The reality of cloud compliance in 2026
Cloud security compliance is no longer a checklist. Companies now deal with a mess of overlapping regulations and threats that target data spread across different clouds. Most teams I talk to are falling behind because they don't have enough people who actually understand how these systems talk to each other.
The move to the cloud initially promised simplified IT, but it introduced a shared responsibility model that many haven't fully grasped. This model shifts some security obligations to the cloud provider, but leaves significant aspects – data security, access control, application security – squarely with the customer. Failing to understand these boundaries creates significant risk, and we're seeing a rise in breaches stemming from misconfigured cloud services.
2026 is a critical horizon because several key regulations are expected to undergo significant updates, and enforcement is likely to increase. Organizations that don't proactively address these changes risk substantial fines, reputational damage, and loss of customer trust. It's time to move beyond reactive compliance and embrace a proactive, risk-based approach to cloud security.
Regulations to track this year
Several compliance frameworks will demand attention in 2026. The General Data Protection Regulation (GDPR) will likely see continued scrutiny regarding data transfer mechanisms and the implementation of data minimization principles. Expect increased focus on demonstrating accountability and documenting data processing activities.
Healthcare organizations need to closely monitor updates to the Health Insurance Portability and Accountability Act (HIPAA). Recent guidance emphasizes the importance of securing Protected Health Information (PHI) in the cloud, including robust access controls and encryption. The Office for Civil Rights (OCR) is becoming more aggressive in its enforcement of HIPAA violations.
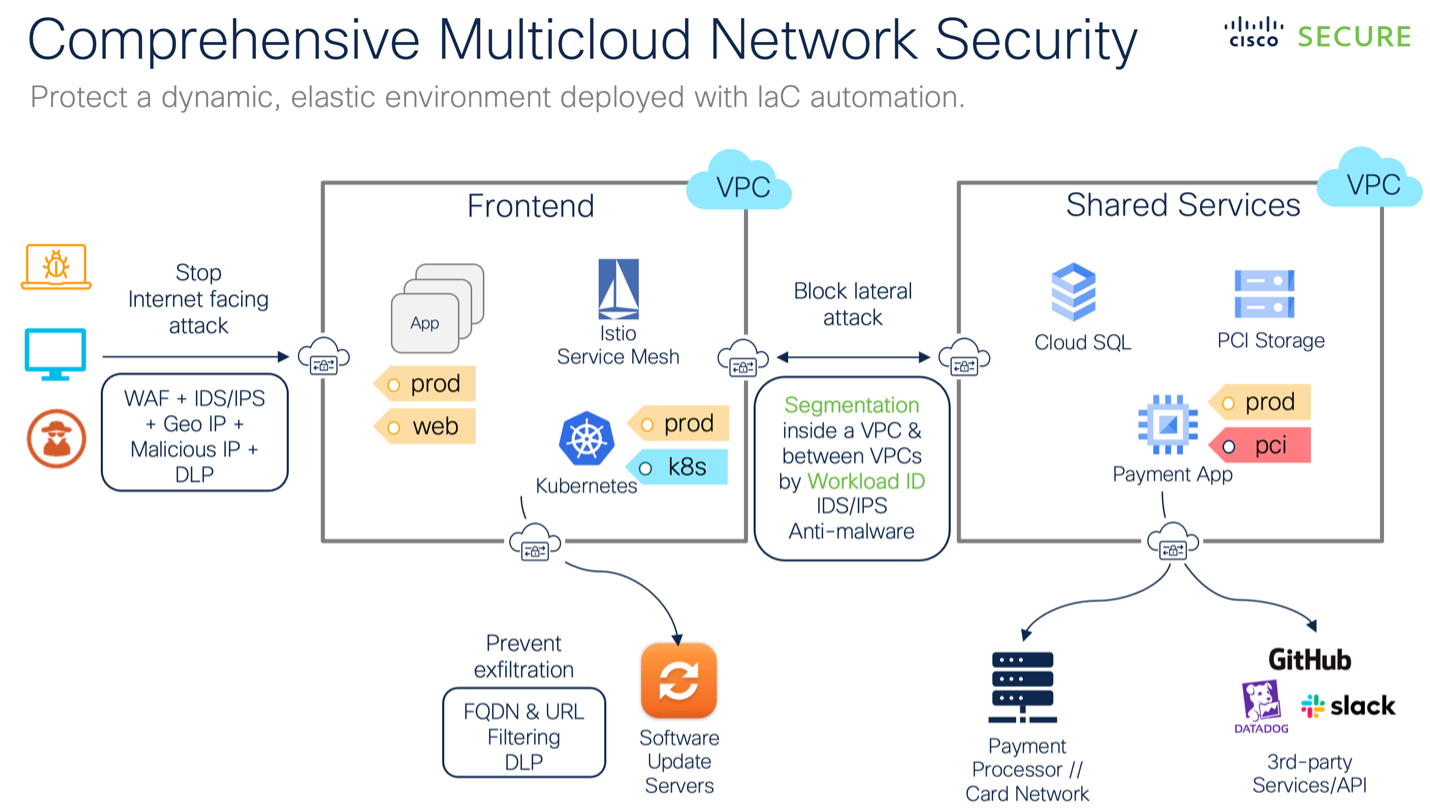
If you handle credit cards, PCI DSS 4.0 is the new baseline. While it was finalized in 2022, the transition period ends soon. By 2026, you'll need to prove your multi-factor authentication covers every access point into the cardholder data environment, not just administrative logins.
