The Dawn of AI-Powered Cyber Warfare: Understanding the 2024 Threat Landscape
The cybersecurity landscape in 2024 has reached an unprecedented inflection point. As artificial intelligence and machine learning technologies become more accessible and sophisticated, cybercriminals are weaponizing these same tools that organizations use for defense. This paradigm shift represents one of the most significant evolutions in digital threats since the advent of the internet itself.

The integration of AI into cyber attacks has fundamentally altered the threat equation. Unlike traditional attacks that rely on human operators and pre-programmed malware, AI-powered threats can adapt, learn, and evolve in real-time. This capability enables attackers to bypass conventional security measures with unprecedented efficiency and scale.
The Scale of AI-Driven Threats in 2024
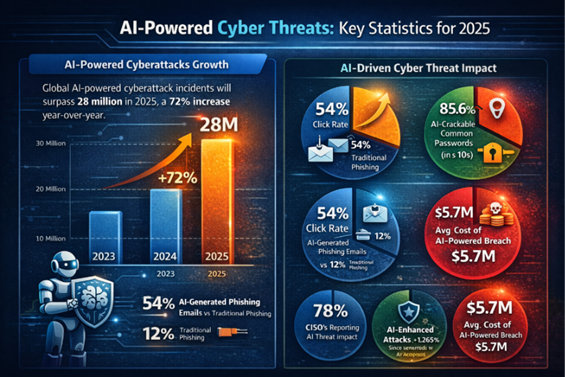
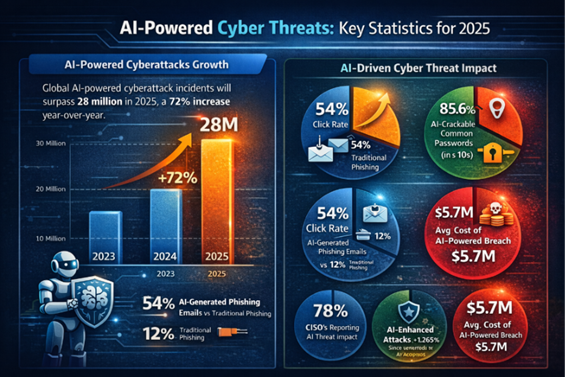
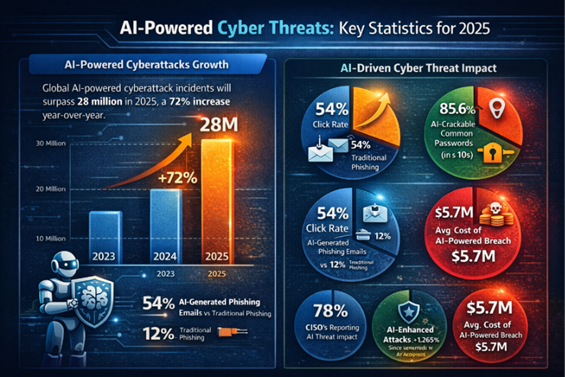
According to recent industry reports, AI cybersecurity has become the primary concern for IT leaders worldwide. Keeper Security's comprehensive analysis revealed that AI-driven attacks now represent the most serious emerging threat vector, with organizations struggling to develop effective countermeasures against these adaptive threats.
Exponential Growth of AI-Powered Cyber Attacks (2020-2024)
The sophistication of these attacks extends beyond simple automation. CrowdStrike's threat intelligence data indicates a notable shift towards malware-free intrusions and AI-assisted social engineering tactics. This evolution represents a strategic pivot by cybercriminals who are abandoning traditional malware-based methods in favor of more subtle, AI-enhanced approaches that are harder to detect and defend against.
Machine Learning Cyber Threats: The New Attack Vectors
Machine learning cyber threats manifest in several distinct categories, each presenting unique challenges for cybersecurity professionals:
AI-Powered Cyber Attack Types and Impact Assessment 2024
| Attack Type | Primary Characteristics | Target Systems | Impact Level | Detection Difficulty |
|---|---|---|---|---|
| Adversarial Machine Learning | Manipulates AI training data and models to bypass security systems | AI-powered security tools, autonomous systems | High | Very High |
| AI-Enhanced Phishing | Uses natural language processing to create highly personalized and convincing phishing emails | Email systems, user credentials, financial accounts | Medium-High | High |
| Deepfake Social Engineering | Employs synthetic media generation to impersonate executives or trusted individuals | Corporate communications, financial transactions | High | Very High |
| Automated Vulnerability Discovery | Leverages ML algorithms to identify zero-day exploits and system weaknesses | Network infrastructure, web applications, IoT devices | Very High | Medium |
| AI-Driven Password Attacks | Uses machine learning to optimize brute force and dictionary attacks | Authentication systems, user accounts | Medium | Low-Medium |
| Intelligent Malware | Self-adapting malware that learns from environment to evade detection | Endpoint systems, network security tools | High | Very High |
| ML-Powered DDoS | Employs AI to optimize attack patterns and bypass mitigation strategies | Web services, network infrastructure | Medium-High | Medium-High |
Adversarial Machine Learning: Attackers are now using machine learning algorithms to identify vulnerabilities in AI-powered defense systems. These adversarial attacks can poison training data, manipulate model outputs, or exploit algorithmic blind spots to bypass security controls.
