In an era where cyber threats are not just prevalent but also sophisticated and insidious, the traditional castle-and-moat approach to network security is being reevaluated. Enter the Zero Trust Model, a paradigm shift in cybersecurity that assumes breaches are not just possible, they're inevitable. This model advocates for continuous verification of trustworthiness across every network segment and user interaction. As we unpack the layers of Zero Trust, it's essential to understand that it's not merely a product you can purchase; it's a comprehensive strategy that encompasses various aspects of your IT environment.
Understanding the Zero Trust Model
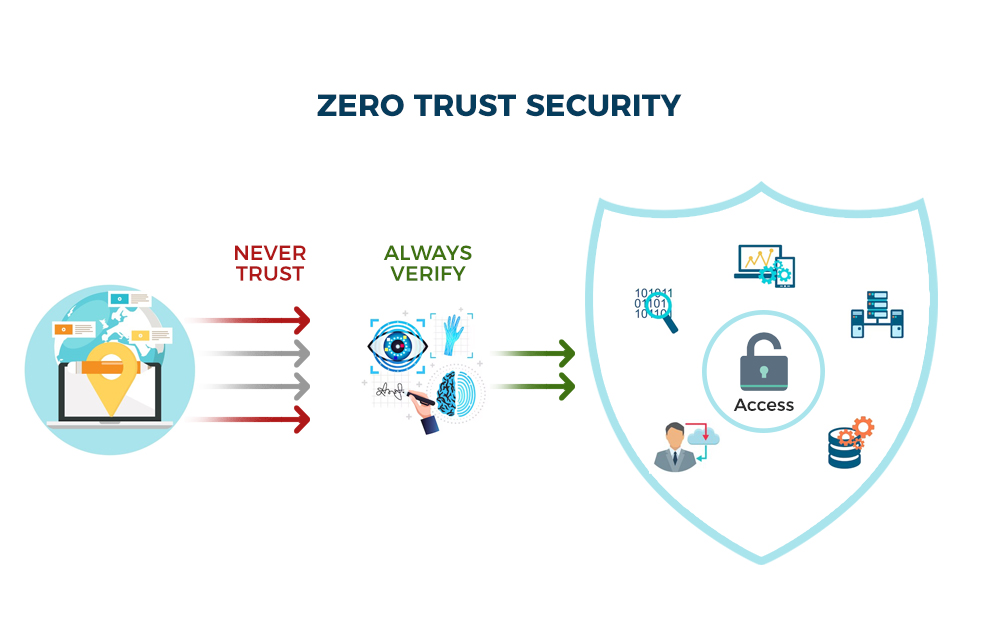
The core principle of the Zero Trust Model is "never trust, always verify." Unlike conventional security models that enforce perimeter-based defenses, Zero Trust operates on the premise that trust is a vulnerability. In practice, this means authentication and authorization are required not just at entry points but throughout the network. Users—whether inside or outside the organization's network—must prove their legitimacy each time they attempt to access resources.
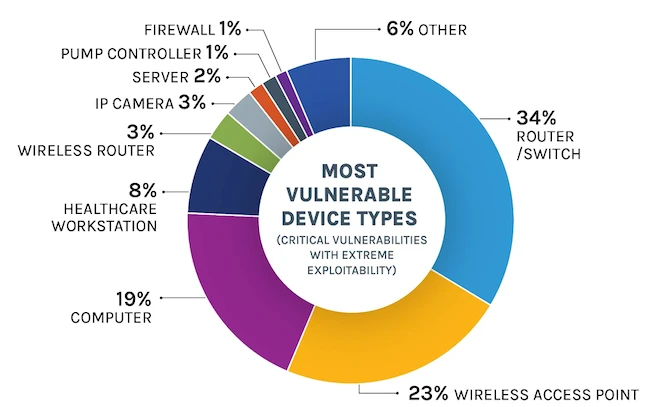
This model is built upon three foundational elements: secure access, least privilege, and micro-segmentation. Secure access ensures that only authenticated and authorized users and devices can access applications and data. The least privilege principle restricts user access rights to only what's needed to perform their job functions, thereby minimizing the attack surface. Micro-segmentation divides the network into secure zones, allowing organizations to tailor security settings to different types of traffic and create policies that limit network propagation by attackers.
The Drivers Behind Adopting Zero Trust
The digital transformation has obliterated what used to be a clear perimeter. With cloud services, mobile workforces, and BYOD (Bring Your Own Device) policies becoming standard practice in businesses, traditional security measures fall short. The rise of sophisticated cyber-attacks like ransomware and state-sponsored hacking further underscores the need for a robust model like Zero Trust. The recent high-profile breaches serve as stark reminders that reliance on outdated security practices can have dire consequences.
Why Adopt Zero Trust?
- Increase in Remote Work - With more employees working from home, traditional network perimeters have dissolved, necessitating a shift to security models that don't rely on a trusted internal network.

