How Does a Sim Swap Scam Work?
Peeling back the layers of a T-Mobile SIM swap scam can be quite an eye-opener. This modern scam is a crafty blend of social engineering and technical trickery, designed to steal your personal information and gain control over your digital life. So, how does it work?
First, the scammer gathers as much personal information about you as they can. This might include your full name, address, date of birth, and even your social security number. They may get this information from data breaches, phishing emails, or even your public social media profiles.

Once they have enough information, they contact your mobile service provider, in this case, T-Mobile, pretending to be you. They claim that they've lost their SIM card and need a new one. If they can convince the customer service representative that they are indeed you, they can get a new SIM card issued in your name.

The new SIM card is then activated, which deactivates your current SIM. This means that all calls, texts, and data now go to the scammer's phone instead of yours. This includes any two-factor authentication codes sent via SMS, which can be used to access your online accounts.

This is why SIM swap scams are so dangerous. They can give scammers access to your email, social media, and even your bank accounts. Understanding how these scams work is the first step towards protecting yourself and maintaining your digital security.
The Impact of Sim Swap Scams
The impact of SIM swap scams is far-reaching and can be devastating. At the heart of it, these scams are a direct assault on your digital identity. When a scammer successfully executes a T-Mobile SIM swap scam, they essentially hijack your digital life, gaining control over your personal and financial information.
Imagine waking up one day to find that you can't access your email, your social media accounts, or even your bank account. Suddenly, you're locked out of your own digital world, and someone else is pulling the strings. This is the harsh reality for victims of SIM swap scams.

But the damage doesn't stop there. With access to your accounts, scammers can wreak havoc in a number of ways. They can empty your bank accounts, make fraudulent purchases in your name, or even steal your identity to commit more crimes. The financial loss can be staggering, and the emotional toll can be equally devastating.
Moreover, the effects of a SIM swap scam can linger long after the initial incident. Victims may have to spend significant time and resources to regain control of their accounts, repair their credit, and restore their reputation. The recovery process can be long and arduous, further highlighting the severity of these modern scams.
Understanding the impact of SIM swap scams is crucial in emphasizing the importance of prevention and protection. As we delve deeper into the digital age, it's more important than ever to stay vigilant and safeguard our digital lives from such threats.
Protecting Yourself Against Sim Swap Scams
Now that we've explored the potential devastation a T-Mobile SIM swap scam can cause, it's time to focus on how you can shield yourself from such threats. Protecting yourself against SIM swap scams is not only about understanding the risks but also about taking proactive steps to secure your digital identity.
Firstly, it's essential to limit the amount of personal information you share online. Scammers often gather information about their targets through social media and other online platforms. Be mindful of what you post and who has access to your information. 
Secondly, consider adding an extra layer of security to your accounts through two-factor authentication (2FA). However, instead of linking 2FA to your phone number, which can be compromised in a SIM swap, use an authenticator app. These apps generate temporary codes that you can use to verify your identity. 
Another crucial step is to regularly update your passwords and avoid using the same password for multiple accounts. This can limit the damage if one of your accounts is compromised. Remember, a strong password is your first line of defense against cyber threats. 
Lastly, stay vigilant. Regularly monitor your accounts for any suspicious activity and immediately report any irregularities to your service provider. Remember, in the digital world, vigilance is key. 
Protecting yourself against SIM swap scams may seem daunting, but by taking these steps, you can significantly reduce your risk and ensure your digital security.
Cybersecurity Measures for Sim Swap Prevention
As we delve deeper into the realm of digital security, it's crucial to understand that preventing a T-Mobile SIM swap scam requires a multi-faceted approach. It's not just about personal vigilance; it also involves implementing robust cybersecurity measures. Let's explore some of these strategies.
Secure Communication: As a first step, ensure that all your digital communications are secure. This means using encrypted messaging apps and secure email services. Remember, any unsecured communication can be a potential entry point for scammers. 
Network Security: Network security is another vital aspect of SIM swap fraud prevention. Make sure your home and work networks are secure. This includes using strong, unique passwords for your Wi-Fi networks and regularly updating your router's firmware. 
Penetration Testing: Regular penetration testing can help identify potential vulnerabilities in your digital security setup. These tests simulate cyber attacks to assess your system's ability to withstand them. By identifying and addressing these vulnerabilities, you can fortify your defenses against SIM swap scams. 
