The state of security in April 2026
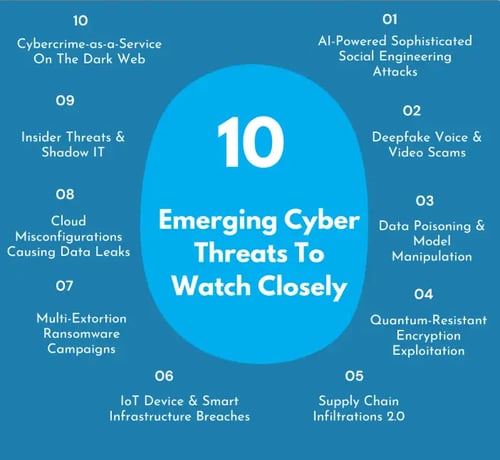
By April 2026, attackers have moved past simple vulnerability scanning. They now probe for logic flaws in complex, interconnected systems. More IoT devices and cloud migrations mean more entry points for anyone looking to get in.
Security teams are shrinking just as the work grows. Most companies can't hire fast enough to keep up with the volume of alerts. This isn't just a technical problem; it's a staffing crisis that leaves doors open.
The pace of change is relentless. What worked as a security measure last year might be insufficient today. Businesses must adopt a mindset of continuous monitoring, adaptation, and improvement to stay ahead of the curve. It’s a challenging environment, but one that demands attention.

Ransomware gets smarter with AI
Ransomware is no longer a blunt instrument. It’s becoming increasingly targeted and effective thanks to the integration of artificial intelligence. Attackers are now using machine learning to analyze potential victims, identify valuable data, and automate the process of vulnerability exploitation.
AI is also being used to craft more convincing phishing campaigns, making it harder for employees to distinguish between legitimate communications and malicious ones. This leads to higher success rates and, consequently, larger ransom demands. The trend of "double extortion"—encrypting data and stealing it—remains prevalent, adding further pressure on victims.
We’re seeing ransom amounts climb significantly. BleepingComputer reported a steady increase throughout 2025, with some organizations paying millions to regain access to their data. The use of AI allows attackers to scale their operations and maximize their profits, making ransomware a particularly lucrative and dangerous cyber threat. The speed and precision AI brings to these attacks are truly alarming.
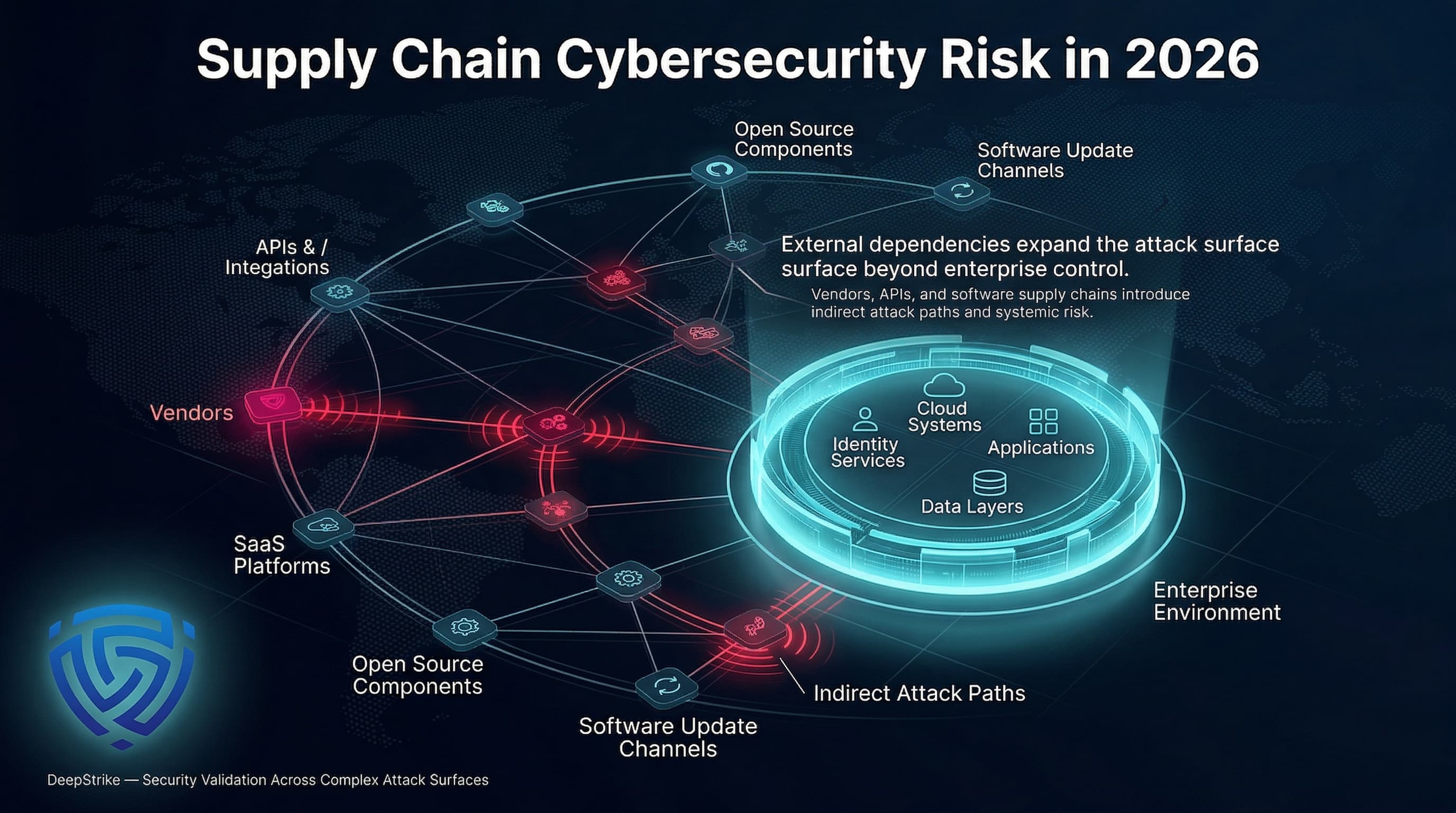
The danger of third-party software
The threat of supply chain attacks continues to loom large. Compromising a single vendor can give attackers access to a vast network of businesses, creating a ripple effect of damage. This is a particularly insidious form of attack because it exploits trust relationships between organizations.
