The quantum threat is closer than it looks
For decades, our digital security has relied on the mathematical difficulty of certain problems. Algorithms like RSA and ECC, used to protect everything from online banking to government communications, depend on the fact that it takes classical computers an impractically long time to factor large numbers or solve the discrete logarithm problem. However, the emergence of quantum computing changes everything. Quantum computers, leveraging the principles of quantum mechanics, can solve these problems efficiently.
The most concerning algorithm for current cryptography is Shor’s algorithm, developed by Peter Shor in 1994. It demonstrates how a quantum computer could break RSA and ECC, rendering them useless. This isn’t a theoretical risk for the distant future; the timeline for a cryptographically relevant quantum computer is shrinking. While building such a machine is incredibly challenging, significant progress is being made. Estimates vary, but many experts believe a quantum computer capable of breaking widely used encryption could exist within the next decade.
If encryption breaks, we lose everything from private bank records to state secrets. I'm most worried about 'harvest now, decrypt later' attacks. Hackers are already vacuuming up encrypted data today, betting they can crack it in a few years with a quantum machine. If we wait until the hardware exists to start switching our math, we've already lost.
NIST's new standards for post-quantum security
Recognizing the threat, the National Institute of Standards and Technology (NIST) launched a post-quantum cryptography (PQC) standardization process in 2016. This ambitious project aimed to identify and standardize cryptographic algorithms that are resistant to attacks from both classical and quantum computers. After a rigorous multi-round evaluation process, NIST announced its first set of finalized PQC standards in July 2022. These standards represent a major step towards securing our digital infrastructure against the quantum threat.
Four algorithms were initially selected: CRYSTALS-Kyber for key-establishment, CRYSTALS-Dilithium and FALCON for digital signatures, and SPHINCS+ as a backup signature scheme. Key-establishment algorithms, like Kyber, are used to securely exchange cryptographic keys between parties. Digital signatures, provided by Dilithium, Falcon, and SPHINCS+, are used to verify the authenticity and integrity of digital documents. The selection wasn't arbitrary; each algorithm underwent extensive scrutiny by the cryptographic community.
These algorithms employ different mathematical approaches to achieve quantum resistance. CRYSTALS-Kyber and CRYSTALS-Dilithium are based on lattice problems, which are considered hard to solve even with quantum computers. FALCON also relies on lattices but uses a different structure. SPHINCS+ takes a fundamentally different approach, relying on hash functions, which are well-understood cryptographic primitives with a strong security record. The diversity in approaches is intentional, providing resilience against potential breakthroughs in attacking a specific mathematical structure.
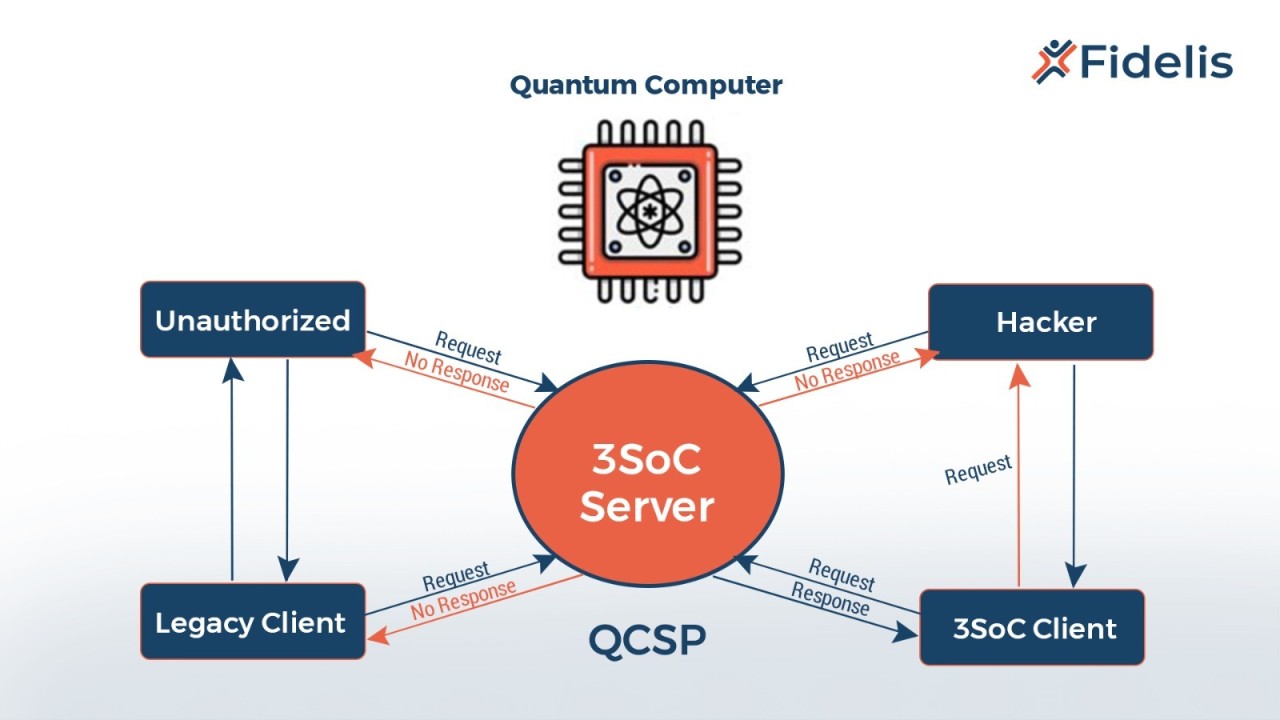
How Kyber handles key exchange
CRYSTALS-Kyber is the first standardized algorithm for general-purpose key encapsulation. In simpler terms, it’s designed to securely exchange cryptographic keys over a network, like during a TLS handshake. It operates by creating a shared secret key that only the communicating parties know, even if an eavesdropper intercepts the exchange. This shared secret is then used to encrypt and decrypt subsequent communications.