Secure Key Exchange Protocols: Implementing secure key exchange protocols can add an extra layer of security. These protocols allow the secure exchange of cryptographic keys over a public channel, making it harder for scammers to intercept your communications. 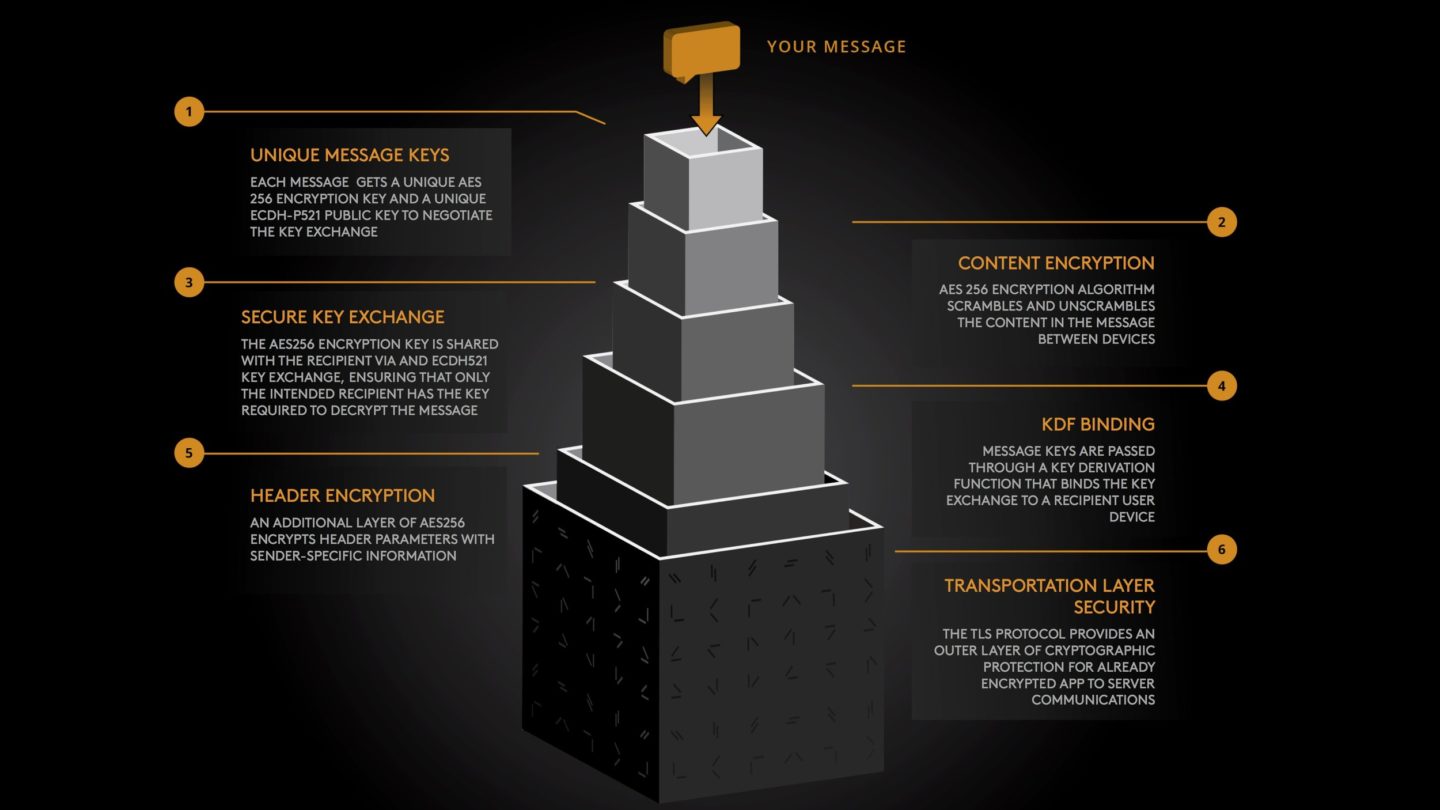
Remember, cybersecurity is a continuous process. It requires regular updates and adjustments to stay ahead of the ever-evolving threats. By implementing these measures, you can significantly enhance your protection against T-Mobile SIM swap scams and other modern digital scams.
How Does a T-Mobile Sim Swap Scam Work?
Let's delve into the mechanics of a T-Mobile Sim Swap Scam. The process begins when a scammer gains access to your personal information. This could be through phishing emails, malware, or even data breaches. They use this information to impersonate you and contact your mobile network provider, in this case, T-Mobile. 
The scammer then convinces T-Mobile's customer service that they are you and have lost or damaged their SIM card. They request a SIM swap, which is a legitimate service provided by T-Mobile for such situations. The provider, believing they are assisting a genuine customer, deactivates your current SIM and activates a new one in the scammer's possession. 
From this point, the scammer can receive all your calls and text messages, including those containing sensitive information such as OTPs (One-Time Passwords) for online banking. This allows them to bypass two-factor authentication and gain access to your financial accounts, social media profiles, and more. 
