Network Security
Dive into the world of network security, learn about its management, and understand the role of a network security engineer.
20 articles
Zero Trust Architecture Implementation Guide: Essential Steps for Modern Digital Security in 2026
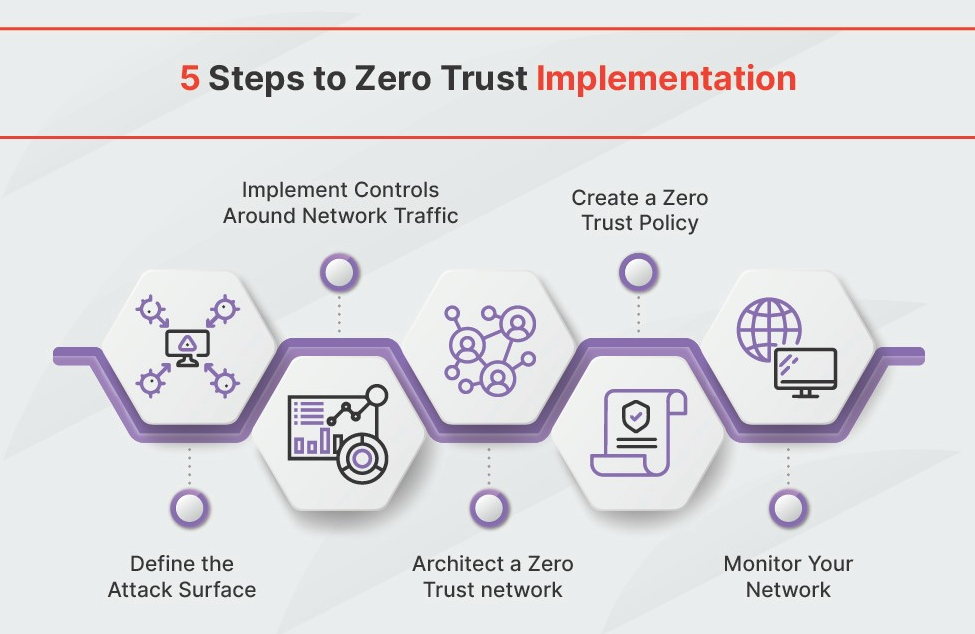
This guide details the shift from perimeter-based security to Zero Trust Architecture, crucial for protecting modern digital environments. It outlines NIST’s seven pillars, emphasizing identity as the new perimeter, and highlights the importance of microsegmentation and continuous monitoring for robust security. Successfully implementing Zero Trust requires addressing common roadblocks with a phased, strategic approach.
2026-05-04 13:16:20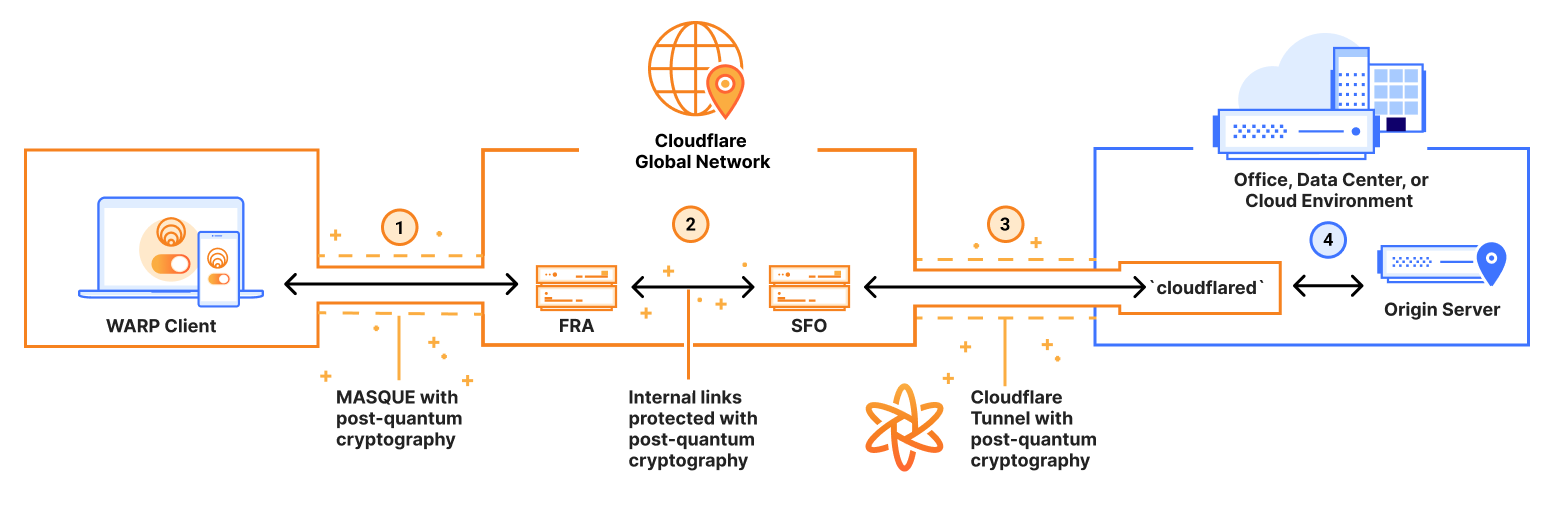
Quantum-Resistant Encryption: How to Prepare Your Network Security for the Post-Quantum Era in 2026
The emergence of quantum computing poses a significant threat to current encryption methods, necessitating a shift to post-quantum cryptography (PQC). Organizations must begin preparing now, leveraging NIST’s new standards and adopting a phased migration strategy to protect sensitive data in the coming years. Prioritizing crypto-agility and updating hardware security modules are essential steps in this transition.
