Understanding Vulnerability Scanning
Let's dive into the world of Vulnerability Scanning. This is a crucial cybersecurity solution that acts as your digital detective, tirelessly hunting for weaknesses within your network. It's like a health check-up for your system, identifying potential areas of concern before they become serious problems.

At its core, vulnerability scanning is a systematic process that inspects your network or system for security gaps. It's like a digital patrol, constantly on the lookout for outdated software, misconfigurations, or any other issues that could potentially be exploited by cybercriminals. This process is automated, meaning it can scan vast networks quickly and efficiently, providing you with a comprehensive overview of your system's security status.
One of the main benefits of vulnerability scanning is its proactive nature. It doesn't wait for a security breach to occur; instead, it identifies potential threats and allows you to address them in advance. This is a best practice in vulnerability scanning, ensuring that your network is always a step ahead of potential attackers.

However, it's important to note that vulnerability scanning is not a one-time process. As new vulnerabilities are discovered and cybersecurity updates and trends evolve, your system's security needs to adapt. Regular vulnerability scanning is therefore essential to maintain a robust defense against the ever-changing landscape of cyber threats.
So, when you're choosing between vulnerability scanning and penetration testing, remember that vulnerability scanning is your first line of defense, providing a broad overview of your system's security status. It's the early warning system that helps you stay ahead of the game in the fast-paced world of cybersecurity.
Exploring Penetration Testing
Now that we've delved into the realm of vulnerability scanning, let's shift our focus to another critical aspect of cybersecurity: penetration testing. While vulnerability scanning is like a vigilant sentry, penetration testing is akin to a skilled warrior, actively probing and attacking your system to assess its resilience.
Penetration testing, often referred to as pen testing, is a simulated cyber attack against your system to check for exploitable vulnerabilities. It's a hands-on approach where the tester plays the role of an attacker, using the same tactics, techniques, and tools that real-world attackers would use. The aim is to identify weak spots in your system's defenses that could be exploited by a malicious hacker.

One of the key advantages of penetration testing is its ability to provide a real-world perspective on your system's security. It goes beyond identifying potential vulnerabilities; it tests them to see if they can be exploited and how much damage they could cause. This gives you a clear understanding of the risks you face and helps you prioritize your security efforts.
Penetration testing is also a valuable tool for validating the effectiveness of your existing security measures. It can help you determine whether your defenses are working as intended and identify any gaps in your security posture. This makes it an essential part of a comprehensive cybersecurity solution.
However, just like vulnerability scanning, penetration testing is not a one-off task. Cyber threats are constantly evolving, and so should your defenses. Regular penetration testing is therefore crucial to ensure that your system remains secure against the latest attack techniques.
So, when considering the importance of penetration testing, think of it as your system's ultimate stress test. It's the process that pushes your defenses to their limits, helping you understand your system's strengths and weaknesses and ensuring that you're prepared for any potential cyber attack.
Benefits of Vulnerability Scanning
Turning our attention to the benefits of vulnerability scanning, it's important to recognize this cybersecurity solution as the first line of defense in your digital fortress. Vulnerability scanning is akin to a health check-up for your system, identifying potential weaknesses before they can be exploited by malicious actors.
One of the primary vulnerability scanning benefits is its proactive nature. It continually monitors your system for known vulnerabilities, helping you stay one step ahead of potential threats. This allows you to patch any weaknesses before they can be exploited, significantly reducing the risk of a successful cyber attack. 
Another key advantage of vulnerability scanning is its breadth of coverage. Unlike penetration testing, which focuses on specific areas, vulnerability scanning provides a comprehensive overview of your entire system. It checks all accessible systems, networks, and applications, ensuring that no stone is left unturned in your quest for robust network security.
Vulnerability scanning also plays a crucial role in maintaining compliance with various cybersecurity regulations. Many industries require regular vulnerability scans as part of their best practices in vulnerability scanning. This not only helps you avoid hefty fines and penalties but also builds trust with your clients and stakeholders, demonstrating your commitment to data security. 
Lastly, vulnerability scanning is a cost-effective cybersecurity solution. It's an automated process that requires less time and resources compared to penetration testing. This makes it a viable option for small to medium-sized businesses that may not have the budget for extensive penetration testing.
In essence, vulnerability scanning is a vital tool in your cybersecurity arsenal. It provides a comprehensive, proactive, and cost-effective solution for identifying and addressing potential vulnerabilities in your system, thereby enhancing your overall network security.
Advantages of Penetration Testing
Shifting our focus to penetration testing, it's essential to understand its unique role in the cybersecurity landscape. Unlike vulnerability scanning, penetration testing is a more in-depth and targeted approach. It simulates real-world attacks on your system, providing a realistic assessment of your network's resilience against cyber threats. This hands-on approach is one of the key penetration testing advantages.