It's important to note that the scammer doesn't need to be a tech wizard to pull off a SIM swap scam. They primarily rely on social engineering techniques to manipulate customer service representatives. This makes cybersecurity for SIM swap a complex issue that goes beyond just technical solutions.
Understanding how a T-Mobile SIM Swap Scam works is the first step towards protecting yourself from this modern scam. In the following sections, we'll discuss how to prevent SIM swap fraud and enhance your digital security.
Enhancing Network Security Against Sim Swap Scams
Sim swap scams, like the infamous T-Mobile sim swap scam, are a growing concern in the digital world. But, fear not! There are ways to enhance your network security to combat these modern scams. Let's dive in and explore how you can fortify your defenses against these cyber threats.
Two-Factor Authentication (2FA): This is a powerful tool in your cybersecurity arsenal. 2FA requires a second level of authentication to access your accounts, making it harder for scammers to gain control. Even if they manage to swap your SIM, they'll hit a wall when they encounter 2FA. 
Limit Personal Information Sharing: The less information you share online, the less ammunition scammers have to use against you. Be mindful of what you post on social media and other public platforms. 
Secure Your Mobile Carrier Account: Use a unique, complex password for your mobile carrier account. This reduces the chance of your account being hacked, which can lead to a sim swap scam. 
Regular Network Security Audits: Regular audits can help identify any vulnerabilities that might make you susceptible to a sim swap scam. These audits should include penetration testing for sim swap vulnerabilities to ensure your defenses are robust. 
By implementing these strategies, you can significantly enhance your network security against sim swap scams. Remember, prevention is always better than cure when it comes to cybersecurity. Stay vigilant, stay safe!
Penetration Testing for Sim Swap Vulnerabilities
Let's delve deeper into the concept of Penetration Testing for Sim Swap Vulnerabilities. This is a crucial aspect of cybersecurity that involves testing your network's defenses against potential sim swap attacks. It's akin to a fire drill, where you simulate an attack to see how well your defenses hold up.
Penetration testing, or 'pen testing' as it's often called, is a method used by cybersecurity experts to identify vulnerabilities in a system. In the context of sim swap scams, pen testing involves simulating a sim swap attack to see if your network security measures can effectively thwart it.

During a pen test, the tester will attempt to exploit any vulnerabilities they find, just as a scammer would in a real attack. This could involve attempting to gain unauthorized access to your mobile carrier account, trying to bypass two-factor authentication, or even trying to trick you or your employees into revealing sensitive information.
The goal of a pen test is not to cause damage, but to uncover weaknesses. After the test, the tester will provide a detailed report of their findings, including any vulnerabilities they discovered and recommendations for improving your security.
Why is pen testing important? It's simple. You can't fix a problem if you don't know it exists. Pen testing gives you a clear picture of your network's vulnerabilities, allowing you to take proactive steps to strengthen your defenses against sim swap scams.
Remember, in the world of digital security, knowledge is power. The more you understand about potential threats and vulnerabilities, the better equipped you are to prevent them. So, consider penetration testing as your secret weapon in the fight against sim swap scams. It's not about being paranoid; it's about being prepared.

Stay ahead of the game. Stay secure. And remember, the best defense is a good offense. So, don't wait for a sim swap scam to happen before you take action. Start your penetration testing today and fortify your defenses against this modern scam.
Preventing Sim Swap Fraud: Tips and Best Practices
Preventing Sim Swap Fraud is not a Herculean task if you follow some simple, yet effective, tips and best practices. Let's delve into them.
1. Safeguard Personal Information: The cornerstone of any cybersecurity strategy is the protection of personal information. Be wary of unsolicited calls or messages asking for personal details. Remember, T-Mobile or any other service provider will never ask for sensitive information over a call or text. 