The 2020 SolarWinds breach showed how one compromised vendor can open thousands of doors, including US government networks. Today, attackers focus on smaller suppliers who lack the budget for heavy security but hold the keys to much larger clients.
Due diligence is critical. Businesses need to thoroughly assess the security practices of their vendors and implement robust monitoring to detect any suspicious activity. It’s not enough to simply trust that your vendors are secure; you need to verify it. The interconnected nature of modern business makes supply chain security paramount.
- Audit the security of every third-party vendor at least twice a year.
- Access Control: Implement strict access controls to limit vendor access to only the data and systems they need.
- Monitoring: Continuously monitor vendor activity for suspicious behavior.
Deepfakes and Social Engineering
The rise of deepfake technology presents a new and frightening dimension to social engineering attacks. Attackers can now create realistic audio and video of company executives, using this fabricated content to trick employees into divulging sensitive information or authorizing fraudulent payments.
These deepfakes are becoming increasingly difficult to detect, even for trained professionals. The ability to convincingly mimic a person’s voice and appearance makes it easier for attackers to bypass traditional security measures. This is particularly concerning for organizations that rely on voice authentication or video conferencing.
Employee training is crucial. Workers need to be educated about the risks of deepfakes and how to identify potential scams. A healthy dose of skepticism and a willingness to verify requests through multiple channels are essential defenses. This threat demands a shift in mindset, recognizing that what you see and hear isn’t always what it seems.
IoT devices are widening the net
The proliferation of Internet of Things (IoT) devices has dramatically expanded the attack surface for cybercriminals. From smart thermostats to industrial sensors, these devices often have weak security protocols and are easily compromised. Many were not designed with security as a primary concern.
