The reality of the quantum threat
For decades, network security has relied on the mathematical difficulty of certain problems. Specifically, things like factoring large numbers and computing discrete logarithms. These underpin the most common encryption algorithms – RSA and Elliptic Curve Cryptography (ECC). But a new threat is emerging that renders these methods vulnerable: quantum computing.
Quantum computers, leveraging the principles of quantum mechanics, approach problems differently than classical computers. Shor’s algorithm, developed by Peter Shor in 1994, demonstrates that a sufficiently powerful quantum computer could break RSA and ECC efficiently. This isn’t a theoretical concern anymore; progress in quantum computing is accelerating, and the potential for decryption of stored data is real.
The timeline for when quantum computers will be capable of breaking current encryption is uncertain, but 2026 is emerging as a critical year for preparation. This isn’t because quantum computers will suddenly be able to break everything then, but because data encrypted today could be stored and decrypted in the future. Organizations need to begin transitioning to quantum-resistant algorithms now to protect long-lived data. It’s about proactive defense, not reacting to a crisis.
The implications for network security are significant. Think about secure websites (HTTPS), Virtual Private Networks (VPNs), and secure shell access (SSH). All rely on these vulnerable algorithms. Protecting sensitive data – financial records, intellectual property, personal information – demands a shift towards post-quantum cryptography (PQC).
Finding vulnerabilities in your network
Before you can implement PQC, you need to understand where your network currently relies on vulnerable cryptographic systems. This requires a comprehensive inventory of your cryptographic assets. Start by identifying all instances of TLS/SSL, which secures web traffic and many other network services.
VPNs are another critical area. Determine which VPN protocols are in use (e.g., OpenVPN, IPSec) and the cryptographic algorithms they employ. SSH, used for secure remote access, also relies on vulnerable algorithms. Make sure to document the ciphers and key exchange methods configured on your SSH servers.
Don’t forget about data-at-rest encryption. What algorithms are you using to protect sensitive data stored on servers, databases, and backups? Are you using full disk encryption? Identify the cryptographic libraries and tools used for data protection. This is often overlooked but is a significant vulnerability.
Tools like network scanners (Nmap) and vulnerability assessment tools can help automate some of this process, but manual review is often necessary. Understanding dependencies is crucial. A seemingly innocuous application might rely on a vulnerable cryptographic library indirectly. A good starting point is to document all cryptographic configurations and create a clear map of your network’s cryptographic posture.
NIST Post-Quantum Cryptography Standardized Algorithms - Comparison
| Algorithm Name | Category | Security Level | Key Size (approximate) | Performance Characteristics (relative) |
|---|---|---|---|---|
| CRYSTALS-Kyber | Key-Establishment | NIST Level 1-5 | 768 - 3072 bits | Fast |
| CRYSTALS-Dilithium | Signature | NIST Level 1-5 | 2560 - 13440 bits | Medium |
| Falcon | Signature | NIST Level 1-5 | 1920 - 6656 bits | Fast |
| SPHINCS+ | Signature | NIST Level 1-5 | 256 - 1280 bytes (public key) | Slow |
Illustrative comparison based on the article research brief. Verify current pricing, limits, and product details in the official docs before relying on it.
A phased migration strategy
A complete, immediate replacement of all existing cryptographic systems with PQC algorithms isn't feasible – or even advisable. A phased approach is the most practical and least disruptive strategy. The first step is to achieve "crypto-agility" – designing your systems so you can easily swap cryptographic algorithms without major code changes. This means abstracting cryptographic operations behind well-defined interfaces.
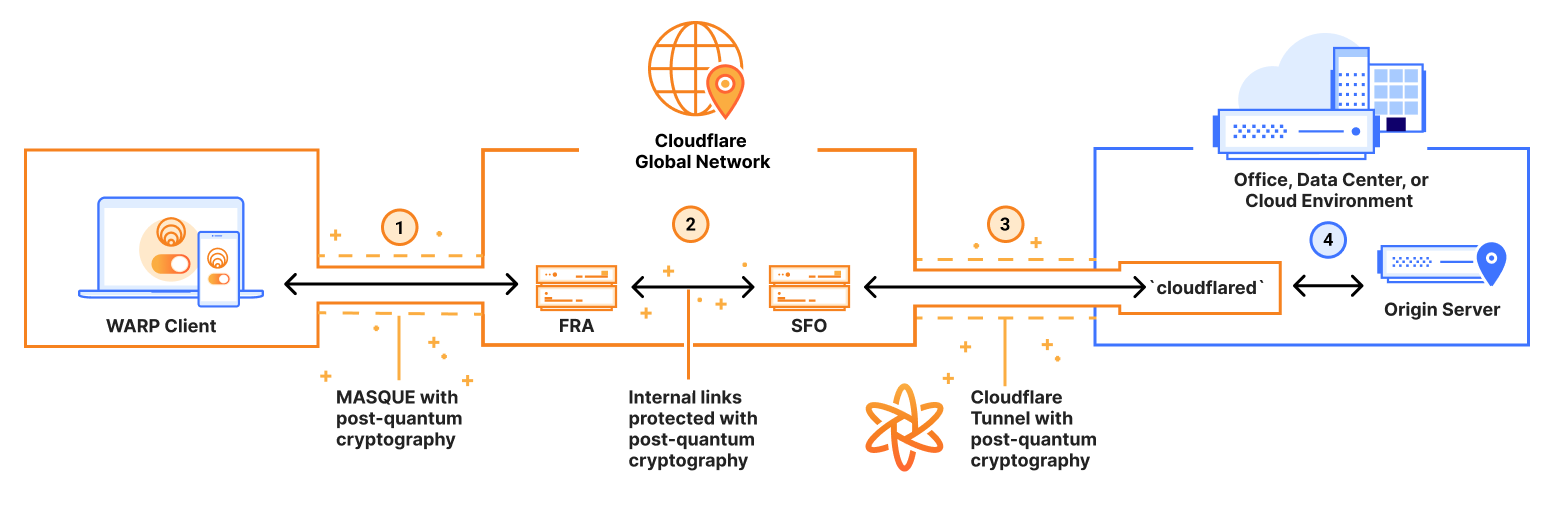
Hybrid deployments are a key component of this phased approach. This involves running both classical and post-quantum algorithms in parallel. For example, a TLS connection could negotiate both an ECDHE key exchange (classical) and a CRYSTALS-Kyber key exchange (PQC). This provides backward compatibility and allows you to gradually increase the reliance on PQC.
