The Importance of Network Security Monitoring
In the rapidly evolving digital world, network security monitoring has emerged as a crucial aspect of cybersecurity. It serves as the first line of defense in cybersecurity, safeguarding your network from potential threats and breaches.
Imagine your network as a bustling city. Just as city surveillance helps maintain law and order, network security monitoring keeps a vigilant eye on your network's activities. It's like having a digital security guard, continuously scanning for any suspicious activities, and alerting you when something seems amiss.

By understanding network security and implementing network security solutions, you can detect and prevent cyber threats before they infiltrate your system. This is where penetration testing for network security comes into play. It's a simulated cyber attack against your system to check for exploitable vulnerabilities.
Moreover, network security monitoring is not just about external threats. It's equally important to monitor internal activities. After all, a threat can come from within your network, often unknowingly triggered by an employee. Hence, internal network security monitoring is equally crucial.
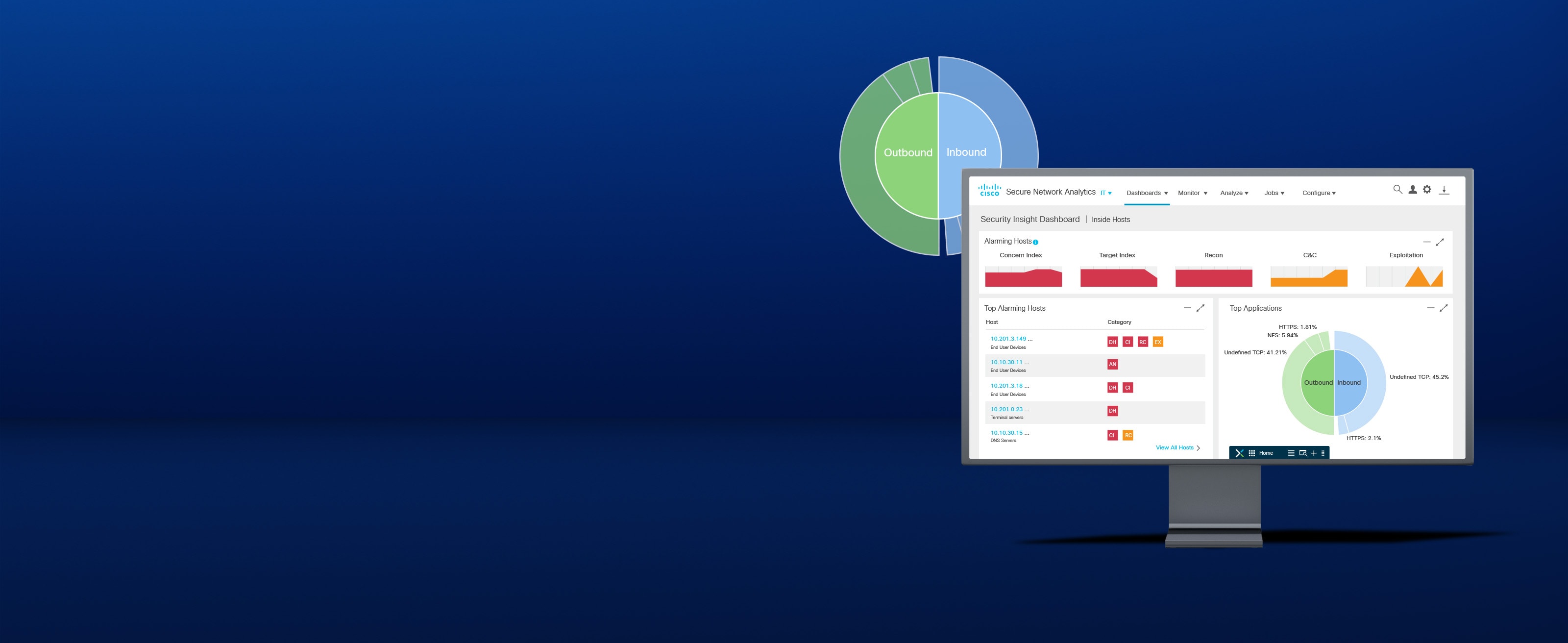
With the right network security monitoring tools, you can keep track of both incoming and outgoing traffic, ensuring your network remains secure from all angles. It's like having a second line of defense in cybersecurity, ready to tackle any threats that might have slipped past the first line.
In conclusion, network security monitoring is an indispensable part of cybersecurity. It's your first line of defense, keeping your digital world secure and your peace of mind intact.
Understanding the Basics of Network Security Monitoring
Let's dive deep into the heart of network security monitoring and unravel its basics. This is the cornerstone of understanding network security. It's akin to learning the ABCs before you start forming sentences. So, what exactly is network security monitoring?
At its core, network security monitoring is a systematic approach to detect and respond to threats and vulnerabilities that could harm your network. It's like a digital watchdog, tirelessly keeping an eye on your network's activities. It's the first line of defense in cybersecurity, always on the lookout for any signs of intrusion or abnormal behavior.
Imagine you're on a ship in the middle of the ocean. Network security monitoring is your radar, scanning the horizon for potential threats. It detects anomalies, like a sudden spike in data traffic or an unfamiliar IP address trying to gain access. Once detected, it sends out an alert, allowing you to take immediate action.
But how does it do all this? The answer lies in the use of advanced network security monitoring tools and software. These tools continuously analyze your network traffic, looking for patterns that could indicate a potential threat. They're like your network's immune system, identifying and neutralizing threats before they can cause any damage.
Understanding network security monitoring is not just about knowing how it works. It's also about understanding its importance in the broader context of cybersecurity. It's your first line of defense in cyber security, protecting your digital world from the ever-growing threat of cyber attacks.
So, whether you're a small business owner or a network administrator at a large corporation, network security monitoring should be at the top of your cybersecurity checklist. It's not just a luxury, but a necessity in today's digital world.

