The rising tide of supply chain attacks
Supply chain attacks are escalating in both frequency and severity, presenting a significant threat to organizations of all sizes. We’ve seen this play out with high-profile incidents like the SolarWinds attack in 2020, where malicious code was inserted into Orion software updates, impacting thousands of organizations, including several US government agencies. More recently, the MOVEit Transfer vulnerability in 2023 exposed the data of millions, demonstrating that even widely used file transfer tools aren’t immune.
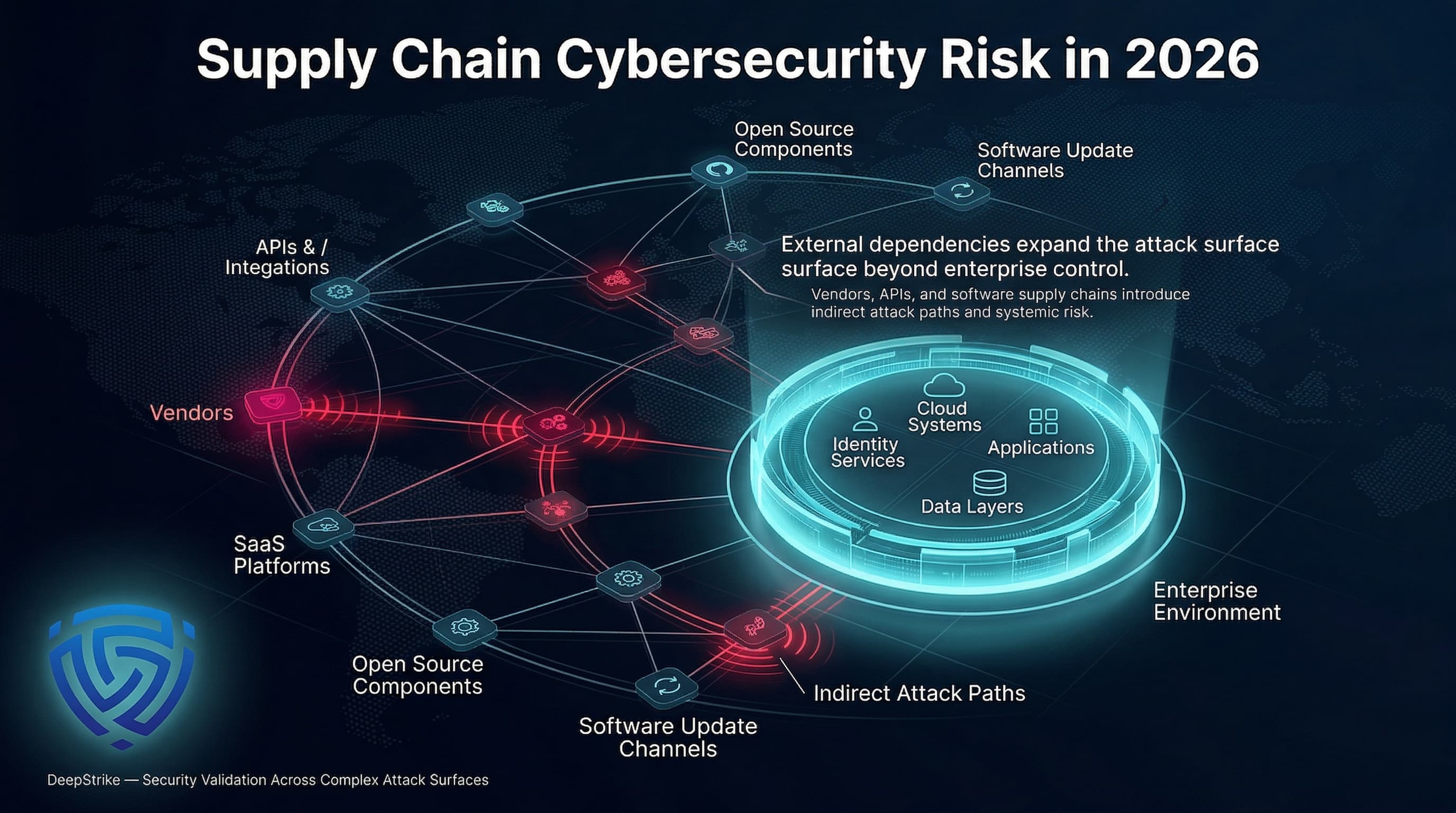
What makes these attacks so effective is the trust placed in third-party vendors. Attackers understand that organizations often have stronger security measures in place to protect their own systems, making it more difficult to gain access directly. Targeting a supplier with weaker defenses allows attackers to gain a foothold and then move laterally into the networks of their customers. This 'cascade' effect amplifies the damage and makes containment far more challenging.
