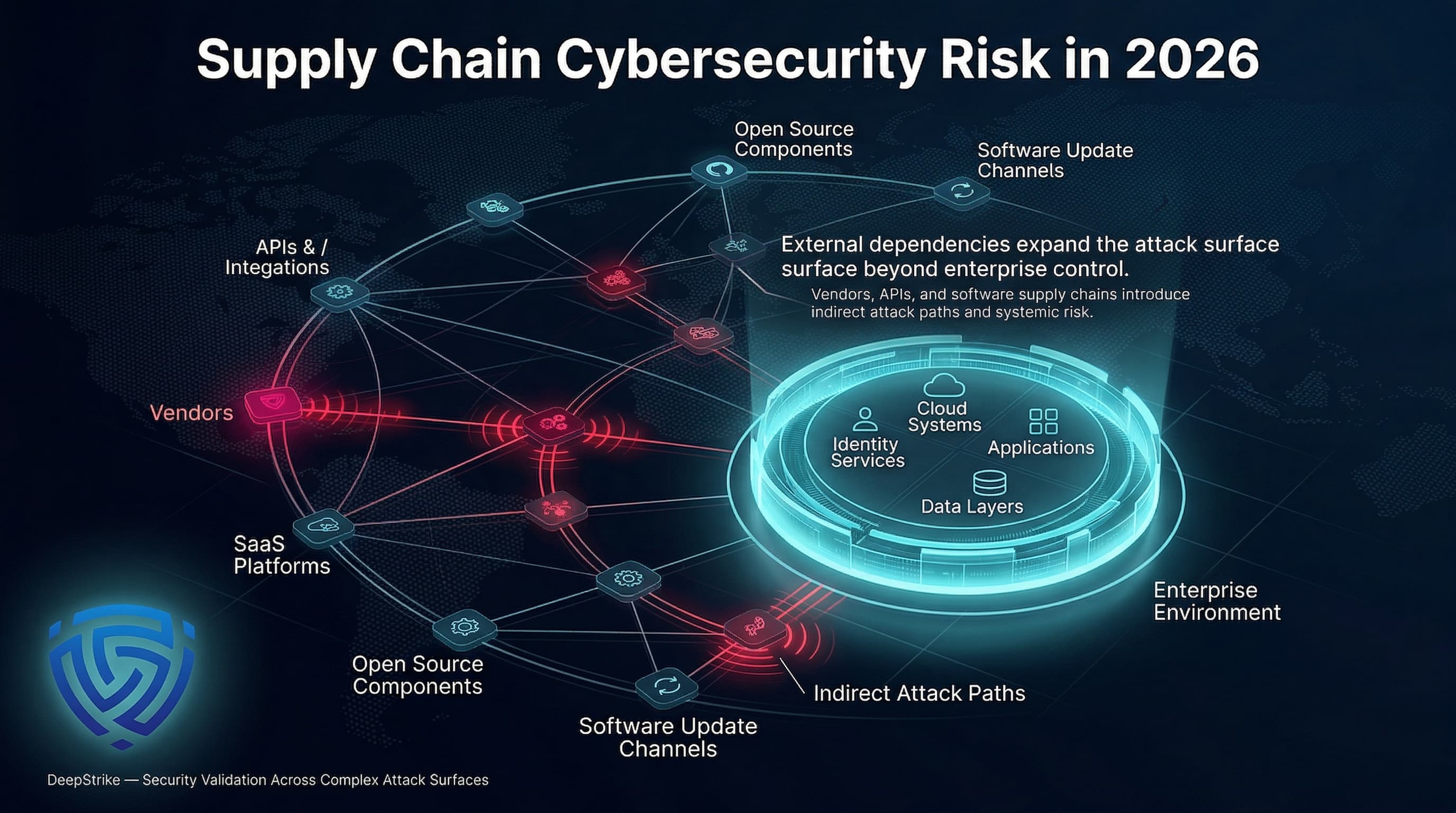
The expanding attack surface
Software is messy. We don't build from scratch anymore, opting instead for a mix of open-source libraries and cloud services that most teams don't fully audit. This complexity is exactly why supply chain attacks are becoming the default path for hackers.