2026-05-04 08:07:12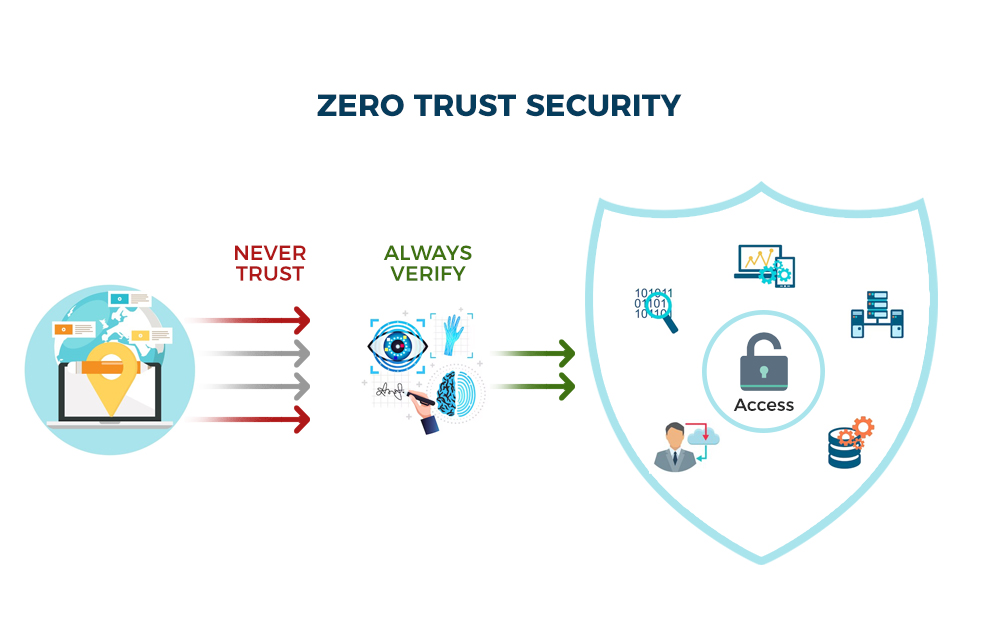
Zero Trust Network Security Architecture: Complete Implementation Guide for 2026
Zero Trust Network Architecture is a modern security framework shifting away from perimeter-based defenses to a 'never trust, always verify' approach. This guide details practical implementation strategies, drawing from DoD best practices, and emphasizes the importance of identity, microsegmentation, and continuous monitoring to mitigate evolving cyber threats. Organizations should prepare for increased automation and AI-driven security solutions in Zero Trust by 2026.
2026-05-04 07:18:35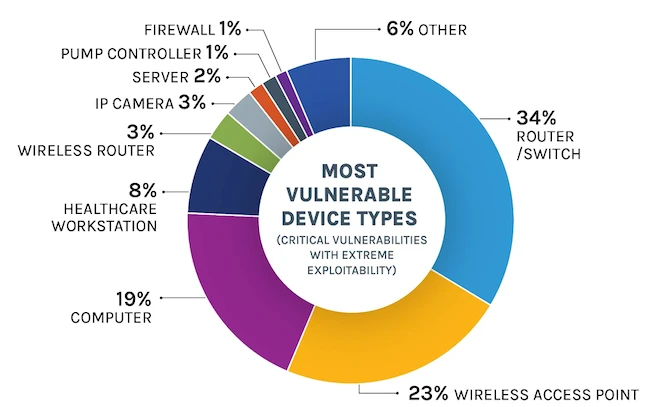
Critical Security Vulnerabilities in Popular IoT Devices: May 2026 Report
The May 2026 report reveals a continued crisis in IoT security, with vulnerabilities persisting across consumer and industrial devices. Weaknesses in SDKs and supply chains exacerbate the problem, while the potential for devastating consequences in critical infrastructure makes industrial IoT a prime target. Regular penetration testing is highlighted as a crucial, yet often neglected, mitigation strategy.
2026-05-04 01:26:10
Zero Trust Network Security Implementation Guide: 2026 Best Practices
This guide details the implementation of Zero Trust Network Security, moving beyond the hype to focus on practical best practices. It emphasizes verifying every user and device, leveraging microsegmentation to contain threats, and continuously monitoring network activity. Adopting a phased approach is key to successfully integrating Zero Trust principles into a modern security posture.
