Moving beyond the perimeter
For decades, network security operated on a simple assumption: everything inside the network was trustworthy. We built walls – firewalls, intrusion detection systems – to keep the bad guys out. But that model is crumbling. The rise of remote work, the explosion of cloud services, and increasingly sophisticated attackers have rendered the traditional perimeter largely meaningless.
The problem isn't just that the perimeter has expanded; it's that the concept of a defined perimeter is becoming obsolete. Data now lives everywhere – in data centers, in the cloud, on employee devices. Attackers don’t need to "break in" anymore; they often just exploit a compromised user or device already inside the network.
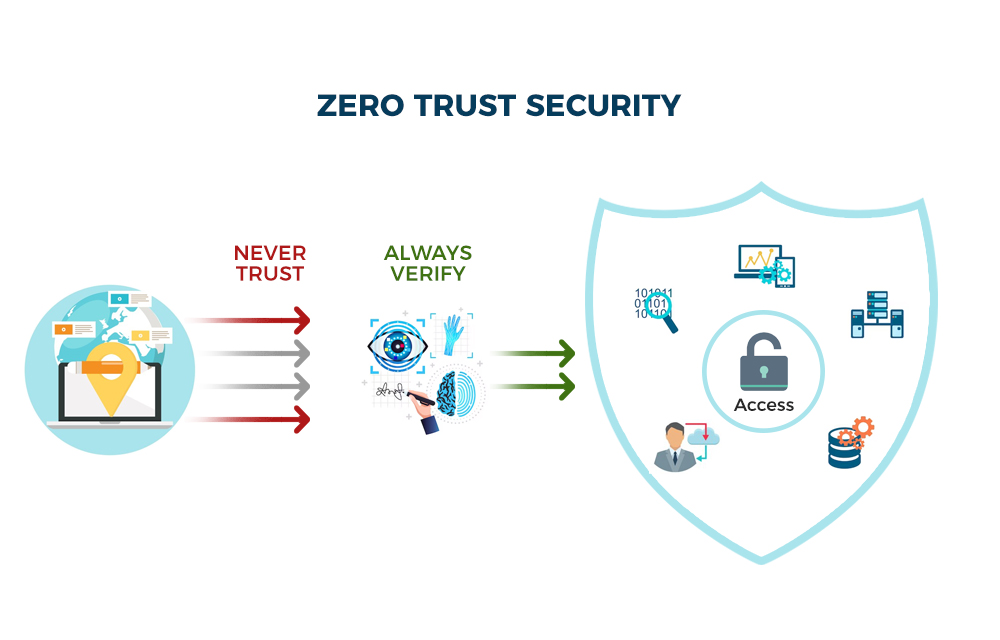
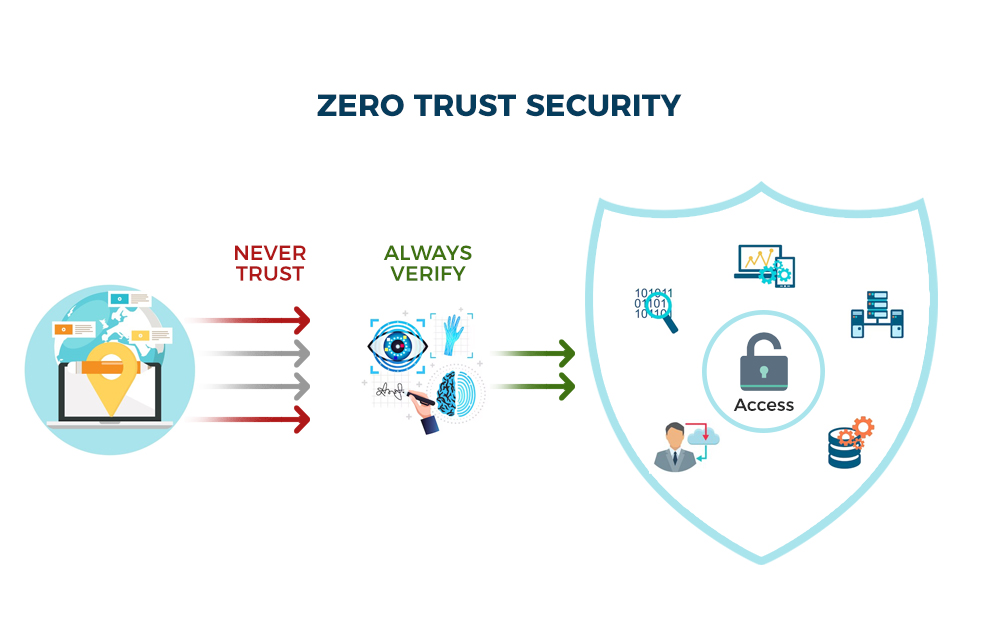
Zero Trust is a fundamental shift in thinking. It operates on the principle of "never trust, always verify." Every user, every device, every application – regardless of location – must be authenticated and authorized before being granted access to resources. It's not a product you buy off the shelf, but a strategic approach to building a more resilient security posture. It assumes breach, meaning it's designed to minimize the damage when – not if – an attacker gets inside.