2. Enable Multi-Factor Authentication (MFA): MFA provides an additional layer of security by requiring more than one method of authentication. It can significantly reduce the risk of a successful sim swap scam. 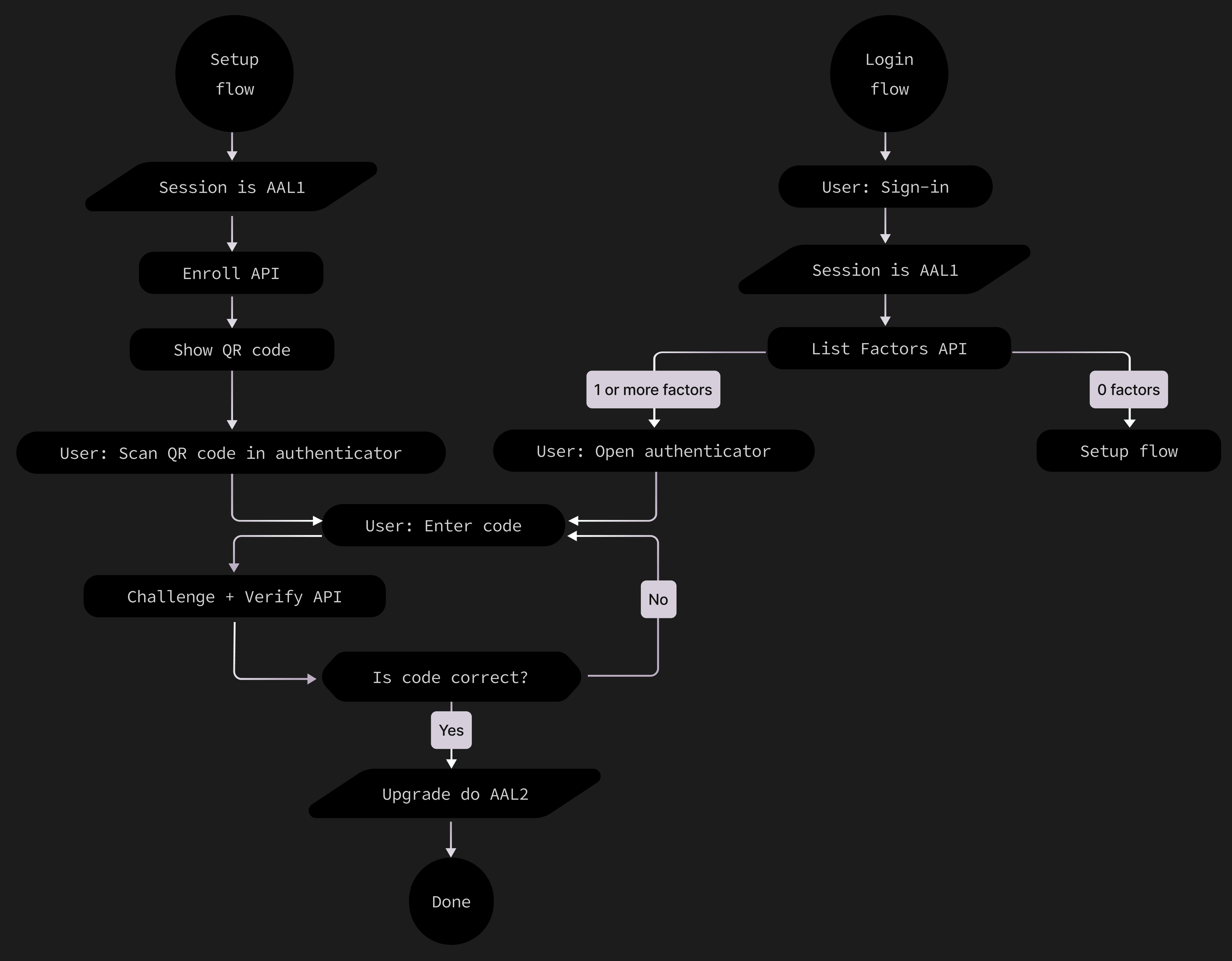
3. Regularly Monitor Accounts: Keep a close eye on your bank accounts, credit cards, and other financial services. Any unusual activity could be a sign of sim swap fraud. 
4. Limit Sharing of Phone Number: Your phone number is a key piece of information for sim swap scammers. Limit its exposure by only sharing it when absolutely necessary. 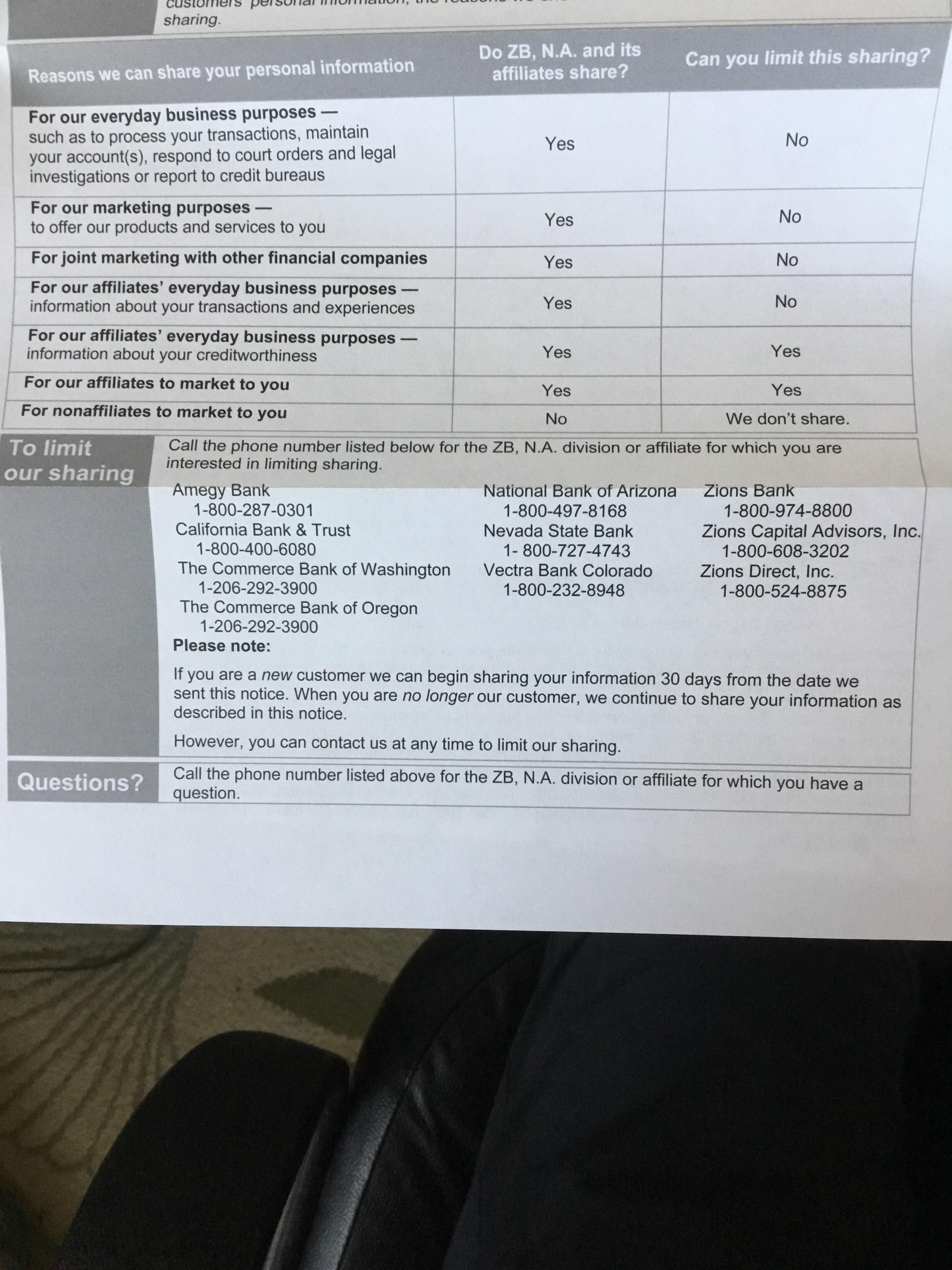
5. Contact Your Service Provider: If you suspect a sim swap scam, immediately contact your service provider. They can take necessary steps to secure your account. 
Remember, understanding sim swap scams and taking proactive steps towards prevention is your best defense against this modern scam. Stay vigilant, stay safe. 
What is a T-Mobile Sim Swap?
Let's dive into the world of modern scams and understand what a T-Mobile Sim Swap is. This is a type of fraud that is rapidly gaining popularity among cybercriminals. It's a sophisticated scam that targets your mobile device, specifically your SIM card, which is the heart of your digital identity.
So, what exactly is a T-Mobile Sim Swap? In simple terms, it's a scam where a fraudster tricks your mobile network provider into transferring (or swapping) your mobile number to a new SIM card that the scammer controls. This is why it's also known as a Sim Swap Scam.