2026-05-04 01:17:08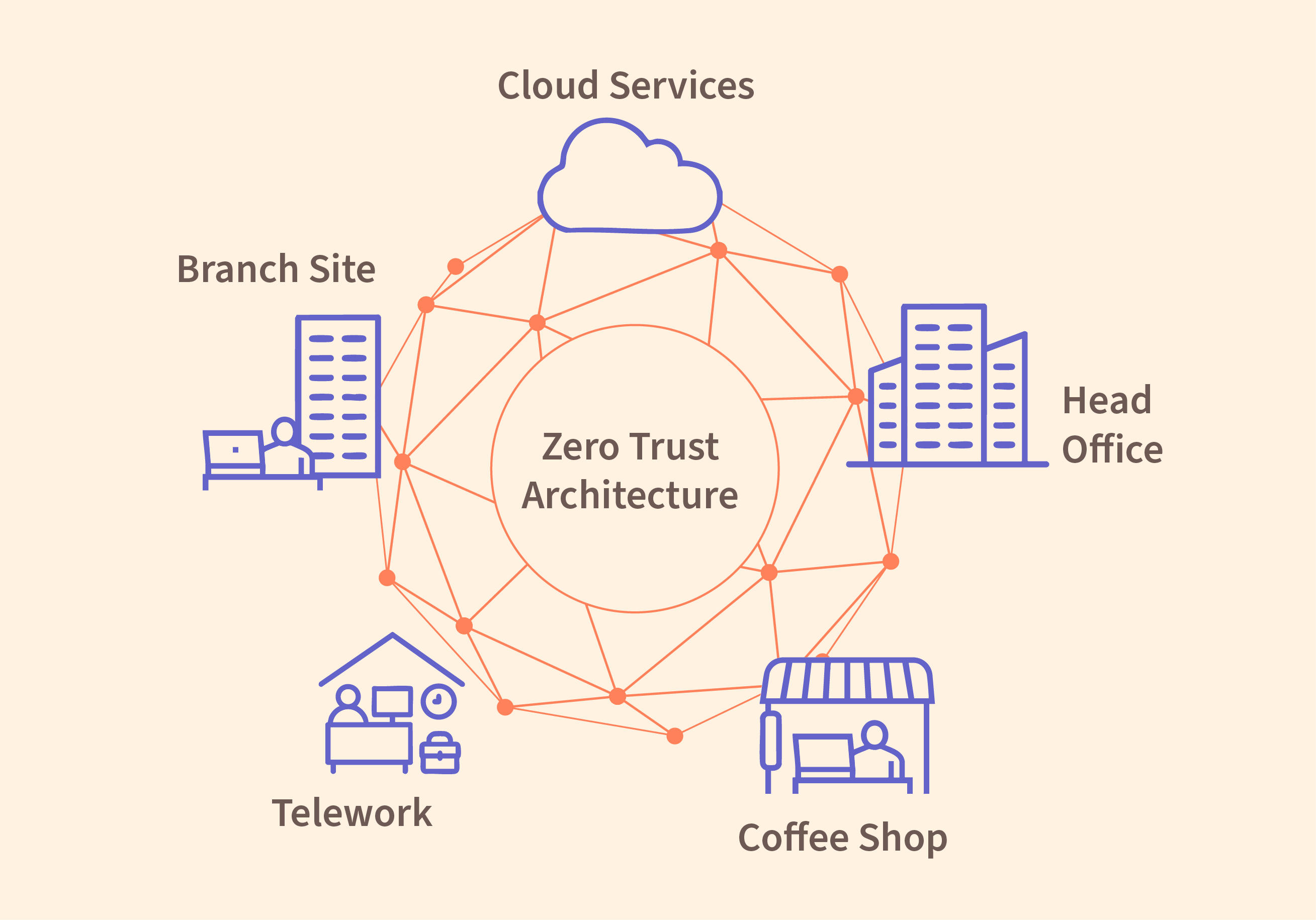
Zero Trust Architecture Implementation: Essential Security Framework for Remote Work in 2026
Zero Trust Architecture is rapidly becoming essential for securing modern, remote-first organizations. This framework shifts security focus from network location to user and device identity, requiring continuous verification and granular access control. Implementing ZTA, guided by the NIST framework, is vital for mitigating risks in today's evolving threat landscape.
2026-04-14 15:28:50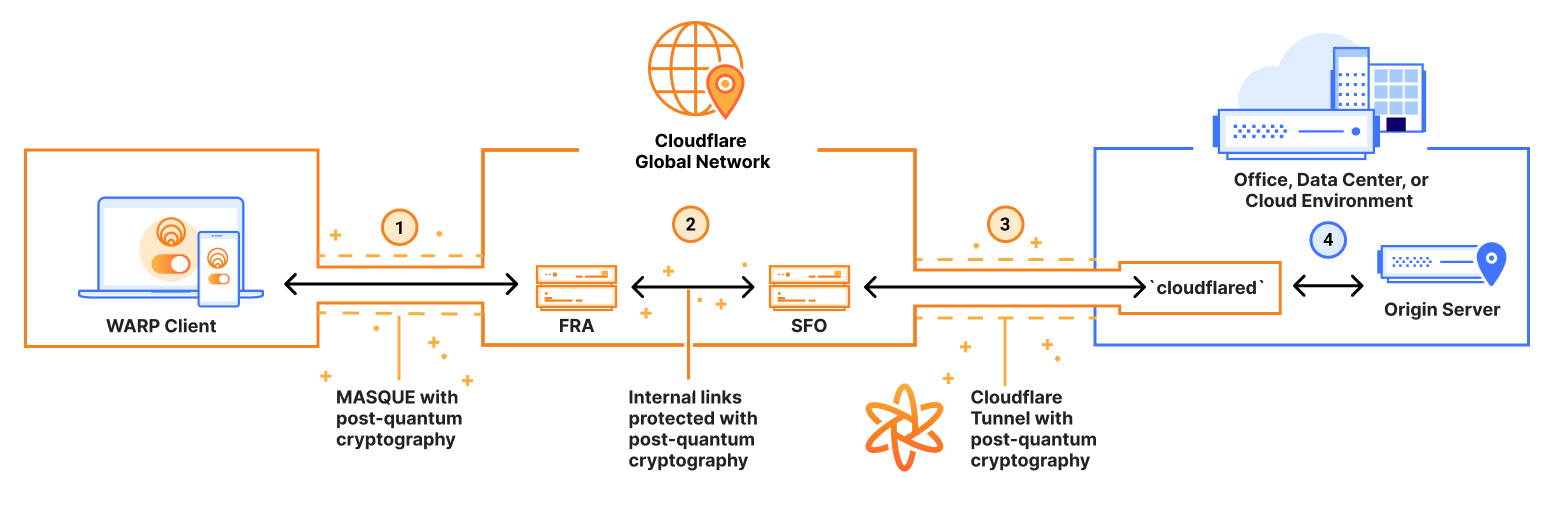
Quantum-Resistant Cybersecurity: How to Prepare Your Network for Post-Quantum Threats in 2026
The rise of quantum computing poses a significant threat to current encryption methods, demanding proactive preparation. Organizations must begin inventorying their cryptographic systems and planning for migration to NIST-standardized Post-Quantum Cryptography (PQC) algorithms, with a critical timeframe around 2026, and recognize this is an ongoing process.
