Zero trust is more than a buzzword
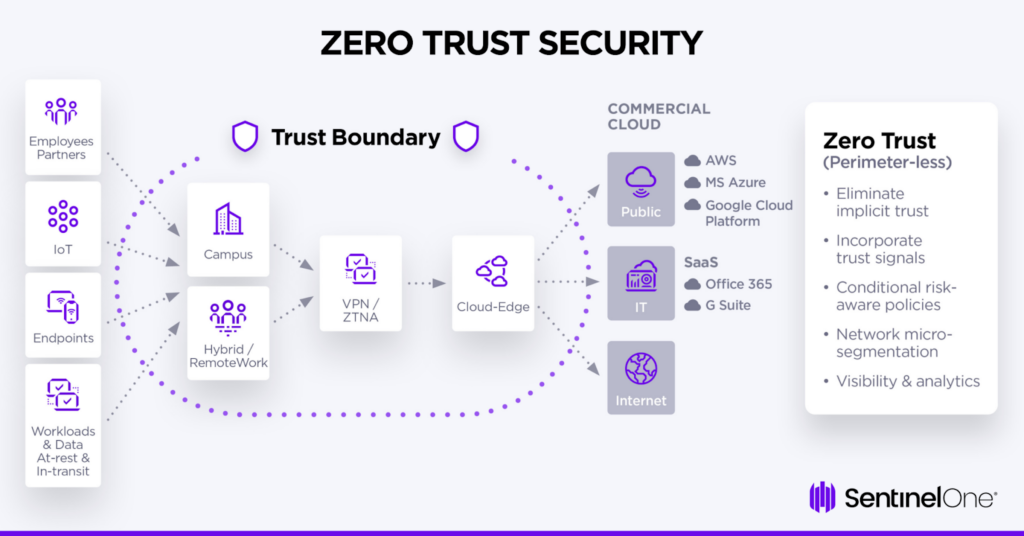
Zero Trust Architecture (ZTA) feels like a constant topic in cybersecurity right now, but it’s more than just the latest trend. As defined by NIST Special Publication 800-207, ZTA isn’t a single product you buy, but a security framework built on the principle of "never trust, always verify." This means no user or device, whether inside or outside the network perimeter, is automatically trusted.
Traditional security assumes everything inside the network is safe. That doesn't work anymore. Cloud services and remote work mean there is no longer a clear perimeter to defend. Most successful breaches now involve attackers moving laterally once they've stolen a single set of credentials.
ZTA addresses this by eliminating implicit trust. Every access request is authenticated, authorized, and continuously validated. It’s a fundamental shift in how we approach security, moving from a castle-and-moat model to a more granular, identity-centric approach. It's a necessary evolution, acknowledging that trust is a vulnerability.
The core components of zero trust
Implementing a Zero Trust Architecture isn’t about flipping a switch; it’s about building a series of interconnected security controls. NIST outlines several core pillars, all working together to create a more resilient security posture. These components aren't installed in sequence, but rather layered and refined over time.
Identity and Access Management (IAM) is foundational. This goes beyond simple usernames and passwords, incorporating multi-factor authentication (MFA) and least privilege access. Device security ensures only authorized and compliant devices can access resources. Network micro-segmentation divides the network into smaller, isolated segments, limiting the blast radius of a potential breach.
Application security focuses on securing the applications themselves, using techniques like code reviews and vulnerability scanning. Data security ensures sensitive data is protected both at rest and in transit, leveraging encryption and data loss prevention (DLP) policies. These pillars aren’t independent; strong IAM informs network segmentation, and data security relies on application-level controls.
The 2026 Penetration Testing Checklist
This checklist provides a starting point for penetration testing a Zero Trust Architecture. It’s categorized by key ZTA components, with specific test cases to validate the effectiveness of your security controls. Remember, this isn’t an exhaustive list, and testing should be tailored to your specific environment and risk profile.
Zero Trust isn't a project you finish. You have to test these controls monthly because configurations drift and new bypasses for MFA or service mesh protocols emerge constantly.
The following tests assume a level of access has already been gained – perhaps through a phishing campaign or compromised credential. The focus is on what an attacker can do after initial access.
- Try to escalate privileges using a standard employee's compromised credentials.
- Run phishing simulations to see if users will provide MFA codes or if SIM swapping can bypass your current provider.
- Identity: Test conditional access policies (e.g., access from untrusted locations).
- Identity: Attempt to exploit vulnerabilities in identity federation or SSO integrations.
- Device: Attempt to access resources from non-compliant devices.
- Device: Bypass device posture checks (e.g., outdated antivirus software).
- Device: Test the effectiveness of mobile device management (MDM) controls.
- Network: Attempt to move laterally between network segments.
- Network: Test firewall rules and access control lists (ACLs).
- Network: Validate micro-segmentation policies.
- Network: Identify and exploit weaknesses in software-defined networking (SDN) configurations.
- Application: Test for vulnerabilities in web applications (e.g., SQL injection, XSS).
- Application: Attempt to bypass application-level access controls.
- Application: Test the security of APIs.