- Advanced Persistent Threats - The sophistication of cyber-attacks requires a security approach that continuously validates every stage of digital interaction.

- Cloud Adoption - As businesses move to the cloud, they need security measures that protect assets outside the traditional network boundary.

- Regulatory Compliance - Increasingly stringent data protection laws mandate more robust security measures, making Zero Trust an attractive compliance solution.

- Insider Threats - The acknowledgment that threats can originate from within an organization has led to the understanding that trust is a vulnerability.

- Supply Chain Attacks - Recent high-profile breaches through supply chains have highlighted the need for stringent security checks irrespective of the source.

- IoT and BYOD Policies - The proliferation of devices and bring-your-own-device practices adds complexity and risk, which Zero Trust can help mitigate.
- Cost of Data Breaches - As the financial and reputational repercussions of data breaches grow, so does the need for a security model that minimizes these risks.

- Scalability and Flexibility - Zero Trust architecture allows organizations to scale securely and adapt quickly to changes in the threat landscape.

- Visibility and Control - Zero Trust provides granular insights and control over who accesses what within the network, enhancing overall security posture.
Moreover, regulatory compliance requirements are pushing companies toward more proactive security measures. Standards such as GDPR (General Data Protection Regulation) and HIPAA (Health Insurance Portability and Accountability Act) demand stringent data protection protocols which align well with Zero Trust principles.
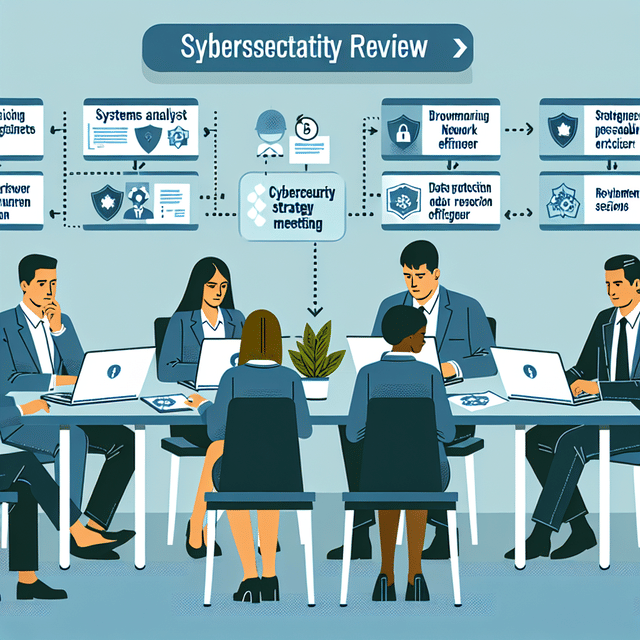
The Architecture of a Zero Trust Network
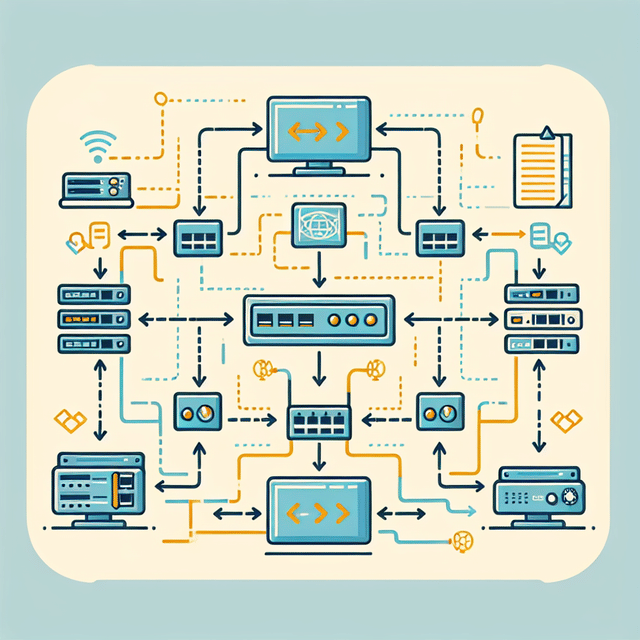
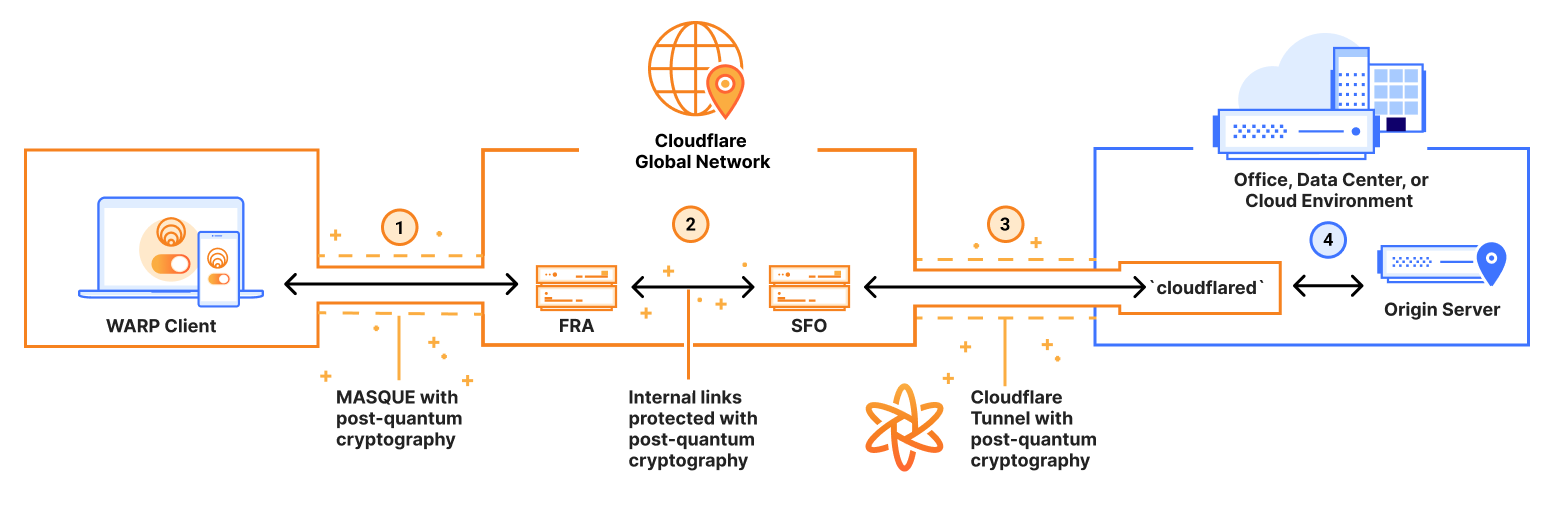
Achieving a Zero Trust architecture involves several key components working in concert. First among these is identity verification, which often involves multi-factor authentication (MFA) to ensure that users are who they claim to be. Next comes device authentication; before granting access, systems must check whether devices meet specific security criteria.
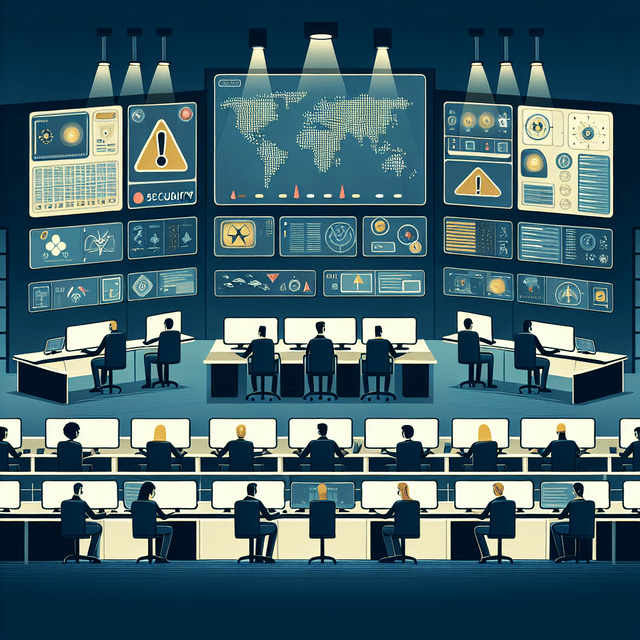
Network security solutions like next-generation firewalls (NGFWs), intrusion prevention systems (IPS), and advanced threat protection (ATP) play critical roles in inspecting and logging traffic for suspicious activity within a Zero Trust framework. Additionally, employing cloud network security practices is crucial given most organizations' reliance on cloud environments today.
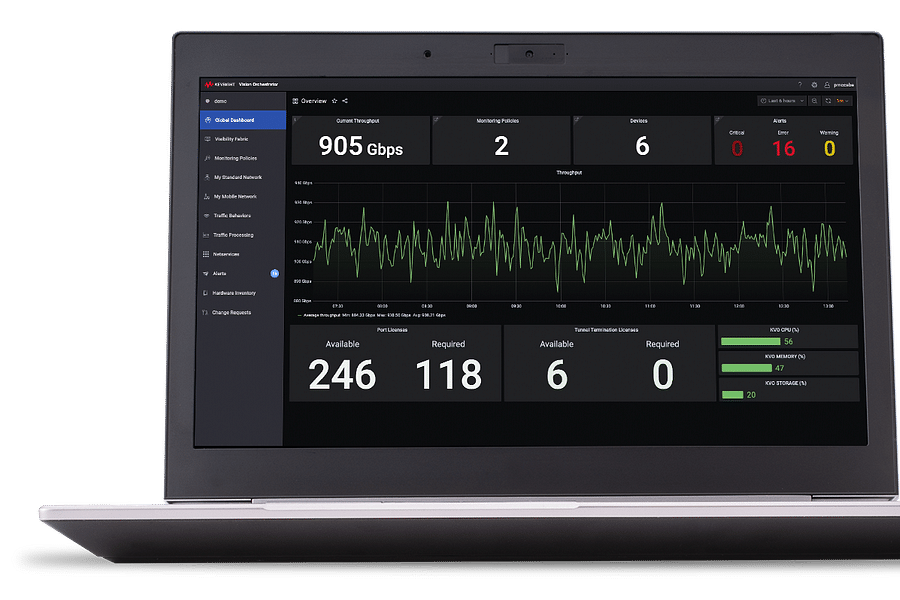
To implement these strategies effectively requires comprehensive visibility across all computing environments—cloud, on-premises, or hybrid—along with sophisticated analytics tools capable of detecting anomalies indicative of cyber threats.
Traffic Flow Analysis in a Zero Trust Network
Migrating to a Zero Trust Network: Challenges & Considerations
