Zero trust: beyond the buzzword
For years, network security operated under a simple assumption: everything inside the network perimeter could be trusted. This "castle-and-moat" approach worked reasonably well when most employees and applications resided within the corporate firewall. But that era is over. The explosion of remote work, cloud adoption, and increasingly sophisticated cyberattacks has rendered that perimeter increasingly porous and unreliable.
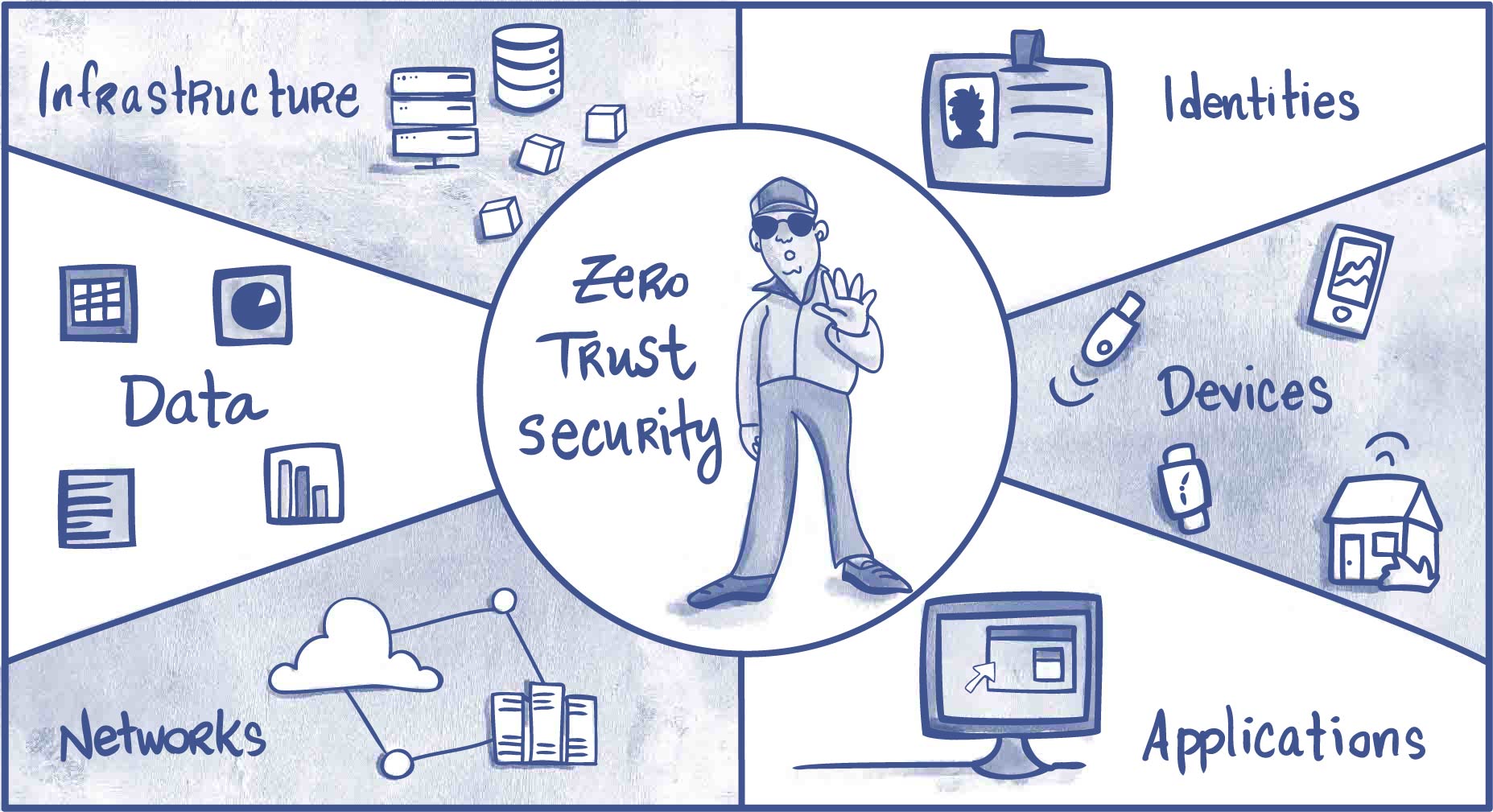
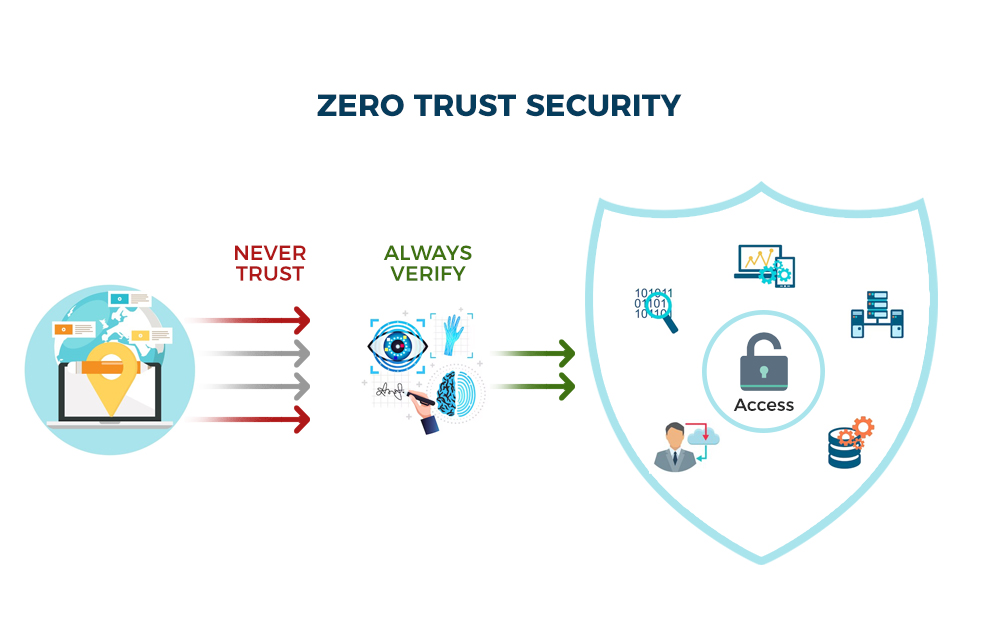
The fundamental principle of Zero Trust is simple: never trust, always verify. It rejects the idea of implicit trust based on network location. Instead, every user, device, and application—regardless of whether it’s inside or outside the traditional network boundary—must be authenticated, authorized, and continuously validated before being granted access to resources.
By 2026, this is a necessity. Distributed workforces and messy cloud environments need a security model that adapts. Old approaches are too slow for modern threats.
The NIST 800-207 blueprint
The National Institute of Standards and Technology (NIST) Special Publication 800-207 provides a comprehensive framework for understanding and implementing Zero Trust Architecture (ZTA). It doesn’t prescribe a specific product or solution, but rather outlines the core principles and components necessary for a successful ZTA implementation.
NIST identifies seven key pillars of Zero Trust: Data Security, Application Security, Infrastructure Security, Command and Control, Visibility and Analytics, Automation, and Services. These pillars aren’t isolated elements, but rather interconnected components that work together to create a robust security posture. A weakness in one area can compromise the entire system.
The Policy Engine and Policy Administrator are the core of the NIST framework. The Engine evaluates access requests while the Administrator enforces them. They adjust access based on risk. Zero trust is a different architecture, not a single tool you install.
- Data security covers data in use, transit, and at rest.
- Application Security: Ensuring applications are secure and resilient to attack.
- Infrastructure Security: Securing the underlying infrastructure that supports applications and data.
- Command and Control: Maintaining control over the network and its resources.
- Visibility and Analytics: Gaining insights into network activity and identifying potential threats.
- Automation: Automating security tasks to improve efficiency and reduce errors.
- Services: Providing security services to users and applications.
