The shift in May 2026
The cybersecurity landscape in May 2026 is markedly different than even a year prior. Both the White House and the New Jersey Cybersecurity and Communications Integration Cell (NJCCIC) indicate a significant escalation in the sophistication and frequency of cyber attacks. New Jersey currently operates at an “ELEVATED” cyber alert level, mirroring a national trend toward heightened vigilance. This isn’t simply an increase in volume; the nature of the attacks is changing.
We’re seeing a clear shift toward more targeted and complex operations, driven by both financially motivated criminals and nation-state actors. The White House’s March 2026 Cyber Strategy explicitly acknowledges the growing threat of non-kinetic powers and the need to maintain dominance in cyberspace. This strategy frames cybersecurity not just as a defensive measure, but as a critical component of national security and economic prosperity.
A key component of this shift is the increasing use of artificial intelligence and automation by attackers. This allows them to scan for vulnerabilities at scale, craft highly personalized phishing campaigns, and evade traditional security measures with greater ease. The NJCCIC assessment corroborates this, noting a rise in attacks leveraging AI-powered tools. It’s a race to adapt, and currently, the attackers seem to be gaining ground.
Software bills of materials and the supply chain
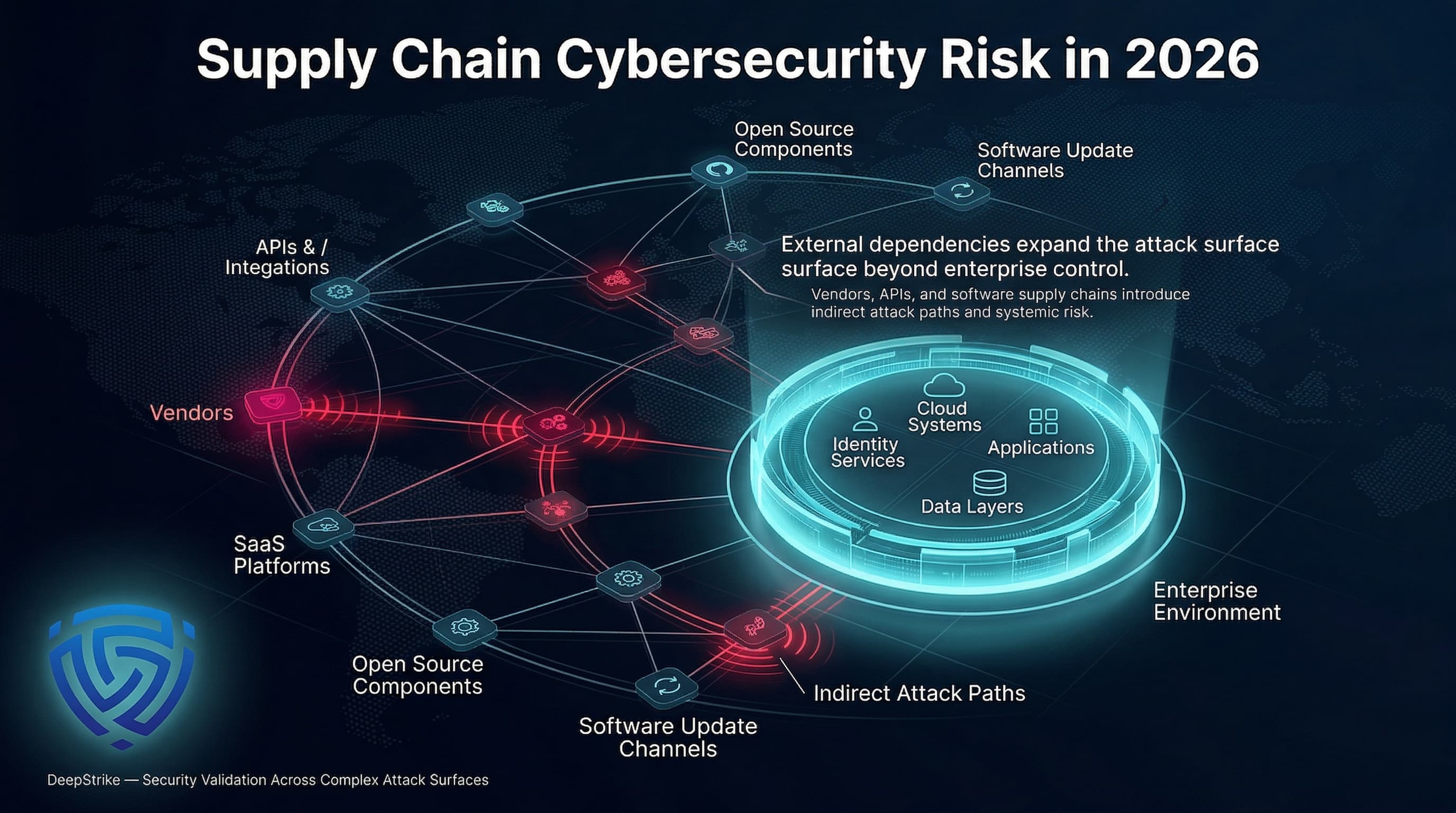
The interconnectedness of modern software development has created a significant new attack vector: the supply chain. Attackers are increasingly targeting software vendors and third-party suppliers to gain access to a wide range of organizations. A compromise at a single point in the supply chain can have a ripple effect, impacting countless customers.
The White House Cyber Strategy places a strong emphasis on improving supply chain security, advocating for the widespread adoption of Software Bills of Materials (SBOMs). An SBOM is essentially a comprehensive inventory of all the components that make up a software application. This allows organizations to quickly identify and mitigate vulnerabilities in their software supply chain.
Implementing SBOMs isn’t without its challenges. It requires collaboration between software vendors and their customers, as well as the development of standardized formats and tools. However, the potential benefits – increased transparency and improved security – far outweigh the costs. While the NJCCIC source doesn’t delve into specifics, the need for robust supply chain security is implicitly understood given the broader threat landscape.