Kyber’s strengths lie in its speed and relatively small key sizes, making it practical for a wide range of applications. Compared to some other PQC candidates, Kyber requires less computational power and network bandwidth. However, it wasn’t without initial concerns. During the standardization process, researchers identified potential vulnerabilities related to side-channel attacks, which exploit information leaked during the execution of the algorithm. These vulnerabilities were addressed through careful implementation and parameter selection.
Kyber works with TLS 1.3, and you can already find it in libraries like OpenSSL. It isn't a simple drop-in replacement, though. You'll need to test how the larger key sizes affect your specific handshake speeds before rolling it out to production.
- verify your current key exchange methods
- check for TLS 1.3 compatibility in your stack
- Test with OpenSSL implementations
Choosing between Dilithium and Falcon
CRYSTALS-Dilithium and FALCON are the two standardized algorithms for digital signatures. They provide a way to verify the authenticity and integrity of digital documents or messages. Both are lattice-based, like Kyber, but differ in their specific approaches and performance characteristics. Dilithium is generally faster for signature generation, while Falcon produces smaller signatures.
Falcon’s compact signature sizes are particularly advantageous in bandwidth-constrained environments, such as IoT devices or blockchain applications. However, Falcon’s verification process is somewhat slower than Dilithium’s. The choice between Dilithium and Falcon often depends on the specific application requirements and the trade-offs between signature size and verification speed. Both algorithms offer multiple security levels, allowing users to choose the level of protection appropriate for their needs.
These algorithms are applicable wherever digital signatures are used today: software updates, code signing, secure email, and more. They are designed to be compatible with existing signature verification infrastructure, although some software updates will be necessary to support the new algorithms. The standardization of Dilithium and Falcon provides organizations with viable alternatives to traditional signature schemes like RSA and ECDSA.
SPHINCS+ as a hash-based backup
SPHINCS+ is a stateless hash-based signature scheme. Unlike Kyber, Dilithium, and Falcon, it doesn’t rely on complex mathematical structures like lattices. Instead, it’s based on the security of cryptographic hash functions, which are widely used and well-understood. This makes SPHINCS+ a conservative choice with strong security properties.
The primary advantage of SPHINCS+ is its resistance to a wide range of attacks, even if future breakthroughs are made in areas like lattice cryptography. However, it comes with significant drawbacks: large signature sizes and slower performance compared to the other standardized algorithms. Its signatures are substantially larger than those produced by Dilithium or Falcon.
I'd only use SPHINCS+ for niche cases like long-term archiving. The signatures are massive and slow, but because it doesn't use lattices, it's a great insurance policy if someone finds a shortcut to crack Kyber or Dilithium.
The mess of migrating old systems
Migrating to post-quantum cryptography is a complex undertaking. It’s not simply a matter of swapping out a few lines of code. It requires updating software libraries, hardware security modules (HSMs), and network protocols. Many systems rely on cryptographic algorithms that are deeply embedded in their infrastructure, making upgrades challenging and time-consuming. A phased approach is generally recommended.
A key concept in this transition is "crypto-agility" – the ability to quickly and easily switch between different cryptographic algorithms. Systems designed with crypto-agility in mind can adapt to new threats and standards more effectively. This involves abstracting the underlying cryptographic implementations and providing a flexible interface for selecting and configuring algorithms. Without crypto-agility, organizations will face significant hurdles when new vulnerabilities are discovered or standards evolve.
Hybrid approaches, where post-quantum algorithms are used alongside classical algorithms, are a practical way to mitigate risk during the transition. For example, a system could generate a digital signature using both ECDSA and Dilithium, providing both classical and quantum resistance. This ensures that the system remains secure even if one of the algorithms is compromised. These hybrid schemes add overhead, but provide a valuable safety net during the migration period.
NIST PQC Algorithm Comparison (as of Late 2023/Early 2024)
| Algorithm | Security Confidence | Performance | Implementation Complexity | Hardware Support |
|---|---|---|---|---|
| CRYSTALS-Kyber | Very High | Generally Fast | Moderate | Growing - some acceleration available |
| CRYSTALS-Dilithium | Very High | Moderate Speed | Moderate | Limited dedicated acceleration currently |
| Falcon | High | Fast - smaller signature sizes | Higher | Limited |
| SPHINCS+ | High | Slower - larger signature sizes | Moderate | Good - relies on standard hash functions |
| Classic McEliece | High | Moderate Speed | Higher - large key sizes | Limited - requires specialized arithmetic |
| BIKE | Moderate | Good performance for key exchange | Complex | Limited |
Qualitative comparison based on the article research brief. Confirm current product details in the official docs before making implementation choices.
What researchers are still tracking
The NIST standardization process was a significant milestone, but it’s not the end of the story. Research in post-quantum cryptography is ongoing, and new algorithms are constantly being developed and analyzed. Several promising candidates that were not selected by NIST are still being investigated, offering potential alternatives or improvements over the standardized algorithms.
Continued research is crucial to identify and address potential vulnerabilities in post-quantum algorithms. The security of these algorithms relies on the difficulty of certain mathematical problems, and new attacks could be discovered. The cryptographic community is actively working to analyze the security of these algorithms and develop countermeasures against potential threats. This includes formal verification techniques and cryptanalysis efforts.
Quantum key distribution (QKD) is a complementary approach to post-quantum cryptography. Unlike PQC, which relies on mathematical algorithms, QKD uses the laws of quantum physics to securely distribute cryptographic keys. While QKD offers strong security guarantees, it requires specialized hardware and has limitations in terms of distance and scalability.



No comments yet. Be the first to share your thoughts!