Cybersecurity's Humble Beginnings: From Obscure to Essential🌅
Picture this: it's the late 1970s, and the world is on the brink of a digital revolution. Amongst the buzz and whir of the first mainframe computers, a new breed of guardians emerges, tasked with a mission as nascent as the field itself - cybersecurity. But what was the initial purpose of these digital world security pioneers? And how has the cybersecurity evolution unfolded?
Well, let's rewind a bit. The earliest cybersecurity measures were akin to digital walls, designed to keep out unwanted intruders. The challenge? Anticipating every possible breach in a rapidly evolving landscape. And yet, these early efforts laid the foundation for the complex, multi-layered security systems we see today.
So, is the future of cybersecurity a daunting labyrinth or a misunderstood art? Are the cybersecurity challenges we face today simply growing pains of an industry in constant flux? Stay with us as we journey through the evolution of cybersecurity, dispel some common misconceptions, and explore the potential of this crucial field.
Let's take a step back in time and trace the significant milestones that have shaped the cybersecurity landscape as we know it today.
These milestones highlight the rapid progression and constant adaptation required in the field of cybersecurity. As we move forward, let's take a closer look at the early days of cybersecurity, illustrated by vintage computer systems.

The Digital Arms Race: Cyber Threats vs Cybersecurity🔒
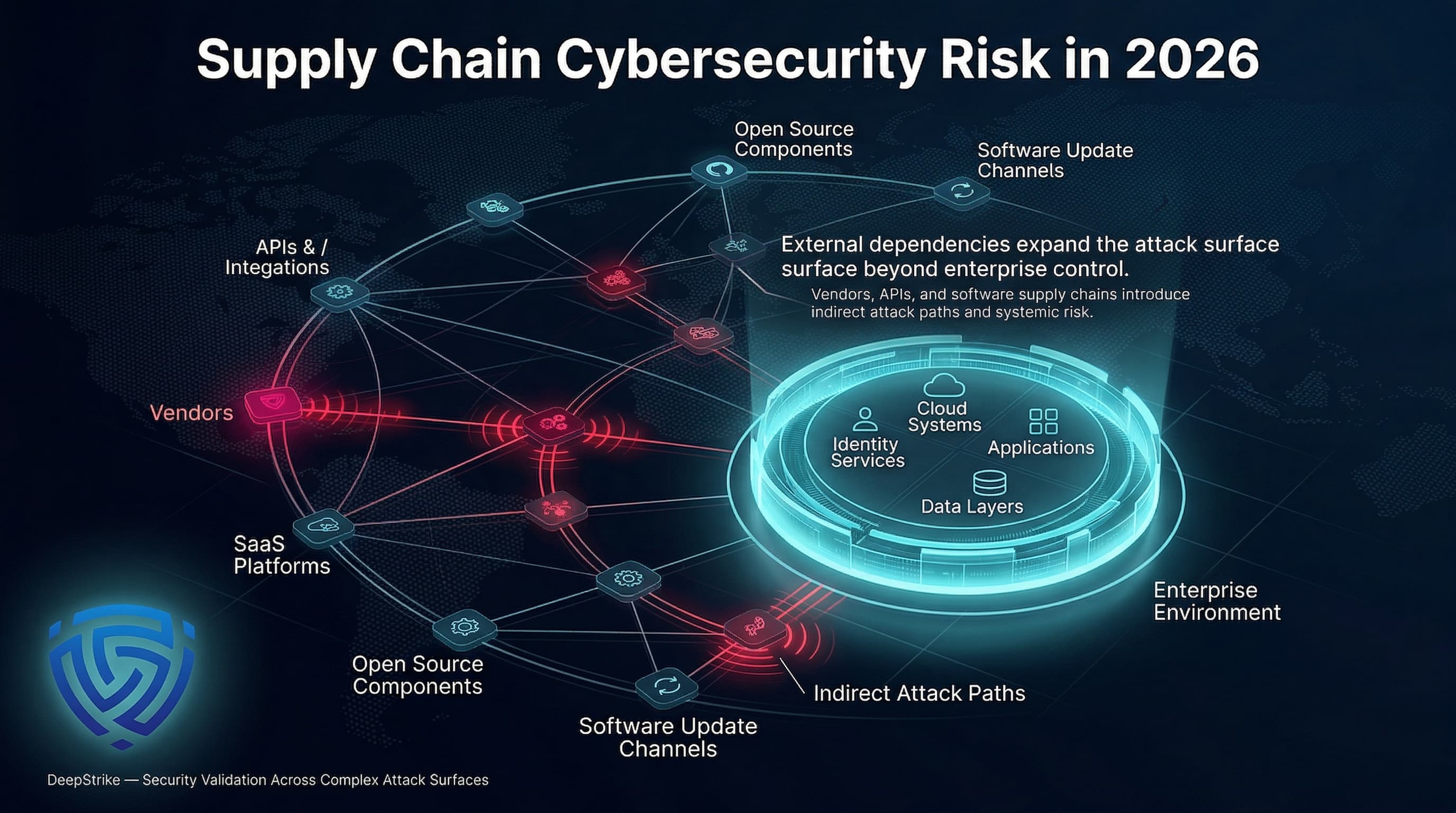
Picture this: you're in a bustling city, the digital world, where everything from your coffee maker to your car is connected to the internet. Sounds convenient, right? But as our cities grow, so do the shadows. The expansion of cyber threats, a dark underbelly to our shining digital world, has been in lockstep with the advancement of technology.