FedRAMP, the US government's cloud security framework, is also evolving. Expect increased emphasis on continuous monitoring and automated security assessments. Organizations seeking to do business with the federal government will need to demonstrate a high level of security maturity. Emerging regional standards, like those in Australia and Brazil relating to data sovereignty, will also require attention.
- GDPR: New scrutiny on how data moves between the US and EU.
- HIPAA: Emphasis on securing PHI in the cloud.
- PCI DSS 4.0: Stringent requirements for network segmentation and MFA.
- FedRAMP: Focus on continuous monitoring and automated assessments.
Who is responsible for what?
The shared responsibility model is fundamental to cloud security, yet often misunderstood. Cloud providers – like AWS, Azure, and Google Cloud – are responsible for the security of the cloud itself: the infrastructure, physical security, and underlying services. Customers, on the other hand, are responsible for security in the cloud: their data, applications, identities, and configurations.
A common mistake is assuming the cloud provider handles all security aspects. This leads to misconfigurations, such as leaving storage buckets publicly accessible or failing to implement strong access controls. These seemingly small errors are prime targets for attackers. I’ve seen numerous breaches occur because of a failure to properly configure cloud services.
For example, if you use AWS S3, AWS secures the S3 service itself. But you are responsible for setting the correct permissions on your S3 buckets. If you leave a bucket open to the public, AWS isn’t at fault – that’s a customer-side misconfiguration. Similarly, with Azure Virtual Machines, Microsoft secures the hypervisor, but you're responsible for patching the operating system and applications running inside the VM.
- Cloud Provider: Secures the infrastructure, physical security, underlying services.
- Customer: Secures data, applications, identities, and configurations.
Why zero trust simplifies audits
Zero Trust architecture is a security framework based on the principle of 'never trust, always verify.' It assumes that no user or device, whether inside or outside the network perimeter, can be automatically trusted. This aligns perfectly with the goals of many compliance frameworks, which emphasize strong authentication, access controls, and continuous monitoring.
Principles like least privilege access – granting users only the minimum permissions necessary to perform their tasks – are core to both Zero Trust and compliance standards like PCI DSS and HIPAA. Microsegmentation, which isolates workloads and limits the blast radius of a potential breach, also supports compliance by reducing the risk of data exposure. Continuous verification, through multi-factor authentication and behavioral analytics, adds another layer of security.
Zero Trust makes audits easier. When you assume no one is trusted, you naturally create the logs and access restrictions that auditors ask for anyway. It moves the conversation from 'we think we're secure' to 'here is the exact policy that blocked this unauthorized request.'
Automating Compliance: Tools and Technologies
Manual compliance checks are time-consuming, error-prone, and difficult to scale. Automation is essential for maintaining a strong security posture and demonstrating compliance. Tools for continuous monitoring scan cloud environments for misconfigurations and vulnerabilities, alerting security teams to potential issues in real-time.