The reality of AI-powered attacks
Artificial intelligence is a double-edged sword in the cybersecurity realm. While AI can be used to enhance defenses, it’s also being weaponized by attackers. We're seeing a surge in AI-powered phishing campaigns that are incredibly convincing and difficult to detect. These campaigns use natural language processing to craft personalized emails that mimic legitimate communications.
Beyond phishing, AI is being used for automated vulnerability discovery, allowing attackers to scan networks and systems for weaknesses at scale. AI can also be used to create polymorphic malware – malicious code that constantly changes its appearance to evade detection. The speed and scale of these attacks are unprecedented.
AI isn't a magic bullet. It is a tool. Defenders use it to automate detection, but attackers are already finding ways around those filters. The White House strategy calls for more R&D money to keep up, but money alone won't fix the vulnerability of these models.
Nation-state actors
Nation-state actors remain a significant and persistent threat to cybersecurity. These actors have the resources, expertise, and motivation to conduct sophisticated attacks that can have far-reaching consequences. Their primary targets include critical infrastructure, government agencies, and intellectual property.
The White House’s Cyber Strategy identifies several key nation-state adversaries, although it doesn’t name them specifically. It details their tactics, techniques, and procedures (TTPs), and outlines a strategy for deterring and responding to their attacks. These actors are constantly evolving their tactics to evade detection and achieve their objectives.
There are indications of increased collaboration between nation-state actors, with some countries sharing intelligence and resources to conduct joint operations. This makes it even more difficult to attribute attacks and hold perpetrators accountable. The strategy emphasizes the importance of international cooperation to counter these threats, but achieving consensus among nations is a significant challenge.
The zero-day race
Zero-day exploits – vulnerabilities that are unknown to the software vendor – pose a particularly serious threat. Because there are no patches available, organizations are left scrambling to defend themselves using other measures, such as intrusion detection systems and firewalls. The discovery and exploitation of zero-day vulnerabilities is a constant race against time.
