The shift toward AI testing
Penetration testing, the practice of ethically hacking systems to find vulnerabilities, is facing a new reality. Traditional methods, relying heavily on manual effort and rule-based automation, are increasingly challenged by the speed and complexity of modern software and infrastructure. We’re seeing attack surfaces expand dramatically, and defenders need to keep pace, but the sheer volume of potential entry points makes it nearly impossible for humans alone to find everything.
For years, automated pentesting tools have offered some relief, scanning for known vulnerabilities. However, these tools often lack the adaptability and creativity to uncover more subtle or novel weaknesses. They’re good at finding what they’re looking for, but less adept at discovering what they haven’t been programmed to recognize. That's where artificial intelligence steps in, promising to augment and enhance the pentesting process.
Pentesting used to be a manual grind. As systems grew, we built scanners and fuzzers to keep up. AI is the next step in that progression. It doesn't replace a human tester, but it handles the heavy lifting of pattern recognition that manual tools miss.
Modern systems, particularly those built using cloud technologies and microservices, present a moving target. Constant updates, dynamic configurations, and complex interactions make it difficult to maintain a comprehensive understanding of potential vulnerabilities. AI offers the potential to continuously learn and adapt to these changes, providing a more proactive and effective approach to security testing.
How AI finds vulnerabilities
AI isn’t simply about automating existing pentesting tasks; it’s about fundamentally changing how those tasks are performed. Several key AI techniques are being applied to vulnerability research and exploitation. Machine learning algorithms, for example, can be trained on vast datasets of code and vulnerability reports to identify patterns and predict potential weaknesses. They can learn to recognize code smells that often indicate security flaws, even if those flaws haven’t been explicitly documented.
Natural language processing (NLP) plays a vital role in analyzing security reports, vulnerability descriptions, and even threat intelligence feeds. NLP can extract key information from unstructured text, helping penetration testers quickly understand the context and severity of potential threats. It can also automate the process of documenting findings and generating reports, saving significant time and effort. Reinforcement learning is emerging as a powerful technique for automated exploit development.
Reinforcement learning allows an AI agent to learn through trial and error, iteratively improving its ability to exploit vulnerabilities. The agent receives rewards for successful exploits and penalties for failures, gradually refining its strategies. This approach can uncover exploits that might be missed by traditional methods, and it can adapt to changing system configurations. The difference between automated and AI-driven pentesting is significant, as HackerSec.com points out – AI-driven tests offer a depth that pure automation often lacks.
These AI techniques improve efficiency by automating repetitive tasks, improve accuracy by identifying subtle vulnerabilities, and improve coverage by exploring a wider range of attack vectors. They allow penetration testers to focus on the most critical areas of concern, rather than spending time on mundane tasks. However, it’s important to remember that AI is a tool, and it requires human expertise to interpret the results and validate the findings.
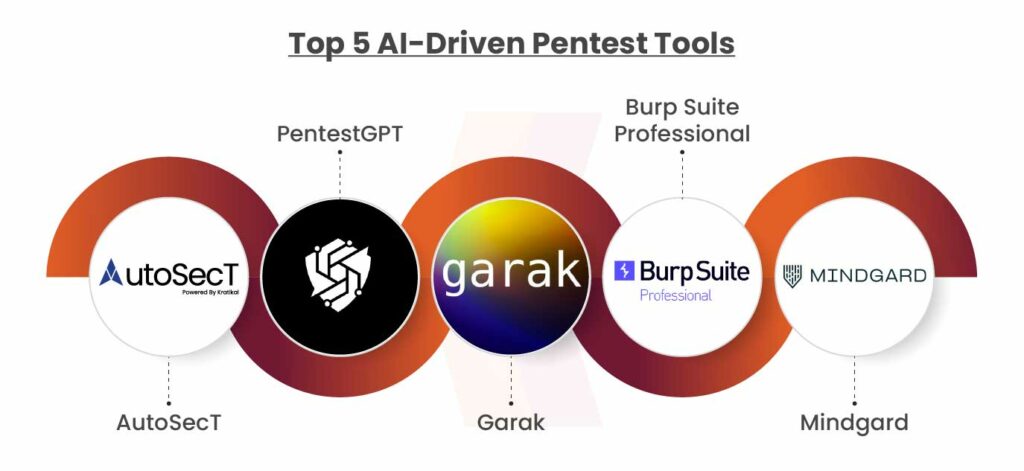
Top platforms for 2026
The market moves fast. Based on StackHawk's 2026 data, these platforms are currently leading the way in automated testing.