2026-04-14 13:08:20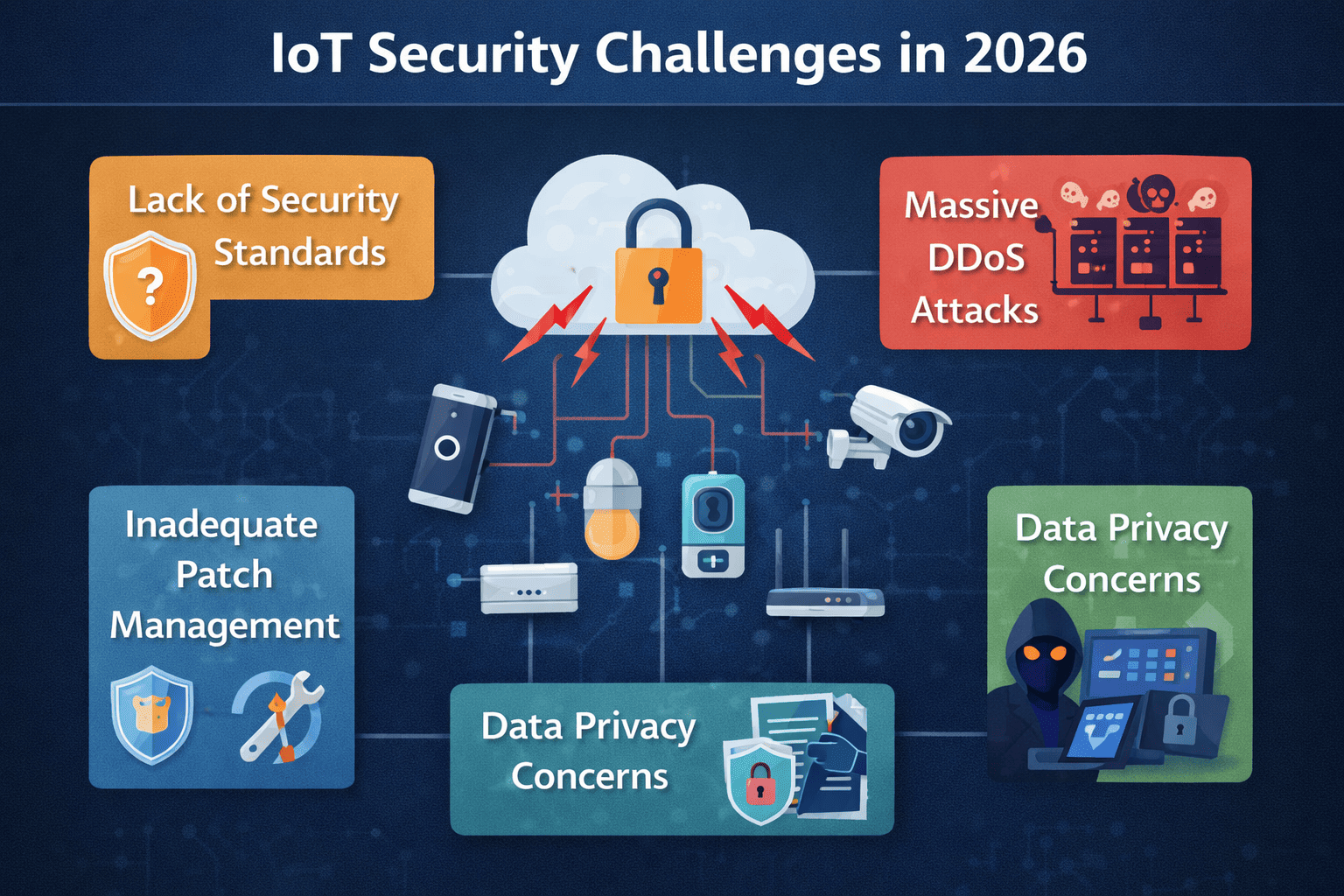
Critical IoT Security Vulnerabilities Exposed in 2026: Protection Strategies That Work
The Internet of Things is facing a surge in security vulnerabilities stemming from expanding attack surfaces, weak supply chains, and insecure configurations. Organizations must adopt layered mitigation strategies, including robust authentication, secure updates, and network segmentation, to protect their IoT deployments. Ignoring these risks could lead to significant data breaches and operational disruptions.