Internal Network Security Monitoring: Protecting from Within
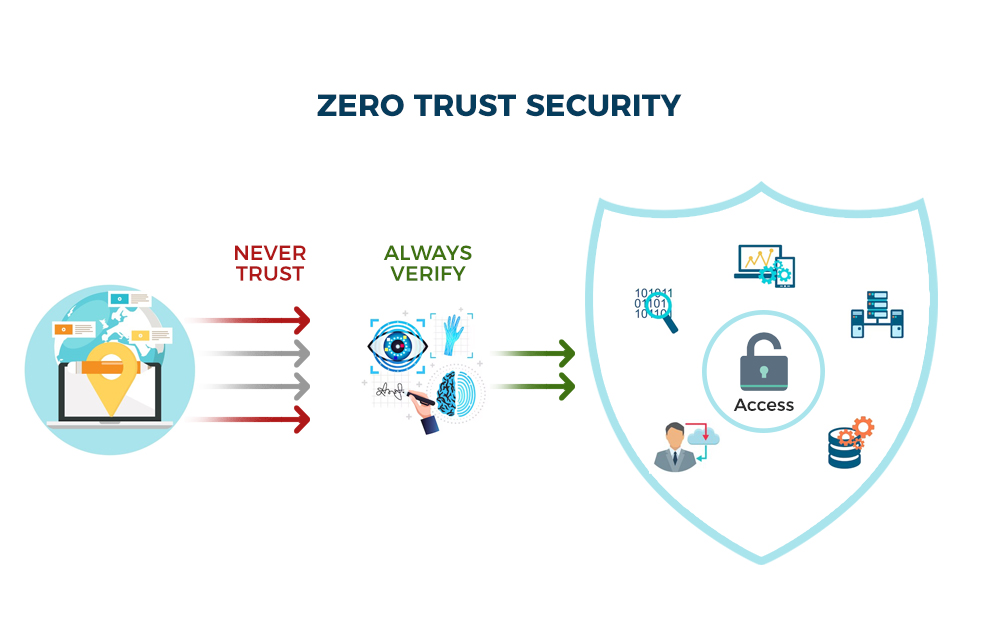
When it comes to cybersecurity, it's not just about keeping the bad guys out. It's also about keeping a watchful eye on what's happening inside. That's where internal network security monitoring comes into play. This is your first line of defense in cybersecurity, acting as a vigilant guard, always on the lookout for any signs of trouble within your network.
Imagine your network as a castle. The external defenses are crucial, but what happens if an enemy slips past them? That's when your internal guards, your network security monitoring tools, spring into action. They patrol the corridors of your castle, ready to respond at the first sign of an intruder.

Internal network security monitoring involves the continuous analysis of your network for any unusual activities or anomalies. It's about understanding network security from the inside out. This can include anything from detecting a sudden surge in data transfer to identifying unauthorized access to sensitive information.
Penetration testing for network security is a key part of this process. By simulating cyber-attacks, you can identify potential vulnerabilities and strengthen your defenses. It's like a fire drill for your network, preparing you for the real thing.
There are various network security monitoring software and tools available to help with this. These tools provide real-time updates and alerts, allowing you to respond quickly to any potential threats. Remember, in the digital world, security is not a one-time thing. It's a continuous process of monitoring, testing, and improving.
So, don't just focus on keeping the bad guys out. Make sure you're also protecting from within. Because when it comes to cybersecurity, your internal network security monitoring is your first line of defense.
Network Security Monitoring as Your First Line of Defense
Network Security Monitoring (NSM) is not just a tool; it's your first line of defense in the vast battlefield of cybersecurity. It's the digital equivalent of a vigilant sentinel, tirelessly keeping watch over your network's activities, ready to raise the alarm at the first sign of trouble.
Think of NSM as your network's immune system. Just as your body's immune system identifies and fights off infections, NSM identifies and helps combat cyber threats. It's a proactive approach to cybersecurity, designed to detect threats before they can cause significant damage.
But how does it work? At its core, NSM involves the continuous collection, analysis, and escalation of network data. It's about understanding the normal behavior of your network so you can quickly spot anything out of the ordinary. This could be anything from an unexpected data transfer to a sudden spike in network traffic.
NSM is also about speed. In the digital world, threats can emerge and escalate in a matter of seconds. That's why real-time monitoring is so crucial. With NSM, you get instant cybersecurity updates, allowing you to respond quickly and effectively to any potential threats.
Remember, in the world of cybersecurity, the best defense is a good offense. And that's exactly what NSM provides. It's your early warning system, your first line of defense, and your best chance of staying secure in the ever-evolving digital landscape.
So, whether you're a small business owner looking to protect your data or a large corporation safeguarding sensitive information, NSM should be a key part of your cybersecurity strategy. Because when it comes to network security solutions, prevention is always better than cure.

Enhancing Cybersecurity with Network Security Monitoring
Now that we've established the importance of Network Security Monitoring (NSM) as your first line of defense in cybersecurity, let's delve into how it enhances your overall cybersecurity strategy. NSM is not just about detection; it's also about providing actionable insights that can help fortify your digital world security.
One of the key ways NSM enhances cybersecurity is through penetration testing for network security. This involves simulating cyber attacks on your network to identify vulnerabilities before they can be exploited. It's like a fire drill for your network, preparing you for the real thing. 
NSM also provides a wealth of data that can be used to improve your network's security posture. By understanding network security monitoring basics, you can identify patterns and trends in your network activity. This can help you anticipate potential threats and take proactive measures to prevent them.
