The expanding attack surface
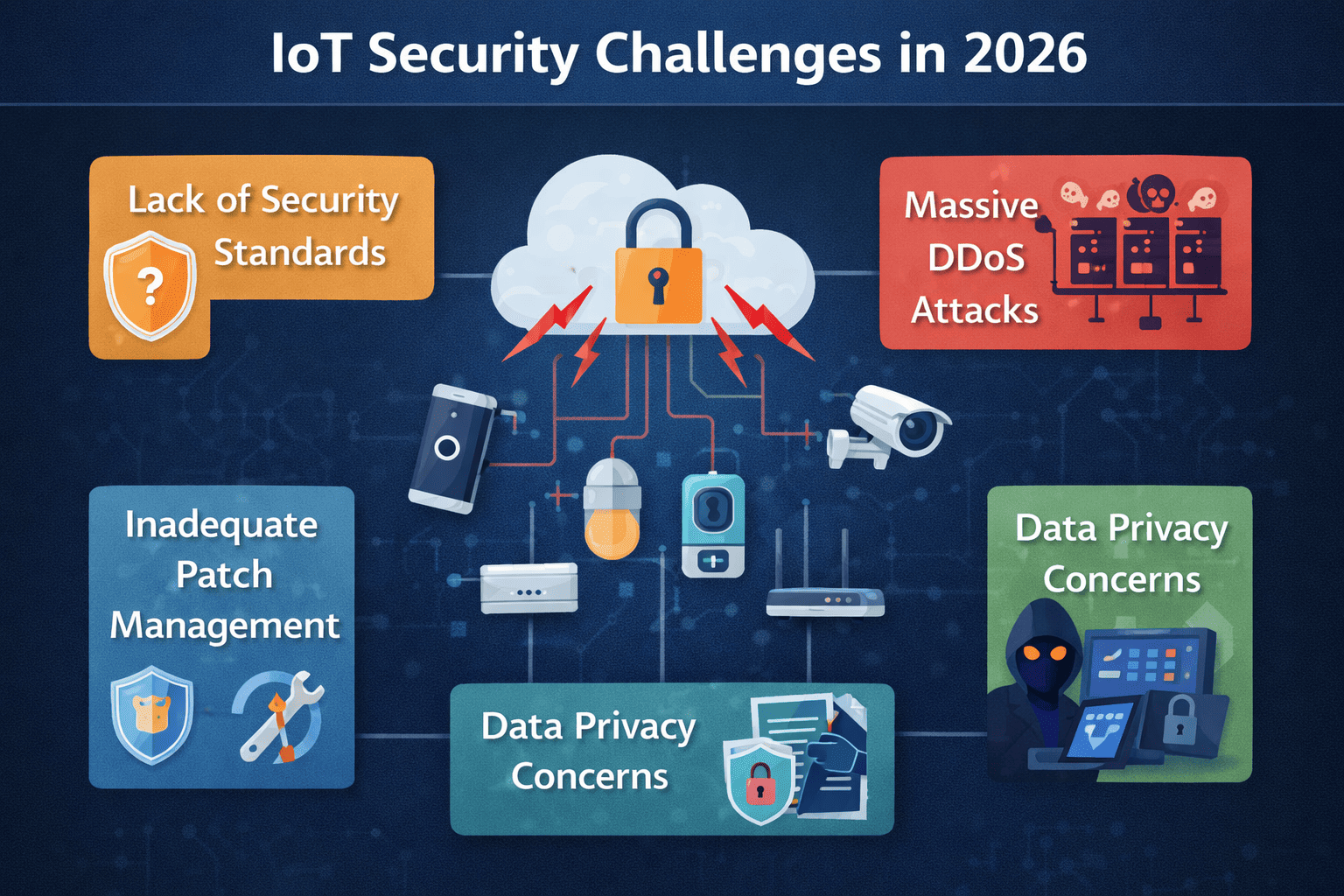
By 2026, the sheer number of connected devices will present a massive challenge to cybersecurity. Estimates suggest we’ll be managing over 55 billion IoT devices globally. This isn't just smart thermostats anymore; the biggest growth is in industrial sensors, connected vehicles, and increasingly sophisticated smart healthcare equipment. Each new device represents a potential entry point for attackers.