This isn't just about targeting massive corporations. Small and medium-sized businesses are just as susceptible, often lacking the resources to adequately assess and mitigate third-party risks. The increasing sophistication of threat actors—including nation-states and organized criminal groups—means even well-defended organizations are finding themselves compromised. We're seeing a shift from opportunistic attacks to carefully planned, targeted campaigns.
Geopolitical motivations are also playing a growing role. Nation-states often use supply chain attacks to gain access to sensitive information or disrupt critical infrastructure. The SolarWinds attack is a prime example of this, demonstrating the potential for widespread damage and long-term consequences. The problem is compounded by the speed of modern software development; security often takes a backseat to speed and features.
Software risks from the DNI report
The DNI report on software supply chain attacks highlights the breadth of vulnerabilities present throughout the software development lifecycle. Attackers aren’t just targeting the final product; they’re looking for weaknesses at every stage—from the initial code development to the eventual distribution to end-users. This includes targeting the developers themselves, hoping to compromise their systems and inject malicious code.
Specifically, the report emphasizes the risks associated with code development and testing environments. Attackers aim to gain access to source code repositories, build systems, and CI/CD pipelines. Compromising these areas allows them to introduce backdoors, steal intellectual property, or manipulate the software’s functionality. The build and packaging stages are also critical; attackers can alter the build process to include malicious components without the developers’ knowledge.
Gaining access to update mechanisms is another key objective. Once an attacker controls the update process, they can distribute malware to a large number of users. The DNI report stresses the importance of securing these channels and implementing robust integrity checks. Ultimately, attackers are seeking access to anything that gives them control over the software’s lifecycle, whether it's source code, build servers, or distribution networks. Protecting these points is paramount.
The DNI report makes it clear: you can't assume a library is safe just because it's popular. We have to verify every component manually or through automated checks before it touches production code.
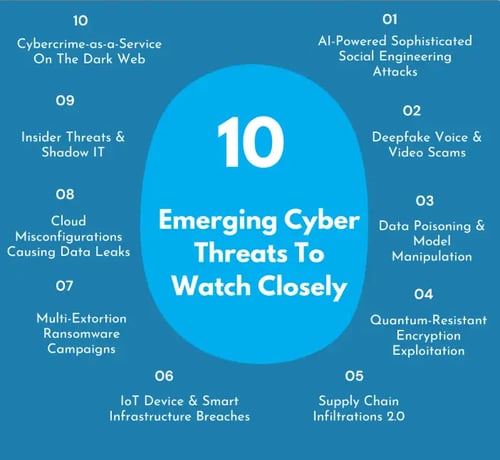
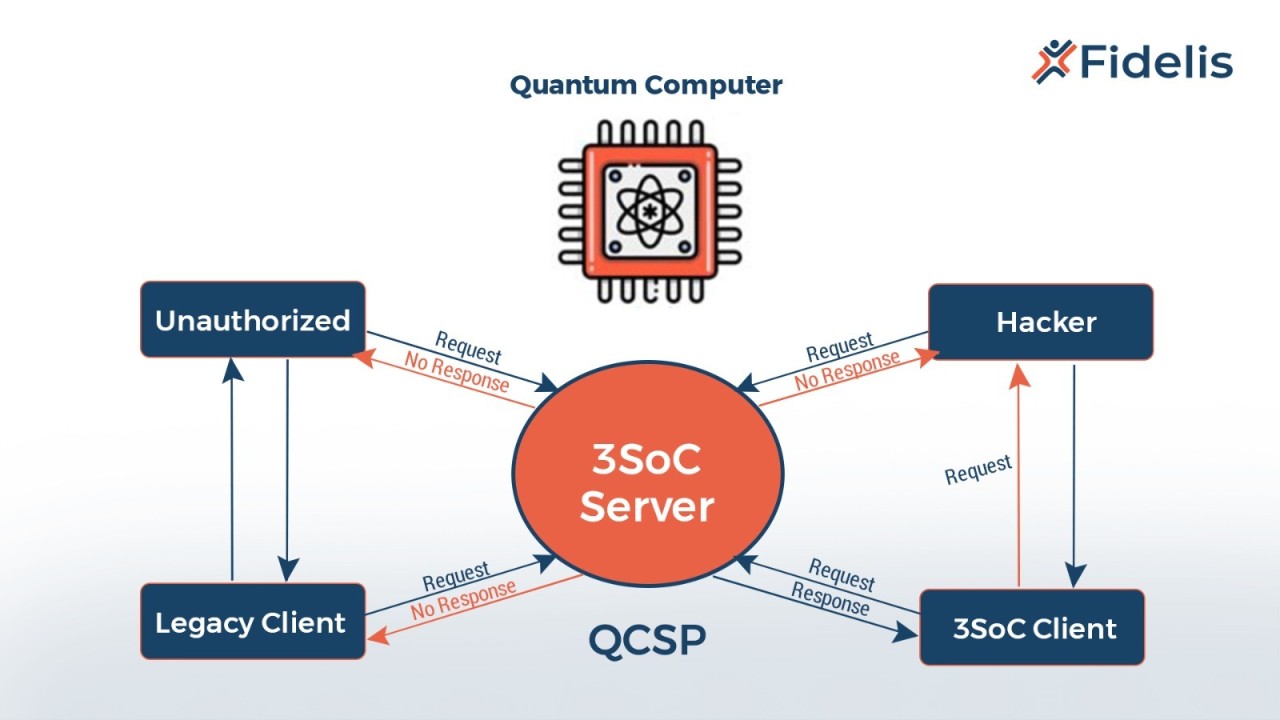
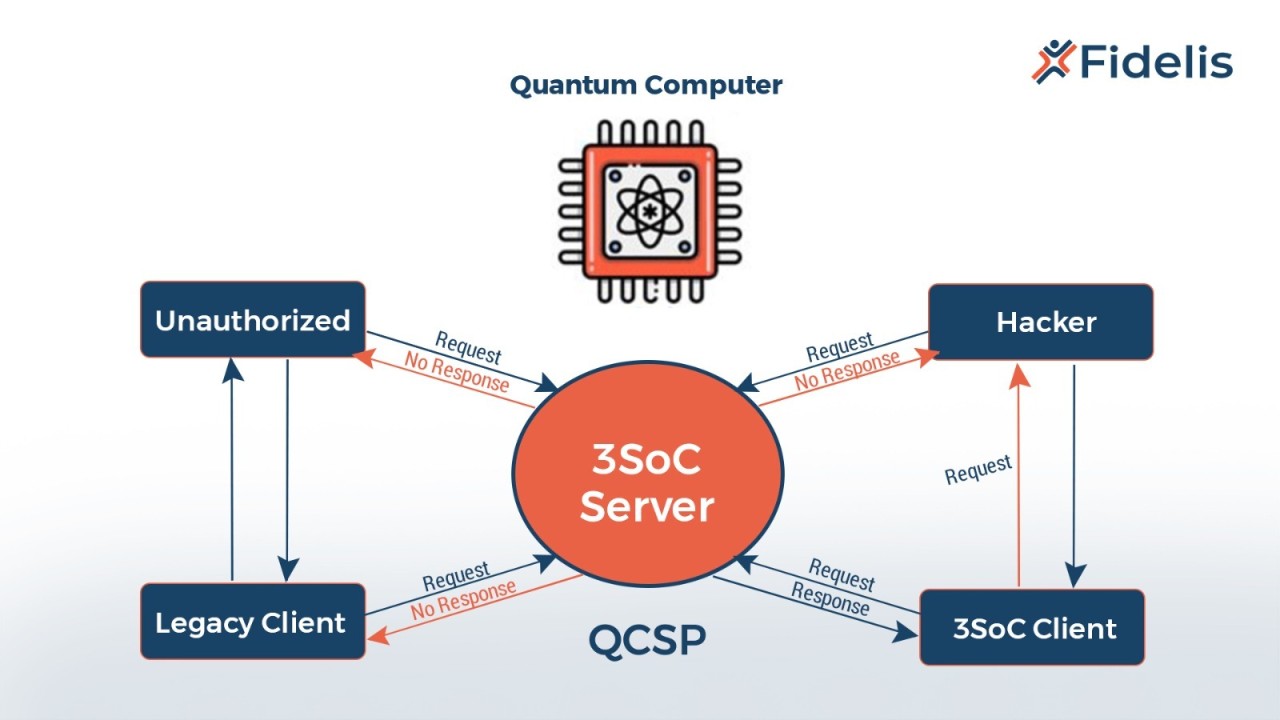
New threats for 2026
Looking ahead to 2026, the threat landscape is expected to become even more complex. While third-party software will remain a primary target, we’ll likely see an increase in attacks targeting specific dependencies and components. The 2026 cybersecurity threat outlook from eccu.edu points to the continued exploitation of open-source vulnerabilities, and anticipates attackers will become more adept at identifying and exploiting weaknesses in less-maintained packages.