Another crucial aspect of NSM is internal network security monitoring. This focuses on threats that originate from within your organization. By monitoring user behavior and access patterns, NSM can detect suspicious activity that may indicate a security breach. 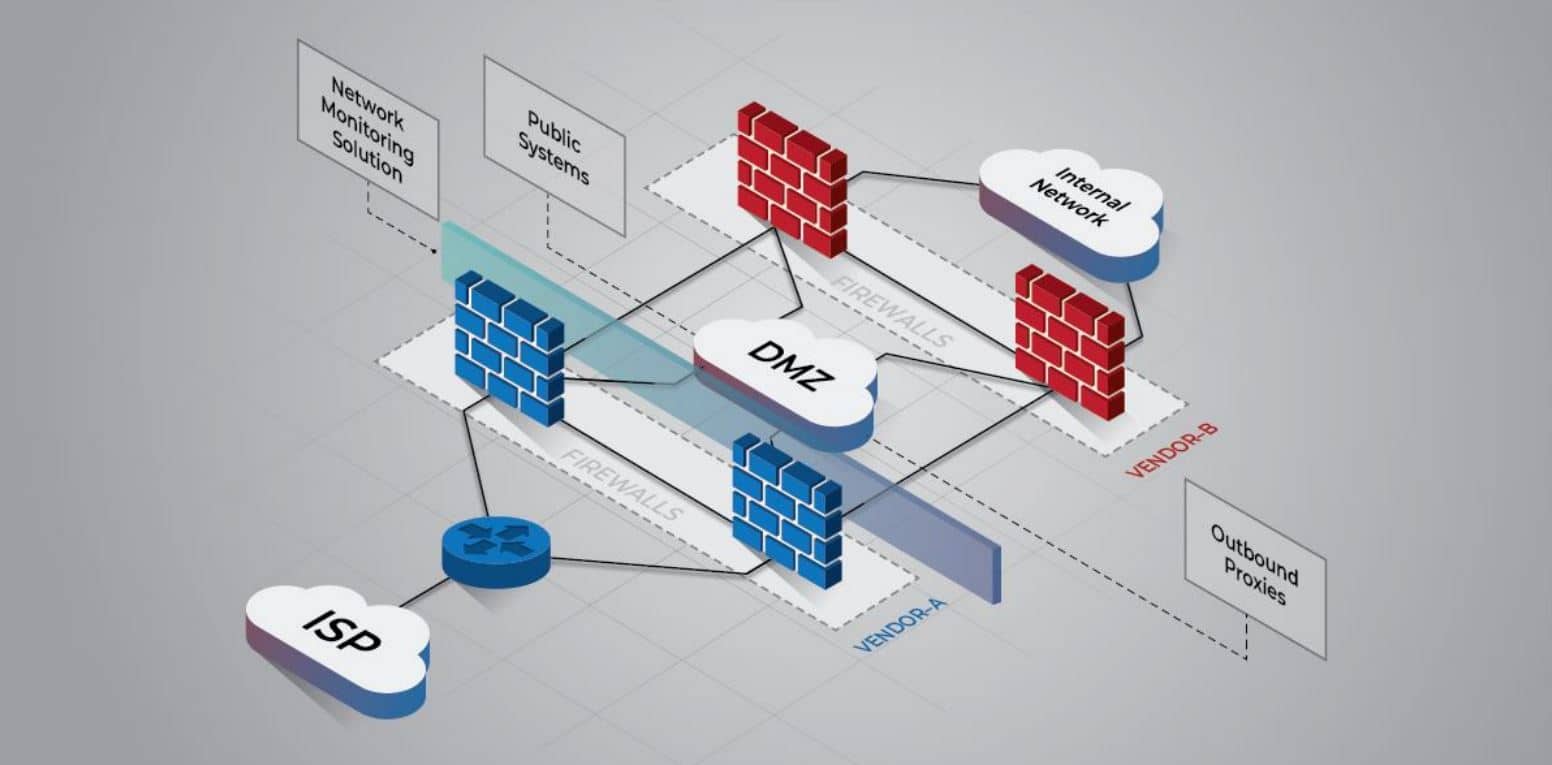
Finally, NSM tools and software play a vital role in enhancing cybersecurity. These tools provide real-time monitoring and alerts, allowing you to respond swiftly to any security incidents. They also offer features like automated threat hunting and incident response, making them an indispensable part of any cybersecurity network monitoring strategy.
In essence, NSM is not just your first line of defense in cybersecurity; it's also your second line of defense, your scout, and your strategist. It's a comprehensive solution that provides a 360-degree view of your network security, helping you stay one step ahead of the cyber threats in the digital world.
Network Security Monitoring: Staying Secure in the Digital World
Living in the digital world, we are constantly exposed to a myriad of cyber threats. The key to staying secure lies in understanding network security and implementing effective network security monitoring (NSM) strategies. NSM serves as your vigilant guardian, your first line of defense in cybersecurity, constantly scanning your network for any signs of intrusion or abnormal activity.

Think of NSM as your personal cybersecurity update center. It keeps you informed about the latest threats and vulnerabilities that could potentially harm your network. It's like having your own cybersecurity news feed, providing you with real-time updates about the state of your network security.
But NSM is not just about staying informed; it's also about taking action. With the right network security solutions, you can use the data from your NSM to bolster your defenses and respond to threats more effectively. For instance, penetration testing for network security can help you identify weak spots in your defenses and strengthen them before they can be exploited.

Moreover, NSM is not just an external shield; it also serves as an internal watchdog. Through internal network security monitoring, NSM can detect threats that originate from within your organization, helping you address them before they can cause significant damage.
So, how can you make the most of NSM? The answer lies in using the right network security monitoring tools and software. These tools not only provide real-time monitoring and alerts but also offer features like automated threat hunting and incident response, making them an essential part of your cybersecurity arsenal.

In the digital world, security is not a destination; it's a journey. And with NSM, you can embark on this journey with confidence, knowing that you have a robust first line of defense protecting your network.