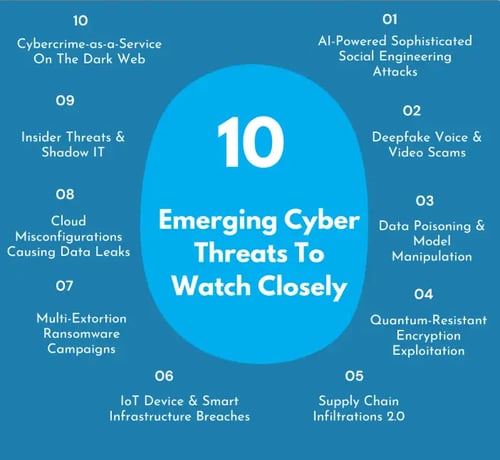
Every new device we connect, every new app we download, presents fresh cybersecurity challenges. The threats are no longer just viruses or worms. We're dealing with sophisticated ransomware, stealthy spyware, and relentless phishing attacks. The digital world security is like a game of chess, with every move countered by a cunning adversary.
But fear not! Cybersecurity has not been sitting idle. It has adapted, evolved, and grown stronger. It's a ceaseless dance, a thrilling chase in the labyrinth of codes and algorithms. Understanding cybersecurity isn't just about knowing what a firewall does. It's about comprehending this ever-evolving dance, understanding the cybersecurity challenge of keeping pace with the threats, and appreciating the tireless guardians who keep our digital world secure.
Trends in Cyber Threats Over the Years
Decoding Cybersecurity: Is It a Monster or a Maze?🔍
Is cybersecurity a labyrinth of complex codes or a misunderstood hero of our digital world? This is where the lines blur. The journey into the heart of cybersecurity reveals an intricate weave of challenges and misconceptions. While it's true that the field is riddled with complex algorithms and high-level tech, it's also a fact that the digital world security we enjoy today is a product of this very complexity.
One common misconception is that cybersecurity is an impenetrable fortress, reserved for the tech-savvy elite. The truth? It's a dynamic field that's constantly evolving to protect us from threats, both seen and unseen. The cybersecurity challenge isn't just about understanding complex codes, but about staying a step ahead of cybercriminals who are becoming increasingly sophisticated.
So, is the future of cybersecurity a tale of escalating difficulty or increasing understanding? Perhaps it's both. As we navigate the evolving landscape of cybersecurity, we must also debunk the myths that shroud it. After all, isn't understanding the first step to mastering any challenge?
Understanding Cybersecurity: Myths and Facts
Test your knowledge about the evolution of cybersecurity and common misconceptions around it.
Learn more about 🔒 Understanding Cybersecurity: Myths and Facts Quiz or discover other HackerDesk quizzes.
Demystifying Cybersecurity: Making It User-Friendly for All🌐
So, how do we navigate this labyrinth of the cybersecurity challenge? It's not as hard as one might think. The key is understanding. Just as we've learned to lock our doors at night, we need to learn the basics of digital world security. But where do we start?
Well, the first step is breaking down the cybersecurity misconceptions. Many people believe cybersecurity is a complex beast, only understandable by tech wizards, but that's far from the truth. In reality, it's a language we can all learn. It's about understanding the risks, knowing how to spot them, and taking the right precautions.
Why is this important? Because as the future of cybersecurity evolves, we all become front-line soldiers in this digital war. The more people understand about cybersecurity, the stronger our collective defense becomes. It's a team effort, and every single one of us has a part to play. So, are you ready to join the ranks?
To make cybersecurity more accessible, let's delve into some basic practices that everyone can adopt. These steps are simple yet effective in enhancing your digital security.
Learn more about 🔒 Your Cybersecurity Starter Kit: A Basic Guide or discover other HackerDesk guides.
By adopting these basic cybersecurity practices, you're taking a significant step towards safeguarding your digital life. Now, as we look towards the future of cybersecurity, let's explore the upcoming developments and trends in this field.
Cybersecurity 2.0: What Lies Ahead in the Digital Frontier?🚀
As we navigate the exciting labyrinth of the digital world, the future of cybersecurity stands as an ever-evolving enigma. Will it scale the daunting walls of cybersecurity challenges, or will it succumb to the labyrinth's deceptive simplicity? The answer lies not in the complexity of the challenge, but in our understanding of it.