Cloud service providers represent a significant attack vector. Organizations are increasingly reliant on cloud infrastructure and services, making them attractive targets for attackers. Compromising a major cloud provider could have cascading effects, impacting hundreds or even thousands of customers. Hardware supply chains are also a growing concern. Tampering with hardware components during manufacturing or transit can introduce vulnerabilities that are difficult to detect.
We're already seeing a trend towards attacks targeting specific software packages, similar to the Log4j vulnerability. It's difficult to predict the next Log4j, but we can expect attackers to continue searching for widely used libraries with known or zero-day vulnerabilities. The focus will likely be on components that are critical to many applications and systems. Attackers will also target those with limited security oversight or a small maintainer base.
- Open-source dependencies
- Cloud service providers
- Hardware components
- Widely used libraries with known vulnerabilities
Notable Attacks: Recent Examples
The SolarWinds attack, discovered in late 2020, remains a stark reminder of the potential impact of supply chain attacks. Attackers compromised the Orion software platform, inserting malicious code that allowed them to gain access to the networks of numerous government agencies and private companies. The scale and sophistication of the attack were unprecedented, and it took months to fully understand the extent of the damage.
More recently, HackerDesk’s April 2026 critical vulnerabilities alert detailed a series of attacks targeting a popular project management tool. Attackers exploited a vulnerability in a third-party library used by the tool to gain access to customer data and systems. This attack highlighted the importance of regularly updating software and patching vulnerabilities. It also underscored the need for vendors to thoroughly assess the security of their dependencies.
In early 2025, a major hardware manufacturer was found to have shipped devices with a pre-installed backdoor. The backdoor allowed attackers to remotely access and control the devices, potentially compromising sensitive data. This incident demonstrated the risks associated with hardware supply chains and the difficulty of detecting hardware-level compromises. The fallout from this attack included significant financial losses and reputational damage.
Another example involved a compromise of a widely used code signing certificate. Attackers used the stolen certificate to sign malicious software, making it appear legitimate. This allowed them to bypass security controls and install malware on unsuspecting systems. This attack highlighted the importance of protecting code signing keys and implementing robust certificate management practices.
Supply Chain Attacks on Hardware Wallets
— Jesse Stone (@JesseStone2023) May 4, 2026
In fact, throughout 2025 and early 2026, there have been multiple reported cases of asset theft resulting from Ledger devices purchased through unofficial platforms (such as Lazada or other third-party resellers). pic.twitter.com/bllfNN1Uo7
SBOMs are your first defense
A Software Bill of Materials (SBOM) is essentially a nested inventory of a software application’s components – think of it as a detailed ingredients list. It lists all the software parts used to build an application, including open-source libraries, third-party modules, and dependencies. SBOMs are becoming increasingly essential for understanding and managing supply chain risks.
The primary benefit of an SBOM is that it provides visibility into the software supply chain. This allows organizations to identify potential vulnerabilities and assess the risk associated with using specific components. If a new vulnerability is discovered in a particular library, organizations with an SBOM can quickly determine which of their applications are affected. The SBOM isn’t a magic bullet, but it’s a critical first step in understanding your exposure.
