Ransomware trends for 2026
The ransomware threat in 2026 isn’t simply more of the same; it’s fundamentally different. Predictions for the coming years suggest a shift away from broad, indiscriminate attacks towards more targeted and sophisticated operations. Thehackernews.com’s 2026 cybersecurity predictions point to a continued rise in attacks exploiting vulnerabilities in the software supply chain and an increased focus on data exfiltration followed by extortion. This means simply preventing initial infection isn’t enough—organizations need to assume compromise and focus on minimizing the damage.
We’re seeing attackers become more selective, prioritizing targets based on their ability to pay and the potential for significant disruption. This isn't just about financial gain either; geopolitical motivations and espionage are increasingly intertwined with ransomware attacks. The Federal Communications Commission (FCC) has responded to these evolving threats with guidance (DA 26-96, January 29, 2026) urging communications providers to bolster cybersecurity practices, recognizing the critical role they play in protecting national infrastructure.
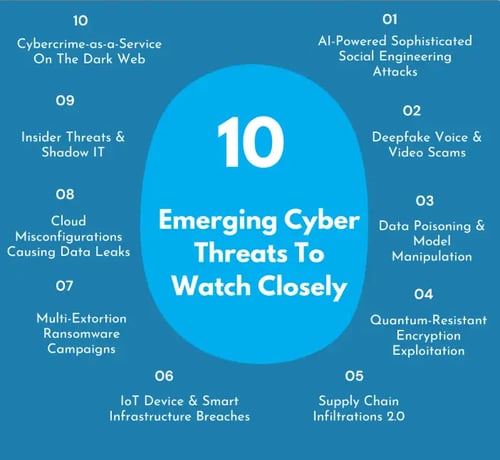
Cybersecurity Ventures data indicates that ransomware will remain a top 10 AI threat in 2026, further complicating the security picture. The overall risk level is elevated, demanding a proactive and adaptive security posture. Organizations can’t rely on reactive measures or outdated security tools. A fundamental shift in mindset is required – one that prioritizes resilience and continuous monitoring over simply trying to prevent all attacks.
The danger of poisoned SDKs
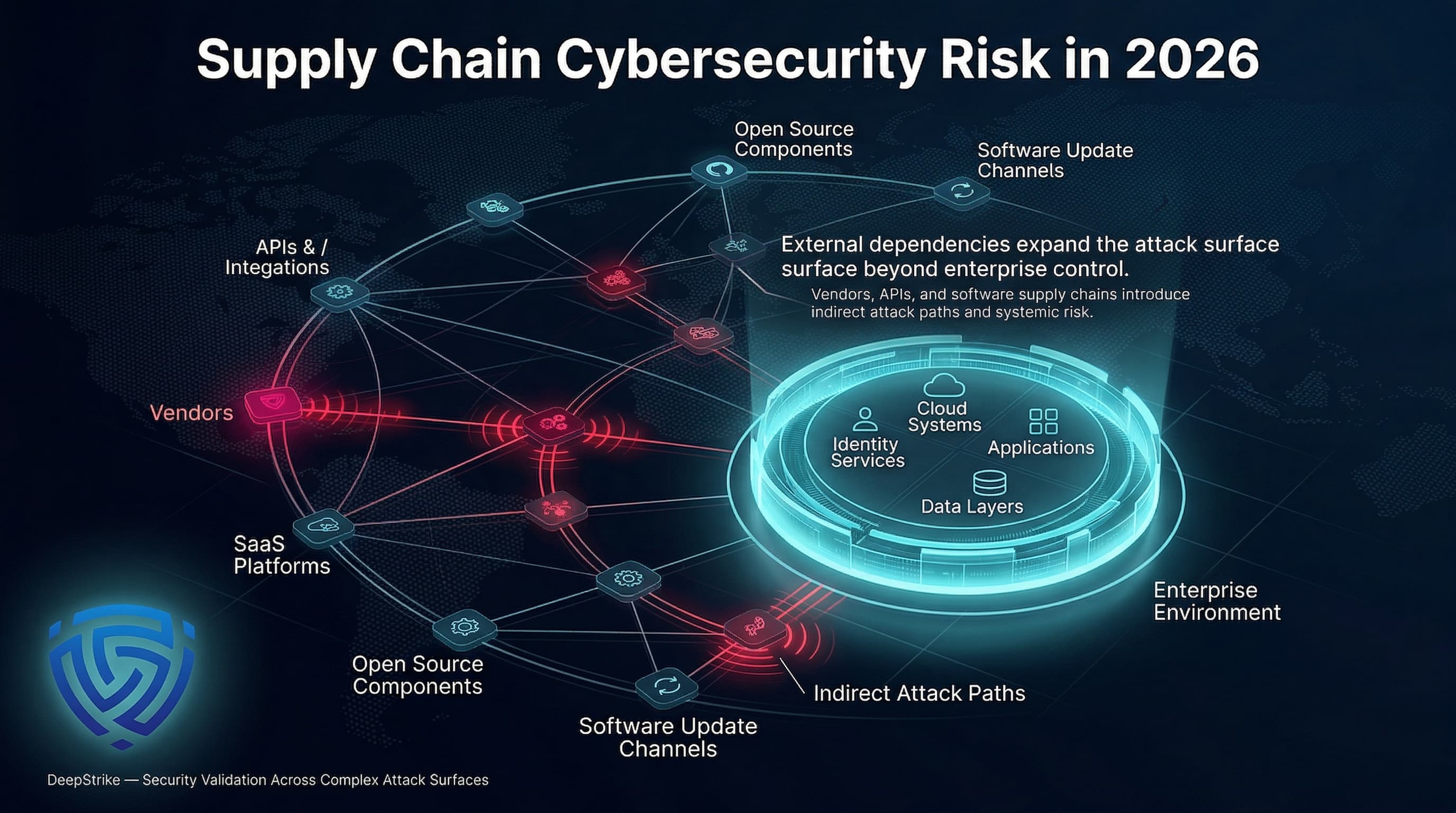
One of the most concerning trends is the rise of software development kit (SDK) poisoning. Attackers are increasingly targeting legitimate SDKs – the building blocks used by developers to add functionality to their applications – and injecting malicious code. This allows them to distribute ransomware to a wide range of users through seemingly trusted software.