Moving an organization toward a Zero Trust framework isn't without its challenges; it requires significant changes in both technology infrastructure and organizational mindset. Legacy systems often lack compatibility with modern security protocols necessary for implementing Zero Trust principles effectively.
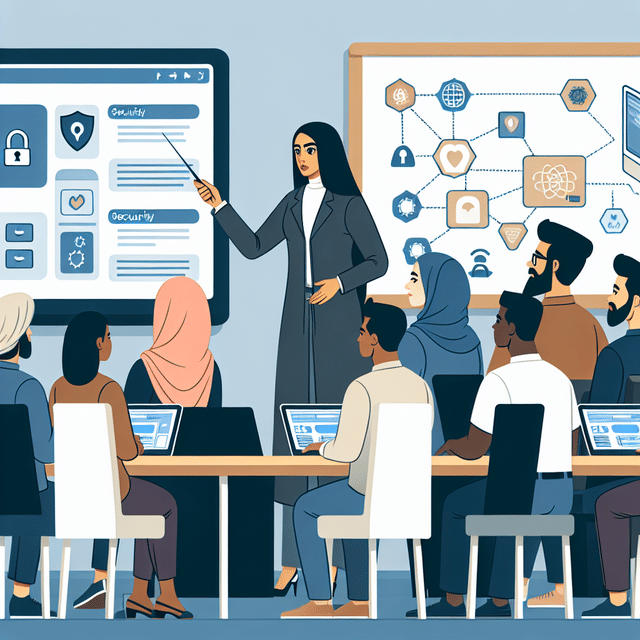
Cultural resistance can also be an obstacle as employees may view these new stringent measures as hindrances rather than protective mechanisms. Therefore, education around cybersecurity risks becomes vital in fostering an environment where everyone understands their role in maintaining organizational security.
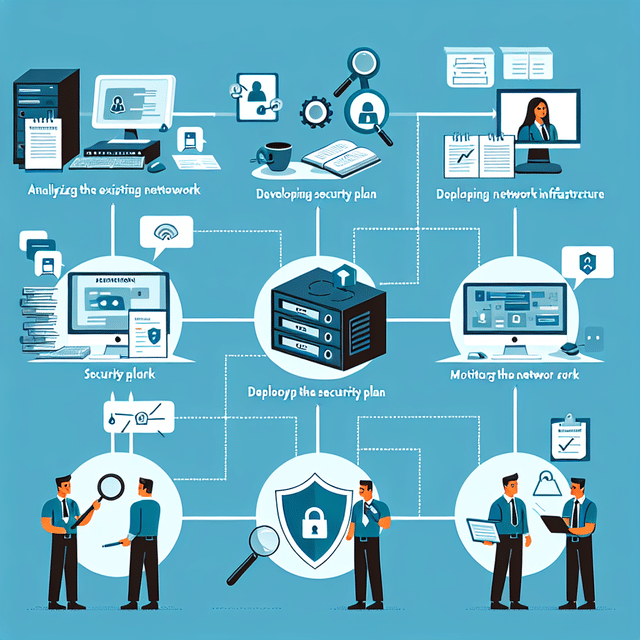
[step_by_step_guide: Steps for successfully transitioning to a Zero Trust network]In addition to technical hurdles and culture change management, there's also the consideration of cost versus benefit analysis when migrating to such an architecture. Decision-makers must weigh potential disruptions against long-term gains in cybersecurity posture.
To learn more about securing your network through various methods including those within the scope of Zero Trust architecture, visit our comprehensive guides on securing your network step-by-step, or take our quiz on Cloud vs Network Security: What Does Your Business Need Most?. For those interested in understanding how this applies specifically to critical infrastructure protection, we offer another engaging quiz at Securing Critical Infrastructure & Preventing Cyber Attacks Quiz.
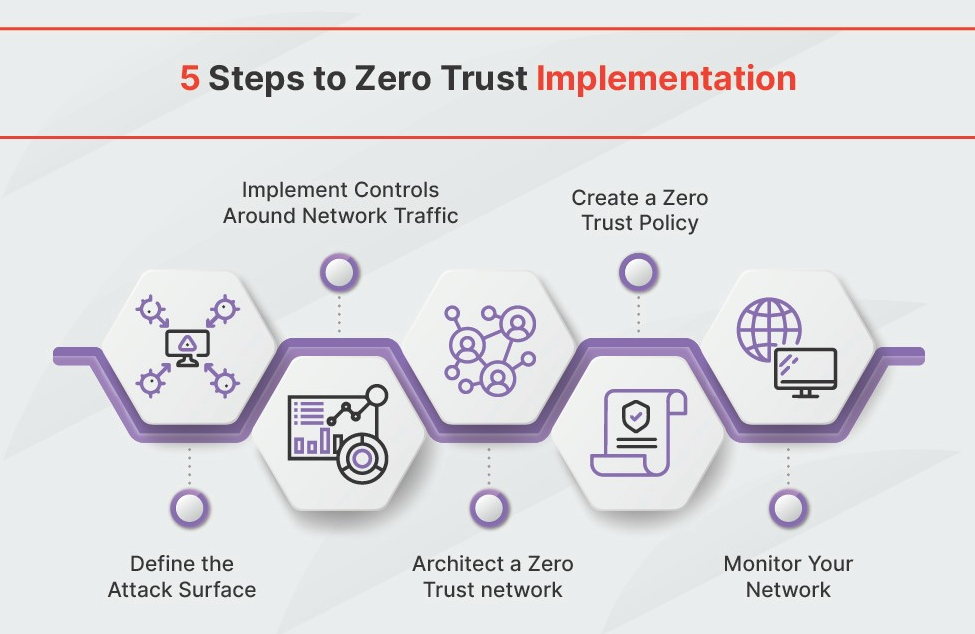
Implementing Zero Trust: Practical Steps