Key management and certificate authorities (CAs) present significant challenges. Existing key management infrastructure may not support the larger key sizes associated with PQC algorithms. CAs will need to issue certificates signed with PQC algorithms, and browsers and other clients will need to be updated to trust these certificates. This is a complex undertaking that requires coordination across the ecosystem.
Thorough testing is paramount. Before deploying PQC in production, you need to test its performance, compatibility, and security. This includes interoperability testing with different vendors and platforms. Monitor performance metrics closely to identify any bottlenecks or issues. Expect to iterate and refine your deployment strategy based on testing results. Don't underestimate the time and effort required for proper testing.
Integrating PQC with current systems
Integrating PQC algorithms into existing systems requires careful planning and execution. For TLS/SSL, OpenSSL 3.0 and later versions offer support for some PQC algorithms, including CRYSTALS-Kyber. However, enabling PQC in OpenSSL often requires recompilation and careful configuration. Other TLS libraries may have varying levels of PQC support.
VPN solutions like OpenVPN and WireGuard are also evolving to support PQC. OpenVPN, being more mature, may have more readily available PQC integrations, but this depends on the specific version and configuration. WireGuard, with its focus on simplicity and performance, is actively exploring PQC options, but support is still developing.
SSH integration is similar to TLS/SSL. OpenSSH, a widely used SSH server and client, is adding support for PQC algorithms. Again, this typically requires recompilation and configuration. If direct integration isn’t possible, consider using cryptographic modules or Hardware Security Modules (HSMs) that support PQC algorithms. These can offload cryptographic operations from your main servers.
It's important to note that not all systems will be easily upgradeable. Legacy systems may not have the resources or capabilities to support PQC algorithms. In these cases, consider isolating these systems or replacing them with more modern alternatives. A layered security approach, combining PQC with other security measures, can provide additional protection.
Performance costs and trade-offs
Post-quantum cryptography doesn’t come without a cost. PQC algorithms generally have larger key and signature sizes compared to classical cryptography. This impacts bandwidth, latency, and storage requirements. Larger keys mean more data needs to be transmitted during key exchange, increasing latency. Larger signatures increase the size of digitally signed data.
The performance impact varies depending on the specific algorithm and implementation. Lattice-based algorithms, like CRYSTALS-Kyber and CRYSTALS-Dilithium, tend to have higher computational costs than ECC. Hash-based signatures, like SPHINCS+, can be particularly slow for signing operations. These performance differences need to be carefully considered when choosing algorithms for specific applications.
Hardware acceleration can help mitigate some of the performance overhead. Dedicated cryptographic accelerators can significantly speed up PQC operations. However, these accelerators are not yet widely available and can add to the cost of deployment. Software optimizations can also help, but there are limits to how much performance can be gained through software alone.
Some trade-offs are unavoidable. You may need to accept higher latency or increased storage costs to achieve quantum-resistant security. The key is to carefully evaluate the trade-offs and choose algorithms that provide the best balance of security and performance for your specific needs. Don’t expect a "drop-in" replacement that matches the performance of existing algorithms.
Monitoring and updates
Post-quantum cryptography is a rapidly evolving field. New research, vulnerabilities, and algorithm updates are constantly emerging. Staying informed is crucial to maintaining a strong security posture. The NIST website (csrc.nist.gov) is the primary source for updates on the PQC standardization process and algorithm evaluations.
Academic publications and security blogs are also valuable sources of information. Follow leading cryptographers and security researchers to stay abreast of the latest developments. Participate in industry forums and conferences to share knowledge and best practices. Don't rely solely on vendor announcements; independent research is essential.
NIST’s current selections aren't permanent. Researchers will likely find new attacks or develop more efficient math. You should build your systems so you can swap these algorithms out when the standards inevitably change.
This isn’t a one-time project; it’s an ongoing process. Regularly review your cryptographic posture, assess your vulnerabilities, and update your systems to stay ahead of the quantum threat. Continuous monitoring and adaptation are the cornerstones of long-term quantum security.
Key & Signature Sizes: Classical vs. Post-Quantum Algorithms (in Bytes)
Data: AI-generated estimate for illustration
What is your organization's biggest challenge in preparing for post-quantum cryptography?
As quantum computing threats move closer to reality, organizations worldwide are racing to transition their cryptographic infrastructure. We want to hear from the HackerDesk community -- what is the most significant barrier your organization faces when it comes to adopting post-quantum cryptography solutions? Your input helps us tailor future content to address the challenges that matter most to cybersecurity professionals in 2026. Vote below!


No comments yet. Be the first to share your thoughts!