StackHawk: Targeted at developers, StackHawk integrates directly into the CI/CD pipeline, providing continuous security testing. It uses AI to prioritize vulnerabilities and provide actionable remediation guidance. Its strength lies in its developer-friendly interface and focus on shifting security left. A potential weakness is its relative newness compared to some established players.
Invicti (formerly Netsparker): Invicti is a robust dynamic application security testing (DAST) platform that incorporates AI to improve scan accuracy and reduce false positives. It's well-suited for enterprise environments with complex web applications. Its strength is its comprehensive coverage and ability to handle sophisticated web technologies. A weakness can be its complexity and higher price point.
Bright Security (formerly NeuraLegion): Bright Security focuses on developer-driven security, offering a platform that integrates seamlessly with existing development workflows. Its AI-powered engine helps developers identify and fix vulnerabilities early in the development lifecycle. Bright Security excels at providing contextualized security feedback to developers. It's a newer platform, so its feature set is still evolving.
Detectify: Detectify uses a crowdsourced vulnerability research platform combined with AI-powered scanning to identify vulnerabilities in web applications. It’s known for its ability to discover zero-day vulnerabilities. The platform’s strength is its constant stream of new vulnerability signatures. A potential weakness is its reliance on crowdsourced data, which may not always be reliable.
Probely: Probely is a full-stack DAST solution that leverages AI to automate vulnerability discovery and prioritization. It provides detailed reports and remediation guidance. It’s a good option for organizations looking for a comprehensive DAST solution. A potential drawback is its limited support for certain types of applications.
Pentest-Tools.com: This platform offers a suite of pentesting tools, including AI-powered vulnerability scanners and exploit frameworks. It’s designed for both beginners and experienced penetration testers. Its strength is its affordability and ease of use. A weakness is its limited depth compared to more specialized platforms.
Breached: Breached focuses on providing comprehensive attack surface management, using AI to identify and map all of an organization’s internet-facing assets. It helps organizations understand their overall security posture. Breached is strong at providing a holistic view of an organization's attack surface. It may not be as focused on deep vulnerability analysis.
Horizon3.ai: Horizon3.ai specializes in breach and attack simulation (BAS), using AI to simulate real-world attacks and identify weaknesses in an organization’s defenses. It’s a valuable tool for validating security controls. Its strength is its ability to provide realistic attack simulations. It's primarily focused on BAS, not traditional vulnerability scanning.
Rhino Security: Rhino Security offers a cloud-native DAST solution that uses AI to prioritize vulnerabilities and provide actionable remediation guidance. It’s designed for modern web applications and APIs. Rhino Security is strong at identifying vulnerabilities in complex web applications. It’s a relatively new platform, so its feature set is still developing.
Essential Learning Resources for Aspiring AI-Powered Penetration Testers

Comprehensive coverage of the CompTIA Security+ SY0-701 exam objectives · Detailed explanations of core security concepts and practices · Practice questions and exam simulations for effective preparation
This study guide offers a thorough foundation in cybersecurity principles, essential for understanding the underlying mechanics of AI-driven penetration testing.

Covers all domains of the Certified Ethical Hacker (CEH) v12 exam · Explains ethical hacking methodologies and tools · Includes practice questions and labs for hands-on learning
The CEH All-in-One Exam Guide provides critical knowledge of ethical hacking techniques, which are foundational to interpreting and leveraging AI penetration testing outputs.

Introduces fundamental penetration testing concepts and methodologies · Offers practical, hands-on exercises for real-world application · Covers reconnaissance, scanning, exploitation, and post-exploitation phases
This book demystifies penetration testing through practical examples, building the necessary context for understanding how AI enhances these processes.

Focuses on practical, actionable penetration testing strategies · Details techniques for various attack vectors and scenarios · Provides guidance on effective reporting and remediation
The Hacker Playbook 3 offers a practical, step-by-step approach to penetration testing, enhancing comprehension of the automated workflows employed by AI tools.