AI-Enhanced Social Engineering: Traditional phishing and social engineering attacks have been supercharged with AI capabilities. Attackers can now generate highly personalized and convincing communications at scale, making it increasingly difficult for users to distinguish between legitimate and malicious interactions.
Automated Vulnerability Discovery: AI systems can now scan for and identify zero-day vulnerabilities faster than human researchers, giving attackers a significant advantage in the race to exploit newly discovered security flaws.
The Evolution Timeline: From Simple Automation to Intelligent Threats
The progression from basic automated attacks to intelligent, self-adapting threats has been remarkably rapid. In 2018, most automated attacks were simple, rule-based systems that followed predetermined patterns. By 2024, we're witnessing the emergence of truly intelligent threat actors that can learn from their environment, adapt to defensive measures, and optimize their attack strategies in real-time.
Understanding the AI Attack Lifecycle
To effectively defend against artificial intelligence attacks, security professionals must understand how these threats operate throughout their lifecycle:
The reconnaissance phase now leverages machine learning to analyze vast amounts of publicly available data, identifying potential targets and vulnerabilities with unprecedented precision. During the initial access phase, AI algorithms can generate and test multiple attack vectors simultaneously, dramatically reducing the time required to breach target systems.
Defensive Implications and Strategic Considerations
The rise of AI-powered threats necessitates a fundamental rethinking of cybersecurity defense strategies. Traditional signature-based detection methods and static security controls are proving inadequate against adaptive, learning-based attacks.
Organizations must now consider not only the immediate technical implications of these threats but also the broader strategic impact on their security posture. The 2024 security trends indicate that the most successful organizations are those that have embraced AI not just as a defensive tool, but as a fundamental component of their security architecture.
As we delve deeper into this three-part series, we'll explore the specific mechanisms behind these AI-powered attacks and examine how organizations can develop robust defense strategies to counter these evolving threats. The battle between AI-powered attacks and AI-enhanced defenses is just beginning, and understanding this landscape is crucial for any organization serious about cybersecurity in the modern era.
The Evolution of Machine Learning Cyber Threats: Attack Vectors and Methodologies
Machine learning has fundamentally transformed the cyberthreat ecosystem, enabling attackers to develop sophisticated, adaptive, and highly targeted offensive capabilities. Unlike traditional static attacks, AI-powered threats continuously evolve and learn from defensive responses, creating an arms race between cybercriminals and security professionals.
The sophistication of machine learning cyber threats has increased exponentially. Attackers now deploy AI algorithms to automate reconnaissance, identify vulnerabilities, and execute multi-stage attacks with minimal human intervention. These AI-driven methodologies have reduced the technical barrier for launching complex cyberattacks, democratizing advanced threat capabilities across criminal organizations.
Advanced Persistent Threat (APT) Groups Leveraging AI
State-sponsored and sophisticated criminal groups have integrated machine learning into their operational frameworks. These groups utilize AI for target selection, payload customization, and evasion techniques. The automation capabilities allow them to simultaneously manage hundreds of campaigns while maintaining operational security and reducing detection risks.
AI-Powered Cyber Attack Types by Frequency in 2024
CrowdStrike's 2024 threat intelligence reveals that AI-assisted social engineering has become the predominant attack vector, accounting for a significant portion of successful breaches. These attacks leverage natural language processing to craft convincing phishing emails, voice synthesis for vishing campaigns, and deepfake technology for business email compromise schemes.
Automated Vulnerability Discovery and Exploitation
Machine learning algorithms now scan vast networks to identify zero-day vulnerabilities faster than traditional methods. Attackers employ automated fuzzing techniques powered by genetic algorithms to discover previously unknown security flaws. This capability has shortened the window between vulnerability discovery and exploitation from months to days.
The automation extends beyond discovery to exploitation. AI systems can now generate custom exploits based on vulnerability characteristics, system configurations, and defensive measures in place. This adaptive approach makes traditional signature-based detection methods increasingly ineffective.
Behavioral Mimicry and Evasion Techniques
Advanced machine learning models enable attackers to study normal user behavior patterns and mimic them precisely. These behavioral cloning techniques allow malicious activities to blend seamlessly with legitimate network traffic, making detection extremely challenging for conventional security tools.
Adversarial machine learning represents another significant threat vector. Attackers poison training datasets used by security systems, causing AI-powered defenses to misclassify malicious activities as benign. This technique has proven particularly effective against machine learning-based email security and network monitoring solutions.
Supply Chain and Third-Party Integration Attacks
AI-powered attacks increasingly target software supply chains and third-party integrations. Machine learning algorithms identify the most vulnerable points in complex supply networks, enabling attackers to compromise multiple organizations through a single entry point. These attacks leverage dependency analysis and relationship mapping to maximize impact while minimizing exposure risk.