2026-04-14 12:46:10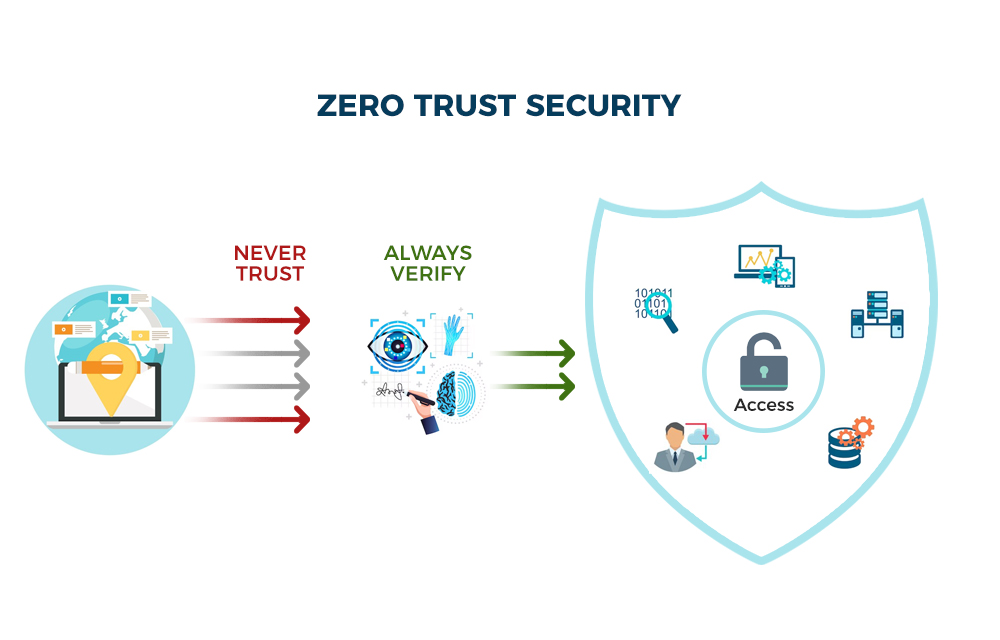
Zero-Trust Network Security Architecture: Implementation Strategies for 2026
This article details the evolving landscape of Zero Trust Network Architecture, moving beyond traditional perimeter security. It highlights implementation strategies, including microsegmentation, continuous monitoring, and multi-cloud considerations, while also outlining common pitfalls and projecting the state of ZTNA by 2026. The DoD’s approach serves as a key example of large-scale ZTNA adoption.
2026-04-14 12:26:26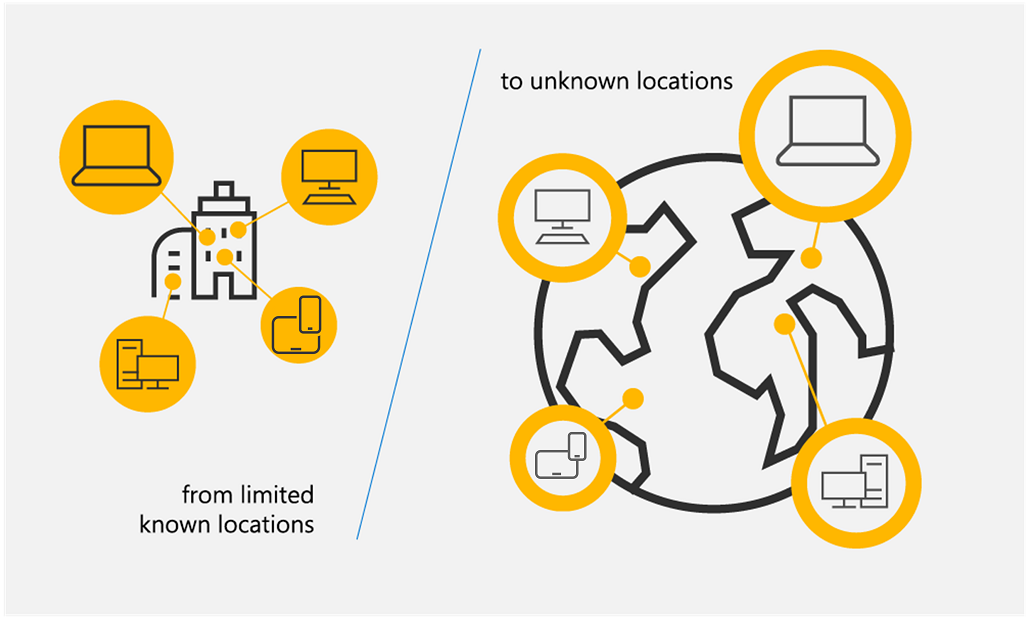
Zero Trust Architecture Implementation Guide: Complete Security Framework for Remote Work Environments in 2026
This guide details the implementation of a Zero Trust Architecture (ZTA) framework, essential for securing modern remote work environments. It emphasizes a 'never trust, always verify' approach, outlining key components like microsegmentation, data encryption, and continuous monitoring. The guide advocates for a phased implementation to ensure a smooth transition and maximize security benefits.
