Moving beyond perimeter security
For years, cybersecurity operated under a fairly simple model: build a strong perimeter and keep threats out. This approach worked reasonably well when applications and data lived within a corporate network. But the explosion of multi-cloud adoption has fundamentally broken that model. Organizations are now running workloads across AWS, Azure, Google Cloud, and various SaaS providers, effectively dissolving the traditional perimeter.
The shift to multi-cloud isn’t just about cost optimization or avoiding vendor lock-in. It’s about agility, scalability, and accessing specialized services. However, this distributed environment introduces significant security challenges. Managing security policies and maintaining visibility across multiple cloud platforms is incredibly complex, and the risk of misconfiguration and data breaches increases exponentially.
This is where the concept of a Cloud Security Mesh (CSM) comes into play. It’s not a single product you can buy, but rather an architectural approach to security. Think of it as a flexible, scalable, and distributed security framework designed to protect data and applications regardless of where they reside. CSM acknowledges that the perimeter is gone and focuses on securing access to resources, no matter their location.
The rise of sophisticated attacks, like those leveraging AI as noted by HackerDesk, further necessitates a move beyond perimeter-based defenses. Traditional security tools are often ill-equipped to handle the dynamic and distributed nature of modern cloud environments. CSM offers a more adaptive and resilient approach to cloud cybersecurity.
How a security mesh works
A Cloud Security Mesh isn’t just about deploying a bunch of security tools. It’s guided by a set of core principles that define how security is implemented and managed. These principles aren’t necessarily ranked in order of importance, but each is critical for a successful CSM implementation.
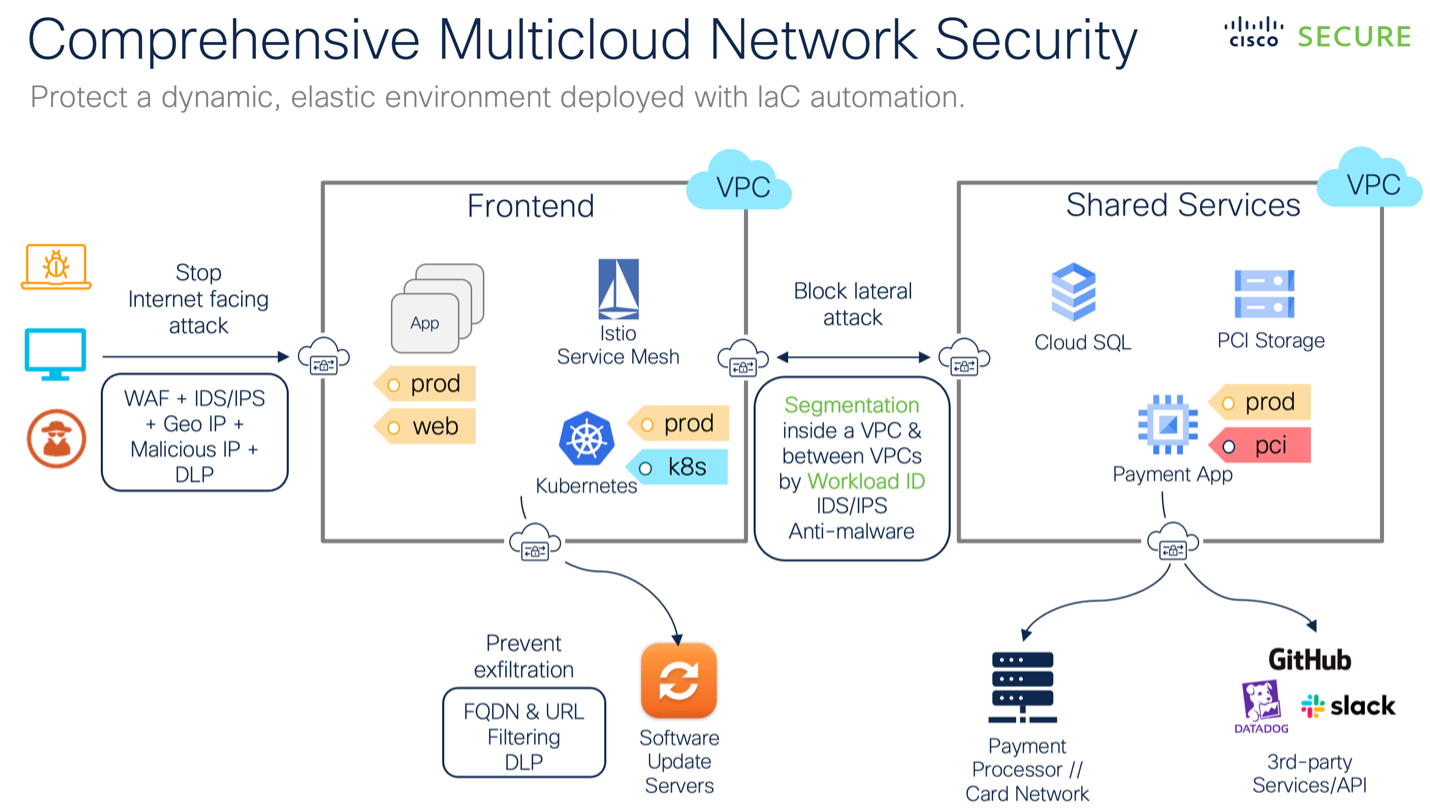
First, there’s distributed policy enforcement. Instead of relying on a central security appliance, policies are enforced at the point of access, closer to the data and applications. This reduces latency, improves scalability, and allows for more granular control. It also means security isn’t a bottleneck.
