The quantum threat
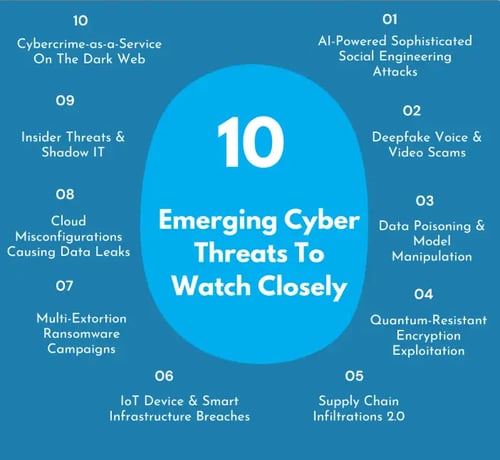
For decades, the security of our digital world has rested on the difficulty of certain mathematical problems. Algorithms like RSA and ECC, the workhorses of modern encryption, are considered secure because breaking them would require an impractical amount of computing power – for classical computers, at least. That’s all changing with the rapid advancement of quantum computing.
Quantum computers, leveraging the principles of quantum mechanics, approach computation in a fundamentally different way. Shor’s algorithm, developed in 1994, demonstrates that a sufficiently powerful quantum computer could break RSA and ECC encryption in a timeframe that renders them useless. This isn’t a hypothetical threat; it’s a growing concern as quantum computing technology matures.
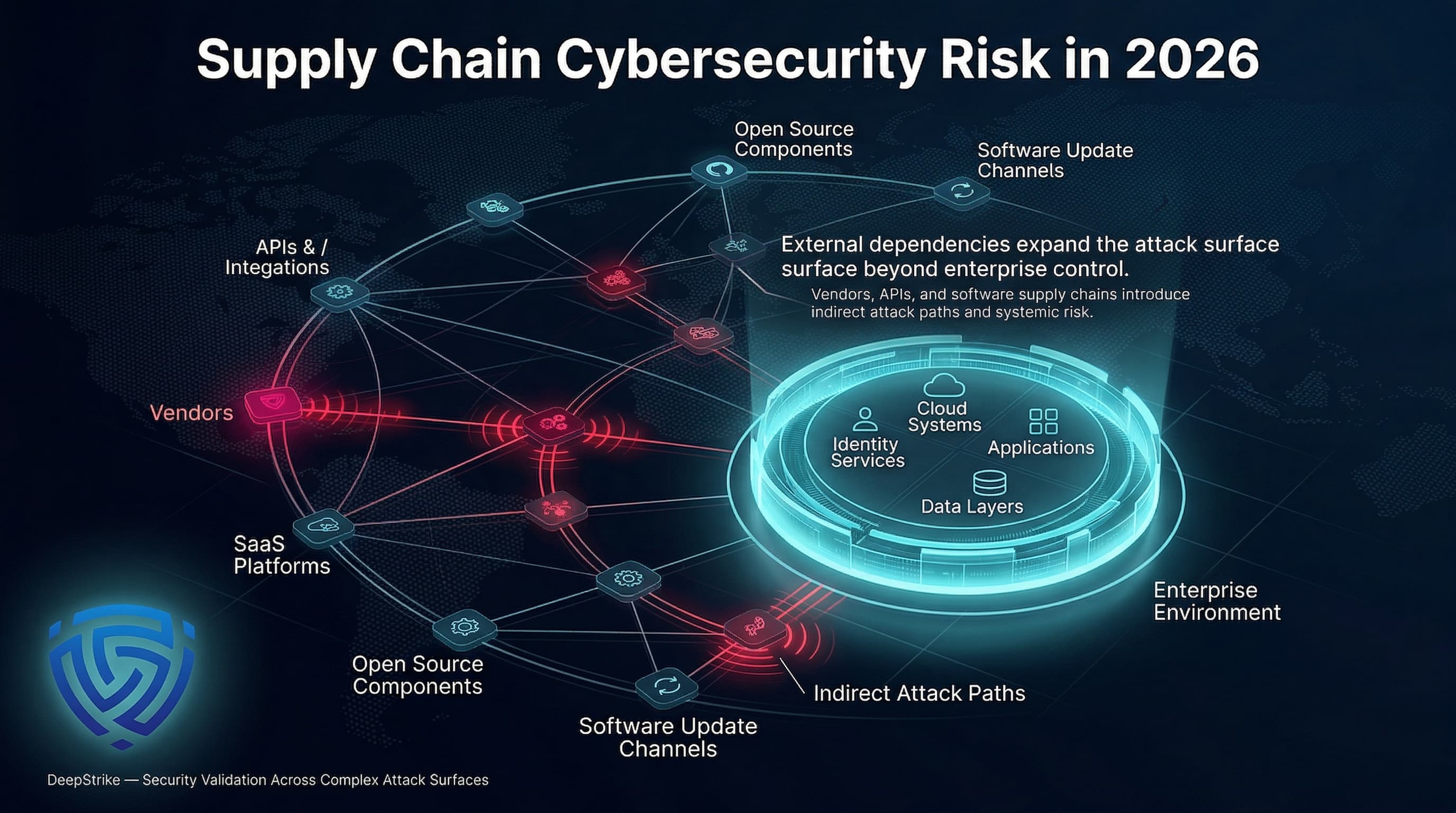
The urgency stems from the "store now, decrypt later" attack scenario. Malicious actors could be collecting encrypted data today, anticipating the availability of quantum computers capable of decryption in the future. This makes protecting data with long-term confidentiality – things like state secrets, intellectual property, and personal records – particularly critical.
NIST expects to finalize its post-quantum standards by 2026. This isn't a hard deadline, but it marks when organizations should move from research to implementation. The actual migration will likely take a decade.
NIST post-quantum standards
Recognizing the quantum threat, NIST launched a standardization process in 2016 to identify and evaluate candidate post-quantum cryptographic (PQC) algorithms. This rigorous process involved public review, analysis by cryptographic experts, and extensive testing. In 2022, NIST announced the first four algorithms selected for standardization, with more to come.
The initial group includes CRYSTALS-Kyber for key encapsulation – essentially, securely exchanging encryption keys – and CRYSTALS-Dilithium, FALCON, and SPHINCS+ for digital signatures, which verify the authenticity and integrity of digital documents. These algorithms represent the first wave of officially endorsed PQC solutions, though it's important to remember they aren’t the only viable options.