2026-04-14 09:26:31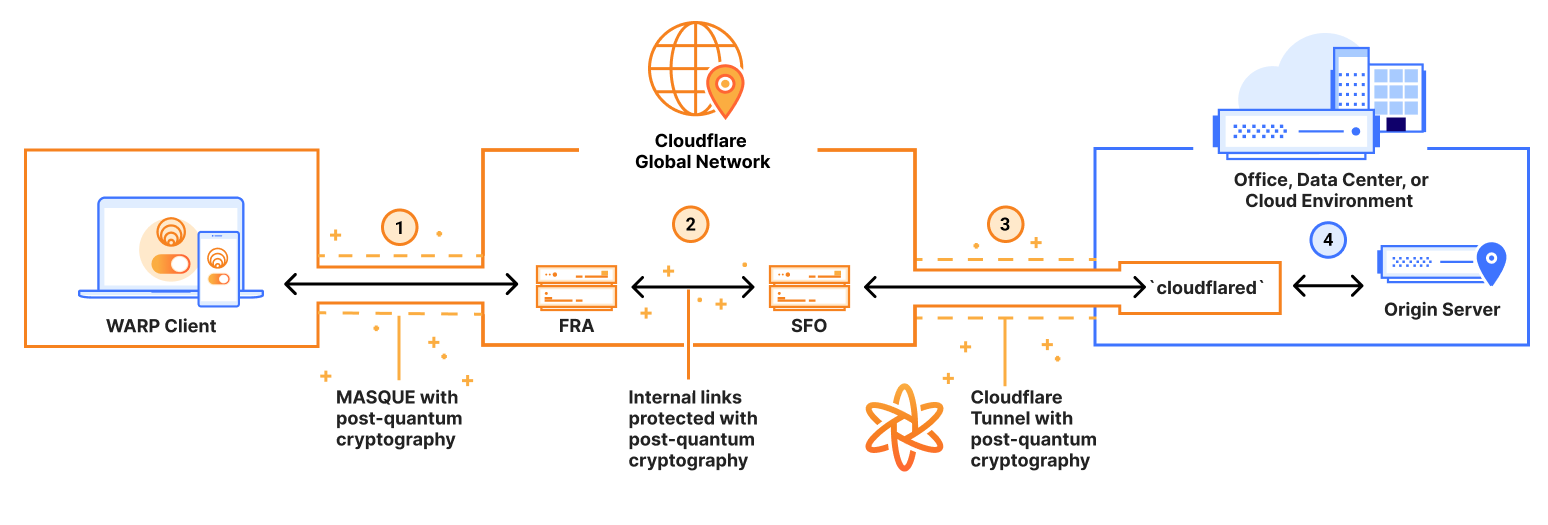
Quantum-Resistant Encryption: How to Prepare Your Network Security for Post-Quantum Threats in 2026
The emergence of quantum computing necessitates a shift to quantum-resistant encryption to protect sensitive data. Organizations must begin preparing now for the NIST-recommended PQC algorithms, with a target implementation timeframe of 2026, focusing on assessment, migration planning, and robust key management practices.
2026-04-14 07:05:55
IoT Security Vulnerabilities Exposed: Critical Digital Security Flaws Every Organization Must Address in 2026
IoT devices are increasingly vulnerable to cyberattacks due to expanding attack surfaces, weak security protocols, and supply chain risks. Organizations must prioritize robust security measures, including strong authentication, data encryption, and proactive network monitoring, to protect themselves from growing IoT-related threats by 2026.
2026-04-14 06:34:26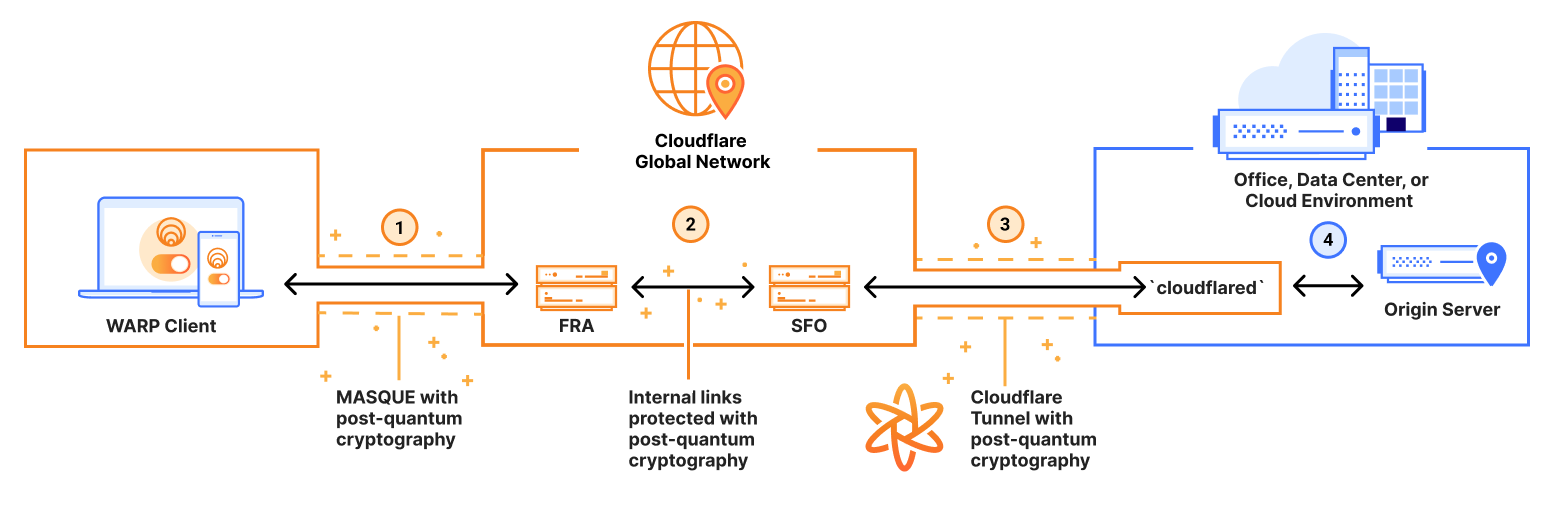
Quantum Computing vs Cybersecurity: Preparing Your Network for Post-Quantum Encryption in 2026
Quantum computing poses a significant threat to current encryption methods, with the potential to break widely used algorithms like RSA and ECC. NIST is leading the charge in standardizing post-quantum cryptography, and organizations must proactively audit their networks and begin planning for implementation by the anticipated 2026 timeline to maintain data security.
