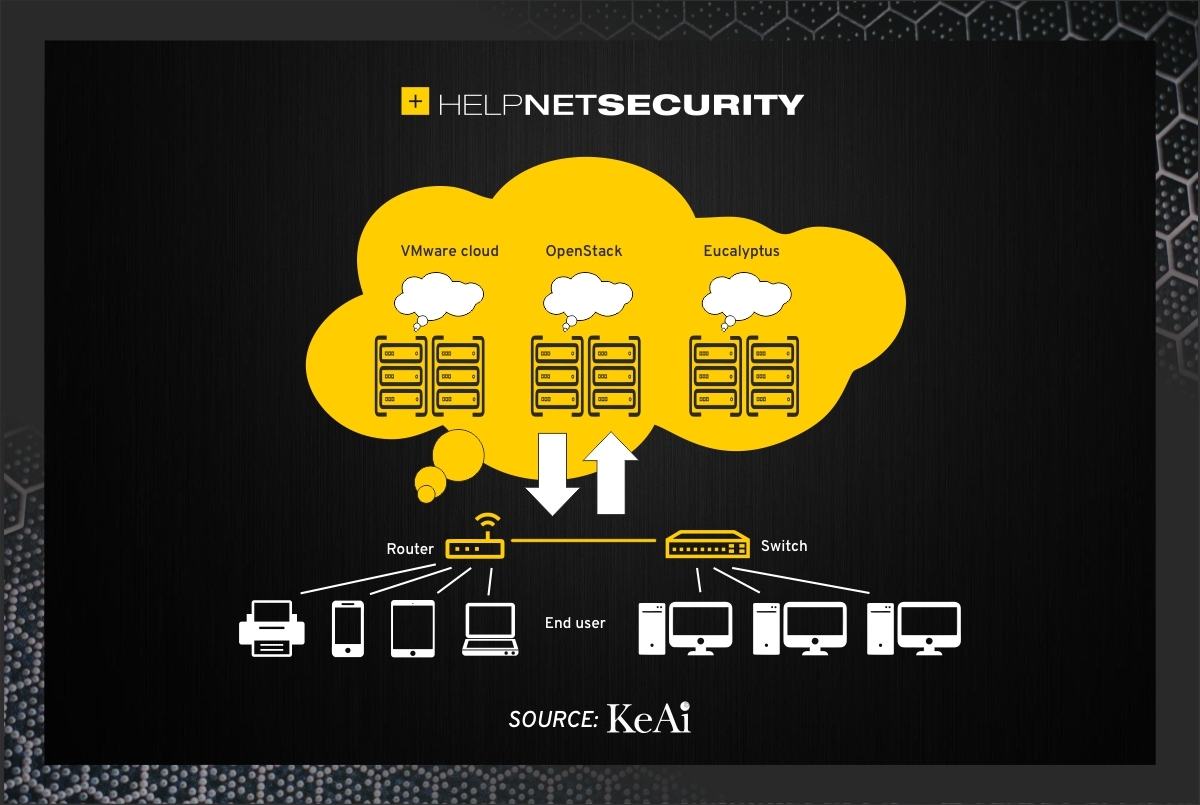
Lastly, penetration testing is a critical aspect of cloud security. It involves simulating cyberattacks on your cloud network to identify vulnerabilities before they can be exploited. Regular penetration tests can help you stay one step ahead of cybercriminals. 
In essence, understanding the basics of cloud security is about understanding how to protect your data in the cloud from unauthorized access, maintain its integrity, ensure its availability, control who can access it, and regularly test your security measures for weaknesses. With these basics, you're well on your way to a more secure cloud network.
The Importance of Penetration Testing for Cloud Networks
Stepping into the spotlight, let's focus on penetration testing for cloud networks, an essential pillar in the fortress of cloud security. Penetration testing, often referred to as 'pen testing', is akin to a fire drill for your cloud network. It's an intentional, controlled, and proactive approach to uncovering vulnerabilities in your cloud network before they become a gateway for cybercriminals.

Imagine your cloud network as a castle. Penetration testing is like inviting a friendly knight to test your castle's defenses. This knight, armed with the same tools and tactics as an adversary, will attempt to breach your castle. The objective? To expose any weak spots in your defenses, giving you the chance to reinforce them before an actual adversary strikes.
Penetration testing is particularly crucial for data protection in the cloud. In the vast digital landscape of the cloud, data can be stored in multiple places, making it a potential treasure trove for cybercriminals. Penetration testing helps ensure that your data—your treasure—is well-guarded.
Moreover, with the rise of cloud services like AWS and Google Cloud Platform, penetration testing has become even more vital. These platforms regularly undergo AWS penetration tests and Google Cloud Platform security bulletins to keep their users updated about their security status.