Why Network Security Monitoring is Important
In the vast expanse of the digital world, network security monitoring stands as the first line of defense in cybersecurity. But why is it so crucial? Let's delve into the reasons.
Imagine your network as a bustling city. Just as a city has its law enforcement to monitor and respond to any suspicious activities, your network needs its own form of policing. This is where network security monitoring steps in. It acts as the vigilant eyes and ears of your network, constantly scanning for any signs of intrusion or malicious activity.

Network security monitoring is not just about detecting threats; it's also about understanding them. By continuously monitoring your network, you gain valuable insights into the types of threats you face, their frequency, and their origin. This knowledge is crucial in developing effective network security solutions and staying updated with the latest cybersecurity updates.
Moreover, network security monitoring is a proactive approach to cybersecurity. Instead of waiting for a breach to occur and then taking action, network security monitoring allows you to identify potential threats and neutralize them before they can cause any harm. This proactive stance is what makes network security monitoring the first line of defense in cybersecurity.

Lastly, network security monitoring plays a vital role in penetration testing for network security. By monitoring your network's response to simulated attacks, you can identify vulnerabilities and strengthen your defenses accordingly.
In essence, network security monitoring is not just important; it's indispensable. It's your network's guardian, detective, and strategist, all rolled into one. So, understanding network security monitoring is the first step towards a secure digital world.
The Basics of Network Security Monitoring
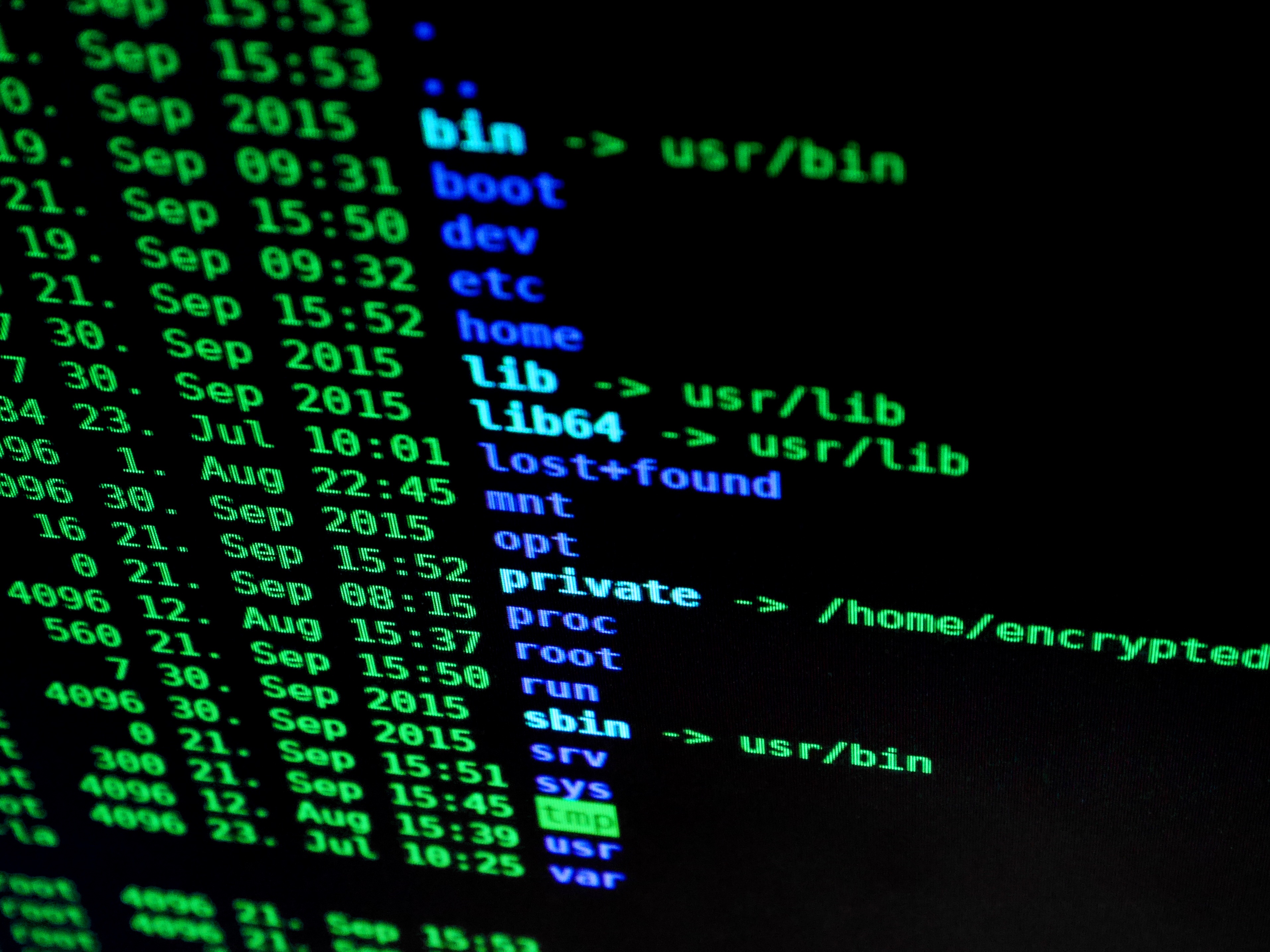
Now that we've established the importance of network security monitoring, let's delve into its basics. Network security monitoring is a multi-faceted process that involves several key components.