Phased implementation at the DoD
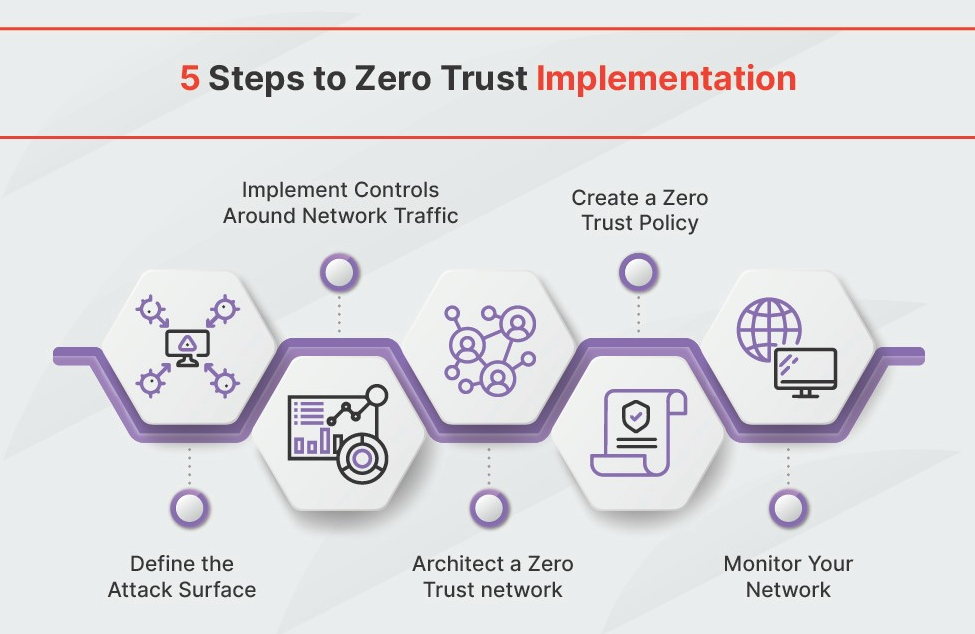
The Department of Defense (DoD) is actively pursuing a Zero Trust implementation, guided by its own phased approach outlined in the Zero Trust Implementation Guideline Phase One. This guideline provides a practical roadmap for organizations looking to adopt ZTA, focusing initially on four key areas: identity, devices, applications, and data.
A central tenet of the DoD’s approach is microsegmentation. By dividing the network into smaller, isolated segments, the blast radius of a potential breach is significantly reduced. This aligns directly with the NIST framework's emphasis on infrastructure security and limiting lateral movement. This approach assumes compromise and limits the attacker’s ability to move freely within the network.
The guideline emphasizes the importance of continuous monitoring and assessment. Organizations are encouraged to regularly evaluate their Zero Trust posture and make adjustments as needed. It's a process of constant refinement, not a one-time implementation. The DoD’s commitment demonstrates the seriousness with which Zero Trust is being taken at the highest levels of government.
Identity is the new perimeter
In a Zero Trust architecture, identity becomes the new perimeter. Traditional perimeter-based security relied on network location as a primary factor for trust. With Zero Trust, trust is established based on the identity of the user or device seeking access. This requires robust Identity and Access Management (IAM) solutions.
Multi-Factor Authentication (MFA) is a foundational element of any Zero Trust strategy. Requiring users to verify their identity through multiple factors – something they know, something they have, and something they are – significantly reduces the risk of unauthorized access. Privileged Access Management (PAM) is equally important, controlling and monitoring access to sensitive systems and data.
The industry is moving towards passwordless authentication methods, such as biometrics and hardware security keys. These methods are more secure and user-friendly than traditional passwords. Continuous authentication and behavioral analytics add another layer of security, constantly monitoring user behavior for anomalies. Managing identities across hybrid environments—on-premises and in the cloud—presents a significant challenge, requiring integrated IAM solutions.
- Use MFA for every user.
- Deploy Privileged Access Management (PAM) to control access to sensitive resources.
- Explore passwordless authentication options.
- Utilize continuous authentication and behavioral analytics.
- Integrate IAM solutions across hybrid environments.
