The multi-cloud security headache
Organizations are rapidly adopting multi-cloud strategies. It makes sense: leveraging the unique strengths of AWS, Azure, Google Cloud, and others can boost innovation and resilience. But this move introduces a serious security challenge. Traditional security models, built around a defined network perimeter, simply don't translate well to this distributed environment.
The core problem is a lack of consistency. Each cloud provider has its own security tools, policies, and configurations. Maintaining a unified security posture across these disparate systems is incredibly difficult. This creates visibility gaps and makes it harder to enforce consistent controls, leaving organizations vulnerable to attack.
The expanding attack surface is another major concern. More cloud instances, more data stored in different locations, and more access points all present opportunities for attackers. Recent reports, like the one from HackerDesk detailing the top 10 cyber threats in April 2026, show a significant increase in attacks targeting misconfigured cloud environments. This isn't a theoretical problem; it's happening now.
Managing multiple clouds overwhelms security teams. They can't keep up with constant configuration changes and new vulnerabilities. This leads to breaches. We see this often during our penetration tests at HackerDesk; teams usually know their primary cloud well but leave the secondary environment wide open.
Defining the security mesh
The Cloud Security Mesh (CSM) isn't a product you buy and install. It is an architectural shift that moves security controls closer to the individual application rather than the network edge. In a multi-cloud setup, the old perimeter is gone, so the security has to follow the data.
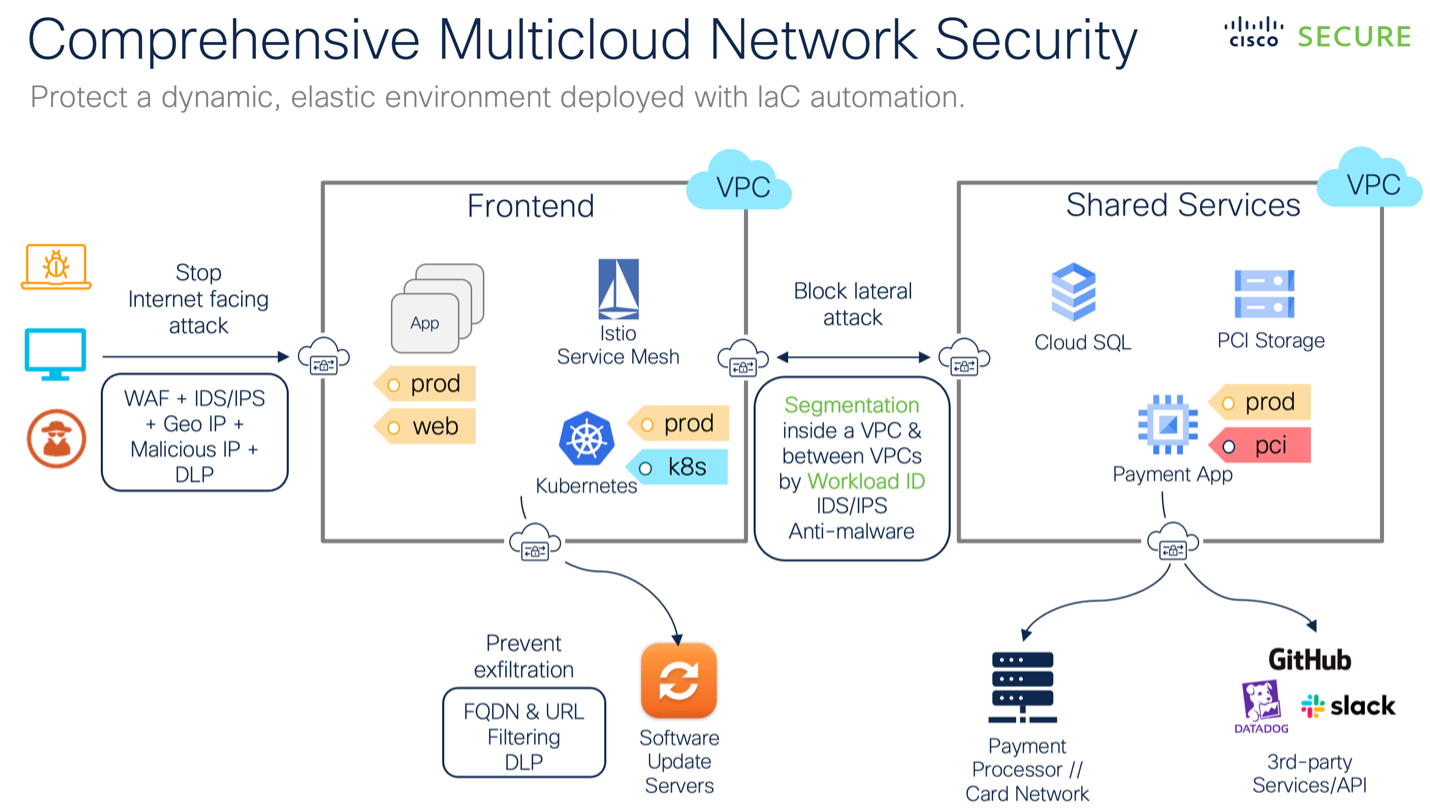
Unlike traditional perimeter-based security, which focuses on protecting the network boundary, a CSM distributes security controls across the cloud environment. This means placing security functions closer to the applications and data they protect, regardless of where those resources reside. Think of it as building a network of interconnected security services.