In the grand scheme of cybersecurity for cloud networks, penetration testing is not just an optional extra—it's a necessity. It's a proactive measure that helps you stay ahead in the ever-evolving world of cloud security. So, remember, a secure digital world with cloud technology is not just about building robust defenses, but also about regularly testing and improving them.
Cybersecurity Measures for Cloud Networks
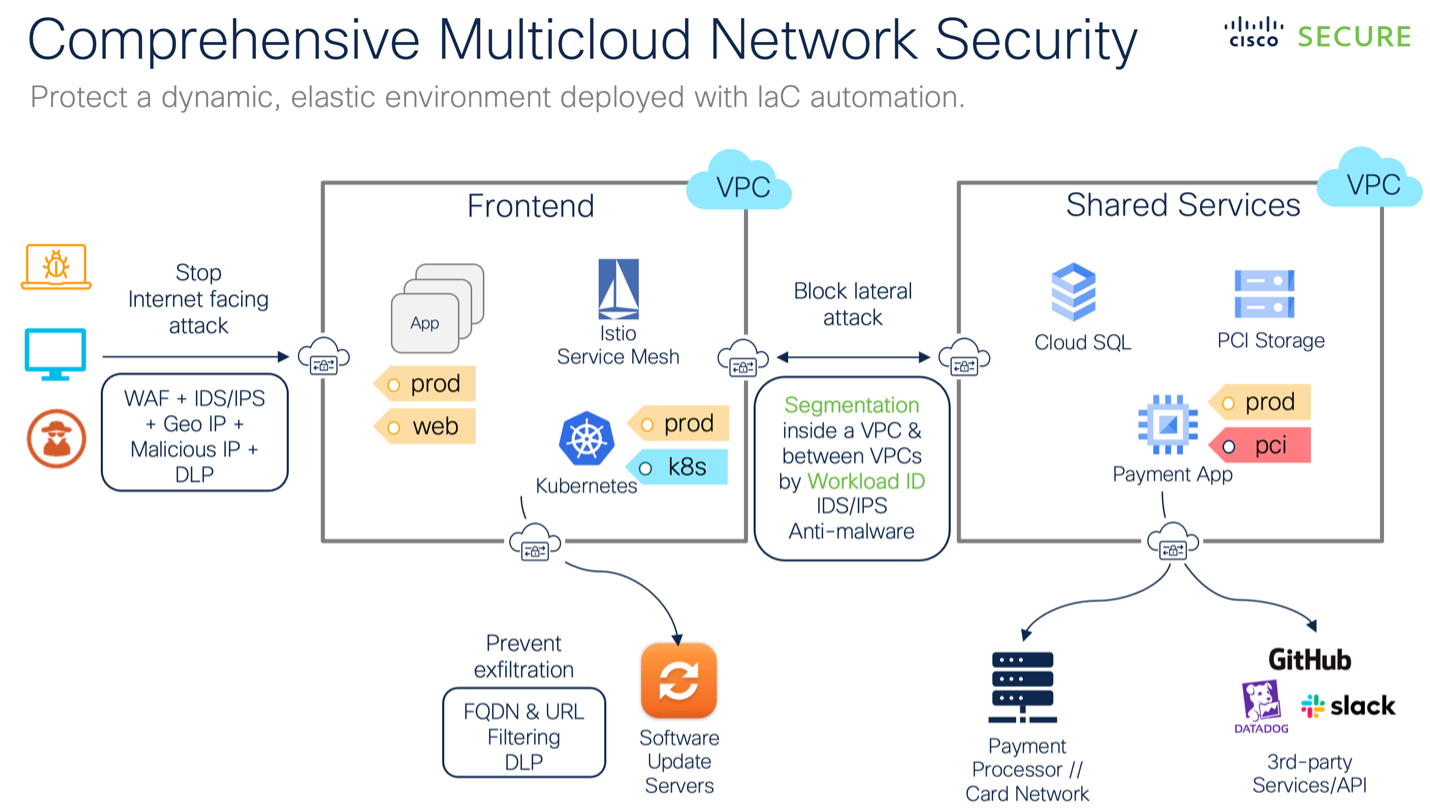
Now that we've explored the importance of penetration testing, let's delve into the broader realm of cybersecurity measures for cloud networks. These measures are the building blocks of a secure digital world with cloud technology. They encompass a wide range of strategies, tools, and practices designed to protect your data and maintain the integrity of your cloud network.
At the heart of these measures is the principle of defense in depth. This approach layers multiple security controls across every aspect of your cloud network. It's akin to having not just a castle wall, but also a moat, watchtowers, and a well-trained garrison. If one layer is breached, others stand ready to thwart the attack.
One of the key measures is access control. This involves managing who can access your cloud network and what they can do within it. It's like having a strict guest list for your castle, ensuring only trusted individuals can enter and limiting their access to sensitive areas.