At its core, it involves the continuous observation of your network traffic. This includes monitoring all incoming and outgoing data, identifying unusual patterns, and flagging any suspicious activity. 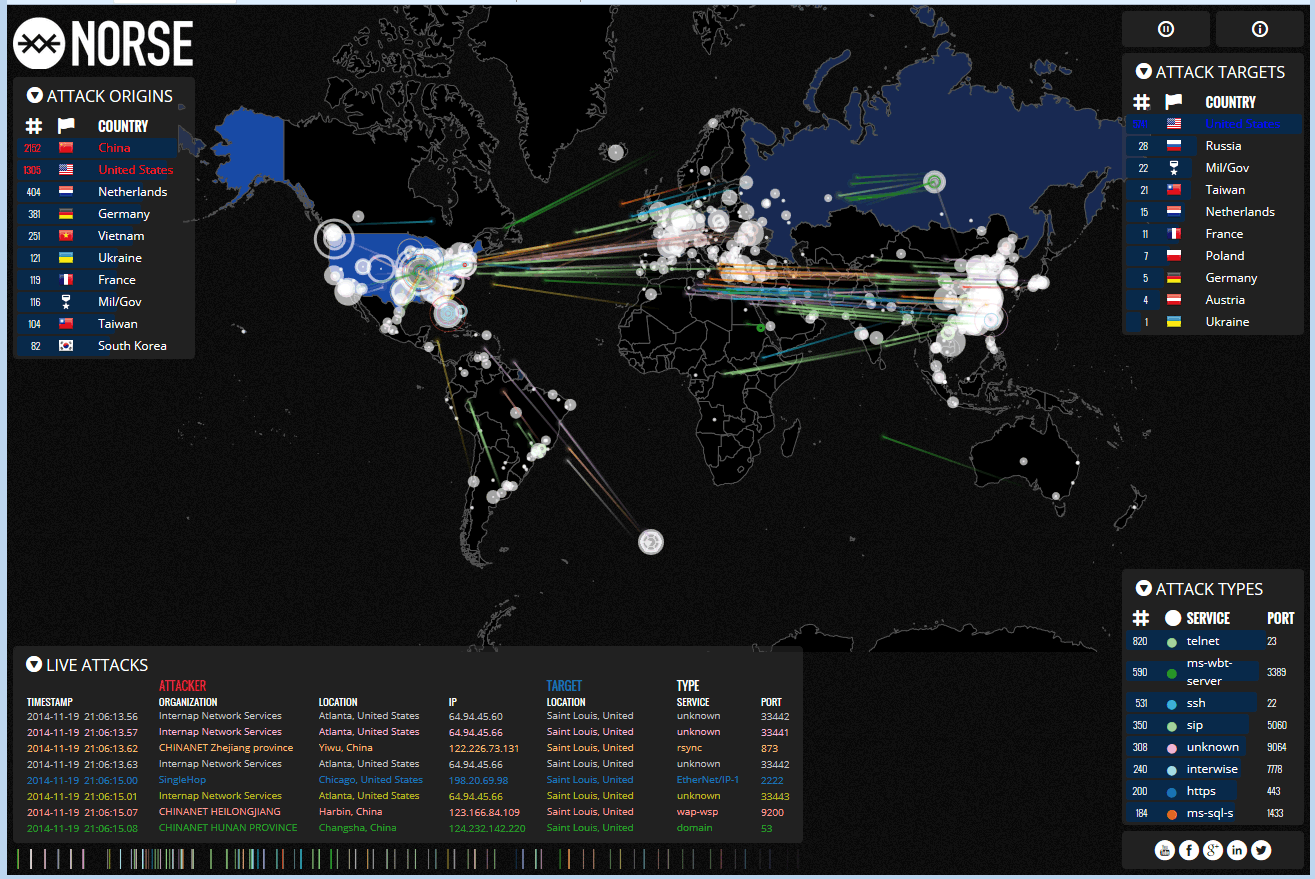
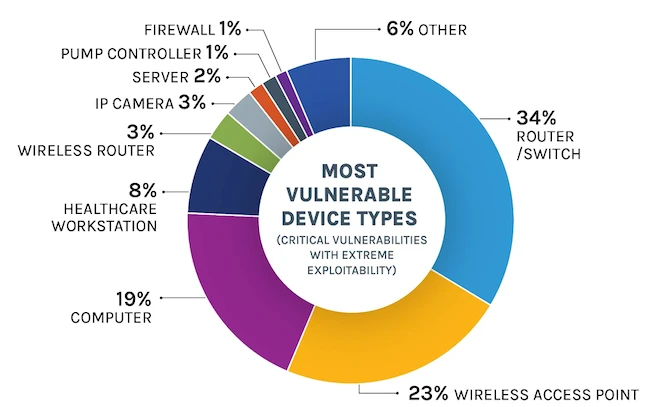
One of the fundamental aspects of network security monitoring is anomaly detection. This involves identifying patterns that deviate from the norm. For instance, a sudden surge in data transfer from a particular device could indicate a potential security breach.
Another crucial component is intrusion detection. This involves identifying attempts to compromise your network's security. Intrusion detection systems (IDS) are often employed for this purpose. These systems monitor network traffic for malicious activities or policy violations and generate alerts when they detect potential threats. 
Moreover, network security monitoring also involves log management. Logs are records of events that happen in an operating system or software. By analyzing these logs, you can gain insights into your network's activities and identify any potential security issues.
Lastly, network security monitoring involves incident response. This is the process of managing and responding to security incidents. The goal is to minimize damage and reduce recovery time and costs.
In summary, understanding network security monitoring involves grasping these key components: network traffic monitoring, anomaly detection, intrusion detection, log management, and incident response. Together, they form the first line of defense in cybersecurity, helping you stay secure in the digital world.
Network Security Monitoring Best Practices
Now that we've established the importance of internal network security monitoring and the tools available for it, let's delve into the best practices for network security monitoring. These practices are crucial to ensure that your cybersecurity network monitoring is effective and efficient, providing a robust first line of defense in cybersecurity.
1. Regularly Update Your Cybersecurity Measures: In the ever-evolving digital world, staying updated with the latest cybersecurity updates is crucial. Regularly updating your network security solutions helps you stay one step ahead of potential threats.