How the DoD handles zero trust
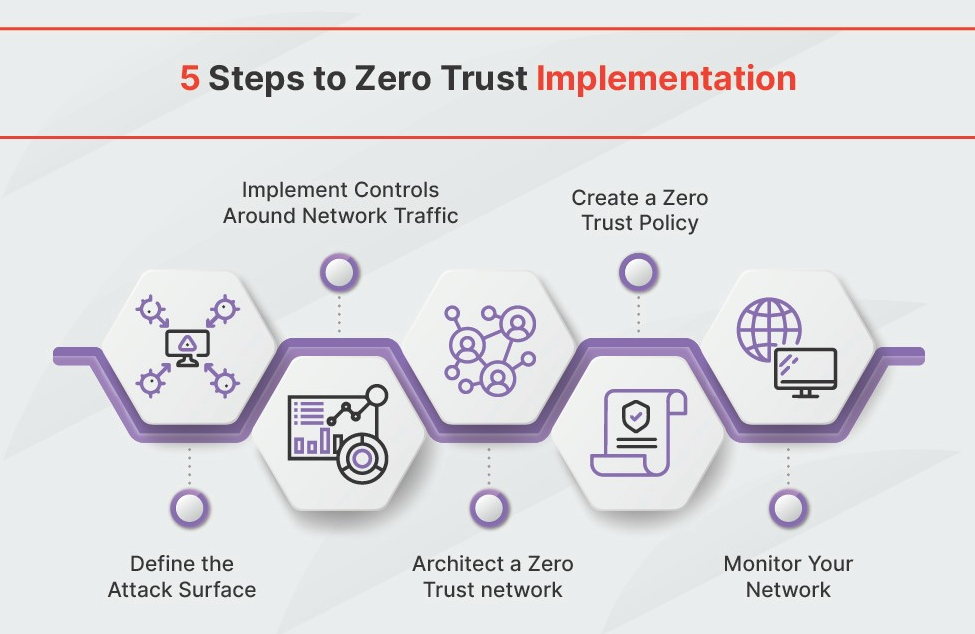
The Department of Defense (DoD) is moving toward zero trust because of a mandate to speed up security adoption. Their Phase One implementation guideline outlines how they plan to handle their infrastructure.
Their primary goals are to improve cybersecurity posture, reduce attack surface, and enhance data protection. The DoD recognizes that traditional perimeter-based security is insufficient to protect against modern threats. They're specifically focused on securing access to data and applications, regardless of location. This is a particularly challenging task given the DoD’s reliance on legacy systems and diverse environments.
The DoD’s approach differs from many enterprises in its scale and complexity. They’re dealing with millions of users, countless devices, and a highly heterogeneous IT environment. Their phased implementation focuses on identifying critical data and applications, then gradually implementing Zero Trust controls around those assets. While most organizations can take a more agile approach, the DoD’s experience demonstrates that even the largest organizations can benefit from, and are actively pursuing, Zero Trust.