One of the primary benefits of penetration testing is its ability to identify vulnerabilities that automated scans may miss. It delves deeper into your system, testing the effectiveness of your security measures under simulated attack conditions. This allows you to understand how a potential attacker could exploit your system, enabling you to strengthen your defenses accordingly.
Penetration testing also provides an opportunity to test your incident response capabilities. It gives your security team a chance to practice their response to an attack, helping you fine-tune your procedures and ensure that you're prepared for a real-world scenario.

Another advantage of penetration testing is its role in maintaining regulatory compliance. Many cybersecurity regulations require regular penetration testing to ensure that your security measures are up to date and effective. This not only helps you avoid penalties but also demonstrates your commitment to maintaining a secure environment.
Lastly, penetration testing provides valuable insights that can inform your cybersecurity strategy. It helps you prioritize your security investments, focusing your resources on the areas that need the most attention. This targeted approach can lead to more efficient use of resources and stronger overall security.
In summary, penetration testing is a powerful tool for enhancing your cybersecurity posture. It provides a realistic assessment of your defenses, helps you prepare for real-world scenarios, assists in maintaining regulatory compliance, and guides your cybersecurity strategy. It's an essential component of a comprehensive cybersecurity solution.
The Importance of Regular Security Updates
Let's dive into the The Importance of Regular Security Updates. In the rapidly evolving world of cybersecurity, staying updated is not just an option, but a necessity. Regular security updates act as your first line of defense against potential threats and vulnerabilities.
Imagine your cybersecurity solution as a fortress. Now, this fortress is robust, but cyber threats are like a relentless army, always probing for weak spots. Regular security updates are akin to reinforcing your fortress walls, ensuring they remain impervious to the onslaught.

But why are these updates so crucial? The answer lies in the dynamic nature of cyber threats. Hackers are always on the lookout for new vulnerabilities to exploit. When a software provider discovers such a vulnerability, they develop a patch to fix it. If you don't update your software, you're essentially leaving a door wide open for cyber attackers.
Regular security updates also play a pivotal role in both vulnerability scanning and penetration testing. Updated systems can better identify the latest threats, making vulnerability scanning more effective. Similarly, penetration testing advantages are enhanced when testing against updated systems, as it provides a more realistic assessment of your security posture.
Choosing between vulnerability scanning and penetration testing is a critical decision, but remember, without regular security updates, both these cybersecurity solutions lose their efficacy. So, keep your systems updated, and stay one step ahead of the cyber attackers.

Current Trends in Cybersecurity
Now, let's shift our focus to the Current Trends in Cybersecurity. The digital landscape is ever-changing, and so are the methods employed by cybercriminals. Staying ahead of these trends is crucial to maintaining a robust cybersecurity solution.
One of the significant trends is the rise of Artificial Intelligence (AI) and Machine Learning (ML) in cybersecurity. These technologies are being used to predict and identify threats before they can cause harm. They are also enhancing the best practices in vulnerability scanning, making it more accurate and efficient.