CRYSTALS-Kyber is a lattice-based Key Encapsulation Mechanism (KEM) offering strong security and relatively fast performance. It’s designed as a drop-in replacement for algorithms like RSA-KEM and ECC-KEM. CRYSTALS-Dilithium, also lattice-based, provides a digital signature scheme with a focus on speed and security. FALCON is another lattice-based signature scheme, prioritizing smaller signature sizes.
SPHINCS+ stands apart from the others as a hash-based signature scheme. It relies on the security of cryptographic hash functions, making it resistant to attacks even if lattice-based algorithms were to be compromised. However, hash-based signatures generally have larger signature sizes and slower performance than lattice-based schemes. NIST released further selections in 2024, solidifying a more diverse set of standards.
It’s crucial to understand that NIST’s selection isn’t a declaration that these algorithms are perfect or immune to future attacks. It signifies that, based on current knowledge, they represent the best available options for securing our data against both classical and quantum computers. Ongoing research continues to refine these algorithms and explore new approaches.
NIST Post-Quantum Cryptography Standards Comparison
| Algorithm | Type | Key Size | Performance | Security Assumptions |
|---|---|---|---|---|
| CRYSTALS-Kyber | Key Encapsulation Mechanism (KEM) | Relatively small; multiple security levels available | Generally fast; efficient for most applications | Based on the hardness of Module-LWE problem |
| CRYSTALS-Dilithium | Digital Signature | Moderate key and signature sizes | Good performance; balances speed and security | Based on the hardness of Module-LWE and Fiat-Shamir with Aborts assumptions |
| Falcon | Digital Signature | Small signature sizes | Potentially faster signature generation, but verification can be more complex | Based on the Shortest Integer Solution (SIS) problem on lattices |
| SPHINCS+ | Digital Signature | Large signature sizes | Slower performance compared to lattice-based signatures, but stateless | Based on the hardness of Multivariate Quadratic (MQ) problem |
Illustrative comparison based on the article research brief. Verify current pricing, limits, and product details in the official docs before relying on it.