The sheer number of vulnerable IoT devices is staggering. Estimates vary, but there are now billions of connected devices in use worldwide, and many lack basic security features. This creates a massive network of potential entry points for attackers. Once compromised, these devices can be used as botnets to launch distributed denial-of-service (DDoS) attacks or as stepping stones to infiltrate corporate networks.
Organizations need to carefully assess the security risks associated with IoT devices and implement appropriate safeguards. This includes segmenting IoT devices onto separate networks, regularly patching firmware, and using strong authentication protocols. Ignoring IoT security is no longer an option.
IoT Device Security Risk Assessment - April 2026
| Device Type | Common Vulnerabilities | Potential Impact | Mitigation Strategies |
|---|---|---|---|
| Security Cameras | Weak default passwords, unencrypted communication, outdated firmware, buffer overflows | Data breaches (video footage), unauthorized access to network, denial-of-service attacks | Strong password policies, firmware updates, network segmentation, encryption of video streams |
| Smart Thermostats | Insecure web interfaces, lack of authentication, man-in-the-middle attacks, data privacy concerns | Unauthorized access to building climate control, potential for energy theft, data leakage of occupancy patterns | Multi-factor authentication, secure communication protocols (HTTPS), regular security audits, data encryption |
| Industrial Sensors | Lack of security by design, unpatched vulnerabilities, remote access exploits, supply chain attacks | Disruption of industrial processes, equipment damage, safety hazards, intellectual property theft | Robust access controls, network monitoring, intrusion detection systems, secure boot processes, supply chain risk management |
| Smart Locks | Brute-force attacks, replay attacks, vulnerabilities in Bluetooth/Zigbee protocols, physical tampering | Unauthorized physical access to facilities, theft, vandalism | Strong encryption, regular firmware updates, physical security measures, audit trails |
| Connected Medical Devices | Unencrypted data transmission, weak authentication, software vulnerabilities, lack of regulatory oversight | Patient data breaches, manipulation of device functionality, potential harm to patients | Data encryption, strong authentication, regular security assessments, adherence to medical device security standards |
| Smart Lighting Systems | Insecure wireless communication, lack of authentication, vulnerabilities in mobile apps, denial-of-service attacks | Network compromise, disruption of building operations, potential for surveillance | Secure wireless protocols, strong authentication, regular security updates, network segmentation |
Illustrative comparison based on the article research brief. Verify current pricing, limits, and product details in the official docs before relying on it.
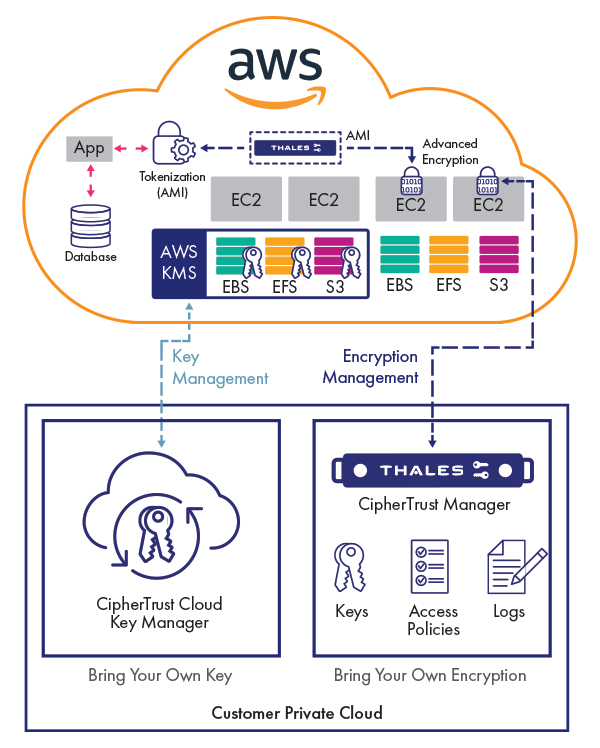
Cloud Misconfigurations: A Persistent Problem
Despite advancements in cloud security, misconfigurations remain a leading cause of data breaches. Simple errors in cloud settings—such as leaving storage buckets publicly accessible—can expose sensitive data to the internet. Human error is often the root cause of these incidents.