Another crucial measure is encryption. Encryption scrambles your data into a code that can only be deciphered with a specific key. It's like having a secret language for your castle's documents, unreadable to anyone without the key.
Regular security audits and cloud penetration tests are also essential. These are like regular inspections of your castle's defenses, identifying potential weak spots and reinforcing them.
Finally, staying updated with cloud security updates, such as AWS penetration tests and Google Cloud Platform security bulletins, is crucial. These updates provide valuable insights into the latest threats and defenses, helping you stay one step ahead of cyber adversaries.
Remember, in the world of cloud network security, there is no 'one-size-fits-all' solution. Each cloud network is unique, with its own set of vulnerabilities and threats. Therefore, it's essential to tailor your cybersecurity measures to your specific needs, ensuring a robust and resilient defense against cyber threats.
Keeping Up with Cloud Security Updates
Keeping pace with cloud security updates is akin to a vigilant watchtower guard, always alert to the shifting landscape of potential threats. In the ever-evolving world of cybersecurity, staying updated is not just an option, but a necessity. It's about being proactive, not reactive, in your defense strategy.
Consider these updates as your intelligence reports. They offer valuable insights into the latest vulnerabilities, threats, and defenses in the cloud security realm. Major cloud service providers like Amazon Web Services (AWS) and Google Cloud Platform regularly release security bulletins and updates. These bulletins are your go-to source for understanding the current state of cloud security.
For instance, AWS penetration tests are designed to identify potential weak points in your cloud network. They simulate cyber-attacks to test your defenses, providing a clear picture of your network's resilience. Staying updated with the results of these tests can help you reinforce your defenses and stay ahead of cyber threats.
Similarly, Google Cloud Platform security bulletins provide timely information about security vulnerabilities and updates. They offer guidance on how to mitigate potential risks and enhance your cloud network's security. 
Remember, knowledge is power in the world of cybersecurity. By staying updated with cloud security updates, you're arming yourself with the knowledge to protect your data and maintain a secure digital world with cloud technology. So, keep your eyes on the horizon and your defenses strong, because in the realm of cloud network security, the only constant is change.
Securing Your Data in the Cloud: AWS Penetration Testing
Now that we've explored the importance of staying updated with cloud security bulletins, let's delve deeper into one of the most crucial aspects of cloud network security - AWS Penetration Testing. This practice plays a pivotal role in securing your data in the cloud, and understanding its nuances can greatly enhance your cybersecurity strategy.
AWS Penetration Testing is a simulated cyber-attack on your cloud network, designed to identify potential vulnerabilities. It's like a fire drill for your cloud security, testing your defenses against a controlled blaze before a real inferno strikes. The goal is to uncover weak spots in your security armor and reinforce them before they can be exploited by malicious actors.

During an AWS Penetration Test, cybersecurity experts mimic the tactics, techniques, and procedures (TTPs) used by real-world attackers. They attempt to breach your cloud network's defenses, just as a hacker would. The difference? Their objective is to fortify your security, not compromise it.
Upon completion of the test, you receive a detailed report outlining the vulnerabilities discovered, their potential impact, and recommended remediation strategies. This invaluable information empowers you to enhance your cloud network security, ensuring your data remains secure in the digital world.
So, how often should you conduct AWS Penetration Tests? The answer is simple - regularly. With the ever-changing landscape of cybersecurity threats, routine penetration testing is essential to maintain robust defenses. It's a proactive approach to data protection in the cloud, keeping your network secure and your peace of mind intact.
Remember, understanding network security in the cloud is not a one-time task, but an ongoing process. With AWS Penetration Testing, you're not just securing your data today, but preparing for the threats of tomorrow.



No comments yet. Be the first to share your thoughts!