Microsegmentation and containment
Microsegmentation is a network security technique that divides a network into granular segments. Unlike traditional network segmentation, which often creates broad zones, microsegmentation creates highly specific, policy-driven segments. This limits the lateral movement of attackers within the network, containing breaches and minimizing damage.
The benefit of microsegmentation is clear: if an attacker gains access to one segment, they are unable to easily move to other parts of the network. This significantly reduces the blast radius of a security incident. However, implementing microsegmentation in complex enterprise networks can be challenging, requiring careful planning and execution.
Technologies like software-defined networking (SDN) and network virtualization facilitate microsegmentation by providing the flexibility and control needed to create and manage granular network segments. Organizations should carefully assess their network architecture and identify critical assets to prioritize for microsegmentation. It's an ongoing process of refinement and adaptation.
Protecting the data
Zero Trust places a strong emphasis on data-centric security. Protecting data is the ultimate goal, and all other security measures should be aligned with that objective. This involves implementing data classification, data loss prevention (DLP), and encryption technologies.
Data classification helps organizations identify and categorize sensitive data, allowing them to apply appropriate security controls. DLP solutions prevent sensitive data from leaving the organization's control, whether through accidental leaks or malicious exfiltration. Encryption protects data both in transit and at rest, rendering it unreadable to unauthorized users.
Implementing robust data access controls and adhering to the principle of least privilege are crucial. Users should only have access to the data they need to perform their jobs. Securing data in the cloud and in transit requires careful consideration, utilizing encryption and secure communication protocols. Data security isn’t just about technology; it’s about people and processes as well.
- Implement data classification to identify sensitive data.
- Deploy data loss prevention (DLP) solutions.
- Encrypt data in transit and at rest.
- Enforce least privilege access controls.
Data Encryption Method Comparison for Zero Trust Environments
| Encryption Method | Best For | Trade-off | Considerations |
|---|---|---|---|
| AES-256 | Bulk data encryption and high-speed applications | Can be vulnerable to side-channel attacks if not implemented carefully | Widely supported in hardware and software, making it a practical choice for many scenarios. |
| RSA-2048 | Digital signatures and key exchange | Slower performance compared to symmetric encryption algorithms | Well-established and broadly trusted, suitable for securing communication channels. |
| ECC (Elliptic Curve Cryptography) | Resource-constrained environments and mobile devices | Requires careful key management to prevent compromise | Offers strong security with smaller key sizes, reducing computational overhead. |
| ChaCha20-Poly1305 | Applications requiring strong confidentiality and integrity | Less widely implemented in hardware acceleration than AES | A modern stream cipher offering good performance and security, often preferred over RC4. |
| Twofish | Situations demanding a highly secure, royalty-free alternative | May have slightly lower performance than AES on some platforms | Designed as a potential replacement for DES, offering a robust and flexible encryption scheme. |
| Blowfish | Legacy systems or applications needing a readily available option | Smaller block size may require more complex chaining modes | A fast and versatile block cipher, though its key length is considered relatively short by modern standards. |
Qualitative comparison based on the article research brief. Confirm current product details in the official docs before making implementation choices.