Identity-centric security is another fundamental principle. CSM recognizes that identity is the new perimeter. By verifying the identity of every user and device attempting to access resources, organizations can significantly reduce the risk of unauthorized access. This is heavily reliant on robust Identity and Access Management (IAM) systems.
Data-centric security is paramount. CSM focuses on protecting the data itself, regardless of where it’s stored or processed. This involves techniques like encryption, data loss prevention (DLP), and data masking. The goal is to ensure that even if an attacker gains access to a system, they can’t access sensitive data.
Finally, automation is essential for managing the complexity of a multi-cloud environment. CSM leverages automation to streamline security operations, respond to threats in real-time, and ensure consistent policy enforcement. Manual processes simply can’t keep up with the pace of change.
Scout Suite — Multi-Cloud Security Auditing Tool ☁️
— Vivek | Cybersecurity (@VivekIntel) April 11, 2026
Assess your cloud security posture across:
• AWS
• Azure
• Google Cloud
• Oracle Cloud
• Alibaba Cloud
• Kubernetes
• DigitalOcean
Automatically maps attack surface and highlights misconfigurations.
Generates a detailed…
The tech behind the mesh
Building a Cloud Security Mesh requires a combination of different technologies working together. These aren’t standalone solutions, but rather components of a larger, integrated framework. Understanding how these technologies complement each other is crucial.
Cloud Access Security Brokers (CASBs) are a cornerstone of CSM. They act as intermediaries between users and cloud applications, providing visibility into cloud usage and enforcing security policies. CASBs can prevent data leakage, detect threats, and ensure compliance.
Secure Access Service Edge (SASE) combines network security functions like firewall as a service (FWaaS), secure web gateway (SWG), and zero trust network access (ZTNA) into a single, cloud-delivered service. SASE provides secure access to applications and data, regardless of the user’s location.
Cloud Workload Protection Platforms (CWPP) focus on securing cloud workloads, such as virtual machines, containers, and serverless functions. CWPP solutions provide vulnerability management, threat detection, and runtime protection for cloud-native applications.
Identity and Access Management (IAM) solutions are critical for controlling access to cloud resources. IAM solutions provide features like multi-factor authentication, role-based access control, and privileged access management. They form the foundation of identity-centric security.
Service mesh technologies, originally designed for microservices architectures, also play a role. They provide observability, traffic management, and security features for inter-service communication. They can help secure east-west traffic within the cloud environment.
Key Technologies Contributing to a Cloud Security Mesh (CSM)
| Technology | Primary Function | Deployment | CSM Contribution |
|---|---|---|---|
| CASB | Cloud Application Security Brokerage: Visibility, data security, and threat protection for cloud applications. | Proxy-based, API-based, or Log Analysis | Provides granular visibility and control over data in cloud applications, enforcing security policies and preventing data leakage – a foundational element for consistent security across clouds. |
| SASE | Secure Access Service Edge: Combines network security functions (like firewall as a service, secure web gateway, and zero trust network access) with WAN capabilities. | Cloud-native, globally distributed points of presence (PoPs) | Delivers consistent security policy enforcement and secure access to applications, regardless of user location, contributing to a zero-trust approach within the CSM. |
| CWPP | Cloud Workload Protection Platform: Secures cloud workloads (VMs, containers, serverless functions) across the entire application lifecycle. | Agent-based, agentless, or API-based | Protects the cloud workloads themselves, offering vulnerability management, threat detection, and compliance monitoring – essential for securing the compute layer within the CSM. |
| IAM | Identity and Access Management: Controls user access to cloud resources, ensuring only authorized individuals have appropriate permissions. | Cloud-based, on-premises, or hybrid | Provides the identity foundation for the CSM, enabling consistent authentication, authorization, and access control policies across all cloud environments. Crucial for least privilege access. |
| ZTNA | Zero Trust Network Access: Provides secure, policy-driven access to applications based on user identity and device posture, rather than network location. | Cloud-delivered service | Enforces a 'never trust, always verify' approach, limiting the blast radius of potential breaches and aligning with the core principles of a CSM. |
Illustrative comparison based on the article research brief. Verify current pricing, limits, and product details in the official docs before relying on it.
A plan for implementation
Implementing a Cloud Security Mesh isn't a one-time project; it’s a journey. A phased approach is essential for minimizing disruption and maximizing success. It’s also important to understand that this isn’t about ripping and replacing existing security tools. It’s about integrating them into a cohesive framework.
The first phase is assessment and planning. This involves understanding your current cloud environment, identifying security gaps, and defining your CSM goals. You need to map out your data flows, identify critical assets, and assess your risk tolerance. This is also the time to evaluate different CSM technologies and vendors.