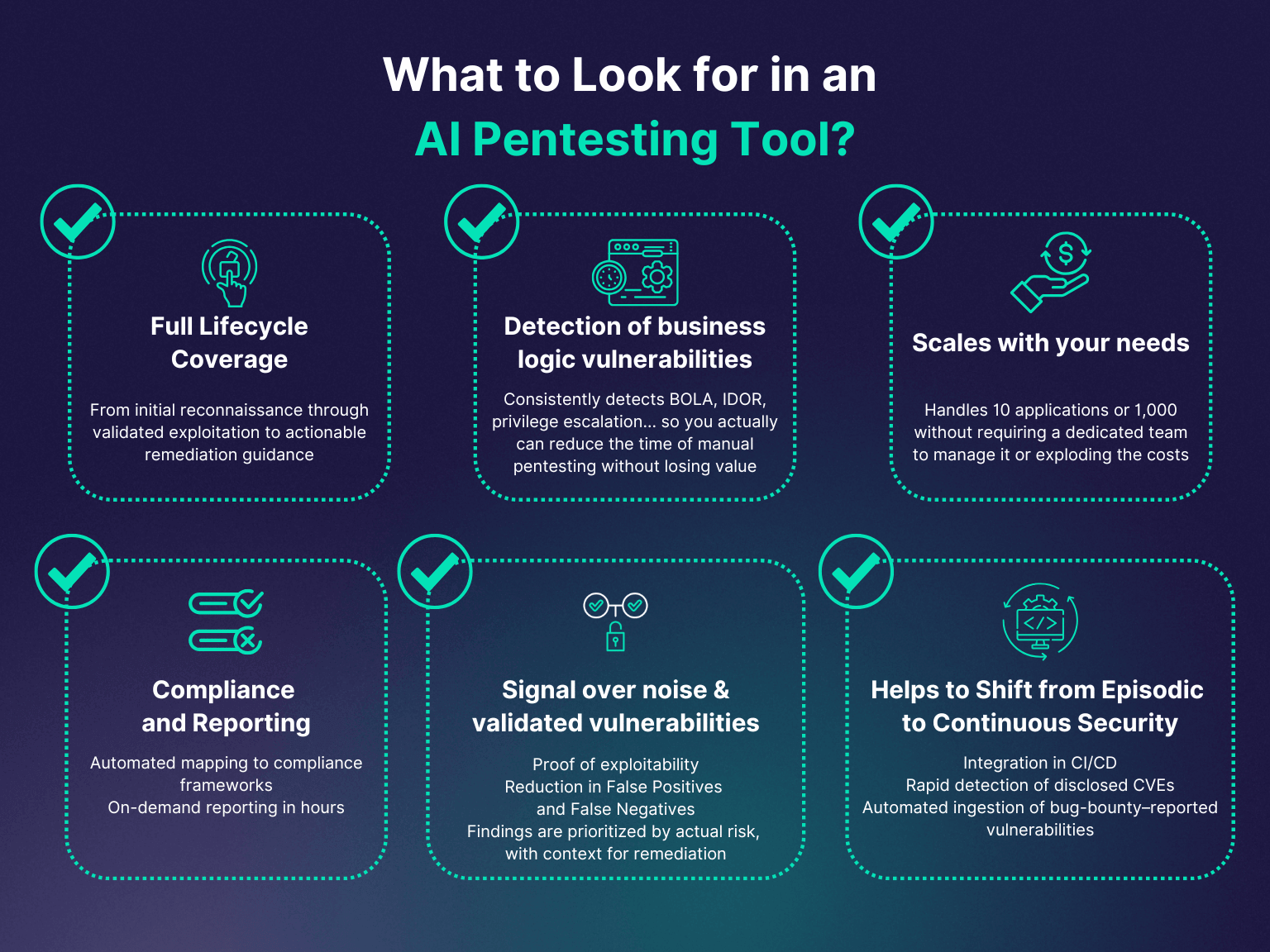
Another trend is the increasing importance of penetration testing. As cyber threats become more sophisticated, the importance of penetration testing is growing. It allows organizations to proactively identify vulnerabilities and fix them before they can be exploited.