Prepares candidates for the AWS Certified Security – Specialty (SCS-C02) exam · Covers AWS security best practices, services, and implementation · Includes review sections and practice exams
This guide equips readers with essential knowledge of cloud security within AWS, a critical domain where AI-powered penetration testing is increasingly applied.
As an Amazon Associate I earn from qualifying purchases. Prices may vary.
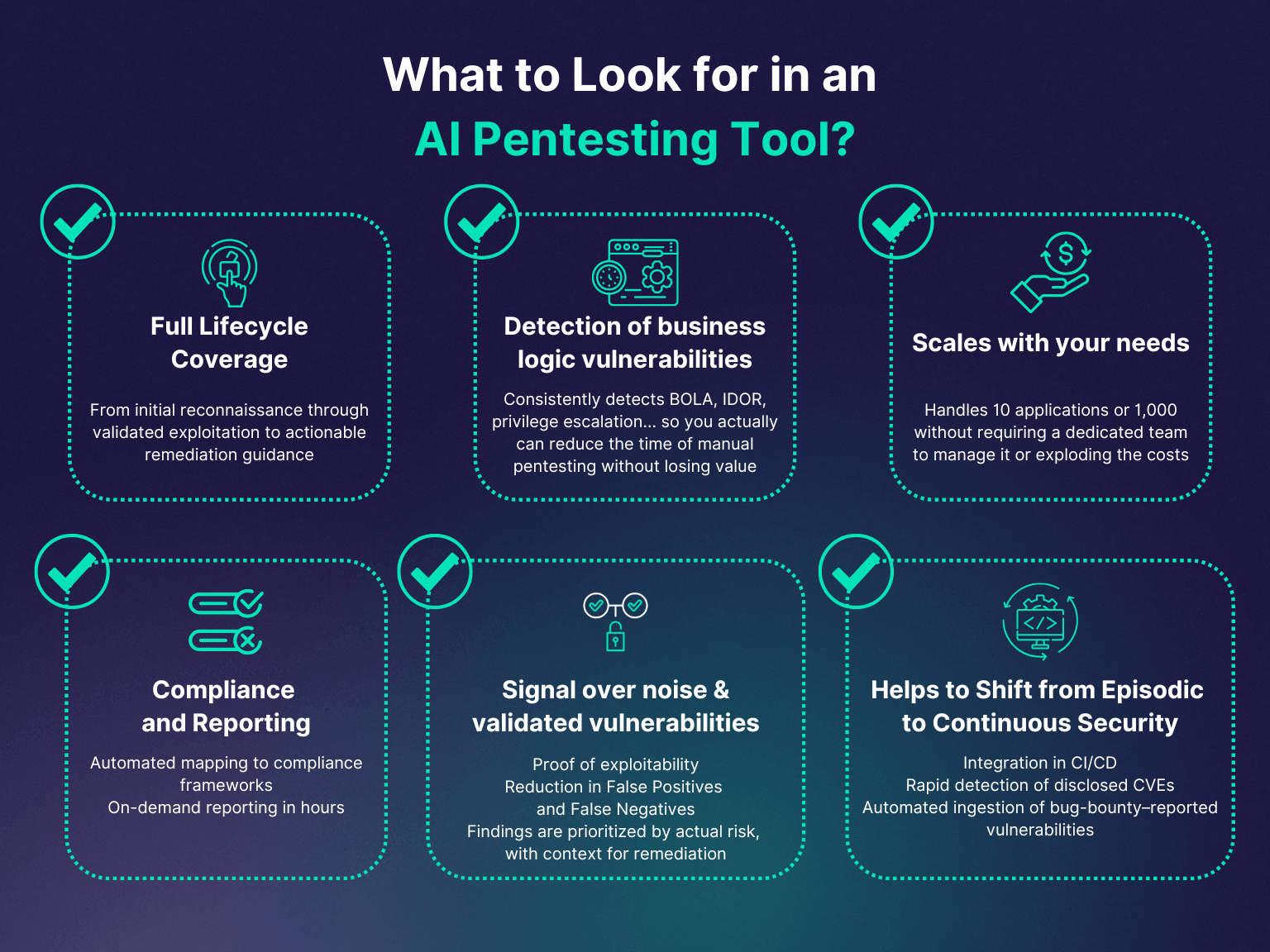
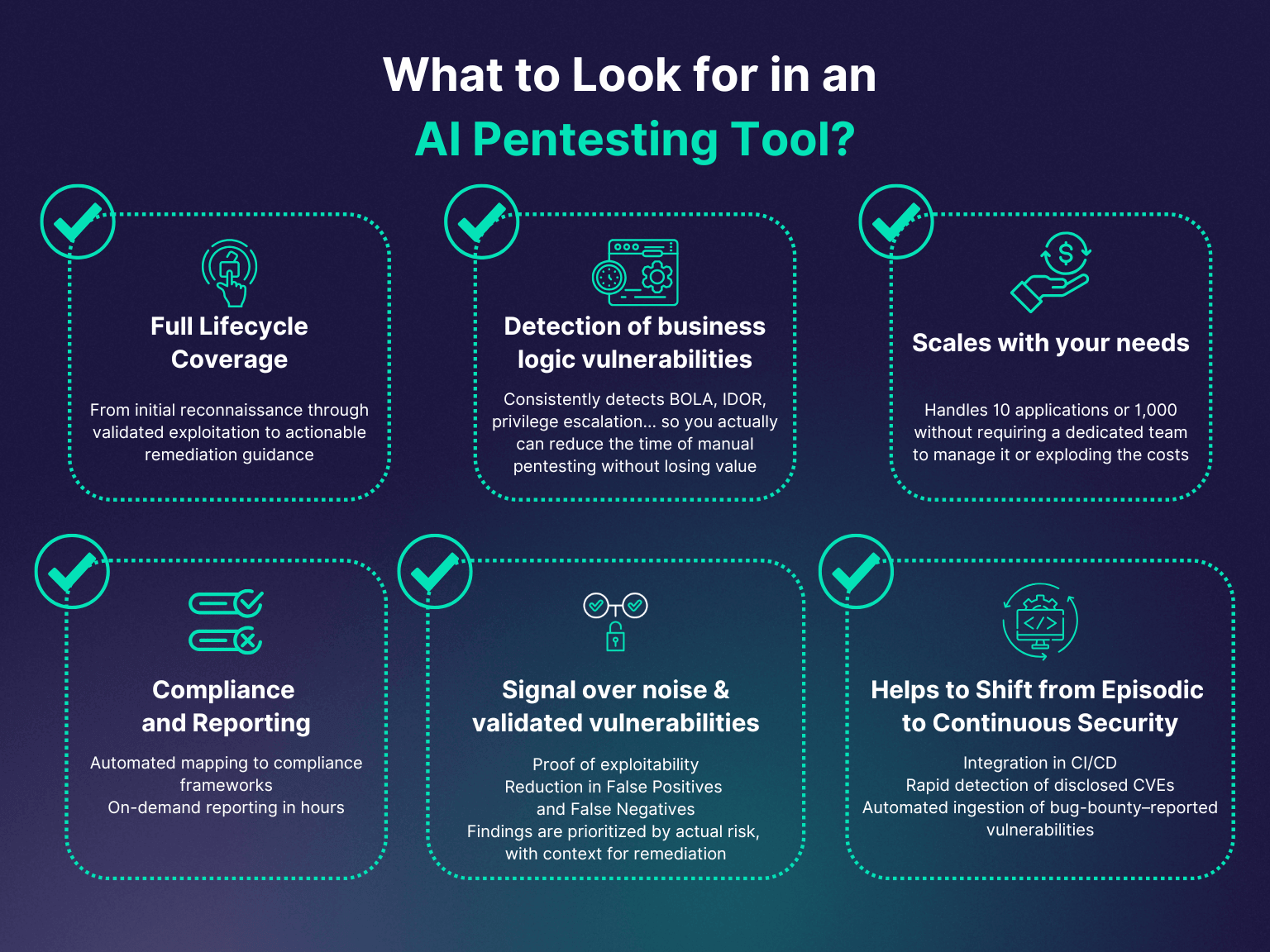
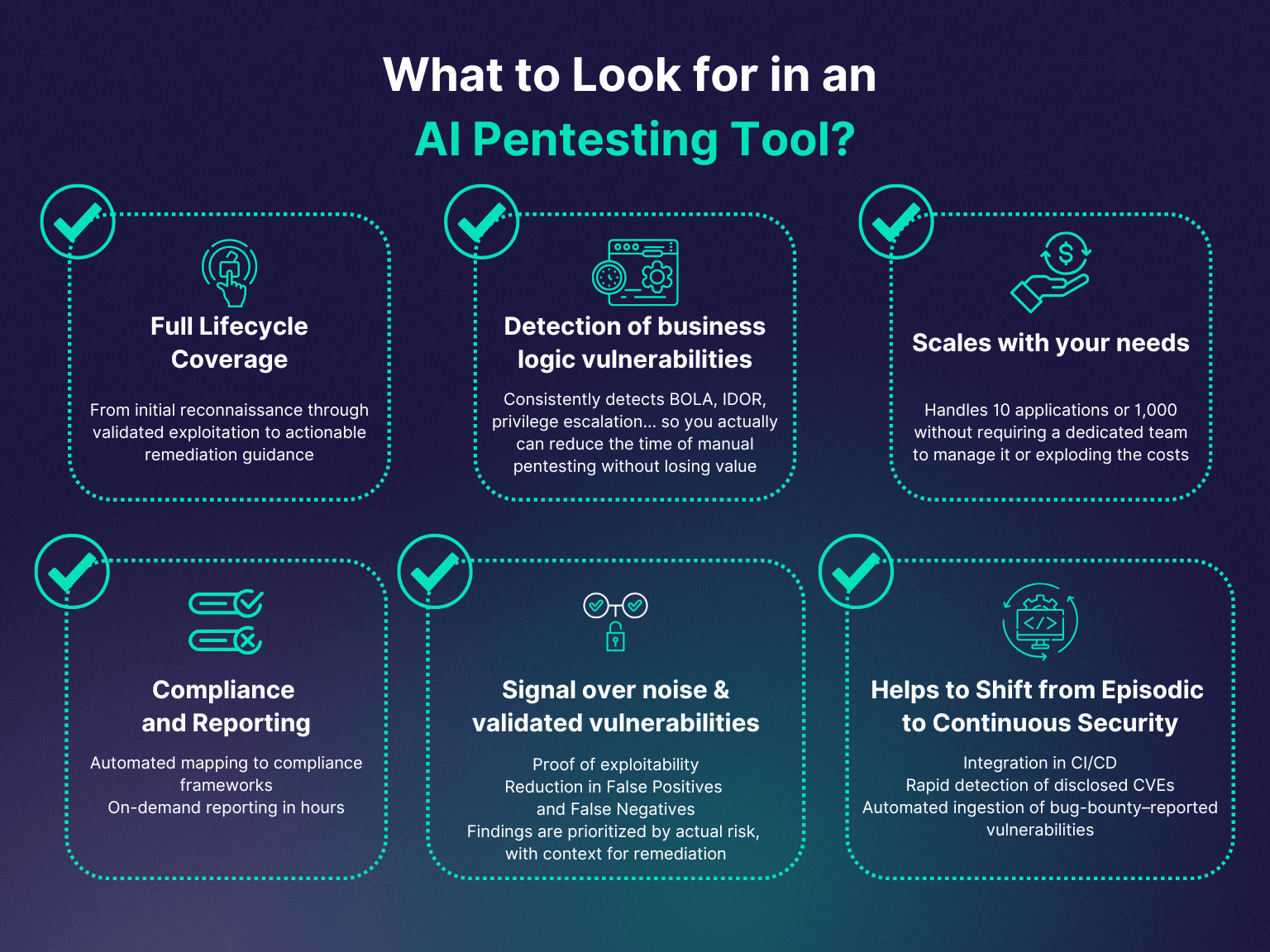
Decoding AI Pentesting Features
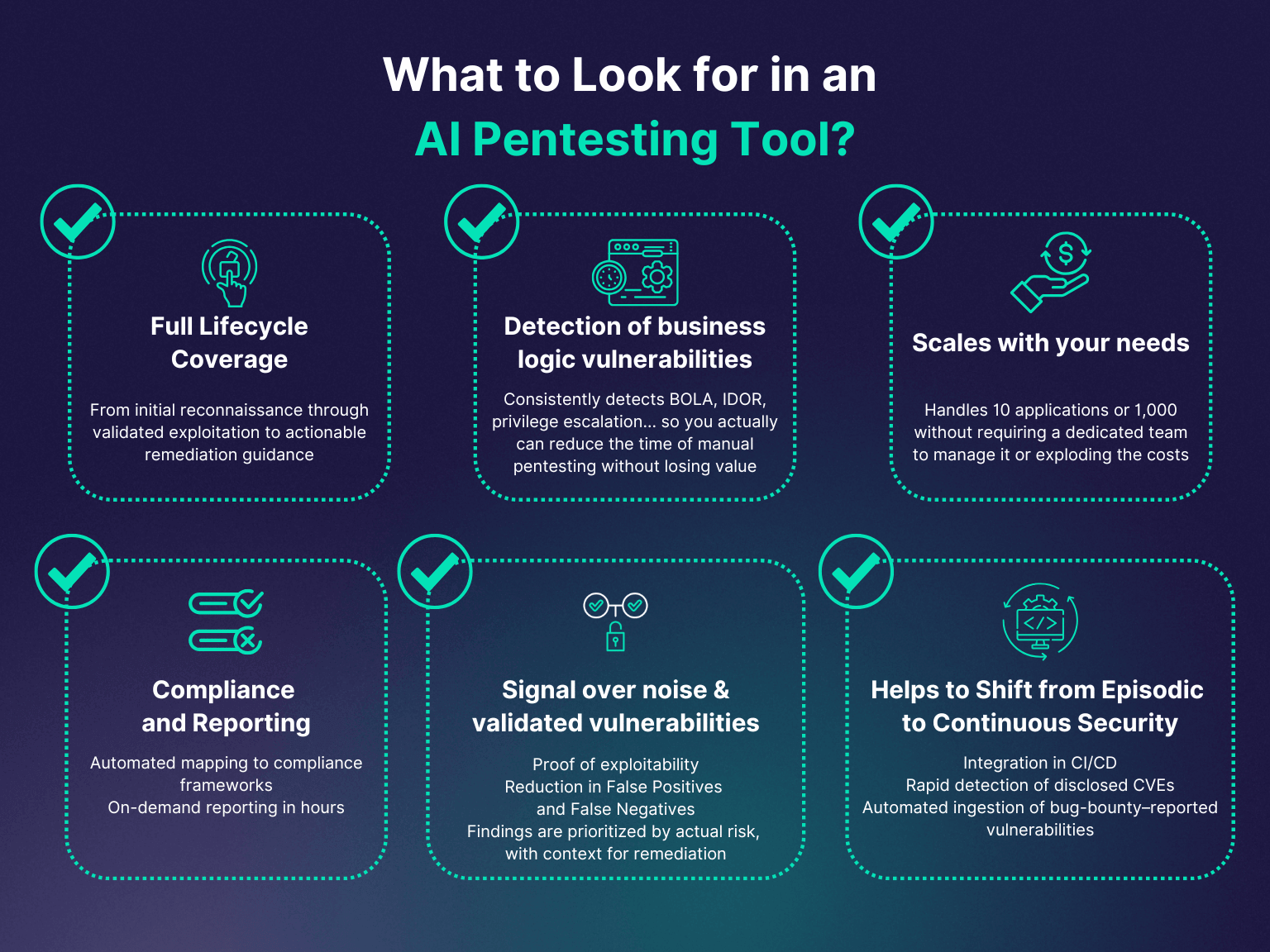
While each platform offers a unique set of features, several common themes emerge across the AI-powered pentesting landscape. Automated vulnerability scanning remains a core capability, but it’s now enhanced by AI algorithms that can identify a wider range of vulnerabilities with greater accuracy. Intelligent fuzzing, another common feature, uses AI to generate test cases that are more likely to uncover hidden flaws.
Exploit recommendation goes beyond simply identifying vulnerabilities; it suggests potential exploits that can be used to compromise the system. This can significantly accelerate the pentesting process and help testers understand the real-world impact of vulnerabilities. Reporting and remediation guidance are also crucial features, providing clear and actionable steps to fix identified weaknesses. The best platforms don’t just find problems; they help you solve them.