2. Comprehensive Monitoring: Don't just monitor your network's perimeter. Make sure to monitor the internal network as well. This includes keeping an eye on data flow, user behavior, and system configurations. Remember, a comprehensive approach to monitoring network security is your best bet against potential threats.
3. Use Advanced Network Security Monitoring Tools: Utilize advanced network security monitoring tools that provide real-time alerts and updates. These tools can help you detect and respond to threats promptly, making them an essential part of your first line of defense in cybersecurity.
4. Regular Penetration Testing: Regular penetration testing for network security is a must. It helps identify potential vulnerabilities in your network and allows you to fix them before they can be exploited.
5. Train Your Staff: Your staff is an integral part of your network security. Make sure they are well-trained in understanding network security and can recognize potential threats. A well-informed team can act as a second line of defense in cybersecurity.
6. Create a Response Plan: Despite your best efforts, breaches can still occur. Having a well-defined response plan can help minimize the damage. This includes identifying the breach, containing it, and implementing measures to prevent future occurrences.
By adhering to these best practices, you can ensure that your network security monitoring is as robust and effective as possible. Remember, in the realm of cybersecurity, vigilance and preparation are key. So, keep monitoring, keep testing, and stay secure.
The Role of Network Security Monitoring in Penetration Testing
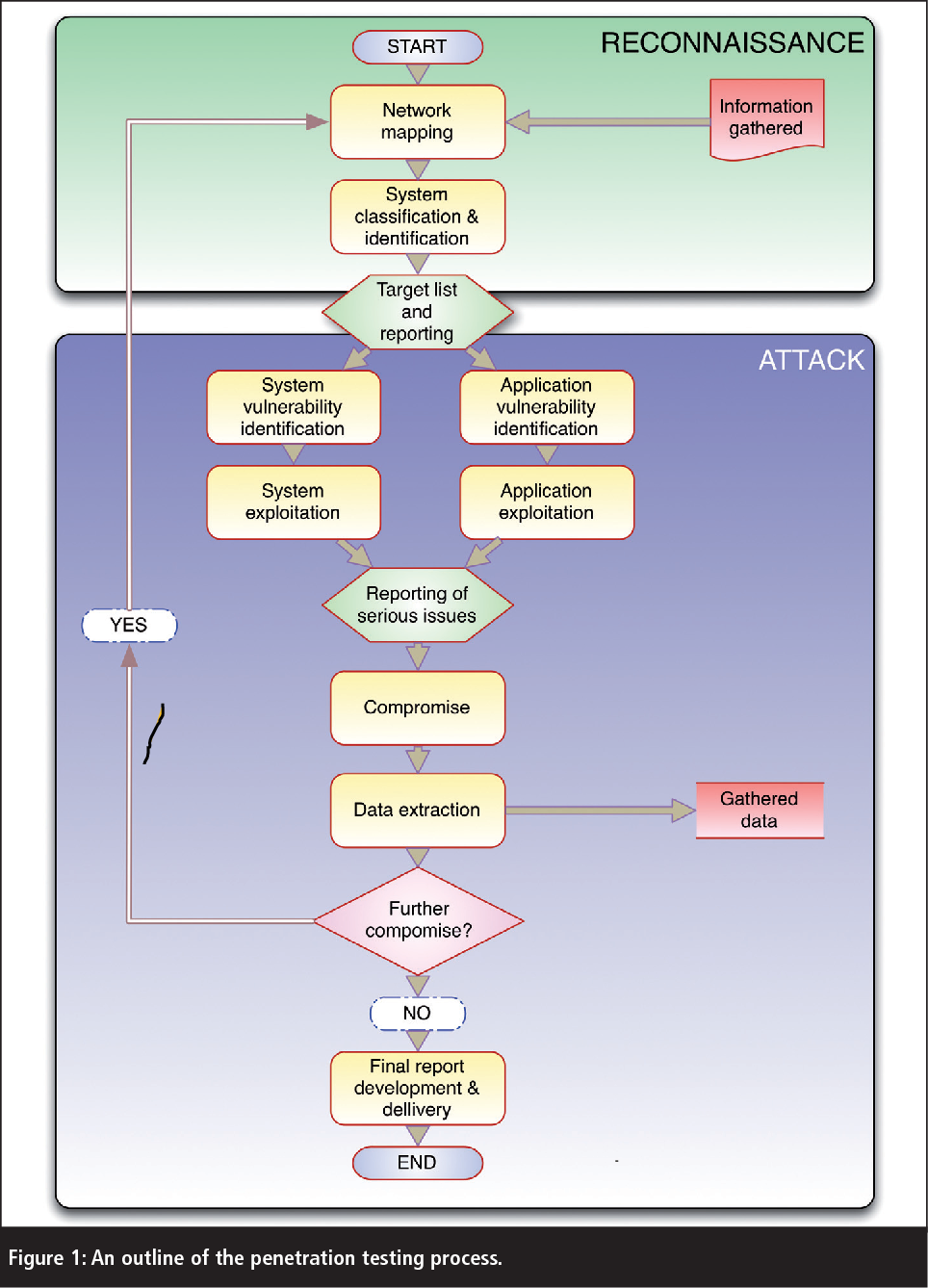
Transitioning into the realm of penetration testing, we find that network security monitoring plays a pivotal role. Penetration testing, or pen testing, is a simulated cyber attack against your system to check for exploitable vulnerabilities. In the context of network security, this means probing for weak spots in your network that could potentially be exploited by hackers.
Here, network security monitoring acts as your eyes and ears during these simulated attacks. It provides you with real-time updates and alerts about what's happening in your network during the test. This allows you to identify which areas of your network are most vulnerable and need strengthening.