Once the scammer has control over your mobile number, they can potentially gain access to a wealth of information and services linked to that number. This includes your email accounts, social media profiles, banking services, and more. Essentially, the scammer can impersonate you digitally, leading to a multitude of potential cybersecurity threats.
It's important to note that while we're focusing on T-Mobile here, this type of scam can happen on any network. The name 'T-Mobile Sim Swap' is often used because T-Mobile is one of the largest mobile network providers, and so, a significant number of these scams occur on their network.
Understanding the mechanics of a T-Mobile Sim Swap is the first step towards protecting yourself from this modern scam. Stay tuned as we delve deeper into how this scam works, its impact on cybersecurity, and how you can protect yourself.

The Impact of Sim Swap Scams on Cybersecurity
The impact of SIM swap scams on cybersecurity is profound and far-reaching. The T-Mobile SIM swap scam is a stark reminder of the vulnerabilities that exist in our digital world. It's not just about losing control over your phone; it's about the potential havoc that can be wreaked on your digital life.
Imagine waking up one day to find out that your email has been hacked, your social media accounts compromised, and your bank account drained. This is the harsh reality of a successful SIM swap scam. The scammer, armed with your personal information and control over your phone number, can bypass two-factor authentication, a security measure that is supposed to add an extra layer of protection to your accounts.