This isn’t solely a problem for large enterprises. Small and medium-sized businesses (SMBs) are increasingly targeted because they often lack the resources and expertise to adequately assess and manage the risks associated with their supply chains. Nation-state actors and ransomware groups now exploit these vulnerabilities for espionage and profit. Because businesses are so tightly linked, one compromise hits everyone. Most security teams I talk to now treat a breach as an inevitability rather than a possibility.
The motivation is simple: access. A successful supply chain attack can grant access to numerous targets through a single point of compromise. This efficiency makes it an attractive strategy for attackers, especially those with limited resources but a high degree of sophistication. We're seeing more sophisticated techniques, including the injection of malicious code during the software development lifecycle and the exploitation of zero-day vulnerabilities in widely used software.
NIST and CISA guidance
The National Institute of Standards and Technology (NIST) and the Cybersecurity and Infrastructure Security Agency (CISA) have published critical guidance to help organizations strengthen their supply chain security. NIST’s guidance, developed under Executive Order 14028, focuses on improving the security of software supply chains and provides a comprehensive framework for secure software development practices. CISA's Secure Software Supply Chain guide, along with its accompanying fact sheet, offers practical recommendations for customers.
A cornerstone of both frameworks is the Software Bill of Materials (SBOM). An SBOM is essentially a nested inventory of the software components that make up a particular application. It lists all the open-source and third-party components, along with their versions and dependencies. This inventory lets you identify vulnerabilities the moment they are disclosed. You can use tools like Dependency-Track to automate the generation of these lists so they don't become a manual burden.
Attestation to secure software development practices is another key recommendation. This involves vendors demonstrating that they follow established security standards throughout the software development lifecycle. It’s not enough to simply claim compliance; organizations need to verify that vendors are actually implementing the necessary controls. However, compliance shouldn't be viewed as a destination. It’s about continuously improving security posture and building a more resilient system. It’s about proactively identifying and mitigating risks, not just reacting to incidents.
- SBOM Generation: Tools like Dependency-Track and CycloneDX can automate SBOM creation.
- Vendor Attestation: Request documentation demonstrating adherence to security standards (e.g., NIST SP 800-53).
- Continuous Monitoring: Regularly review vendor security posture and update risk assessments.
Moving beyond vendor questionnaires
Traditional vendor questionnaires are often inadequate for assessing supply chain risk. They rely on self-reported information, which can be inaccurate or incomplete. Moreover, they provide only a snapshot in time and don’t capture the dynamic nature of an organization’s security posture. We need to move beyond these static assessments and embrace continuous monitoring.
Prioritizing vendors based on risk is essential. Not all vendors pose the same level of threat. Criticality of service, data access, and the vendor’s own security practices should all be considered. Vendors who have access to sensitive data or provide essential services should be subject to more rigorous scrutiny. Security ratings, provided by companies like SecurityScorecard and BitSight, offer a valuable way to assess a vendor’s overall security posture.
Threat intelligence feeds can provide insights into a vendor’s potential vulnerabilities and exposure to attacks. On-site audits, while more resource-intensive, can provide a deeper understanding of a vendor’s security controls. While dedicated vendor risk management platforms exist, organizations can also leverage a combination of open-source tools and manual assessments. The key is to establish a process for regularly evaluating and mitigating vendor risk.
Software composition analysis
Software Composition Analysis (SCA) is a critical component of supply chain security. It involves identifying all the open-source and third-party components used in an application and assessing them for known vulnerabilities and license compliance issues. Many applications rely heavily on open-source code, which can introduce significant risks if not properly managed.