Imagine a world where cybersecurity isn't a misunderstood beast, but a trusted guardian. A world where the evolution of cybersecurity is not perceived as a hard-to-climb mountain, but an adventurous journey that we're all part of. A world where the digital world security doesn't keep us awake at night, but assures us of a safe tomorrow. Doesn't that sound like a world you'd like to live in?
Well, the good news is, we're already on our way. The future of cybersecurity is not just about advanced algorithms and high-tech firewalls. It's about making cybersecurity more accessible, more understandable, and more human. It's about debunking cybersecurity misconceptions and embracing the challenge. So, are you ready to be part of this exciting journey?
What do you think will be the most significant development in cybersecurity in the future?
As we look ahead, we can't help but wonder about the future of cybersecurity. What do you believe will be the most impactful development in this field?
Final Bytes: Reflecting on Cybersecurity's Journey and Importance💡
So, is cybersecurity really a labyrinth, or have we just been holding the map upside down? The journey we've traced from the dawn of cybersecurity to its current landscape and potential future, paints a vivid picture of a discipline often misunderstood and oversimplified. It's a never-ending chase between digital world security and the miscreants who threaten it—a thrilling cat-and-mouse game that's as complex as it is crucial.
As we peek into the future of cybersecurity, it's clear that the cybersecurity challenge won't be slowing down anytime soon. The digital world is in constant flux, cyber threats mutating and evolving in tandem. But perhaps, instead of viewing this as a terrifying prospect, we should see it as a call to arms, an opportunity for innovation and growth.
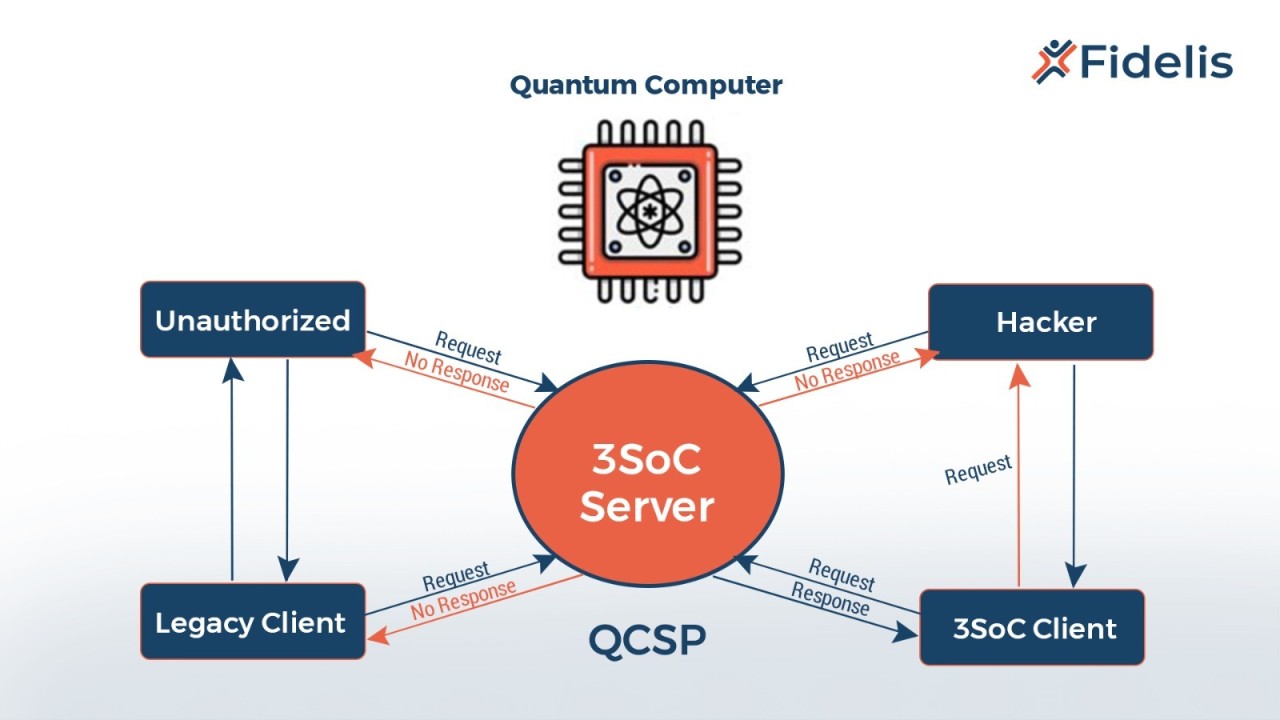
What if the real challenge isn’t the threats themselves, but our collective understanding—or more accurately—the misunderstandings about cybersecurity? An intriguing thought to ponder, isn't it? Maybe the next quantum leap in cybersecurity isn't a groundbreaking technology or a new algorithm, but rather a shift in perception, a widespread enlightenment. As we say in the tech world, to be continued...









No comments yet. Be the first to share your thoughts!