The challenge with SDK poisoning is its subtlety. Traditional signature-based detection methods are often ineffective because the malicious code is embedded within legitimate components. Identifying compromised SDKs requires deep visibility into the software supply chain and sophisticated analysis techniques. This is incredibly difficult, especially for organizations that rely on a multitude of third-party libraries and dependencies.
This tactic is particularly insidious because it bypasses many common security controls. It’s not about exploiting a vulnerability in your code; it’s about exploiting a vulnerability in code you trust. I think this is where things get really tricky for security teams, demanding a new level of scrutiny and a more proactive approach to vendor risk management.
AI and polymorphic code
Artificial intelligence is no longer just a theoretical threat; attackers are actively leveraging AI to enhance their ransomware capabilities. Specifically, we’re seeing the emergence of AI-powered polymorphic ransomware – variants that can automatically modify their code to evade detection by signature-based antivirus and other traditional security tools.
This isn't simply about faster mutation; it’s about intelligent evasion. AI algorithms can analyze security responses in real-time and adapt the ransomware's behavior accordingly. For example, if a particular code pattern is flagged as malicious, the AI can quickly generate a new variant that avoids that pattern. This creates a constant cat-and-mouse game, making it increasingly difficult for defenders to keep up.
The use of AI also extends to other aspects of the attack chain, such as reconnaissance and lateral movement. Attackers can use AI to identify vulnerable systems and prioritize targets, as well as to automate the process of spreading ransomware across a network. This requires a shift in defensive thinking – focusing on behavior analysis and anomaly detection rather than relying solely on signature-based detection.
- Identify suspicious activity through behavioral analysis rather than relying on static malware signatures.
- Flag deviations by establishing a baseline of what normal network traffic looks like.
- Use machine learning models to classify malicious activity in real-time.