Moreover, network security monitoring tools can provide valuable insights into how an actual cyber attack may unfold. By monitoring the network during a pen test, you can see how an attacker navigates your network, what tactics they use, and which systems they target. This can help you better understand your network's vulnerabilities and how to address them.
Furthermore, penetration testing for network security is not a one-time event. It should be done regularly to keep up with the latest cybersecurity threats. And each time you conduct a pen test, your network security monitoring tools will be there, providing you with the information you need to improve your network's security.
Thus, network security monitoring is not just your first line of defense in cybersecurity, but also an invaluable ally in your ongoing efforts to strengthen your network security through penetration testing.

Network Security Monitoring in the Digital World
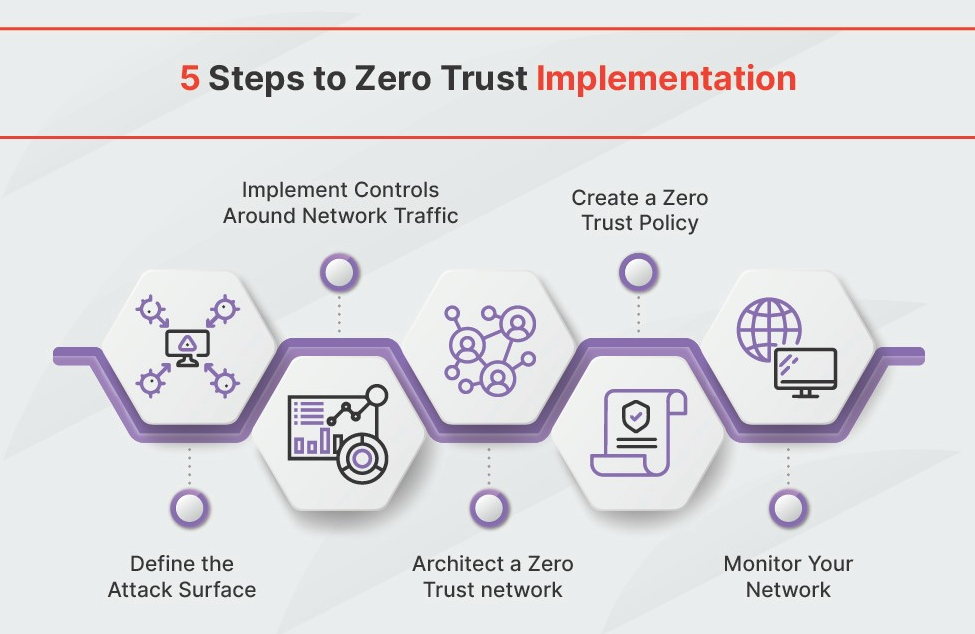
As we delve into the realm of Network Security Monitoring in the Digital World, we find ourselves in an ever-evolving landscape of cybersecurity threats and network security solutions. The digital world is not static; it's a dynamic, ever-changing environment where new vulnerabilities can emerge at any moment. This constant flux calls for a robust and adaptable approach to network security monitoring.
With the rise of cloud computing, IoT devices, and remote work, the traditional boundaries of networks have blurred. This shift has necessitated a new approach to network security monitoring that can handle these complex, distributed environments. In this context, network security monitoring serves as the first line of defense in cybersecurity, providing real-time insights into your network's health and security status.
One of the key aspects of network security monitoring in the digital world is its proactive nature. Instead of waiting for a cyber attack to occur, network security monitoring tools actively scan for potential threats and vulnerabilities. This proactive approach allows you to address potential issues before they become full-blown cybersecurity incidents.
Moreover, network security monitoring in the digital world is not just about detecting threats. It's also about understanding them. By analyzing the data collected by network security monitoring tools, you can gain insights into the tactics, techniques, and procedures used by cyber attackers. This understanding can help you develop more effective defense strategies and strengthen your network's security posture.
As we continue to navigate the digital world, network security monitoring will remain a critical component of our cybersecurity toolkit. It's our eyes and ears in the digital realm, providing us with the information we need to stay one step ahead of cyber threats.
Network Security Monitoring: Your First Line of Defense
Network Security Monitoring: Your First Line of Defense
Imagine your network as a fortress. The walls are your firewalls, the guards are your antivirus software, and the watchtowers are your network security monitoring tools. These tools are your first line of defense in the digital world, tirelessly scanning the horizon for potential threats. 
But what exactly does this first line of defense entail? At its core, network security monitoring involves the continuous observation and analysis of your network traffic. It's about keeping a vigilant eye on the data flowing in and out of your network, looking for anything unusual that might indicate a cybersecurity threat. This could be anything from a sudden surge in data transfer to an unauthorized login attempt.
However, network security monitoring is not just about detection. It's also about response. When a potential threat is detected, your network security monitoring tools should be able to alert you in real-time, giving you the chance to act swiftly and mitigate the threat before it can cause any damage. 
But remember, network security monitoring is only as effective as the tools you use. There are a plethora of network security monitoring tools available, each with their own strengths and weaknesses. Some are better suited for small businesses, while others are designed for large enterprises. Some focus on intrusion detection, while others specialize in data loss prevention. The key is to choose the right tools for your specific needs and to keep them updated with the latest cybersecurity updates.
In the end, network security monitoring is your first line of defense in the digital world. It's your watchtower, your early warning system, your eyes and ears in the ever-changing landscape of cybersecurity threats. So keep your tools sharp, your eyes open, and your network secure.
Network Security Monitoring Tools and Software
Now that we've grasped the essence of network security monitoring, let's delve into the tools and software that make it possible. These are the digital sentinels, the guardians of your network, tirelessly working to ensure that your cybersecurity is never compromised.
Network Security Monitoring Tools are the heart and soul of your cybersecurity infrastructure. They are the ones that keep a constant watch on your network, analyzing traffic, detecting anomalies, and alerting you to potential threats. They are your first line of defense in cyber security, always vigilant, always ready.