This expansion dramatically increases the attack surface. Industrial sensors, for example, often operate in environments with limited physical security, making them easy to tamper with. Connected vehicles, with their complex systems and reliance on wireless communication, are vulnerable to remote exploitation. And the sensitive data handled by smart healthcare devices makes them prime targets for data breaches.
Financial fallout is real. When an industrial controller goes down, production stops. If a vehicle is hijacked, people get hurt. Beyond the physical risk, healthcare breaches now carry regulatory fines that can bankrupt smaller providers.
Supply chain weaknesses
One of the most persistent and difficult-to-solve problems in IoT security is the vulnerability introduced through the supply chain. Many IoT device manufacturers lack standardized security practices, relying on cheaper components and prioritizing time-to-market over robust security measures. This often results in devices with inherent vulnerabilities that are difficult to detect and remediate.
The use of compromised components is a significant concern. Attackers can introduce malicious code or hardware backdoors during the manufacturing process, creating a hidden vulnerability that can be exploited later. Once a device is deployed, patching these vulnerabilities can be incredibly challenging, if not impossible. This is particularly true for devices with limited processing power or network connectivity.
Both NIST Special Publication 800-213 and CISA guidance emphasize the importance of secure acquisition. CISA specifically recommends a risk-based approach to IoT procurement, focusing on identifying and mitigating supply chain risks. However, the lack of transparency within many supply chains makes it difficult to assess the true security posture of a device. I believe this is the fundamental problem – we need greater visibility into how these devices are built.
Default Credentials and Poor Authentication
Despite years of warnings, a surprising number of IoT devices continue to ship with default or easily guessable credentials. This is a basic security failure that allows attackers to gain unauthorized access with minimal effort. The IoT For All website details numerous historical examples of breaches stemming directly from this simple oversight.
Weak authentication mechanisms, such as simple passwords or a complete lack of multi-factor authentication, exacerbate the problem. Even if a user changes the default password, a weak password can be easily cracked using brute-force attacks. The usability argument – that strong authentication is too inconvenient for consumers – is wearing thin, especially considering the potential consequences.
Mandatory password changes at setup help, but people still pick '123456'. We need to move toward hardware-level unique passwords or automated management where the user never actually sees the credential.
- Change default credentials immediately upon unboxing.
- Enable multi-factor authentication whenever possible.
- Use strong, unique passwords.
Insecure Firmware Updates
Firmware updates are essential for patching vulnerabilities and improving the security of IoT devices, but the update process itself can be a significant security risk. Man-in-the-middle attacks can intercept and modify firmware updates, injecting malicious code into the device. The lack of secure boot mechanisms means a device might execute compromised firmware without detection.
The potential for malicious firmware is a serious threat. An attacker could use a compromised firmware update to gain complete control of a device, steal data, or even use it as a bot in a larger attack. Over-the-air (OTA) update security is therefore paramount. Devices need to verify the authenticity and integrity of firmware updates before installing them.
Managing updates for a large fleet of devices can be challenging. Many devices lack automated update mechanisms, requiring manual intervention. This can lead to delays in patching critical vulnerabilities, leaving devices exposed to attack. A centralized update management system is crucial for ensuring that all devices are running the latest, most secure firmware.
Vulnerable Communication Protocols
Many common IoT communication protocols, such as MQTT, CoAP, and Zigbee, were not originally designed with security as a top priority. These protocols often lack built-in security features, making them vulnerable to eavesdropping, message tampering, and denial-of-service attacks. The inherent limitations of these protocols present ongoing challenges.
Eavesdropping attacks can allow attackers to intercept sensitive data transmitted over the network. Message tampering attacks can modify data in transit, potentially causing devices to malfunction or behave unexpectedly. Denial-of-service attacks can disrupt communication, rendering devices unusable. The consequences of these attacks can range from minor inconveniences to serious safety hazards.