2026-04-14 06:14:42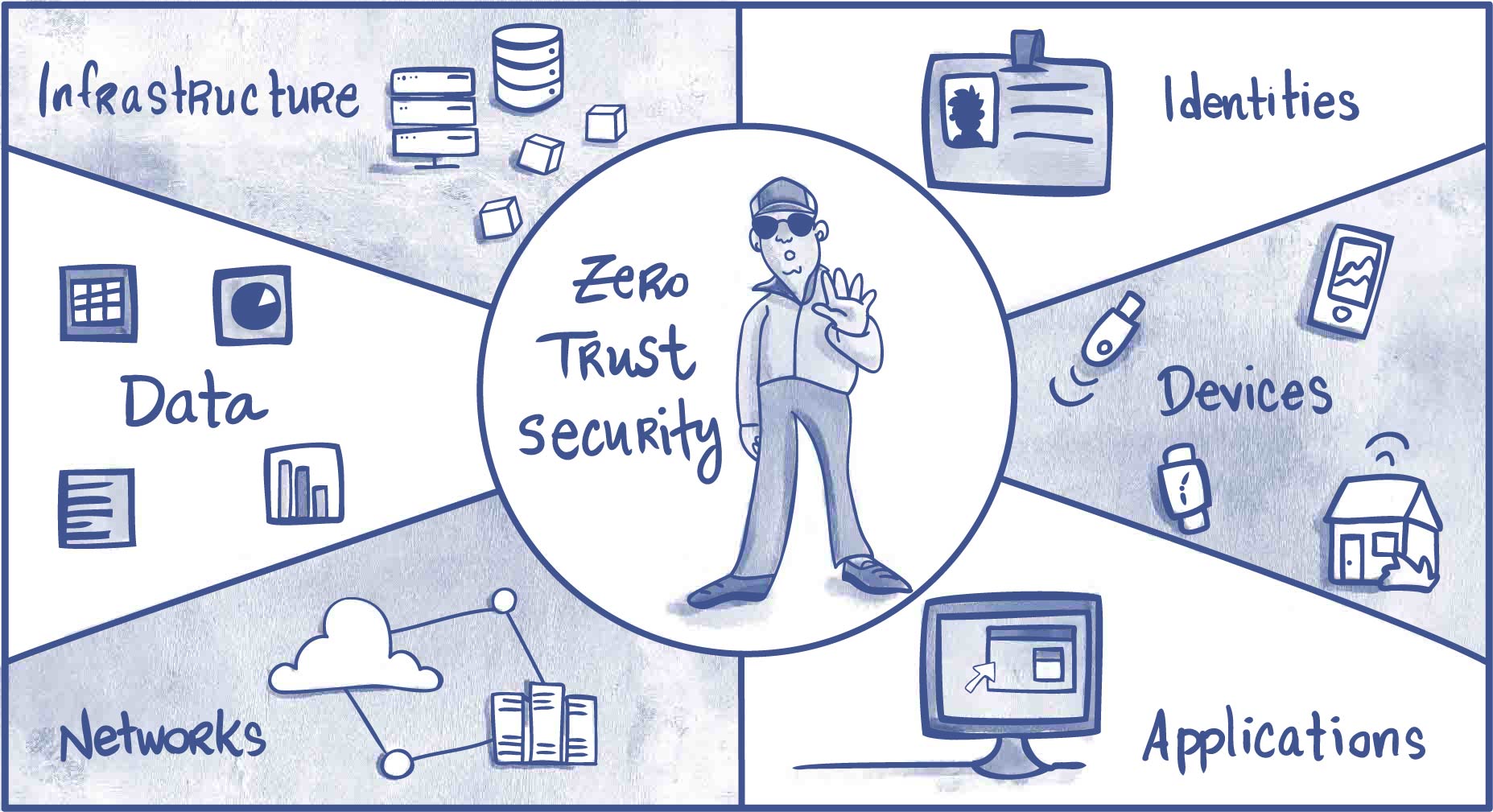
Zero Trust Architecture Best Practices: Complete Security Framework Implementation for 2026 Enterprise Networks
This article details the principles and implementation of Zero Trust Architecture (ZTA), moving beyond the hype to provide a practical framework for modern enterprise security. It leverages the NIST 800-207 blueprint and real-world examples like the DoD's phased implementation, emphasizing identity, microsegmentation, and data protection as key components for securing networks in 2026 and beyond.