- Data: Attempt to exfiltrate sensitive data.
- Data: Validate access controls to sensitive data stores.
- Data: Test data loss prevention (DLP) policies.
- Data: Test data masking and tokenization techniques.
- Data: Attempt to access encrypted data without proper authorization.
- Data: Verify encryption at rest and in transit.
Breaking identity and access controls
Identity is the cornerstone of a Zero Trust Architecture, making thorough testing of IAM controls paramount. Beyond basic credential stuffing, pentesters should focus on techniques that bypass or circumvent authentication mechanisms. This includes attempting to escalate privileges after gaining initial access with compromised credentials.
Multi-Factor Authentication (MFA) is a critical control, but it’s not foolproof. Testing should include phishing campaigns designed to steal MFA codes, as well as attempts to exploit vulnerabilities in MFA implementations. SIM swapping attacks, where an attacker ports a victim’s phone number to a new SIM card, are also a growing threat.
Conditional Access policies, which restrict access based on factors like location and device posture, should be rigorously tested. Privilege Access Management (PAM) solutions, which control access to privileged accounts, also need to be validated. Finally, testing identity federation and SSO integrations is crucial, as these can introduce new attack vectors.
Testing micro-segmentation and lateral movement
Micro-segmentation is a key tenet of ZTA, limiting the blast radius of a breach by isolating network segments. Penetration testing must validate that these segments are truly isolated and that lateral movement is difficult. The goal is to determine if an attacker, having compromised a single endpoint, can access other critical systems.
Testing should focus on firewall rules, access control lists (ACLs), and software-defined networking (SDN) configurations. Pentesters should attempt to identify misconfigurations or vulnerabilities that allow them to bypass segmentation controls. This often involves mapping network connectivity and identifying potential pathways for lateral movement.
A critical aspect is testing for 'east-west' traffic vulnerabilities – attacks that move laterally within the network. This can be achieved by attempting to establish connections between systems in different segments and monitoring network traffic for unauthorized communication. A table summarizing network segment access policies can be helpful during this process:
- Segment A -> Segment B: Denied
- Segment A -> Segment C: Allowed (specific ports)
- Segment B -> Segment C: Denied
Data Security and Encryption Verification
Protecting sensitive data is a primary goal of ZTA. Penetration testing should verify that data is adequately protected both at rest and in transit. This includes validating encryption algorithms and key management practices. Testing should also focus on data loss prevention (DLP) policies.
Pentesters should attempt to exfiltrate sensitive data using various techniques, such as uploading it to cloud storage or sending it over unencrypted channels. Access controls to sensitive data stores, such as databases and file servers, should be rigorously tested to ensure only authorized users have access.
Data masking and tokenization techniques, which replace sensitive data with non-sensitive substitutes, should also be validated. Ensure that these techniques are correctly implemented and that the original data cannot be easily recovered. It’s also important to verify that encryption keys are properly protected and rotated regularly.
Network Segmentation Effectiveness Evaluation - Penetration Testing Checklist
| Test Case | Expected Result | Actual Result | Pass/Fail | Remediation Steps |
|---|---|---|---|---|
| Lateral Movement Attempt (East-West Traffic) | Traffic between segmented zones is blocked or heavily restricted, requiring re-authentication for access. | Successful lateral movement observed from a compromised system in Zone A to a system in Zone B without re-authentication. | Fail | Review and strengthen micro-segmentation policies. Implement stricter access controls and monitoring between zones. Investigate potential firewall misconfigurations. |
| Access to Critical Data Asset | Access to critical data assets is limited to authorized users and applications, even from within the network. | Unauthorized access to a critical database was achieved from a compromised workstation within the same network segment. | Fail | Implement least privilege access controls. Enhance data encryption both in transit and at rest. Review and refine Identity and Access Management (IAM) policies. |
| Compromised Endpoint Communication | A compromised endpoint should be unable to communicate with command-and-control (C2) servers, even if the C2 server is hosted within the network. | Compromised endpoint successfully established communication with a known C2 server located on an internal network segment. | Fail | Implement egress filtering to block known malicious domains and IP addresses. Deploy endpoint detection and response (EDR) solutions to identify and block C2 communication. |
| Application-to-Application Trust | Communication between applications should be explicitly authorized and verified, not implicitly trusted. | Application A was able to directly access resources on Application B without proper authentication or authorization. | Fail | Implement application-level segmentation and mutual TLS authentication. Enforce strict API access controls. |
| Policy Enforcement Consistency | Zero Trust policies are consistently enforced across all network segments and access points. | Inconsistent policy enforcement observed; a policy blocking access in one segment was not enforced in another. | Fail | Centralize policy management and enforcement. Regularly audit policies for consistency and accuracy. Automate policy deployment and updates. |
| Microsegmentation Bypass | Attempts to bypass microsegmentation controls should be prevented. | Bypass of microsegmentation controls achieved through manipulation of network protocols. | Fail | Strengthen network security controls, including intrusion detection and prevention systems (IDPS). Regularly update security patches and firmware. |
| Internal Reconnaissance | Internal reconnaissance attempts should be limited and detectable. | Extensive internal reconnaissance was conducted without triggering alerts or detection mechanisms. | Fail | Implement network traffic analysis (NTA) and intrusion detection systems (IDS) to detect reconnaissance activity. Enhance logging and monitoring capabilities. |
Illustrative comparison based on the article research brief. Verify current pricing, limits, and product details in the official docs before relying on it.