Switching to DTLS for UDP or TLS for TCP traffic adds the encryption layer these devices lack by default. Most legacy IoT protocols were built for speed and low power, completely ignoring the need for a handshake that verifies who is talking to whom.
IoT Device Privacy and Security Assessment - 2026
| Device Type | Data Collected | Encryption Strength | Privacy Policy Clarity | Overall Privacy Score |
|---|---|---|---|---|
| Smart Thermostat | Temperature data, usage patterns, location (if geofencing enabled), potentially voice recordings (if voice control is present). | Variable - many utilize TLS/SSL for communication, but encryption of stored data is inconsistent. Some may use AES, but key management practices vary. | Often lengthy and complex, requiring significant user effort to understand data usage and sharing practices. | Low |
| Security Camera | Video and audio recordings, motion detection data, timestamps, potentially facial recognition data (depending on features). | Encryption during transmission is common (TLS/SSL), but local storage encryption is often weak or absent. Cloud storage encryption quality varies significantly between vendors. | Frequently buried within Terms of Service, lacking clear explanations of data retention policies and third-party access. | Low |
| Smart Speaker | Voice recordings, search queries, usage patterns, location data (if enabled), contact lists (if linked). | Encryption of data in transit is generally strong (TLS/SSL). However, concerns remain regarding data storage encryption and access controls. | Often vague regarding the extent of data collection and its use for targeted advertising or other purposes. Opt-out options can be difficult to find. | Medium |
| Smart Lighting System | Usage patterns, schedules, potentially location data (if integrated with other smart home devices). | Typically relies on standard Wi-Fi security protocols (WPA2/WPA3) for communication. Encryption of data stored within the hub or cloud is inconsistent. | Privacy policies often focus on data security rather than detailed data usage practices. | Medium |
| Smart Door Lock | Access logs, user codes, potentially remote access data. | Encryption strength varies. Some utilize robust encryption for communication and data storage, while others rely on less secure methods. | Policies may detail physical security measures but are often less transparent about data handling practices. | Medium |
| Wearable Fitness Tracker | Health data (heart rate, sleep patterns, activity levels), location data, personal information. | Encryption during data transmission is generally good, but data storage encryption and access controls can be problematic. Data aggregation and anonymization techniques are often used, but their effectiveness varies. | Privacy policies are becoming more detailed due to increased regulatory scrutiny, but understanding data sharing practices remains challenging. | Medium |
| Smart Refrigerator | Inventory data, usage patterns, potentially voice recordings (if voice control is present). | Encryption standards are inconsistent. Communication may be secured, but data stored locally or in the cloud may not be adequately protected. | Privacy policies often lack specific details about data collection and usage, particularly regarding connected services. | Low |
Illustrative comparison based on the article research brief. Verify current pricing, limits, and product details in the official docs before relying on it.
Layered mitigation strategies
Securing IoT devices requires a comprehensive, layered approach. Manufacturers need to prioritize security throughout the entire device lifecycle, from design to deployment to end-of-life. This includes incorporating security features into the hardware and software, conducting thorough security testing, and providing regular security updates.