The complexity of cloud environments can make it difficult to identify and remediate misconfigurations. Organizations need to implement robust cloud security posture management (CSPM) tools to automate the process of identifying and fixing security vulnerabilities. These tools can continuously monitor cloud environments and alert administrators to potential risks.
Best practices, like the principle of least privilege, are critical. Granting users only the access they need, and regularly reviewing those permissions, can significantly reduce the risk of data breaches. A proactive approach to cloud security is essential.
API Attacks: Exploiting the Connective Tissue
Application Programming Interfaces (APIs) are becoming an increasingly attractive target for attackers. APIs are the connective tissue that allows different applications to communicate with each other, and they often handle sensitive data. Insecure APIs can lead to data breaches, account takeovers, and denial-of-service attacks.
APIs are often overlooked in security assessments. Developers may prioritize functionality over security, leaving APIs vulnerable to exploitation. Common vulnerabilities include lack of authentication, insufficient input validation, and excessive data exposure.
API security testing is essential. Organizations need to regularly scan their APIs for vulnerabilities and implement robust authentication protocols, such as OAuth 2.0. Protecting APIs is crucial for maintaining the security of modern applications.
The Rise of 'Living Off The Land' Attacks
Attackers are increasingly adopting a tactic known as "living off the land" (LotL). This involves using legitimate system tools and processes to carry out malicious activities, making it harder to detect their presence. Instead of introducing new malware, attackers leverage existing tools like PowerShell and Windows Management Instrumentation.
LotL attacks are particularly stealthy because they blend in with normal system activity. Traditional security solutions that rely on signature-based detection may struggle to identify these types of attacks. Detecting LotL requires more sophisticated security monitoring and behavioral analysis.
You have to know what 'normal' looks like on your network. If a system tool like PowerShell suddenly starts acting up, you need to catch it immediately. It's about watching behavior, not just looking for a virus file.
Critical Infrastructure Under Fire
Critical infrastructure—including power grids, water treatment plants, and transportation systems—is facing an escalating threat from cyberattacks. These attacks have the potential to cause widespread disruption and damage, with far-reaching consequences.
The World Economic Forum has repeatedly warned about the growing risk of attacks on critical infrastructure. These systems are often outdated and lack adequate security measures, making them vulnerable to exploitation. A successful attack could disrupt essential services and endanger public safety.
Strengthening the cybersecurity of critical infrastructure is a national priority. This requires increased investment in security technologies, improved information sharing, and closer collaboration between government and industry. The stakes are incredibly high.
- Power grids remain a primary target for state-sponsored groups looking to cause blackouts.
- Water Treatment Plants: Susceptible to attacks that could contaminate water supplies.
- Transportation Systems: At risk of attacks that could disrupt air travel, rail networks, and shipping lanes.
Fortify Your Defenses: Top Hardware Security Modules and Network Appliances for Business Protection
High-performance cryptographic processing · Secure key generation and management · Tamper-resistant hardware security module
This hardware security module provides robust protection against emerging cyber threats, ensuring the integrity and availability of your critical business infrastructure.
Secure key lifecycle management · Compliance with industry security standards · Versatile cryptographic functions
This hardware security module provides robust protection against emerging cyber threats, ensuring the integrity and availability of your critical business infrastructure.

Next-generation firewall capabilities · Intrusion prevention and detection · Advanced threat protection services
This hardware security module provides robust protection against emerging cyber threats, ensuring the integrity and availability of your critical business infrastructure.

Next-generation firewall features · Application control and visibility · Integrated intrusion prevention system
This hardware security module provides robust protection against emerging cyber threats, ensuring the integrity and availability of your critical business infrastructure.
As an Amazon Associate I earn from qualifying purchases. Prices may vary.



No comments yet. Be the first to share your thoughts!