SCA tools work by scanning an application’s codebase and identifying its dependencies. They then compare these dependencies against databases of known vulnerabilities, such as the National Vulnerability Database (NVD). When a vulnerability is detected, the SCA tool will flag it and provide information on how to remediate it. Tools like Snyk and Sonatype Nexus Lifecycle are popular choices for SCA.
SCA fails if you treat it as a one-time check. I've seen teams run a scan at launch and then ignore it for a year, leaving them exposed to every vulnerability found since. You need automated patching and weekly scans to keep up with the National Vulnerability Database.
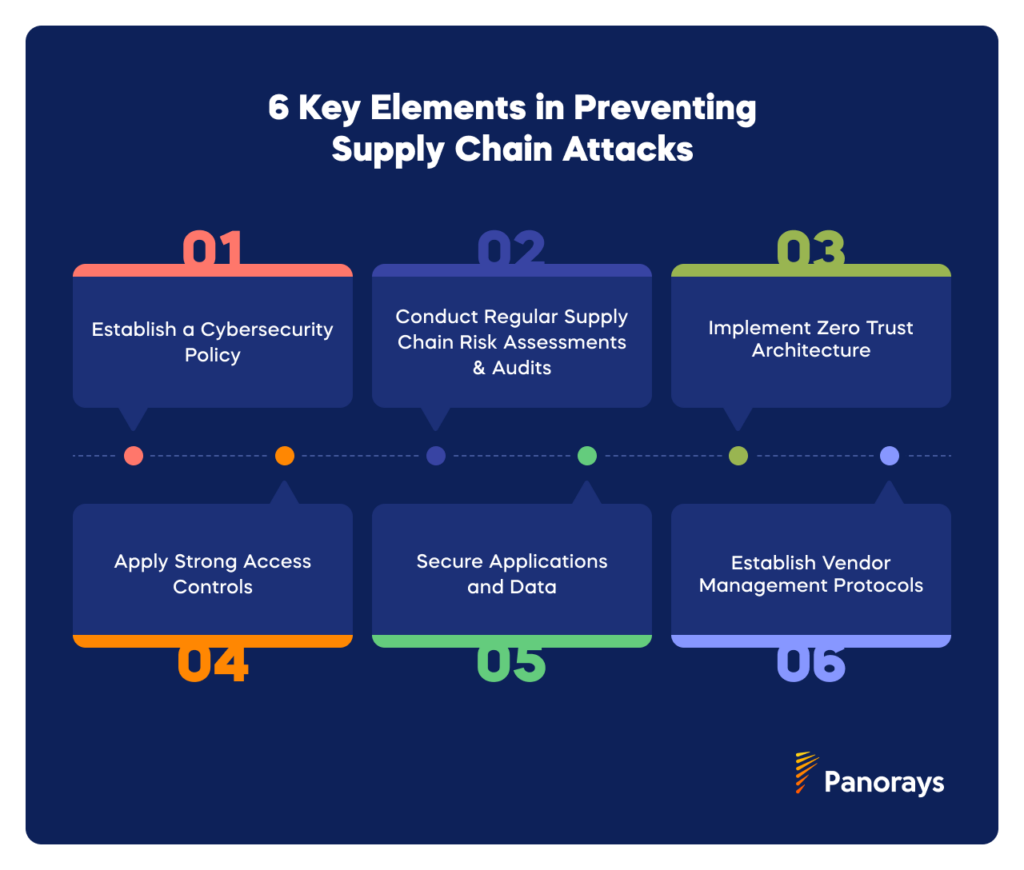
Planning for the supply chain angle
Traditional incident response plans often focus on internal threats and may not adequately address supply chain attacks. When an incident originates with a third-party vendor, the response process becomes far more complex. Clear communication protocols are essential for quickly notifying and coordinating with affected vendors. Establishing a dedicated point of contact at each organization can streamline this process.
Forensic investigation can be particularly challenging when the attack originates with a third party. Access to logs and other evidence may be limited, making it difficult to determine the root cause of the incident. It’s important to have a clear understanding of the vendor’s incident response capabilities and their willingness to cooperate with investigations. Tabletop exercises that simulate supply chain compromises can help organizations prepare for these scenarios.