From a cybersecurity perspective, SIM swap scams expose a critical flaw in our reliance on mobile phones as a form of identity verification. It highlights the need for stronger and more secure methods of authentication. 
Furthermore, these scams also underscore the importance of protecting personal information. In the hands of a scammer, your personal details become a weapon that can be used against you. It's a stark reminder that in the digital age, information is power.
So, what does this mean for the future of cybersecurity? It means that we need to rethink our approach to digital security. We need to move beyond passwords and two-factor authentication via SMS. We need to embrace more secure methods, such as biometric authentication and hardware tokens.
In the fight against SIM swap scams, we need to be proactive, not reactive. We need to understand the risks, take steps to mitigate them, and stay one step ahead of the scammers. After all, cybersecurity is not just about protecting our devices; it's about protecting our digital lives.
Preventing Sim Swap Scams: Best Practices
Stepping into the realm of prevention, let's delve into the best practices to safeguard against the T-Mobile SIM swap scam and similar threats. The key to prevention lies in a multi-layered approach that combines personal vigilance, enhanced security measures, and a deep understanding of how these scams operate.
1. Guard Your Personal Information: Your personal information is the key that unlocks the door to a SIM swap scam. Be wary of unsolicited calls, emails, or messages asking for your personal details. Remember, your service provider will never ask for sensitive information over a call or text. 
2. Enable Additional Security Measures: Most service providers, including T-Mobile, offer additional security measures such as a unique PIN or passcode that must be provided before any changes can be made to your account. This adds an extra layer of security, making it harder for scammers to execute a SIM swap. 
3. Regularly Monitor Your Accounts: Regularly check your bank accounts, credit card statements, and other sensitive accounts for any unusual activity. Early detection can help prevent a scam from escalating. 
4. Be Cautious of Phishing Attempts: Scammers often use phishing emails or messages to trick you into revealing your personal information. Be cautious of any communication that prompts you to click on a link or provide your details. 
5. Use Two-Factor Authentication: While SIM swap scams can bypass SMS-based two-factor authentication, there are other forms that remain secure. Consider using app-based two-factor authentication or hardware tokens for an added layer of protection. 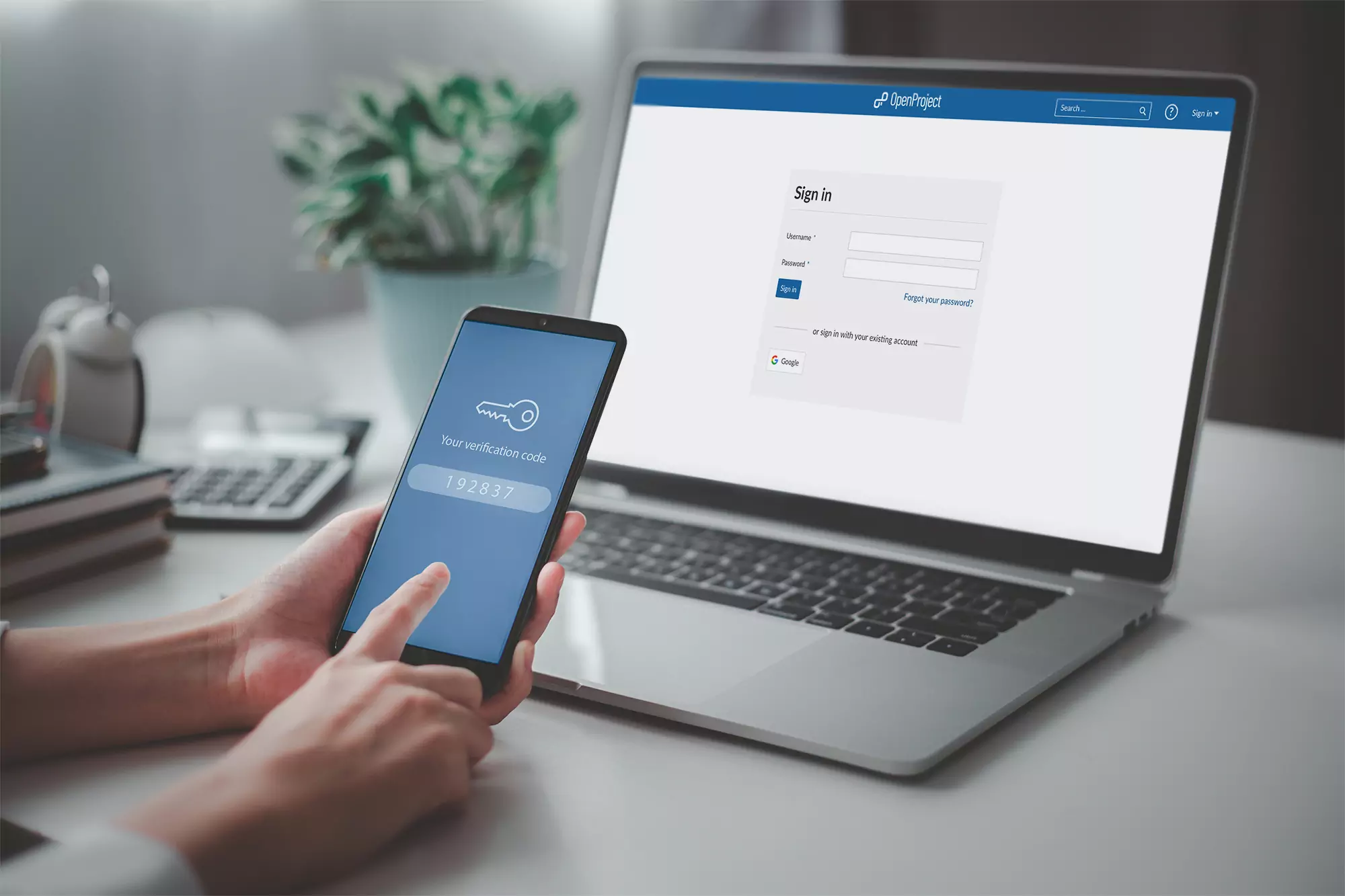