Vulnerability scanners identify weaknesses in systems and applications, helping organizations prioritize remediation efforts. Configuration management tools ensure that cloud resources are configured according to security best practices and compliance requirements. Security Information and Event Management (SIEM) systems collect and analyze security logs, providing a centralized view of security events and facilitating incident response.
Cloud-native security tools, offered by providers like AWS, Azure, and Google Cloud, are increasingly popular. These tools are tightly integrated with the cloud platform and offer features like automated compliance checks and threat detection. They can significantly simplify the compliance process and reduce the burden on security teams.
- Continuous Monitoring Tools: Scan for misconfigurations and vulnerabilities.
- Vulnerability Scanners: Identify weaknesses in systems and applications.
- Configuration Management Tools: Enforce security best practices.
- SIEM Systems: Collect and analyze security logs.
Automation Approaches for Cloud Security Compliance - A Comparative Assessment
| Automation Approach | Cost | Complexity | Scalability | Integration Effort |
|---|---|---|---|---|
| Scripting (e.g., Python, Bash) | Generally low initial cost, but can increase with maintenance. | High – requires significant expertise in scripting and cloud APIs. | Moderate – scalability depends on script design and infrastructure. | Moderate – requires custom integration with existing systems and tools. |
| Configuration-as-Code (e.g., Terraform, Ansible) | Moderate – cost associated with tooling and training. | Moderate – requires understanding of infrastructure-as-code principles and the specific tool. | High – designed for repeatable and scalable infrastructure deployments. | Moderate – often requires adapting existing systems to work with IaC principles. |
| Cloud-Native Tools (provided by cloud provider) | Variable – often usage-based pricing, can be cost-effective for specific services. | Low to Moderate – typically easier to use within the provider's ecosystem. | High – designed to scale with the cloud provider's infrastructure. | Low – natively integrates with other services within the same cloud provider. |
| Third-Party Cloud Security Platforms | Potentially high – subscription-based pricing models. | Moderate – platform handles much of the complexity, but configuration is still required. | High – designed for scalability and multi-cloud environments. | Moderate to High – integration can be complex depending on existing security stack. |
| Policy-as-Code (e.g., Open Policy Agent) | Moderate - cost associated with tooling and potential consulting. | Moderate to High - requires understanding of policy languages and enforcement mechanisms. | High - designed for consistent policy enforcement across environments. | Moderate - requires integration with existing infrastructure and CI/CD pipelines. |
| Automated Security Scanning Tools | Variable – dependent on features and scale of deployment. | Low to Moderate – typically user-friendly interfaces, but requires configuration. | High – designed to scan large and complex environments. | Moderate – integration via APIs or existing CI/CD pipelines. |
Illustrative comparison based on the article research brief. Verify current pricing, limits, and product details in the official docs before relying on it.
Data Residency and Sovereignty Challenges
Data residency and sovereignty requirements are becoming increasingly important, particularly for multinational businesses. These regulations dictate where data can be stored and processed, often based on geographic location. Failing to comply can result in hefty fines and legal repercussions.
For example, the EU's GDPR requires that personal data of EU citizens be processed within the EU, or in countries with equivalent data protection standards. Many countries are enacting similar regulations, making it challenging for organizations to manage data across borders. This is especially true for cloud deployments, where data may be stored in multiple regions.
Strategies for complying with these requirements include data localization – storing data within the required geographic region – and encryption. Encryption can protect data in transit and at rest, even if it's stored in a region with less stringent data protection laws. Organizations need to carefully consider their data residency requirements when choosing cloud providers and designing their cloud architecture.
Preparing for Audits: Documentation is Key
Cloud security audits are becoming more common, and organizations need to be prepared. Accurate and up-to-date documentation is crucial for demonstrating compliance to auditors. This includes documenting security controls, policies, procedures, and evidence of their implementation.
Auditors will want to see evidence that you've implemented appropriate access controls, encryption, and monitoring. They’ll also review your incident response plan and disaster recovery procedures. Don’t underestimate the importance of a well-maintained audit trail. It’s often the first thing auditors will request.
Focus on documenting how you’re meeting specific compliance requirements. Simply stating that you’re compliant isn’t enough; you need to provide evidence to support your claims. Regularly review and update your documentation to ensure it reflects your current security posture. A little preparation goes a long way.



No comments yet. Be the first to share your thoughts!