Three core principles underpin the CSM approach. First, identity-centric security: verifying the identity of every user and device before granting access. Second, data-centric security: protecting data itself, no matter where it lives. And third, automation: using automation to streamline security operations and respond to threats quickly and efficiently.
delivers native anti-MEV execution, multi-cloud security, and direct connections between blockchains and traditional rails. For high-frequency or high-value trading, this setup looks solid.Appreciate projects that solve actual problems at the infrastructure level.@aeredium
— Ravi | Early Roller 🎲 (@Ravi44577653002) May 1, 2026
Core components of a mesh architecture
Building a CSM requires integrating several key components. It starts with robust Identity and Access Management (IAM) that extends across all cloud providers. This means a single source of truth for identity and consistent policies for access control. Properly configured IAM is foundational.
Cloud Access Security Brokers (CASBs) play a vital role in providing visibility and control over cloud applications. They can enforce security policies, detect threats, and prevent data loss. CASBs act as gatekeepers between users and cloud services, monitoring activity and enforcing security rules.
Data Loss Prevention (DLP) solutions are also essential. They help organizations identify and protect sensitive data, preventing it from leaving the organization’s control. DLP can be implemented at the network, endpoint, and cloud levels to provide comprehensive data protection. The goal is to classify, monitor, and protect sensitive information.
Microsegmentation is another critical element. By dividing the cloud environment into smaller, isolated segments, organizations can limit the blast radius of a potential breach. Network security controls, such as firewalls and intrusion detection systems, are deployed within these segments to further enhance security. Finally, comprehensive observability and threat intelligence are needed to detect and respond to threats effectively. You need to see what's happening across all your cloud environments.
How mesh enables zero trust
The principles of a Cloud Security Mesh align remarkably well with the Zero Trust security model. Zero Trust, at its core, assumes that no user or device should be trusted by default, regardless of whether they are inside or outside the network perimeter. CSM provides the architectural foundation to implement Zero Trust effectively.
The principle of least privilege is central to both CSM and Zero Trust. CSM enables granular access control, ensuring that users and applications only have access to the resources they absolutely need. This minimizes the attack surface and reduces the potential impact of a breach. Continuous verification is also a key component, constantly validating the identity and security posture of users and devices.
Microsegmentation, a core element of CSM, directly supports Zero Trust by limiting lateral movement within the cloud environment. If an attacker gains access to one segment, they are prevented from easily moving to other parts of the network. Identity is truly the new perimeter in this model. While CSM isn't strictly Zero Trust in itself, it's a powerful enabler, making it much easier to adopt a Zero Trust approach.
CSM in Action: Real-World Use Cases
Let's look at some practical examples of how CSM can address specific security challenges. Consider a multi-cloud data analytics platform. Data is pulled from various sources, processed in different clouds, and used to generate insights. A CSM can ensure consistent data protection across all stages, preventing unauthorized access and data leakage.
Another use case is protecting sensitive data in a hybrid cloud environment. An organization might store some data on-premises and other data in the cloud. A CSM can provide a unified security layer, ensuring that the same security policies are applied to data regardless of its location. This simplifies compliance and reduces risk.
Finally, imagine a scenario where remote developers are working across multiple clouds. A CSM can enable secure access to cloud resources, verifying the identity of each developer and enforcing access controls based on their role and permissions. This protects sensitive data and prevents unauthorized access. The benefits in each scenario are clear: improved security, reduced complexity, and enhanced compliance.
The shift toward 2026
Over the next few years, we can expect to see increased adoption of Cloud Security Meshes as organizations grapple with the complexities of multi-cloud environments. The demand for more effective and efficient security solutions will continue to drive this trend. I anticipate a significant increase in the use of AI and machine learning for threat detection and response. AI can help automate security tasks, identify anomalies, and respond to threats in real-time.
Greater integration with DevSecOps practices is also on the horizon. This means embedding security into the entire software development lifecycle, from design to deployment. DevSecOps helps organizations build more secure applications and reduce the risk of vulnerabilities. We’ll likely see the emergence of more standardized CSM platforms, making it easier for organizations to adopt and manage this architecture.
The growing importance of cloud-native security tools will also be a key trend. These tools are specifically designed for cloud environments and offer features that traditional security solutions lack. Expect to see more organizations leveraging cloud-native security capabilities to enhance their overall security posture. It’s a dynamic field, and adapting quickly will be essential.
While predicting the future is always uncertain, the direction is clear. Cloud Security Meshes represent a fundamental shift in how organizations approach security in the multi-cloud era. The ability to adapt and embrace this new architecture will be critical for protecting data and applications in the years to come. The work we're doing at HackerDesk shows that organizations that start planning now will be better positioned to succeed.



No comments yet. Be the first to share your thoughts!