The shift to a Zero Trust model requires a strategic approach that encompasses various aspects of your network and security protocols. The first step is to identify sensitive data and where it resides. Once identified, enforce strict access controls and continuously monitor data movement within your network. It's not just about having the right tools; it's about having the right mindset that assumes breach and verifies each transaction.
Network segmentation is another critical component of Zero Trust. By dividing your network into smaller, more manageable sections, you can limit an attacker's movement within your system, should they gain access. This method not only helps in containing potential breaches but also in monitoring traffic flow more effectively.
Moreover, adopting multi-factor authentication (MFA) across all user accounts significantly enhances security. MFA ensures that even if a password is compromised, unauthorized users are still kept at bay.
Understanding Multi-Factor Authentication in Zero Trust Security
As the Zero Trust model becomes increasingly relevant in the world of cybersecurity, understanding its components, such as Multi-Factor Authentication (MFA), is essential. Test your knowledge on how MFA contributes to the Zero Trust framework and its role in enhancing network security.
Zero Trust and Regulatory Compliance
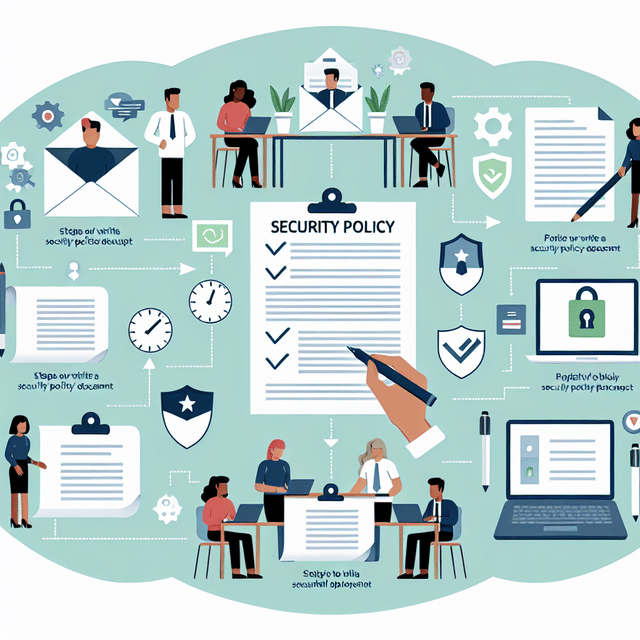