Microsegmentation as a foundation
Microsegmentation is arguably the most important technical component of a Zero Trust architecture. It’s the practice of dividing a network into small, isolated segments, each with its own security policies. Think of it as building internal firewalls within your network.
Why is it so important? Because it limits the blast radius of a breach. If an attacker compromises one segment of the network, they can’t easily move laterally to other segments. This prevents a small breach from escalating into a catastrophic one. It's a core principle of containing threats.
There are several approaches to microsegmentation. Software-defined networking (SDN) allows you to dynamically create and manage network segments. Traditional firewalls can also be used, but managing a large number of firewall rules can become complex. Newer technologies, like workload-aware microsegmentation, automatically create security policies based on application dependencies.
Implementing microsegmentation in legacy environments can be challenging. It often requires significant changes to network infrastructure and application configurations. Organizations often start by microsegmenting their most critical assets and gradually expanding coverage over time. It's not about simply adding more firewalls; it's about creating granular security policies that are tailored to the specific needs of each segment.
Monitoring and analytics
Zero Trust isn't a "set it and forget it" approach. Continuous monitoring, threat detection, and security analytics are essential for maintaining a strong security posture. You need to constantly monitor your network for suspicious activity and respond to threats in real-time.
Tools like Security Information and Event Management (SIEM) systems collect and analyze security logs from various sources. User and Entity Behavior Analytics (UEBA) uses machine learning to detect anomalous behavior that may indicate a threat. These tools can help you identify and respond to attacks that would otherwise go unnoticed.
Automation plays a crucial role in this process. Automated threat response can help you quickly contain breaches and minimize damage. For example, you can automatically isolate a compromised device or block a malicious IP address. The goal is to reduce the time it takes to detect and respond to threats, minimizing the potential impact.
Security in a multi-cloud setup
Many organizations are now using multiple cloud providers – a strategy known as multi-cloud. This adds complexity to security because each cloud provider has its own security controls and policies. Zero Trust principles still apply, but you need to ensure consistent security across all cloud environments.
Cloud Access Security Brokers (CASBs) can help you enforce security policies across multiple cloud applications. They provide visibility into cloud usage and can detect and prevent unauthorized access. However, CASBs are just one piece of the puzzle. You also need to ensure that your identity and access management (IAM) systems are integrated with all of your cloud providers.
A unified policy engine is essential for effective Zero Trust in a multi-cloud setup. This allows you to define and enforce consistent security policies across all of your cloud environments, regardless of the underlying infrastructure. Without a unified approach, you risk creating security gaps and inconsistencies.
Where implementation usually fails
Implementing Zero Trust isn’t easy. Organizations often face a number of hurdles, including legacy systems, organizational silos, and skill gaps. Many organizations have invested heavily in traditional security technologies, and it can be difficult to justify the cost of replacing them.
Organizational silos can also hinder implementation. Security teams, IT teams, and business units often operate in isolation, making it difficult to coordinate efforts. A successful Zero Trust implementation requires collaboration across all departments. A lack of skilled personnel is another common challenge. Zero Trust requires expertise in areas like identity management, network security, and cloud security.
Start small and focus on high-risk areas. Don’t try to implement Zero Trust across your entire organization at once. Begin with a pilot project, such as securing access to your most critical data. This will allow you to learn from your mistakes and refine your approach before scaling up.
What to expect by 2026
Over the next few years, I expect to see continued adoption of Zero Trust, driven by the increasing frequency and sophistication of cyberattacks. CrowdStrike’s 2026 Global Threat Report indicates a growing reliance on AI-powered attacks, making proactive security measures like Zero Trust even more critical.
We’ll likely see increased use of AI and machine learning in Zero Trust security, automating threat detection and response. Identity-centric security will become even more important, with a focus on verifying user identity throughout the entire session. We can also expect to see greater convergence of Zero Trust with other security frameworks, such as Secure Access Service Edge (SASE), which combines network security functions with wide area network capabilities.
Zero trust is a practical step toward a resilient network. While the setup is difficult, the reduction in risk and better data protection are the primary reasons to start.


No comments yet. Be the first to share your thoughts!