Next comes identity and access control implementation. This involves strengthening your IAM systems, implementing multi-factor authentication, and enforcing the principle of least privilege. Ensure you have a clear understanding of who has access to what resources.
The third phase focuses on data security controls. This includes implementing encryption, DLP, and data masking. You need to classify your data, identify sensitive information, and apply appropriate security measures.
Threat detection and response is the fourth phase. This involves deploying threat intelligence feeds, implementing security information and event management (SIEM) systems, and automating incident response processes. You need to be able to detect and respond to threats in real-time.
Finally, continuous monitoring and improvement is essential. Regularly review your security posture, assess the effectiveness of your controls, and make adjustments as needed. CSM is an ongoing process, not a one-time fix.
Mesh and zero trust
Cloud Security Mesh and Zero Trust are often discussed in the same breath, and for good reason. They are highly complementary security models. Zero Trust, at its core, is a security framework based on the principle of "never trust, always verify." CSM provides the infrastructure and controls necessary to enable Zero Trust in a multi-cloud environment.
CSM facilitates least privilege access by providing granular control over who can access what resources. It enables microsegmentation, allowing you to isolate workloads and limit the blast radius of a potential breach. This is achieved through technologies like SASE and CWPP.
Continuous verification is another key aspect of Zero Trust. CSM provides the visibility and monitoring capabilities needed to continuously assess the security posture of users and devices. This includes verifying identity, assessing device health, and monitoring user behavior.
Essentially, Zero Trust defines what you want to achieve – a security model based on trustlessness – while CSM provides how you achieve it. CSM provides the tools and technologies to implement Zero Trust principles in a practical and scalable way across your multi-cloud environment.
Common hurdles
Implementing a Cloud Security Mesh isn’t without its challenges. Organizations often encounter obstacles related to complexity, skills gaps, integration issues, and vendor lock-in. Acknowledging these challenges upfront is crucial for developing a successful implementation strategy.
Complexity is a major hurdle. Managing security across multiple cloud platforms and integrating different security tools can be overwhelming. It’s important to start small, focus on high-priority assets, and gradually expand your CSM implementation.
A lack of skilled personnel is another common challenge. CSM requires expertise in cloud security, networking, and automation. Investing in training and hiring skilled professionals is essential. Consider partnering with a managed security service provider (MSSP) to supplement your internal resources.
Integration issues can arise when trying to integrate different security tools and technologies. Ensure that your chosen solutions are compatible and can seamlessly exchange data. APIs and open standards can help facilitate integration.
Vendor lock-in is a risk to be aware of. Choosing proprietary technologies can limit your flexibility and make it difficult to switch vendors in the future. Prioritize solutions that are based on open standards and support interoperability.
What changes by 2026
The Cloud Security Mesh landscape is constantly evolving. Several emerging trends are likely to shape the future of CSM in the coming years. While predicting the future with certainty is impossible, these developments seem highly probable.
AI-powered security automation will play an increasingly important role. AI and machine learning can be used to automate threat detection, incident response, and policy enforcement. This will help organizations scale their security operations and respond to threats more effectively.
Serverless security is gaining traction. As more organizations adopt serverless computing, securing these environments will become increasingly important. CSM solutions will need to adapt to the unique challenges of serverless architectures.
The integration of CSM with DevSecOps practices will become more common. Embedding security into the development lifecycle will help organizations build more secure applications from the start. This requires close collaboration between security, development, and operations teams.
New regulations and compliance requirements will continue to drive the evolution of CSM. Organizations will need to adapt their security posture to meet changing regulatory demands. This could include stricter data privacy regulations and more stringent security standards.
Recent CSM Discussions
- Cloud Security Posture Management (CSPM) integration - Experts anticipate CSM will heavily rely on CSPM tools to continuously assess and improve the security configurations across all cloud environments. This includes automated remediation of misconfigurations.
- Zero Trust Network Access (ZTNA) as a core component - Discussions highlight ZTNA’s crucial role within a CSM, providing granular access control and minimizing the attack surface by verifying every user and device.
- Data Security Posture Management (DSPM) gaining prominence - Several experts foresee DSPM becoming integral to CSM, focusing on discovering, classifying, and protecting sensitive data across multi-cloud deployments. This goes beyond traditional perimeter security.
- Shift towards API security within CSM - The increasing reliance on APIs in cloud environments is driving a need for robust API security solutions integrated into CSM architectures. This includes API discovery, threat protection, and access control.
- Importance of consistent policy enforcement - A common theme is the need for a centralized policy engine within a CSM to ensure consistent security policies are applied across all cloud providers and services, regardless of underlying infrastructure.
- Integration with Cloud Native Application Protection Platforms (CNAPP) - Experts suggest CSM will increasingly integrate with CNAPP solutions to provide comprehensive security across the entire application lifecycle, from code to runtime.
- Focus on observability and threat detection - A key aspect of future CSM deployments will be enhanced observability and threat detection capabilities, leveraging security information and event management (SIEM) and extended detection and response (XDR) solutions.



No comments yet. Be the first to share your thoughts!