Integration with CI/CD pipelines is becoming increasingly important, enabling continuous security testing throughout the software development lifecycle. This allows developers to identify and fix vulnerabilities early in the process, reducing the risk of security incidents. These features aren’t just about automation; they’re about enabling a more proactive and integrated approach to security. They provide the capabilities needed to shift security left and build more secure applications from the ground up.
Consider the value of a platform that doesn’t just flag a cross-site scripting (XSS) vulnerability, but also suggests a specific code change to mitigate it. Or a tool that automatically generates a proof-of-concept exploit to demonstrate the impact of a vulnerability. These are the types of capabilities that truly differentiate AI-powered pentesting platforms.
AI and the Developer's Security Workflow
AI-powered pentesting tools are increasingly focused on integrating into the software development lifecycle (SDLC), empowering developers to take ownership of security. By identifying and fixing vulnerabilities early in the process, developers can prevent them from making their way into production. This "shift left" approach is considered best practice in modern application security.
Continuous security testing is a key enabler of this shift left approach. AI-powered tools can automate the process of scanning for vulnerabilities in code commits, pull requests, and deployments. This provides developers with immediate feedback on the security implications of their changes. Integrating these tools with existing development tools, such as IDEs and CI/CD systems, is essential for seamless adoption.
The benefits of this integration are significant. Developers can fix vulnerabilities more quickly and easily, reducing the cost and effort of remediation. Security becomes an integral part of the development process, rather than an afterthought. This leads to more secure applications and a stronger overall security posture. Platforms like StackHawk are specifically designed to embed security testing into the developer’s daily workflow.
Ultimately, the goal is to make security a shared responsibility, empowering developers to build secure applications without slowing down the development process. AI-powered pentesting tools are playing a critical role in enabling this paradigm shift.
Future Trends: What's Next?
The field of AI-powered pentesting is rapidly evolving, with several exciting trends on the horizon. Generative AI, the technology behind tools like ChatGPT, is beginning to be used for exploit creation. Generative AI can automatically generate code that exploits known vulnerabilities, potentially accelerating the attack process. However, this technology also raises ethical concerns.
More sophisticated AI models for vulnerability discovery are also under development. These models will be able to identify a wider range of vulnerabilities with greater accuracy, even in complex and obfuscated code. The integration of AI with threat intelligence feeds is another promising area of research. This will allow AI-powered tools to proactively identify and address emerging threats.
We can also expect to see increased automation of the entire pentesting process, from reconnaissance to exploitation and reporting. AI will likely play a key role in automating the creation of attack plans and the execution of complex attacks. The development of AI-powered virtual assistants that can guide penetration testers through the process is also a possibility.
These trends have the potential to significantly impact the cybersecurity landscape, making it more challenging for attackers and more difficult for defenders. Organizations will need to stay ahead of the curve by adopting the latest AI-powered security tools and investing in the skills and expertise needed to use them effectively.
Standout Platforms: A Deeper Dive
From the initial list of ten, StackHawk, Bright Security, and Invicti stand out for their distinct approaches and strong capabilities. StackHawk’s developer-centric design is a key differentiator. By integrating directly into the CI/CD pipeline, it empowers developers to take ownership of security and fix vulnerabilities early in the process. This approach is particularly valuable for organizations adopting DevOps practices.
Bright Security also focuses on developer empowerment, but it takes a slightly different approach. Its AI-powered engine provides contextualized security feedback to developers, helping them understand the impact of their code changes. This feedback is designed to be actionable and easy to understand, making it more likely that developers will address vulnerabilities promptly. It's a solid choice for organizations prioritizing developer experience.
Invicti, on the other hand, is a more comprehensive DAST solution geared towards larger enterprises. Its strength lies in its ability to handle complex web applications and its comprehensive coverage of vulnerabilities. While it may be more complex to set up and use than StackHawk or Bright Security, it offers a wider range of features and a higher level of assurance. It's a good option for organizations with mature security programs and complex security requirements.
These three platforms represent different approaches to AI-powered pentesting, each with its own strengths and weaknesses. The best choice for a particular organization will depend on its specific needs and priorities.


No comments yet. Be the first to share your thoughts!