The RaaS market is specializing
The Ransomware-as-a-Service (RaaS) model continues to thrive, lowering the barrier to entry for aspiring cybercriminals. RaaS platforms provide all the tools and infrastructure needed to launch a ransomware attack, from the ransomware itself to the payment negotiation services. This allows even individuals with limited technical skills to participate in ransomware operations.
We're seeing a trend towards increased specialization within the RaaS ecosystem. Some platforms now offer dedicated exfiltration specialists who focus on stealing sensitive data before encrypting systems, increasing the pressure on victims to pay the ransom. Others provide professional negotiation teams to handle communications with victims and maximize profits.
I'm not sure if we’ll see entirely new RaaS models, but I expect existing ones to become more modular. Attackers will likely offer a wider range of services on a pay-per-use basis, allowing them to customize attacks to specific targets and maximize their revenue potential.
Attacks on industrial systems
The increasing targeting of Operational Technology (OT) systems – industrial control systems, critical infrastructure, etc. – is a major cause for concern. These systems, which control essential services like power grids, water treatment plants, and manufacturing facilities, are often poorly secured and highly vulnerable to attack.
OT systems were traditionally isolated from corporate networks, but that’s no longer the case. Increased connectivity and the adoption of Industrial Internet of Things (IIoT) devices have created new attack vectors. A successful ransomware attack on an OT system could have devastating consequences, ranging from service disruptions to physical damage and even loss of life.
The FCC guidance (DA 26-96) emphasizes the importance of protecting communications networks that support OT systems. This includes implementing robust cybersecurity measures, conducting regular risk assessments, and developing incident response plans specifically tailored to OT environments. This is a serious concern, and the impact goes far beyond data breaches – it threatens the stability of critical infrastructure.
Where EDR falls short
While Endpoint Detection and Response (EDR) solutions remain an important part of a comprehensive security strategy, they are no longer sufficient on their own. The evolving tactics of ransomware attackers – particularly the use of SDK poisoning and AI-powered evasion – are increasingly bypassing traditional EDR detection methods.
EDR solutions are often reactive, relying on identifying known threats and suspicious behavior. They struggle to detect novel attacks or attacks that are carefully crafted to avoid detection. Furthermore, EDR can generate a high volume of alerts, overwhelming security teams and leading to alert fatigue.
I think a lot of companies are over-reliant on EDR and haven’t adequately prepared for more advanced attacks. A layered security approach is essential, combining EDR with other security controls such as network segmentation, intrusion detection systems, and threat intelligence feeds.