In today's digital landscape, adhering to regulatory standards is paramount. The Zero Trust framework aligns well with many compliance requirements due to its stringent access controls and monitoring capabilities. For instance, regulations such as GDPR, HIPAA, and PCI-DSS all require protection of sensitive data, which is a fundamental principle of Zero Trust.
- Understanding Security Threats
- Securing Your Network Step by Step
- Securing Enterprise Networks
- Insights into Managed Network Security
- What Is Cloud Network Security?
To maintain compliance while implementing Zero Trust principles, organizations must document their policies clearly and train their staff accordingly. Regular audits should be conducted to ensure that the controls are effective and meet the necessary standards.
The Future of Cybersecurity with Zero Trust
The evolution of cybersecurity threats continues to outpace traditional security measures. As such, the future of cybersecurity hinges on proactive models like Zero Trust that can adapt to the ever-changing threat landscape. With advancements in artificial intelligence (AI) and machine learning (ML), Zero Trust systems are becoming smarter and more capable of detecting anomalies in real-time.
"In cybersecurity, trust is not a strategy; it's a vulnerability."
This paradigm shift towards AI-driven security solutions will further empower organizations to anticipate threats rather than react to them post-compromise. It's essential for businesses to stay informed on these developments as they consider enhancing their own security postures.
AI-Driven Zero Trust
- Behavioral Analytics Enhancement - AI algorithms will evolve to predict threats by analyzing user behavior patterns more accurately.