Automation and Continuous Verification
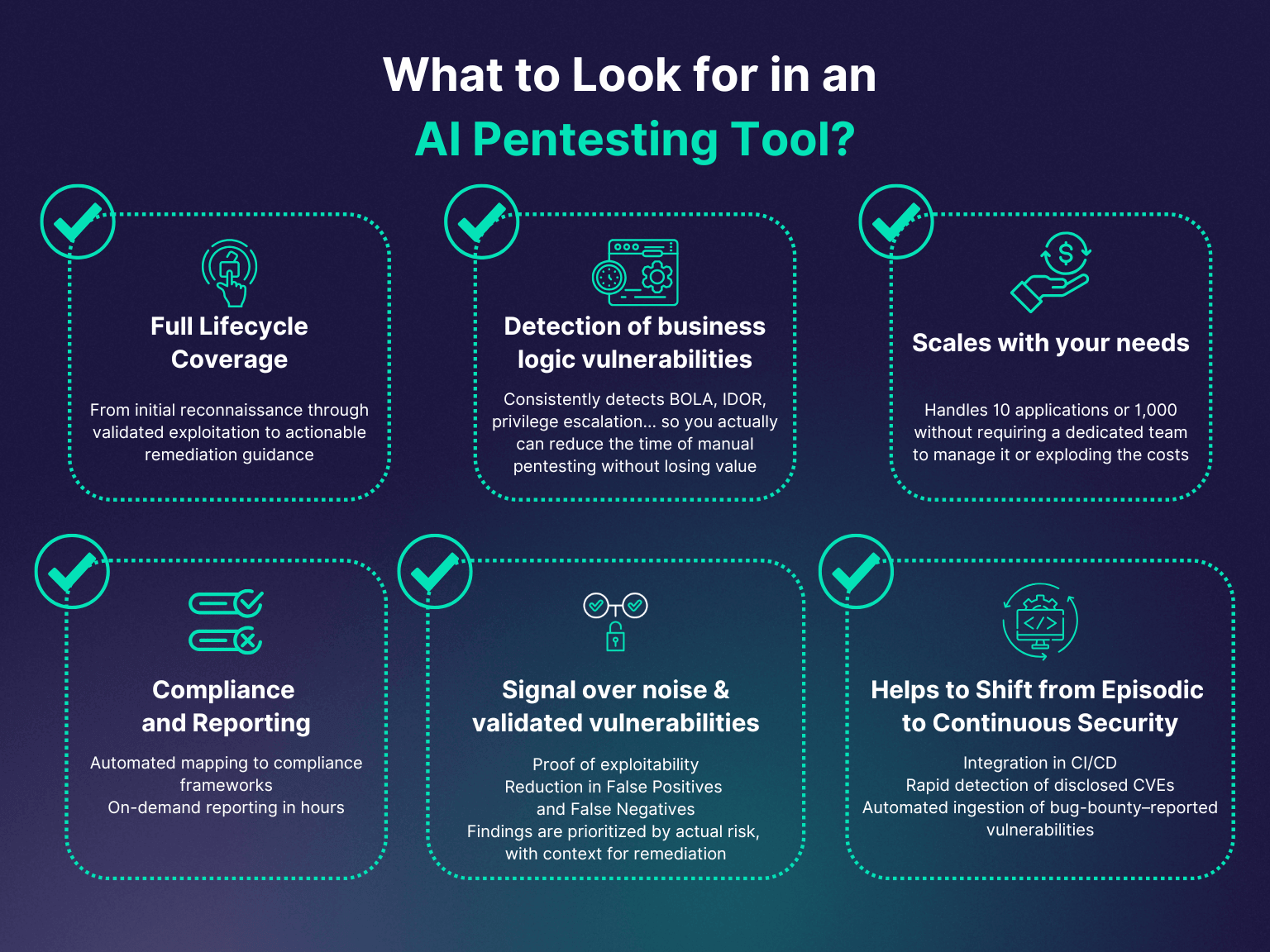
Manual penetration testing is valuable, but it’s not scalable. Automation plays a critical role in ZTA penetration testing, enabling continuous monitoring and verification of security controls. Vulnerability scanners can automatically identify known vulnerabilities in systems and applications.
Intrusion detection systems (IDS) and security information and event management (SIEM) systems can be used to detect and respond to malicious activity. These tools can be integrated with ZTA controls to provide real-time visibility into the security posture. Automating tests for common vulnerabilities and misconfigurations can significantly reduce the time and effort required to maintain a secure environment.
Continuous verification is the only way to catch misconfigured S3 buckets or expired certificates before they become entry points. Automated scanning handles the routine checks, leaving manual testing for complex logic flaws.


No comments yet. Be the first to share your thoughts!