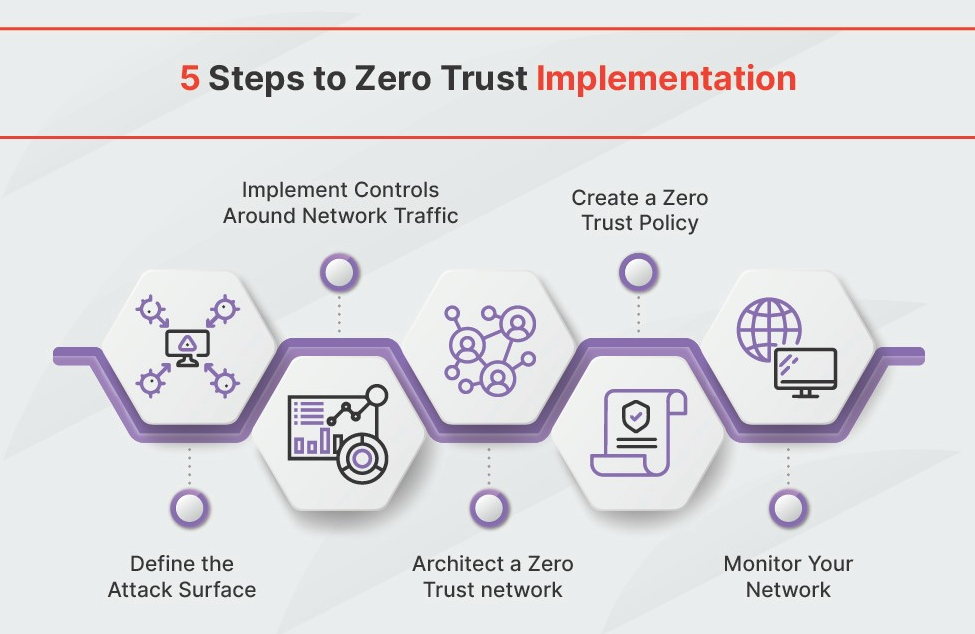
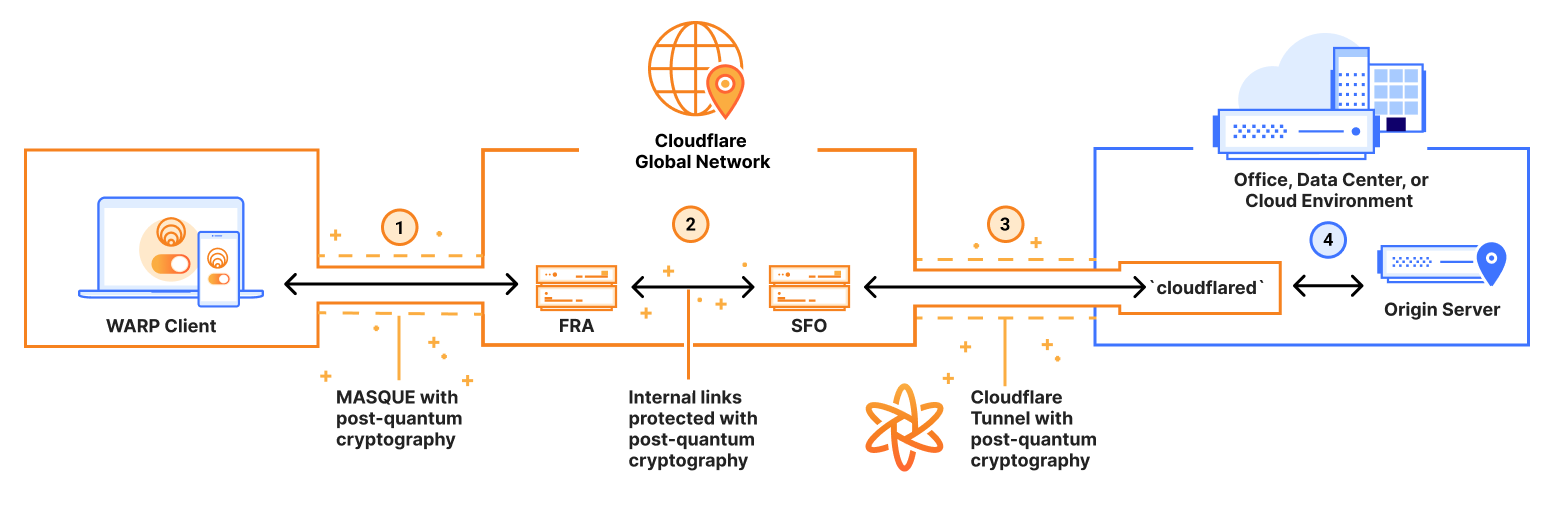
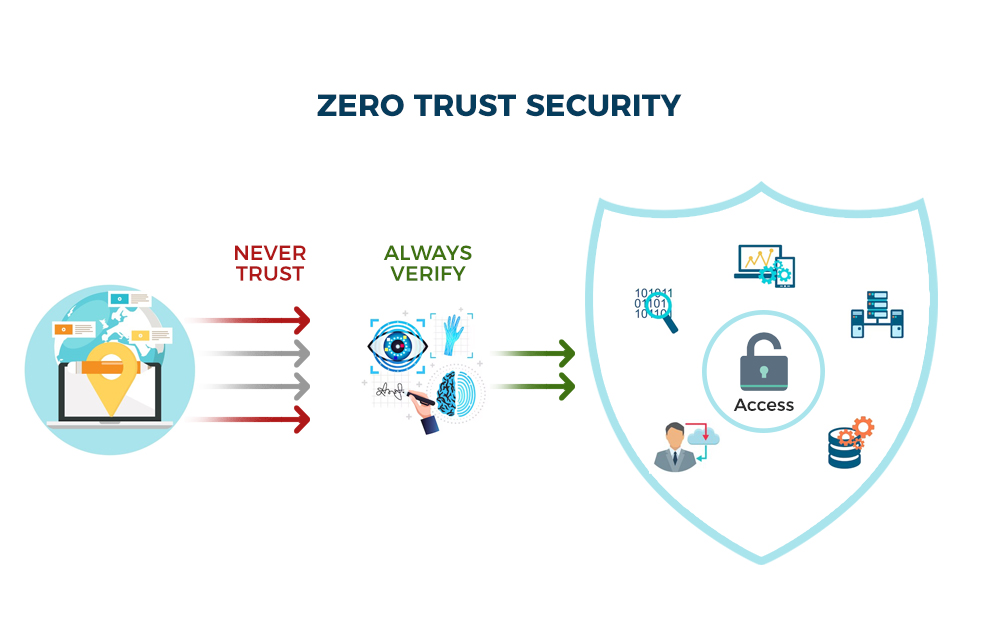
Businesses need to implement robust network security measures to protect their IoT devices. This includes network segmentation, intrusion detection and prevention systems, and strong access control policies. Regular vulnerability assessments and penetration testing are also essential. A zero-trust architecture, where no device is trusted by default, can significantly reduce the risk of compromise.
Consumers can also take steps to protect their IoT devices. This includes changing default credentials, enabling multi-factor authentication, keeping devices updated, and being mindful of the data they collect. User education is crucial for raising awareness about IoT security risks and promoting safe practices. A layered approach is the most effective way to reduce the overall risk.
- Secure Device Design: Incorporate security features into the hardware and software.
- Vulnerability Management: Regularly scan for and patch vulnerabilities.
- Isolate IoT devices on a separate VLAN to keep them away from sensitive company data.
- Intrusion Detection: Monitor network traffic for malicious activity.
- User Education: Raise awareness about IoT security risks.
Emerging threats
The IoT security landscape is constantly evolving, and new threats are emerging all the time. AI-powered attacks, for example, could automate the discovery and exploitation of vulnerabilities. The exploitation of machine learning models used in IoT devices is another emerging concern. Attackers could potentially manipulate these models to cause devices to malfunction or behave maliciously.
Potential solutions include blockchain-based security, which can provide a tamper-proof audit trail for device data and updates. Federated learning can allow devices to collaboratively train machine learning models without sharing sensitive data. Zero-trust architectures, which assume that no device is inherently trustworthy, can also help to mitigate the risk of compromise.
Winning this requires moving toward zero-trust architectures where no device is trusted by default, regardless of its location on the network. It is a technical arms race that requires faster patching cycles than we currently see in the consumer market.
🚨 Adobe Patches Acrobat Reader 0-Day Vulnerability Exploited in the Wild
— Cyber Security News (@The_Cyber_News) April 13, 2026
Source: https://t.co/vKP73YmZ1G
Adobe has issued an emergency security patch to neutralize a critical zero-day vulnerability in Acrobat Reader that is currently being exploited in the wild. Tracked as… pic.twitter.com/YLksutFkPA


No comments yet. Be the first to share your thoughts!