How lattice-based math works
CRYSTALS-Kyber and CRYSTALS-Dilithium, two of the foundational NIST selections, are based on a mathematical concept called lattice-based cryptography. Lattices, in this context, are essentially multi-dimensional grids of points. Problems involving finding the "shortest’ vector or the ‘closest" point within a lattice are believed to be computationally hard for quantum computers.
The security of lattice-based cryptography stems from the difficulty of solving these lattice problems, even with the power of quantum computers. While RSA and ECC rely on the difficulty of factoring large numbers or computing discrete logarithms, lattice-based schemes operate on a different mathematical foundation, making them resistant to Shor’s algorithm.
Think of it like this: RSA is like trying to find the prime factors of a very large number—a problem easy to state but incredibly hard to solve for classical computers. Lattice-based cryptography is like trying to find a hidden point within a complex, high-dimensional grid—a different kind of hard problem. Both are difficult, but Shor’s algorithm only breaks the first type.
The 'hardness' of lattice problems isn't mathematically proven like prime factorization is. Instead, we rely on the fact that decades of research haven't produced an efficient way to break them. It remains the most solid foundation we have for quantum resistance.
Other cryptographic approaches
While the NIST selections are a significant step forward, research into post-quantum cryptography is far from over. Several other cryptographic families show potential, each with its own strengths and weaknesses. Code-based cryptography, such as the McEliece cryptosystem, relies on the difficulty of decoding general linear codes. It boasts a long history and is relatively well-understood.
Multivariate cryptography uses systems of polynomial equations over finite fields. These systems are generally hard to solve, but constructing secure schemes has proven challenging. Hash-based signatures, like SPHINCS+, offer strong security guarantees but often come with larger signature sizes and slower performance. Isogeny-based cryptography, a more recent development, utilizes mathematical structures called elliptic curves and their isogenies.