Zero trust tools
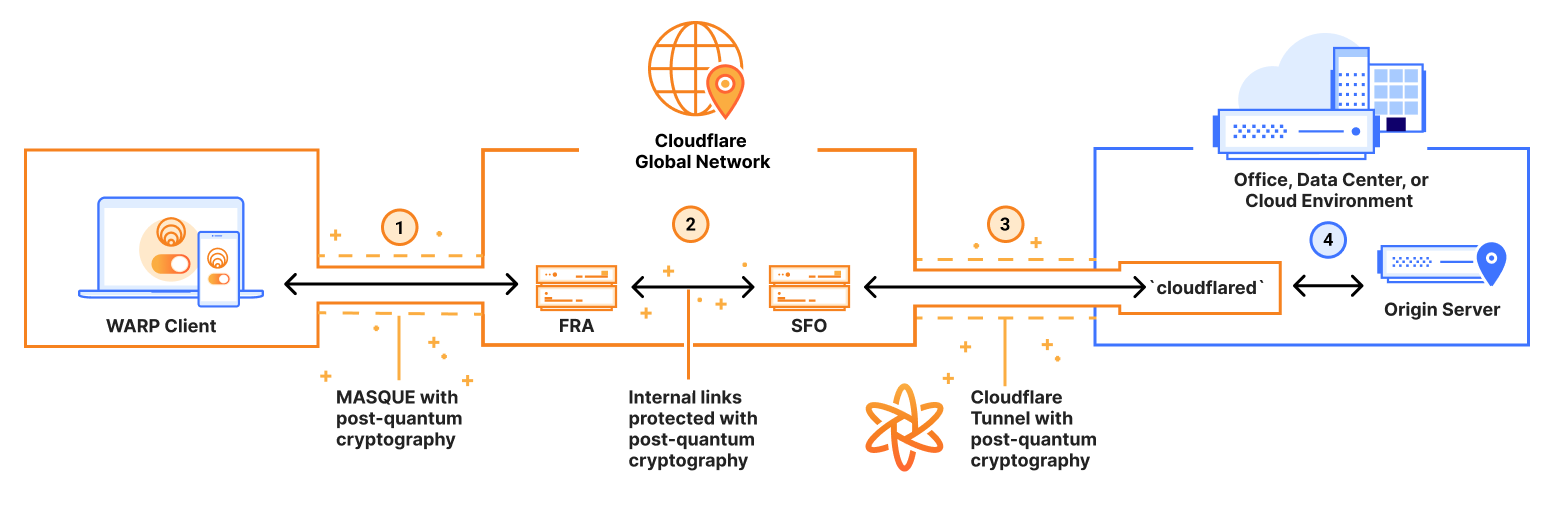
Implementing Zero Trust requires a suite of technologies working together. Secure Access Service Edge (SASE) combines network security functions – such as firewall-as-a-service, secure web gateway, and zero trust network access – into a single, cloud-delivered service. Network Detection and Response (NDR) solutions continuously monitor network traffic for malicious activity.
Security Information and Event Management (SIEM) systems collect and analyze security logs from various sources, providing a centralized view of security events. Extended Detection and Response (XDR) takes SIEM a step further, correlating data across multiple security layers to provide more comprehensive threat detection and response. These aren't standalone solutions, but rather components of a broader Zero Trust architecture.
Amazon Web Services (AWS) offers a range of services that support Zero Trust implementation. AWS Identity and Access Management (IAM) provides granular control over access to AWS resources. AWS Security Hub offers a centralized view of security alerts and compliance status. AWS Network Firewall provides network security as a service. AWS CloudTrail logs API calls made to AWS services, providing valuable audit trails.
- SASE combines firewalls and web gateways into one cloud service.
- Network Detection and Response (NDR)
- Security Information and Event Management (SIEM)
- Extended Detection and Response (XDR)
Essential AWS Services for Implementing a Robust Zero Trust Architecture

Practical solutions for securing AWS cloud infrastructure · Covers essential AWS security services · Provides best practices for cloud security
This book offers practical guidance and best practices for securing AWS cloud infrastructure, providing foundational knowledge for implementing Zero Trust principles.

Tutorial on AWS Security Hub · Covers AWS security, identity, and compliance services · Free resource
This tutorial provides a free, in-depth look at AWS Security Hub, a crucial service for centralizing security alerts and compliance checks, essential for a Zero Trust model.

Secures AWS, Azure, and GCP · Covers VPCs, security groups, and WAF · Explains Zero Trust network architecture in multi-cloud
This guide addresses the complexities of securing multi-cloud environments, including AWS, Azure, and GCP, by detailing network security controls and Zero Trust architecture implementation.

Comprehensive guide to Amazon GuardDuty · Details threat detection capabilities · Explains how to leverage GuardDuty for security
Amazon GuardDuty is a key service for intelligent threat detection, and this complete guide explains how to effectively utilize its capabilities to enhance your Zero Trust security posture.
As an Amazon Associate I earn from qualifying purchases. Prices may vary.


No comments yet. Be the first to share your thoughts!