Moreover, the adoption of cloud-based cybersecurity solutions is on the rise. These solutions offer scalability, cost-effectiveness, and ease of use, making them an attractive option for businesses of all sizes.

Lastly, the concept of Zero Trust is gaining traction. This security model operates on the principle of 'never trust, always verify.' It assumes that any network, internal or external, could be compromised and thus requires strict identity verification for every person and device trying to access resources on the network.

These trends highlight the evolving nature of cybersecurity. Whether it's choosing between vulnerability scanning and penetration testing, or deciding on the right cybersecurity solutions, staying abreast of these trends can help you make informed decisions and keep your digital fortress secure.
Choosing the Right Approach for Your Needs
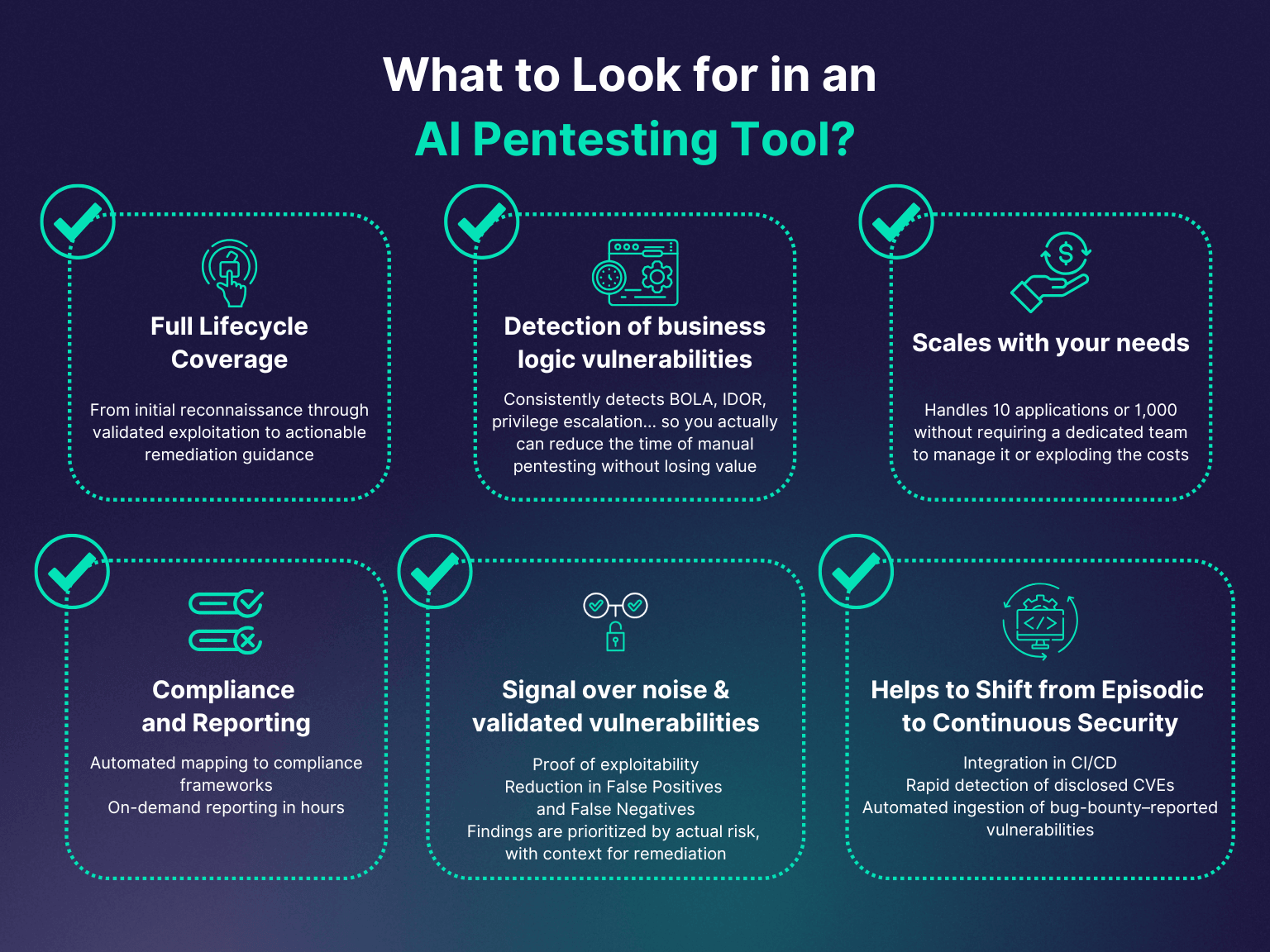
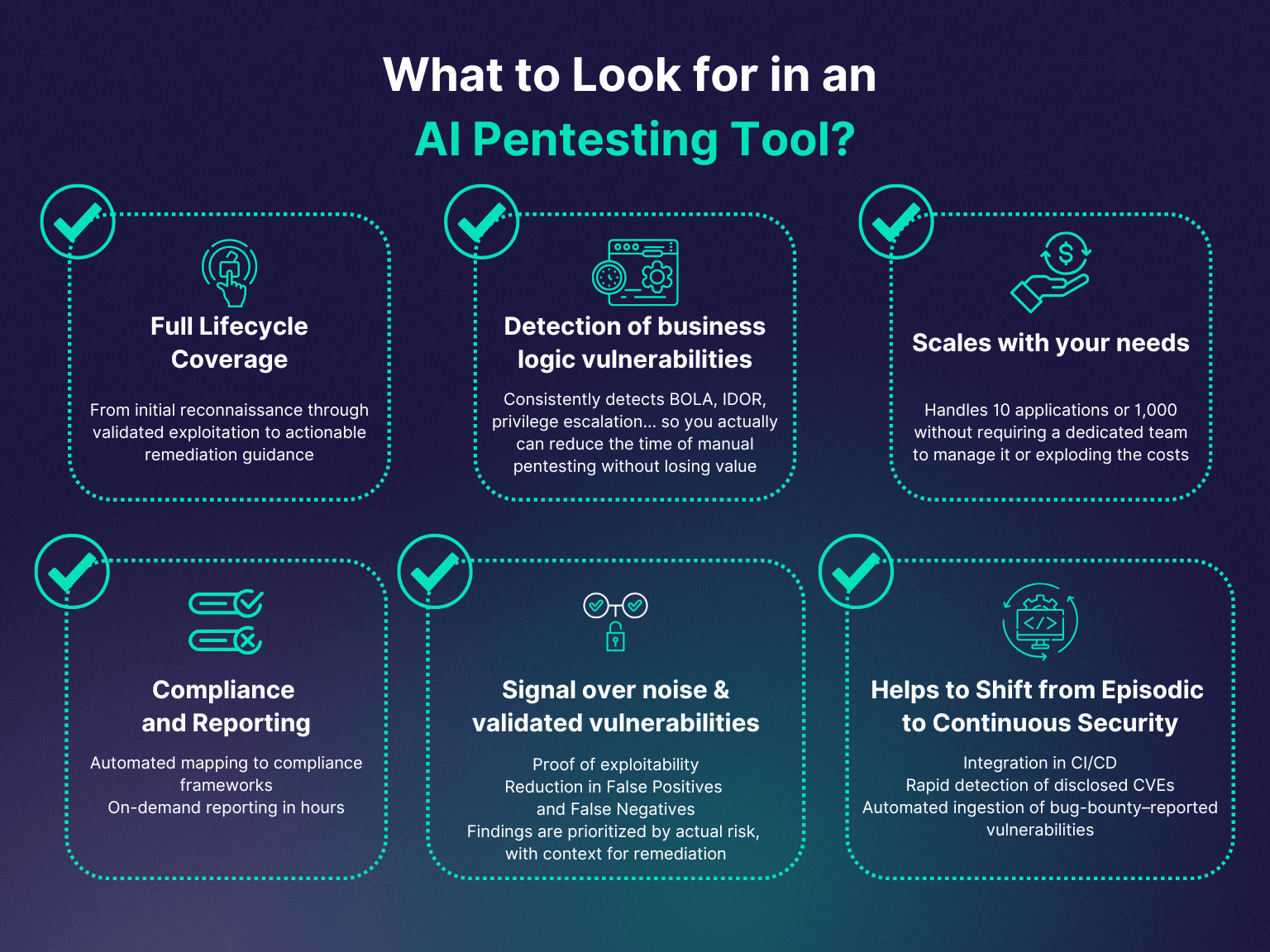
When it comes to choosing between vulnerability scanning and penetration testing, the decision largely depends on your specific needs and circumstances. Both methods offer unique benefits and are crucial components of a robust cybersecurity solution. However, understanding your organization's requirements and the nature of your digital assets can guide you towards the right approach.
Vulnerability scanning is an excellent choice for organizations that need regular, automated checks for potential weaknesses. It's a proactive measure that helps you stay ahead of the curve, identifying and addressing vulnerabilities before they can be exploited. This approach is particularly beneficial for large networks with numerous devices, where manual testing might be impractical.