Legal considerations and potential liability are also important factors to consider. Organizations may be held liable for damages resulting from a supply chain attack, even if they were not directly responsible for the compromise. Contracts should clearly define security expectations and consequences for non-compliance. Consulting with legal counsel is crucial for understanding your organization’s legal obligations.
Contractual safeguards
Vendor contracts play a critical role in managing supply chain risk. Organizations should incorporate specific security requirements into their contracts, including clauses related to data protection, incident reporting, audit rights, and liability. Clearly defining security expectations and consequences for non-compliance can help shift the burden of security to the vendor.
Contracts should require vendors to maintain adequate security controls and to promptly notify the organization of any security incidents. Audit rights allow organizations to verify that vendors are actually complying with the agreed-upon security requirements. Liability clauses should clearly define the financial and legal consequences of a security breach. It’s important to consult with legal counsel to ensure that your contracts are enforceable and adequately protect your organization.
Cybersecurity insurance can also provide a valuable layer of protection. However, it’s important to understand the terms and conditions of your policy and to ensure that it covers supply chain attacks. Insurance can help offset the costs of incident response, data recovery, and legal fees. A well-crafted contract, coupled with appropriate insurance coverage, can significantly reduce your organization’s exposure to supply chain risk.
New threats on the horizon
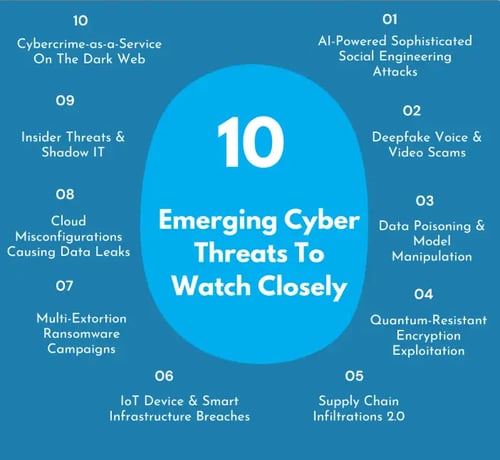
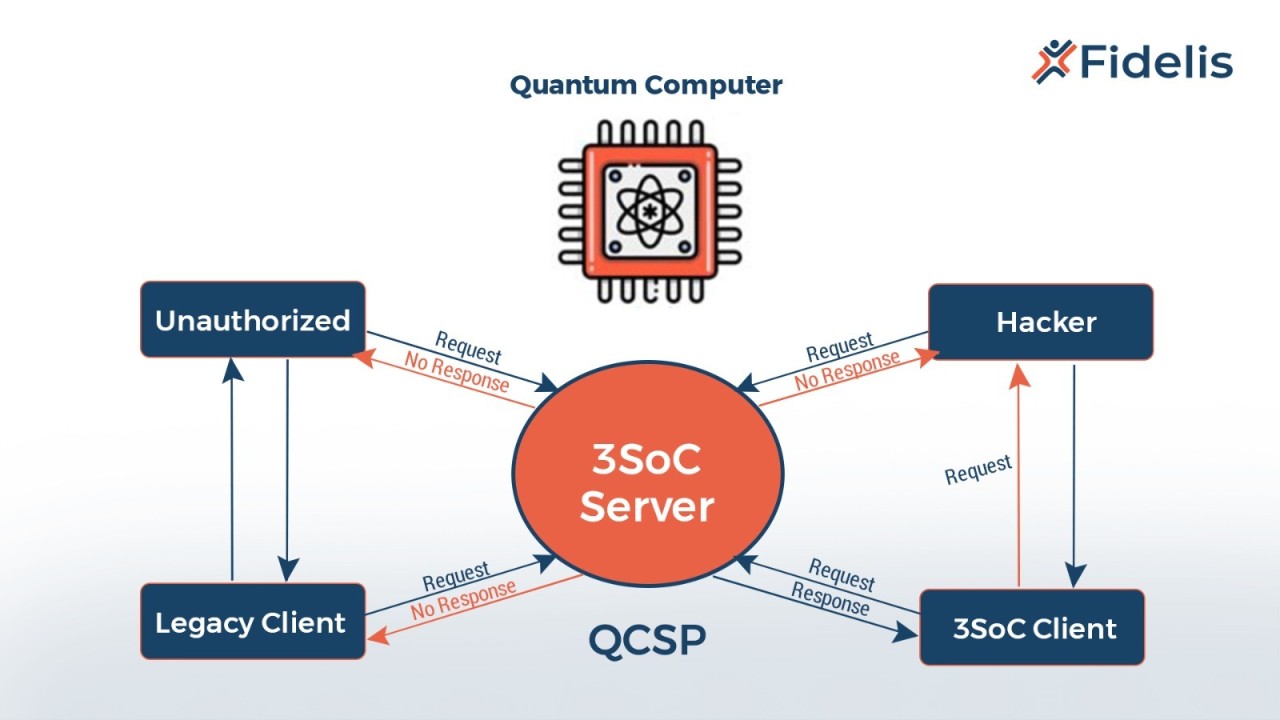
The supply chain threat landscape is constantly evolving. Emerging threats like AI-powered attacks, which can automate the discovery and exploitation of vulnerabilities, are becoming increasingly sophisticated. The security of cloud-based supply chains is also a growing concern, as organizations increasingly rely on third-party cloud providers.
Technologies like blockchain offer the potential to improve supply chain transparency and security. By creating an immutable record of transactions, blockchain can help verify the authenticity of software and prevent tampering. However, blockchain is not a silver bullet and requires careful implementation to be effective.
Ultimately, supply chain security is an ongoing process, not a one-time fix. There’s no single technology or solution that can eliminate all risks. Continuous monitoring, proactive risk management, and information sharing within the industry are essential for staying ahead of the evolving threat landscape. Collaboration and a commitment to security are vital to protect against these increasingly complex attacks.