Creating and maintaining accurate SBOMs can be challenging. It requires automated tools and processes to scan software and identify its components. Different SBOM formats exist, including SPDX and CycloneDX. SPDX is a widely adopted standard, while CycloneDX is gaining traction due to its focus on security. Several tools are available to generate SBOMs, ranging from open-source options to commercial solutions.
- SPDX
- CycloneDX
SBOM Format Comparison: SPDX vs. CycloneDX (as of late 2026)
| Feature | SPDX | CycloneDX |
|---|---|---|
| Data Model | More generalized, tag-based. Focuses on legal compliance and broad component descriptions. | Graph-based, designed for security analysis and vulnerability identification. Emphasizes relationships between components. |
| Tooling Support | Mature ecosystem, wider range of tools for generation and analysis, particularly for license compliance. | Rapidly growing tooling support, strong focus on vulnerability scanning and integration with security platforms. |
| Ease of Use (Generation) | Can be complex to generate manually due to the tag-based structure and required metadata. Automated tools are often necessary. | Generally considered easier to generate programmatically, especially with existing build systems and dependency management tools. |
| Ease of Use (Consumption) | Requires understanding of SPDX tag definitions and relationships. Analysis can be more challenging without specialized tools. | Graph structure facilitates easier traversal and analysis for security professionals. More intuitive for vulnerability correlation. |
| Industry Adoption | Historically strong in legal and compliance-driven industries. Becoming more widely adopted across sectors. | Gaining significant traction in the software security community and increasingly adopted by organizations prioritizing vulnerability management. |
| Flexibility | Highly flexible and adaptable to various software types and licensing models. | Designed with a focus on modern software ecosystems and package managers, offering good flexibility for complex dependencies. |
| Vulnerability Data | Supports linking to vulnerability databases, but is not its primary strength. | Strong emphasis on vulnerability integration and reporting. Designed to easily incorporate vulnerability data from multiple sources. |
Qualitative comparison based on the article research brief. Confirm current product details in the official docs before making implementation choices.
Stop relying on vendor questionnaires
Traditional vendor risk management approaches, like sending out lengthy security questionnaires, are often inadequate. These questionnaires rely on self-reporting and can be easily circumvented. They provide a snapshot in time, but don’t offer continuous monitoring or real-time threat intelligence. A more robust approach is needed.
Continuous monitoring is crucial. This involves regularly assessing vendor security posture through techniques like penetration testing, security audits, and vulnerability scanning. Real-time threat intelligence feeds can also provide early warning of potential risks. Establishing clear security requirements in vendor contracts is essential. These requirements should specify the security controls that vendors must implement and the consequences of non-compliance.
Instead of simply asking vendors if they're secure, organizations should verify their security posture. This requires actively testing their systems and monitoring their activity. It also means establishing clear expectations and holding vendors accountable for meeting those expectations. The goal is to build a collaborative relationship based on trust, but also on verifiable security practices.
Defense Strategies: A Layered Approach
Mitigating supply chain risks requires a layered approach, combining technical and organizational controls. Technical controls include code signing, vulnerability scanning, and intrusion detection systems. Code signing ensures that software hasn’t been tampered with, while vulnerability scanning identifies known weaknesses. Intrusion detection systems can detect malicious activity.
Organizational controls are equally important. These include developing comprehensive security policies, creating incident response plans, and providing regular employee training. Security policies should outline the organization’s expectations for vendor security. Incident response plans should detail the steps to take in the event of a supply chain attack. Employee training should educate users about the risks and how to identify and report suspicious activity.
Preparation matters more than tools. You need an incident response plan that specifically covers vendor breaches, and you need to test it. There isn't a single product that fixes this; it's just a cycle of checking your dependencies and watching for anomalies.
- Sign your code to ensure it hasn't been tampered with.
- Run vulnerability scans to catch known weaknesses in your libraries.
- Intrusion detection systems
- Comprehensive security policies
- Incident response plans
- Regular employee training



No comments yet. Be the first to share your thoughts!