On the other hand, penetration testing is a more targeted and thorough method. It's ideal for organizations that handle sensitive data or operate in highly regulated industries. Penetration testing provides a realistic assessment of your network's resilience, helping you understand how an attacker could exploit your system. It also plays a crucial role in maintaining regulatory compliance and testing your incident response capabilities.

Ultimately, the best practices in vulnerability scanning and the importance of penetration testing are not mutually exclusive. Many organizations find value in employing both methods, using vulnerability scanning for regular checks and penetration testing for a more in-depth analysis. This combination allows for a comprehensive, multi-layered approach to network security, ensuring that your digital assets are protected from all angles.
Remember, the digital landscape is constantly evolving, and staying updated with the latest cybersecurity updates and trends is key to maintaining a robust defense. Whether you choose vulnerability scanning, penetration testing, or a combination of both, the goal remains the same: to safeguard your organization from the ever-present threat of cyber attacks.
The Importance of Regular Testing
Delving into The Importance of Regular Testing, it's crucial to understand that cybersecurity isn't a one-time solution. It's an ongoing process that requires constant vigilance and adaptation. The digital world is ever-evolving, with new threats emerging and old ones morphing into more sophisticated forms. Regular testing, whether it's vulnerability scanning or penetration testing, is a vital part of staying ahead of these threats.
Imagine your cybersecurity solution as a fortress. Regular testing is akin to routinely checking the fortress's walls for cracks or weak spots. Without this regular inspection, you might not notice a vulnerability until it's too late - when an attacker has already exploited it. 
Regular testing offers several benefits. It helps you keep up with the latest cybersecurity updates and trends, ensuring that your defenses are always up-to-date. It also allows you to detect and fix vulnerabilities promptly, minimizing the window of opportunity for attackers. Furthermore, regular testing can help you assess the effectiveness of your current security measures and make necessary adjustments.
Whether you're using vulnerability scanning, penetration testing, or a combination of both, regular testing is a best practice that should not be overlooked. It's a proactive measure that can significantly enhance your network security, providing you with peace of mind in today's unpredictable digital landscape. 
In essence, the importance of regular testing lies in its ability to keep your cybersecurity solutions agile and responsive. It's not just about finding vulnerabilities; it's about continually improving your defenses and staying one step ahead of potential threats. Remember, in the realm of cybersecurity, complacency is the enemy. Regular testing is your ally.
Choosing the Right Approach
Choosing between vulnerability scanning and penetration testing can feel like a daunting task. But fear not, the right approach depends on your specific needs and circumstances. Both methods have their unique benefits, and understanding these can guide you to the best decision for your cybersecurity solution.
Vulnerability scanning is a fantastic starting point for organizations looking to identify and address potential weaknesses in their network. It's like a routine health check-up for your system, ensuring that no glaring issues go unnoticed. If you're seeking a cost-effective, automated way to regularly monitor your network's health, vulnerability scanning could be your best bet. It's especially useful for businesses that need to manage a large number of systems, as it can quickly provide a broad overview of your network's security posture.
On the other hand, penetration testing is akin to a stress test for your system. It simulates real-world attacks, providing a detailed picture of how your defenses might hold up under pressure. If you're looking for a more in-depth analysis, or if you need to meet specific regulatory requirements, penetration testing might be the right choice for you. It's particularly beneficial for organizations that handle sensitive data, as it can help ensure that your security measures are robust enough to withstand targeted attacks.
Ultimately, the best approach may be a combination of both. Regular vulnerability scans can help you stay on top of potential issues, while periodic penetration tests can provide a deeper understanding of your system's resilience. This balanced approach can provide a comprehensive cybersecurity solution, helping you stay secure in an ever-evolving digital landscape.