Preventing SIM swap scams requires a proactive approach to digital security. By following these best practices, you can significantly reduce your risk and stay one step ahead of the scammers.
Network Security Measures Against Sim Swap Scams
Now that we've covered some personal best practices, let's shift our focus to the broader network security measures against SIM swap scams. These measures are crucial in providing a robust defense against the T-Mobile SIM swap scam and similar threats.
Firstly, service providers like T-Mobile need to implement advanced authentication protocols. This could include biometric verification or behavioral analytics, which track typical user behavior to identify any anomalies. For instance, a sudden change in the location or device used to access the account could raise a red flag. 
Secondly, real-time monitoring and alert systems can play a pivotal role in detecting and preventing SIM swap scams. These systems can quickly identify suspicious activity, such as multiple failed login attempts or unusual account changes, and alert both the user and the service provider. 
Another important measure is penetration testing. This involves ethical hackers trying to exploit vulnerabilities in the network to identify potential security weaknesses. Once these weaknesses are identified, they can be addressed to fortify the network against SIM swap scams. 
Lastly, service providers should implement strict protocols for SIM card changes. This could include requiring physical presence at a store or additional verification steps before a SIM card can be swapped. 
In essence, network security measures against SIM swap scams involve a combination of advanced authentication, real-time monitoring, penetration testing, and strict SIM card change protocols. By implementing these measures, service providers can significantly enhance their defense against this modern scam.
Educating Users: Understanding Sim Swap Scams
Now that we've explored the technical side of sim swap scams, let's shift our focus to the user's perspective in our section: Educating Users: Understanding Sim Swap Scams. The key to preventing these scams lies not only in robust network security measures but also in informed users who can recognize and avoid potential threats.
Sim swap scams, such as the T-Mobile sim swap scam, are a type of identity theft where a scammer convinces your mobile carrier to switch your phone number over to a sim card they control. Once they have your number, they can bypass security measures like two-factor authentication to gain access to your personal and financial accounts.