- Automated Policy Adjustments - AI will enable dynamic security policies that adapt in real-time to emerging threats and user context.
- Self-Healing Networks - Networks will autonomously detect vulnerabilities and perform corrective actions without human intervention.

- AI-Powered Risk Scoring - More sophisticated risk scoring systems will be developed, leveraging AI to assess and prioritize threats.

- Intelligent Access Control - Access decisions will be made by AI, considering the context, behavior, and risk level in a granular manner.

- Enhanced Incident Response - AI will orchestrate response actions across various security platforms, reducing response times significantly.

- Proactive Threat Hunting - AI systems will proactively search for hidden threats, using advanced data analysis and pattern recognition.
- Seamless Integration with IoT - Zero Trust security will become more integrated with IoT devices, with AI ensuring the scalability of security measures.
- AI-Enhanced User Education - Personalized security training programs powered by AI will be developed to educate users on evolving cyber threats.
- Next-Gen Authentication Methods - AI will drive the creation of new biometric authentication methods, making identity verification more secure and user-friendly.
Incorporating Zero Trust does not happen overnight; it's an ongoing process that evolves with your organization's growth and technological advancements. Staying informed through resources like our comprehensive guides on securing networks can help ease this transition.
Avoiding cybersecurity risks starts with understanding that no environment is immune from threats—acknowledging this is the cornerstone of the Zero Trust philosophy.To further explore this topic or check your understanding, take our interactive quizzes:
The journey towards a secure digital ecosystem is complex but necessary. Embracing the principles of Zero Trust offers a robust framework for defending against modern cyber threats. As we move forward into an increasingly connected world, let us be vigilant by adopting a mindset where security never sleeps—and neither does our commitment to safeguarding our digital frontiers.



No comments yet. Be the first to share your thoughts!