- AI-Powered Attacks: Automated vulnerability discovery and exploitation.
- Cloud Supply Chain Security: Securing data and applications in cloud environments.
- Blockchain for transparency: Using immutable ledgers to verify software authenticity.
Key Contractual Clauses for Supply Chain Security
| Clause | Description | Purpose | Key Considerations |
|---|---|---|---|
| Data Security | Specifies requirements for protecting sensitive data shared with or accessed by the vendor. | Ensures appropriate safeguards are in place to prevent data breaches and maintain confidentiality, integrity, and availability. | Address data encryption, access controls, data residency, and data disposal practices. Align with relevant data privacy regulations. |
| Incident Reporting | Outlines the vendor’s obligations to report cybersecurity incidents affecting the organization or its data. | Facilitates rapid response and mitigation of security breaches, minimizing potential damage. | Define reporting timelines, required information (e.g., nature of the incident, systems affected, containment measures), and communication channels. |
| Audit Rights | Grants the organization the right to audit the vendor’s security practices and compliance with contractual obligations. | Provides assurance that the vendor is adhering to agreed-upon security standards and identifying potential vulnerabilities. | Specify the scope of audits (e.g., on-site reviews, documentation requests), frequency, and any limitations. Consider independent third-party audits. |
| Liability | Defines the allocation of liability in the event of a security breach or other security-related incident. | Clarifies financial and legal responsibilities, protecting the organization from undue risk. | Address issues like data breach notification costs, remediation expenses, and potential legal claims. Consider insurance requirements. |
| Compliance Standards | Requires the vendor to adhere to specific security frameworks, standards, or regulations (e.g., NIST Cybersecurity Framework, ISO 27001, CISA guidance). | Establishes a baseline level of security and demonstrates a commitment to industry best practices. | Clearly identify the applicable standards and the vendor’s obligations to maintain compliance. Include provisions for regular assessments and updates. |
| Termination Rights | Grants the organization the right to terminate the contract if the vendor experiences a significant security breach or fails to meet security requirements. | Provides a mechanism to disengage from a vendor that poses an unacceptable security risk. | Define specific termination triggers, notice periods, and any associated penalties or wind-down procedures. |
Illustrative comparison based on the article research brief. Verify current pricing, limits, and product details in the official docs before relying on it.



No comments yet. Be the first to share your thoughts!