Keeping Up with Cybersecurity Updates
As we delve deeper into the digital age, the importance of staying updated with the latest cybersecurity trends cannot be overstated. The world of cybersecurity is dynamic, with new threats emerging and old ones evolving at a rapid pace. Therefore, keeping your finger on the pulse of cybersecurity updates is crucial to maintaining a robust defense against potential attacks.
One way to stay informed is by subscribing to reputable cybersecurity news platforms. These platforms provide timely updates on the latest threats, vulnerabilities, and best practices in vulnerability scanning and penetration testing. They can serve as a valuable resource for understanding the current cybersecurity landscape and making informed decisions about your cybersecurity solutions.
Another effective strategy is to participate in cybersecurity forums and online communities. These platforms can provide real-time insights from other cybersecurity professionals, fostering a collaborative environment for sharing experiences and learning from each other. 
Attending cybersecurity conferences and webinars can also be beneficial. These events often feature presentations from industry experts, offering a wealth of knowledge on topics such as network security scanning vs testing, the advantages of penetration testing, and the benefits of vulnerability scanning. 
Lastly, consider investing in continuous education and training for your team. This can help ensure that everyone is up-to-date with the latest cybersecurity trends and best practices. Remember, a well-informed team is your first line of defense against cyber threats. 
In summary, keeping up with cybersecurity updates is not just about staying informed. It's about empowering yourself and your team with the knowledge and skills needed to navigate the ever-changing digital landscape confidently and securely.
Emerging Trends in Network Security
As we navigate through the ever-evolving landscape of cybersecurity, it's essential to stay abreast of the emerging trends in network security. These trends not only shape the way we approach cybersecurity but also influence the decisions we make when choosing between vulnerability scanning and penetration testing.
One significant trend is the increasing adoption of Artificial Intelligence (AI) and Machine Learning (ML) in cybersecurity solutions. AI and ML can automate the process of identifying vulnerabilities and predicting potential threats, thereby enhancing the effectiveness of vulnerability scanning and penetration testing. 
Another trend is the shift towards proactive cybersecurity. Instead of reacting to cyber threats after they occur, organizations are now focusing on predicting and preventing attacks. This shift underscores the importance of penetration testing, which simulates real-world attacks to identify potential vulnerabilities before they can be exploited.
Finally, there's a growing emphasis on integrated cybersecurity solutions. Rather than relying on standalone tools for vulnerability scanning and penetration testing, organizations are now seeking comprehensive solutions that offer a holistic approach to network security. 
These trends highlight the dynamic nature of network security and the need for continuous learning and adaptation. As such, it's crucial to stay updated with the latest developments in the field and incorporate these insights into your cybersecurity strategy. Whether it's leveraging AI and ML, adopting a proactive approach, or integrating your cybersecurity tools, staying ahead of the curve can make all the difference in safeguarding your digital assets.


No comments yet. Be the first to share your thoughts!