2026-04-14 03:34:47
Post-Quantum Cryptography Implementation Guide: Securing Networks Against Quantum Computing Threats in 2026
This guide details the importance of preparing for the quantum computing threat by transitioning to Post-Quantum Cryptography (PQC). It outlines a phased migration strategy, emphasizing vulnerability assessment, hybrid implementations, and performance considerations. Organizations should begin planning now to secure their networks against future quantum attacks, with NIST standardization expected to finalize in 2026.
2026-04-14 03:25:35
Wi-Fi at War: How Air Force Cyber Security Innovations Influence Commercial Practices
Explore the crossover of Air Force cyber security into the business realm. From military-grade encryption to Zero Trust models, our latest post offers a practical checklist for robust cyber defense, insights into AES, and the role of ISACs. Elevate your companys security now.
2024-03-22
The Zero Trust Model: Rethinking Network Security in the Age of Cyber Threats
Explore the essentials of the Zero Trust Model and learn how to fortify your network against cyber threats. This post delves into the crucial elements of Zero Trust architecture, offers a step-by-step guide for transitioning, and answers your FAQs on compliance. Plus, get a sneak peek at AIs role in the future of network security.
2024-03-06
The Rise of Quantum Computing: Implications for Network Security Testing
Dive into the world of quantum computing and its profound effects on network security. Our post compares traditional vs. quantum encryption, charts the evolution of cryptography standards, and tests your knowledge on quantum-resistant methods. Plus, explore the pivotal role of Quantum Key Distribution in safeguarding data. Get answers to pressing FAQs and stay ahead in the cybersecurity game.
2024-01-18
Next-Gen Network Security: How AI is Revolutionizing Intrusion Detection Systems
Explore the transformative power of AI in network security with our deep dive into advanced intrusion detection systems. Learn how AI reduces false positives, fends off sophisticated cyber threats, and integrates with cybersecurity frameworks. Gain insights from expert analyses and case studies, and envision the future of cybersecurity with quantum computing and blockchain.
2024-01-02
Securing the Virtual Gates: An Insight into Managed Network Security
Explore the world of Managed Network Security with our in-depth analysis. Learn about its importance in today's digital landscape, its core components, implementation process, and future trends. Get insights from a successful case study and test your knowledge with our interactive quiz.
2023-09-14
Demystifying the Role of a Network Security Engineer in Today’s Digital Landscape
Dive into the crucial role of Network Security Engineers in our digital age. Understand their responsibilities, the skills required, and the growing demand for this profession. This post even includes a step-by-step guide to kickstart your career in Network Security. Stay secure in our digital world!
2023-09-06
Network Security Monitoring: Unveiling Its Significance in Real-Time Threat Detection
Explore the world of Network Security Monitoring with our in-depth guide. Learn its vital role in real-time threat detection, understand its working mechanism, and appreciate its significance in cybersecurity. Gain insights on best practices to enhance your network's security.
2023-08-29
A Layman's Guide to WiFi Security Types: Understanding the Basics
Dive into the basics of WiFi security with our comprehensive guide. Understand different security types like WEP, WPA, and WPA3, and learn why some are more secure than others. Test your knowledge with quizzes, compare security strengths, and learn how to upgrade your own WiFi security!
2023-08-20
Network Security Engineer: Roles, Responsibilities, and Career Path
Explore the role of a Network Security Engineer: responsibilities, required skills, career path, job opportunities and tips for success. Understand the importance of network security in today's digital world.
2023-08-18
Cloud Vs Network Security: Which is More Important for Your Business?
Delve into the intricate world of cloud and network security in our latest blog post. Uncover their roles in today's digital business landscape, their unique features, and how they differ. We'll guide you through which is more crucial for your business and provide practical strategies for securing your digital assets. Stay vigilant, stay secure.
2023-07-27
Network Penetration Testing: A Deep Dive into Keeping Networks Secure
Explore the depth of Network Penetration Testing to secure your digital world. Learn the basics, techniques, and importance of this method in cybersecurity. Understand how to choose the right service for comprehensive network protection.
2023-07-07
Understanding Network Security Monitoring: Your First Line of Defense
Explore the essentials of Network Security Monitoring (NSM) in this comprehensive guide. Learn its importance, basics, tools, role in penetration testing, and best practices to fortify your digital world.
2023-07-07
The Air Force Cybersecurity: A Look into Military Grade Security
Explore military-grade cybersecurity with a focus on the Air Force. Learn about their robust security measures, penetration testing, secure protocols, and high-level network security to safeguard national digital assets.
2023-07-06
Weak Wi-Fi Security: Understanding and Fixing the Problem
Explore the intricacies of Wi-Fi security, understand common vulnerabilities, and learn effective fixes. Dive into penetration testing, network security improvement, and enterprise Wi-Fi security enhancement. Secure your digital world with HackerDesk.
2023-07-06