There's a wide array of network security monitoring tools available, each with its unique set of features. Some of the most popular ones include Wireshark, known for its detailed traffic analysis capabilities; Snort, a powerful intrusion detection system; and Nessus, renowned for its vulnerability scanning features.

On the other hand, Network Security Monitoring Software provides a more comprehensive solution. These are robust platforms that integrate various tools and technologies to offer a holistic approach to network security. They not only detect threats but also help in managing and mitigating them. Examples of such software include SolarWinds Network Performance Monitor and Nagios XI.

Choosing the right tools and software for your network security monitoring needs can be a daunting task. It's crucial to consider factors like the size of your network, the nature of your data, and your specific security needs. Remember, the goal is to create a robust and resilient network security system that can stand up to the ever-evolving threats of the digital world.
So, equip yourself with the right tools and software, and fortify your first line of defense in cybersecurity. After all, in the battle against cyber threats, your network security monitoring system is your most trusted ally.
Staying Secure in the Digital World: Network Security Monitoring Best Practices
As we journey further into the digital landscape, it's clear that network security monitoring is a crucial component of our cybersecurity strategy. It's not just about having the right tools and software but also about implementing best practices to ensure maximum protection. Here are some key strategies to help you stay secure in the digital world.
Stay Updated: The world of cybersecurity is ever-evolving. New threats emerge every day, and old ones evolve into more sophisticated versions. Keeping your network security solutions updated is essential. This includes not just your monitoring tools but also all software and hardware components of your network. Regularly check for updates and patches, and apply them promptly. 
Continuous Monitoring: Network security monitoring is not a one-off task. It's a continuous process that requires constant vigilance. Use your network security monitoring tools to keep an eye on your network 24/7. Set up alerts for any unusual activity and investigate promptly. 
Internal Monitoring: Often, threats come from within. Whether it's a disgruntled employee or a compromised device, internal threats can be just as damaging as external ones. Implement internal network security monitoring to keep track of all activities within your network. 
Regular Penetration Testing: As mentioned earlier, penetration testing for network security should be a regular part of your cybersecurity strategy. It helps you identify vulnerabilities and fix them before they can be exploited. 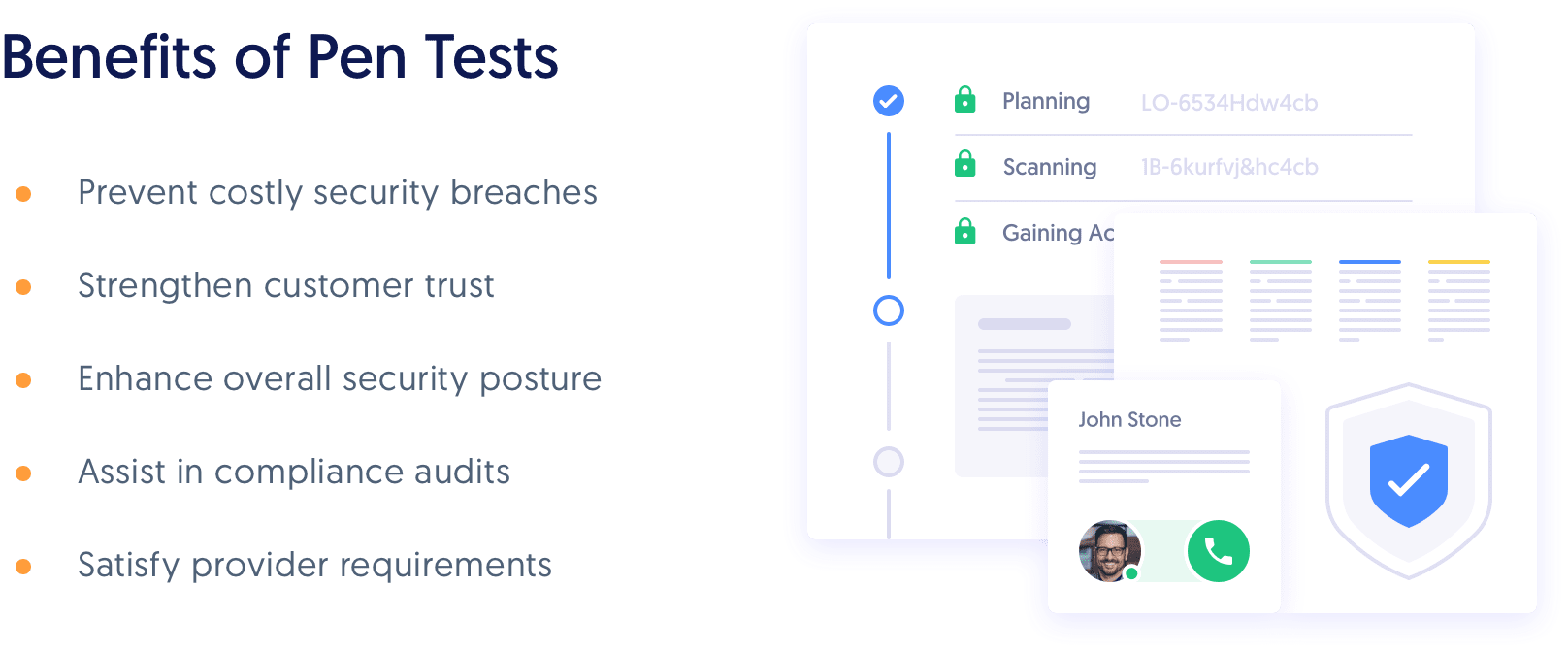
Remember, in the realm of cybersecurity, your network security monitoring is your first line of defense. Implement these best practices to ensure that it's as strong as it can be. 



No comments yet. Be the first to share your thoughts!