Each of these approaches has its own set of trade-offs. Code-based cryptography has large key sizes, multivariate cryptography has faced security vulnerabilities, hash-based signatures are slow, and isogeny-based cryptography is relatively new and requires further analysis. There isn’t a single "silver bullet" solution; diversity in cryptographic algorithms is crucial for resilience.
The ongoing research and development in PQC are essential. It’s possible that new algorithms will emerge that offer better performance, smaller key sizes, or stronger security guarantees than the current candidates. The field is dynamic, and staying informed about the latest advancements is important.
Migration hurdles
Transitioning to post-quantum cryptography isn’t a simple matter of swapping out algorithms. It presents significant challenges, including key management, performance overhead, integration with existing systems, and the need for a phased approach. Existing key management infrastructure may not be compatible with the larger key sizes of some PQC algorithms.
The performance impact of PQC algorithms can also be a concern. Some algorithms are computationally more expensive than their classical counterparts, potentially impacting application performance. Integrating PQC into existing systems requires careful planning and testing. Many systems were built with the assumption of specific key sizes and algorithm characteristics.
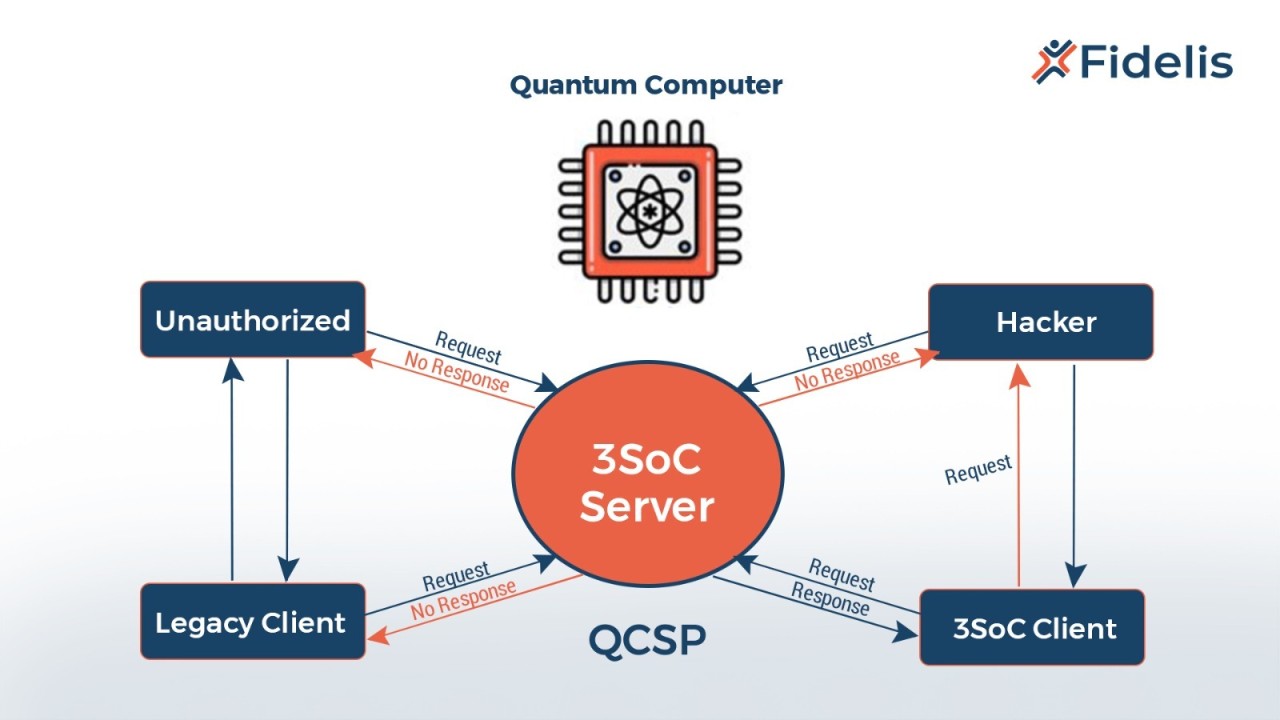
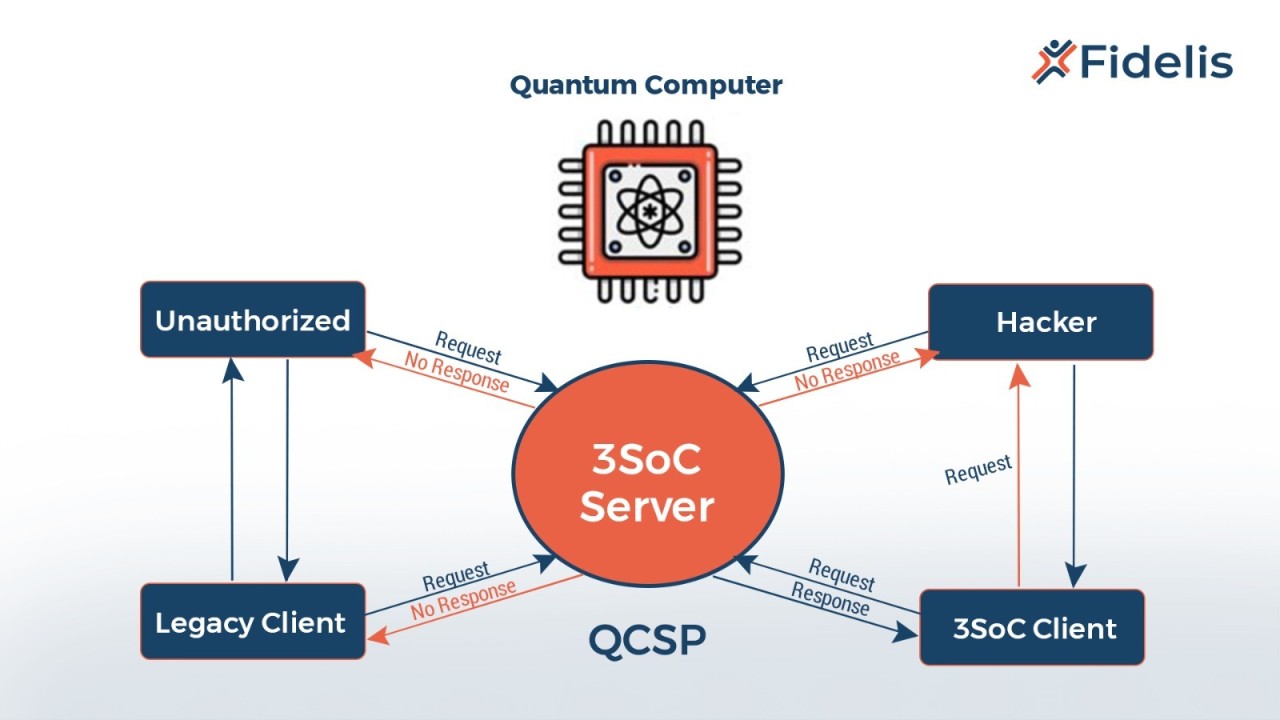
A key strategy is crypto agility – designing systems that can easily switch between different cryptographic algorithms. This allows organizations to adapt to new threats and take advantage of improvements in PQC algorithms. Another important approach is hybrid key exchange, where both classical and post-quantum algorithms are used simultaneously.