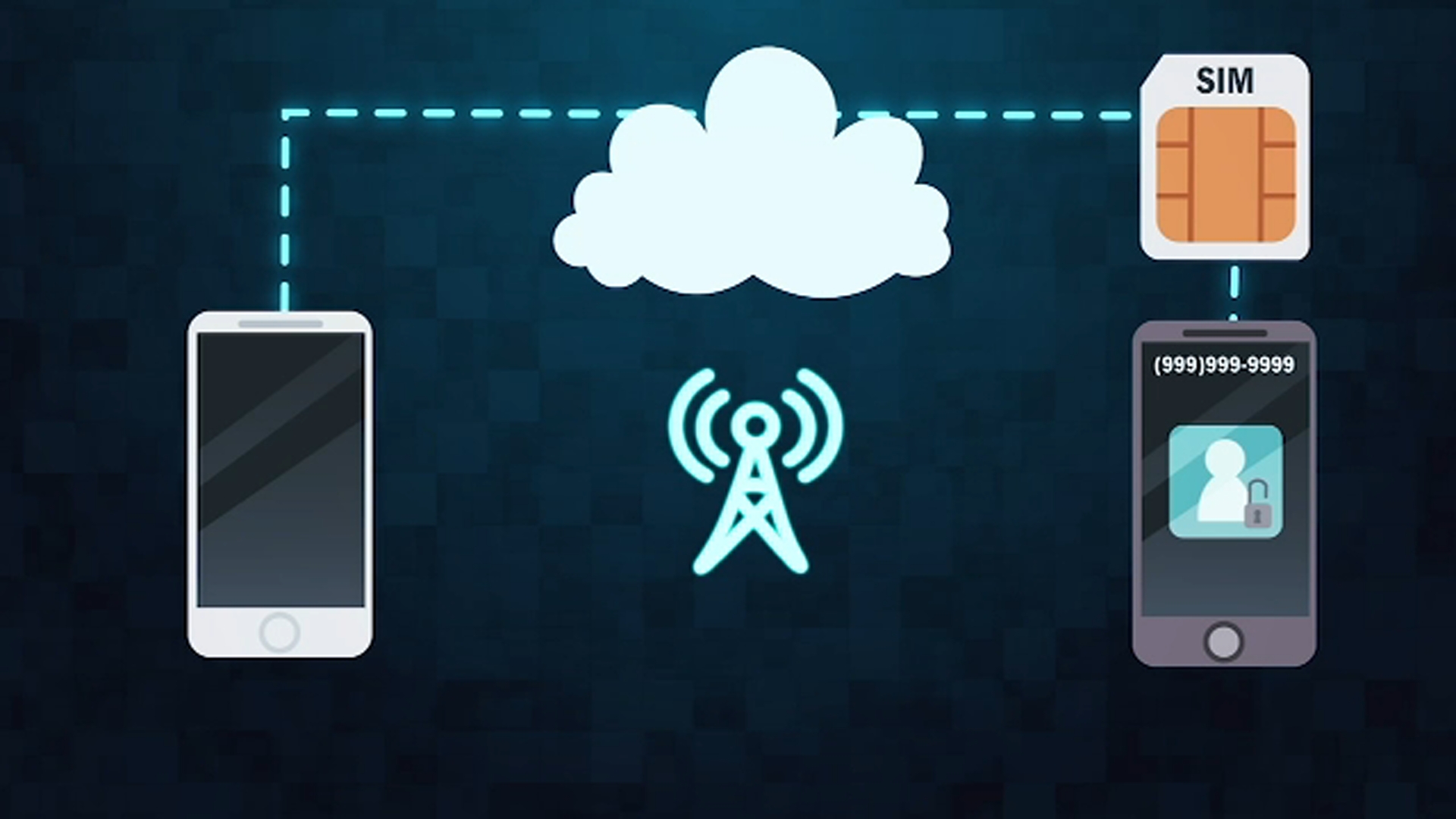
Understanding how these scams work is the first step to preventing them. Scammers often start by gathering as much personal information about you as they can. They might get this information from data breaches, social media, or even through phishing emails. Once they have enough information, they contact your mobile carrier, pretending to be you. They'll claim they've lost their phone or that it's been stolen, and ask the carrier to transfer your number to a new sim card.
So, how can you protect yourself? First, be wary of unsolicited calls or messages asking for personal information. Never give out sensitive information unless you're sure of who you're dealing with. Second, consider adding extra security measures to your mobile account, like a unique pin or password. This can make it harder for scammers to impersonate you.

Remember, cybersecurity isn't just about having the right systems in place. It's also about understanding the threats you face and knowing how to avoid them. By educating yourself about sim swap scams, you're taking a crucial step towards protecting your digital identity.
Digital Security and Sim Swap: Protecting Your Identity
Stepping into the realm of Digital Security and Sim Swap: Protecting Your Identity, it's essential to grasp the importance of safeguarding your digital persona. The T-Mobile sim swap scam, like other sim swap scams, is a stark reminder of the modern threats we face in our increasingly digital world.
One of the most effective ways to shield yourself from sim swap fraud is to fortify your digital security. This involves a blend of vigilance, knowledge, and the use of advanced security tools. 
Firstly, always keep your personal information private. Be cautious about what you share online, especially on social media. Scammers often use the information you post publicly to impersonate you. Remember, the less information they have, the harder it is for them to trick your mobile carrier.
Secondly, make use of the security features offered by your mobile carrier and financial institutions. This could include biometric authentication, unique pins, or security questions. 
Lastly, consider using a password manager. These tools can generate and store complex passwords, making it harder for scammers to crack your accounts even if they manage to perform a sim swap. 
Remember, the goal of a sim swap scam is to steal your identity. By bolstering your digital security, you're not just protecting your phone number - you're safeguarding your entire digital identity. As the saying goes, prevention is better than cure. In the world of cybersecurity, this couldn't be more true.







No comments yet. Be the first to share your thoughts!