The most common vulnerabilities being exploited include buffer overflows, SQL injection, and cross-site scripting. However, attackers are also increasingly targeting more complex vulnerabilities, such as those related to cloud computing and IoT devices. Keeping systems up to date with the latest security patches is crucial, but it’s not always enough to protect against zero-day exploits.
Vulnerability disclosure programs and bug bounty programs can help organizations identify and fix vulnerabilities before they are exploited by attackers. These programs incentivize security researchers to report vulnerabilities responsibly. However, it's important to acknowledge that defending against zero-day exploits is incredibly difficult, and even the most sophisticated organizations can be compromised.
Nation-State Actor TTP Comparison - May 2026
| Actor | Primary Objectives | Common Attack Vectors | Observed Targets | Sophistication Level |
|---|---|---|---|---|
| Russia | Geopolitical influence, espionage, disruption of critical infrastructure | Supply chain attacks, disinformation campaigns, spear-phishing, exploitation of zero-day vulnerabilities | Government agencies, energy sector, media organizations, election infrastructure | High - Demonstrates advanced capabilities and persistent threat activity |
| China | Intellectual property theft, economic espionage, strategic advantage | Supply chain compromise, large-scale data breaches, state-sponsored hacking, use of compromised infrastructure | Defense contractors, technology companies, telecommunications providers, research institutions | High - Extensive resources and a broad range of techniques |
| Iran | Regional influence, disruption, retaliation against perceived adversaries | Website defacement, DDoS attacks, data deletion, spear-phishing targeting specific individuals | Critical infrastructure (particularly in Middle East and US), government organizations, financial institutions | Moderate to High - Increasing sophistication and willingness to take aggressive action |
| North Korea | Funding acquisition, intelligence gathering, disruption of adversaries | Financial cybercrime (cryptocurrency theft, bank heists), destructive malware attacks, supply chain attacks | Financial institutions, cryptocurrency exchanges, media organizations, government agencies | Moderate - Relies heavily on disruptive attacks and financial gain |
| Syria | Espionage, intelligence gathering, disruption | Spear-phishing, malware deployment via compromised websites, social engineering | Political dissidents, government organizations, military targets | Low to Moderate - Limited resources, but persistent and opportunistic |
| Vietnam | Espionage, political intelligence, economic gain | Supply chain attacks, targeted malware, credential harvesting | Government, defense, and technology sectors, particularly those with ties to the South China Sea | Moderate - Increasing capabilities and focus on targeted attacks |
Illustrative comparison based on the article research brief. Verify current pricing, limits, and product details in the official docs before relying on it.
Practical mitigation steps
You need layers. Start with multi-factor authentication (MFA). It is the most basic hurdle for an attacker. Patch your software every week, not every quarter. If you aren't running regular security assessments to find your own weaknesses, the NJCCIC will likely find them for you after a breach.
Employee training is another vital component. Phishing attacks remain one of the most common attack vectors, and employees need to be able to recognize and avoid them. The White House strategy stresses the importance of a "whole-of-nation" effort to improve cybersecurity awareness and education.
Beyond these basics, organizations should consider implementing advanced security technologies, such as intrusion detection and prevention systems, security information and event management (SIEM) systems, and endpoint detection and response (EDR) solutions. The NJCCIC assessment recommends a defense-in-depth strategy, combining multiple layers of security to provide comprehensive protection. Regularly review and update your incident response plan to ensure you’re prepared to respond effectively to a cyber attack.
iOS 26.4.2 is Out - This update provides bug fixes and security updates for iPhone. I’ll be testing the software and update you guys tomorrow with any bug fixes that I Notice. pic.twitter.com/lsqglkW2Fl
— iDeviceHelp (@iDeviceHelpus) April 22, 2026



No comments yet. Be the first to share your thoughts!