Hybrid key exchange provides a fallback mechanism: even if the post-quantum algorithm is compromised, the classical algorithm can still provide security. It also allows organizations to gradually transition to PQC without disrupting existing services. Phased implementation is crucial. Start by protecting the most critical data and systems, and then gradually expand the scope of PQC deployment.
Updates to common protocols
The move to post-quantum cryptography will have a widespread impact on the protocols that underpin our digital communications. TLS/SSL, the protocol that secures web traffic (HTTPS), is being updated to support PQC algorithms. Draft standards already exist for incorporating Kyber into TLS 1.3, and work is underway to support other PQC algorithms.
SSH, used for secure remote login, is also being adapted to include PQC. The OpenSSH project has been experimenting with PQC algorithms, and support for these algorithms is expected to become more widespread in future releases. VPNs, which create secure tunnels for network traffic, will also need to adopt PQC to maintain their security.
DNSSEC, which secures the Domain Name System, is another critical protocol that needs to be updated. Protecting DNS from quantum attacks is essential to prevent disruption of internet services. Standardization efforts are underway to incorporate PQC into DNSSEC. These updates aren’t always seamless.
Implementing PQC in these protocols requires careful coordination between developers, standards bodies, and system administrators. Compatibility issues and performance considerations need to be addressed. The transition will likely be gradual, with hybrid approaches being used to ensure backward compatibility.
Tools and Libraries for Developers
For developers eager to experiment with PQC, several tools and libraries are available. OpenSSL, the widely used cryptography library, is being updated to support PQC algorithms. These updates will allow developers to easily integrate PQC into their applications.
Liboqs (Library of Quantum-Safe Cryptography) is an open-source library that provides a standardized interface for accessing various PQC algorithms. It simplifies the process of integrating PQC into existing codebases. Other resources include implementations of PQC algorithms in languages like C and Python.
These libraries are still evolving, so expect API changes. They are the best starting point for testing quantum-safe features today. I'll keep an eye on these releases as the standards solidify.
While specific class and method names are constantly evolving, the general trend is toward easier integration of PQC algorithms into existing cryptographic frameworks. Focusing on high-level APIs and standardized interfaces will simplify the transition.
PQC Resources for Developers
- OpenSSL - OpenSSL 3.0 and later versions include support for post-quantum cryptography algorithms, allowing developers to integrate these algorithms into existing applications. Refer to the official documentation for implementation details and supported algorithms.
- liboqs - This open-source library provides a standardized interface for various post-quantum cryptographic algorithms. It facilitates experimentation and integration of PQC schemes into different projects.
- NIST PQC Website - The National Institute of Standards and Technology (NIST) is leading the standardization effort for post-quantum cryptography. Their website is the central repository for information on the PQC standardization process, including algorithm specifications and evaluation results.
- CRYSTALS-Kyber - As one of the algorithms selected by NIST for standardization, CRYSTALS-Kyber is a key-encapsulation mechanism (KEM) offering strong security and performance characteristics. Understanding its specifications is crucial for developers.
- Falcon - Another NIST-selected algorithm, Falcon is a digital signature scheme designed for efficiency and security. Developers should review its documentation for implementation considerations.
- SPHINCS+ - This stateless hash-based signature scheme, also standardized by NIST, offers a different approach to digital signatures with inherent resistance to certain quantum attacks. It's valuable for applications requiring long-term security.
- PQClean - PQClean is a collection of clean, portable implementations of post-quantum cryptography algorithms. It aims to provide a practical and easy-to-use resource for developers.



No comments yet. Be the first to share your thoughts!