The integration of AI into Internet of Things (IoT) devices has created new attack surfaces. Cybercriminals deploy machine learning models to identify and exploit IoT vulnerabilities at scale, creating massive botnets for distributed denial-of-service attacks and cryptocurrency mining operations.
Real-Time Adaptive Attacks
Modern AI-powered attacks adapt in real-time based on defensive responses. Machine learning algorithms monitor security team reactions and automatically modify attack strategies to maintain persistence and avoid detection. This dynamic adaptation capability represents a fundamental shift from static attack methodologies to intelligent, responsive threat systems.
The financial impact of these evolved threats has been substantial. Organizations face increased costs for advanced detection systems, specialized training for security teams, and incident response capabilities designed to counter AI-powered attacks. The complexity of these threats requires a fundamental rethinking of traditional cybersecurity approaches and investment in next-generation defensive technologies.
Building Resilient AI-Powered Defense Strategies: The Future of Cybersecurity
As AI-powered cyber attacks continue to evolve in sophistication and scale, organizations must adopt equally advanced defense mechanisms. The integration of artificial intelligence into cybersecurity defense represents not just an option but a necessity for maintaining effective protection against modern threats. This transformation requires a comprehensive understanding of AI-driven security tools, implementation strategies, and the development of adaptive defense frameworks.
The foundation of effective AI cybersecurity lies in understanding how machine learning algorithms can enhance traditional security measures. Unlike conventional rule-based systems, AI-powered defense mechanisms can learn from attack patterns, adapt to new threats in real-time, and predict potential vulnerabilities before they are exploited. This proactive approach represents a fundamental shift from reactive security measures to predictive threat prevention.
Essential Components of AI-Enhanced Security Architecture
Modern cybersecurity frameworks must incorporate multiple layers of AI-driven protection to address the diverse range of machine learning cyber threats emerging in 2024. These components work synergistically to create a comprehensive defense ecosystem that can respond to both known and unknown attack vectors.
The implementation of AI-powered security solutions requires careful consideration of organizational needs, existing infrastructure, and threat landscape specifics. Organizations must evaluate their current security posture and identify areas where artificial intelligence attacks pose the greatest risk to their operations.
Implementation Timeline for AI Security Integration
Successful deployment of AI-enhanced cybersecurity measures follows a structured approach that ensures comprehensive coverage while minimizing operational disruption. This phased implementation allows organizations to gradually build their AI cybersecurity capabilities while maintaining existing security protocols.
The integration process begins with a thorough assessment of current security infrastructure and threat exposure. Organizations must identify specific areas where AI-powered solutions can provide the greatest impact, whether in threat detection, incident response, or vulnerability management. This assessment phase typically reveals gaps in existing security measures that AI technologies can address effectively.
Automated Threat Detection and Response Framework
One of the most significant advantages of AI-powered cybersecurity lies in its ability to automate complex threat detection and response processes. Machine learning algorithms can analyze vast amounts of network traffic, user behavior, and system logs to identify anomalies that might indicate potential security breaches.
The automated response capabilities of AI systems enable organizations to react to threats within seconds rather than hours or days. This rapid response time is crucial when defending against AI-powered attacks that can propagate and cause damage at unprecedented speeds. Advanced AI systems can automatically isolate affected systems, block malicious traffic, and initiate containment procedures without human intervention.
Best Practices for AI Security Implementation
Implementing effective AI cybersecurity requires adherence to established best practices that ensure optimal performance and minimize false positives. Organizations must balance automation with human oversight to maintain control over critical security decisions while leveraging the speed and accuracy of AI systems.
Training and continuous learning represent critical aspects of AI-powered security systems. Machine learning models must be regularly updated with new threat intelligence and attack patterns to maintain their effectiveness against evolving cyber threats. This requires establishing robust data pipelines and feedback mechanisms that enable continuous improvement of AI algorithms.
Measuring AI Security Effectiveness
The success of AI-powered cybersecurity initiatives must be measured through comprehensive metrics that evaluate both technical performance and business impact. Organizations need to establish key performance indicators that reflect the effectiveness of their AI security investments and guide future improvements.
Regular assessment and optimization of AI security systems ensure they remain effective against emerging threats while adapting to changes in organizational infrastructure and business requirements. This ongoing evaluation process helps organizations maximize their return on AI security investments and maintain robust protection against sophisticated cyber attacks.
The future of cybersecurity lies in the successful integration of artificial intelligence technologies with human expertise. Organizations that embrace AI-powered defense strategies while maintaining skilled cybersecurity teams will be best positioned to defend against the evolving landscape of machine learning cyber threats in 2024 and beyond.
Step-by-Step AI Security Deployment Guide
Implementing AI-powered cybersecurity requires a systematic approach that ensures successful integration with existing security infrastructure while maximizing the effectiveness of new AI capabilities.


No comments yet. Be the first to share your thoughts!