Zero trust and segmentation
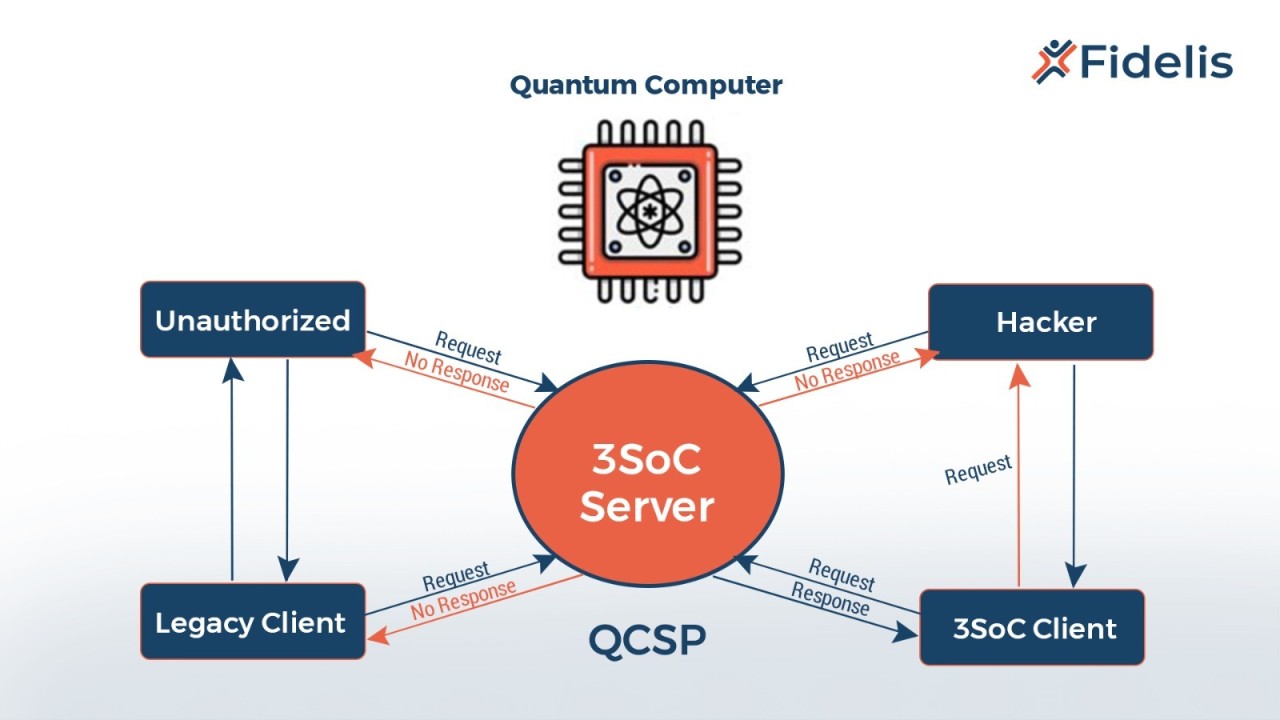
Proactive security measures are crucial for defending against ransomware. Two of the most effective approaches are Zero Trust architecture and network segmentation. Zero Trust assumes that no user or device is inherently trustworthy, regardless of its location or network connection. This means verifying every access request and enforcing the principle of least privilege.
Network segmentation involves dividing the network into smaller, isolated segments. This limits the blast radius of an attack, preventing ransomware from spreading laterally across the entire network. If one segment is compromised, the attacker’s ability to access other critical systems is significantly reduced.
Implementing Zero Trust requires a multi-faceted approach, including strong authentication, microsegmentation, and continuous monitoring. For example, you could implement multi-factor authentication (MFA) for all users, restrict access to sensitive data based on user roles, and use network firewalls to isolate critical systems. Segmentation can be achieved through VLANs, firewalls, or software-defined networking (SDN).
Network Segmentation Strategies for Ransomware Defense – A Comparative Overview
| Segmentation Approach | Implementation Complexity | Performance Impact | Security Effectiveness | Cost Considerations |
|---|---|---|---|---|
| Traditional VLANs | Lower | Minimal | Basic – Limits lateral movement within defined broadcast domains | Generally Lower |
| Firewall Segmentation | Moderate | Moderate – Dependent on firewall capacity and rule complexity | Good – Enforces access control policies between segments | Moderate – Requires firewall infrastructure and expertise |
| Microsegmentation | Higher | Potentially Higher – Requires careful policy design to avoid bottlenecks | Better for – Granular control, significantly limits blast radius of attacks | Higher – Often requires specialized tools and significant administrative overhead |
| Software-Defined Networking (SDN) with Segmentation | Moderate to Higher | Variable – Can be optimized, but requires skilled configuration | Good to Better for – Flexible, policy-driven segmentation, adaptable to changing threats | Moderate to Higher – Initial investment in SDN infrastructure and ongoing management |
| Zero Trust Network Access (ZTNA) | Higher | Moderate – Focus on user and device authentication, minimizing broad network access | Better for – Assumes no trust, verifies every access request, strong protection against compromised credentials | Moderate to Higher – Requires identity and access management integration and policy enforcement |
| Hybrid Approach (VLANs + Firewalls + Microsegmentation) | Highest | Variable – Dependent on implementation choices | Highest – Combines strengths of multiple approaches for layered defense | Higher – Most comprehensive, but also most complex and expensive |
Qualitative comparison based on the article research brief. Confirm current product details in the official docs before making implementation choices.



No comments yet. Be the first to share your thoughts!