The quantum threat
For decades, our digital security has rested on the difficulty of certain mathematical problems. Algorithms like RSA and ECC, which protect everything from online banking to secure communications, rely on the fact that factoring large numbers or solving elliptic curve discrete logarithms is computationally expensive for classical computers. But that’s about to change. Quantum computing introduces a fundamentally different way of processing information, and it threatens to break these foundational algorithms.
The culprit is Shor’s algorithm, developed by mathematician Peter Shor in 1994. This algorithm can efficiently factor large numbers and solve elliptic curve problems – the very problems that underpin much of our current cryptography. While a practical, large-scale quantum computer capable of running Shor’s algorithm doesn’t exist yet, the progress in the field is accelerating. The potential for a "cryptographic winter" – a period where much of our encrypted data becomes vulnerable – is real.
2026 is a target based on current hardware projections. We expect quantum computers to reach sufficient maturity by then to threaten standard encryption. This is why we are moving toward post-quantum cryptography (PQC) now. Waiting for the hardware to arrive before fixing the software is a losing strategy.
The National Institute of Standards and Technology (NIST) has been leading the charge in standardizing PQC algorithms. Their multi-year standardization process, initiated in 2016, aims to identify and validate algorithms that can withstand attacks from both classical and quantum computers. This isn’t just an academic exercise; it’s a critical step in protecting our digital infrastructure.
NIST standards for post-quantum crypto
NIST’s PQC standardization process has been a rigorous, multi-round competition. The goal was to solicit, evaluate, and ultimately standardize a set of cryptographic algorithms that could replace those vulnerable to quantum attacks. It wasn’t simply about finding any quantum-resistant algorithm; it was about finding algorithms that are secure, efficient, and practical for widespread deployment.
After several rounds of evaluation, NIST announced its initial set of selected algorithms in 2022 and 2023. These include CRYSTALS-Kyber for key encapsulation, and CRYSTALS-Dilithium, FALCON, and SPHINCS+ for digital signatures. The selection wasn't based on a single metric; NIST considered factors like security, performance, and implementation complexity. Each algorithm offers a different trade-off between these characteristics.
CRYSTALS-Kyber, a lattice-based algorithm, stands out for its performance and relatively small key sizes. CRYSTALS-Dilithium, also lattice-based, offers strong security but with larger signatures. FALCON, another lattice-based algorithm, aims for smaller signatures than Dilithium. SPHINCS+, a hash-based signature scheme, offers a different security foundation – it doesn’t rely on the hardness of mathematical problems, making it a valuable addition to the toolkit.
These algorithms fall into different categories. Lattice-based cryptography, like CRYSTALS-Kyber and Dilithium, relies on the difficulty of solving problems involving lattices. Code-based cryptography leverages the difficulty of decoding general linear codes. Multivariate cryptography uses systems of multivariate polynomial equations. And hash-based cryptography, exemplified by SPHINCS+, relies on the security of cryptographic hash functions. Having a diversity of approaches is important because it reduces the risk of a single breakthrough in quantum algorithms compromising all of our defenses.
NIST is still evaluating other candidates. The current list is a starting point, and I expect these standards to change as we learn more about how these algorithms perform in the real world.
- Kyber is for key encapsulation
- CRYSTALS-Dilithium: Digital signature scheme
- FALCON: Digital signature scheme
- SPHINCS+: Digital signature scheme
Finding your current encryption
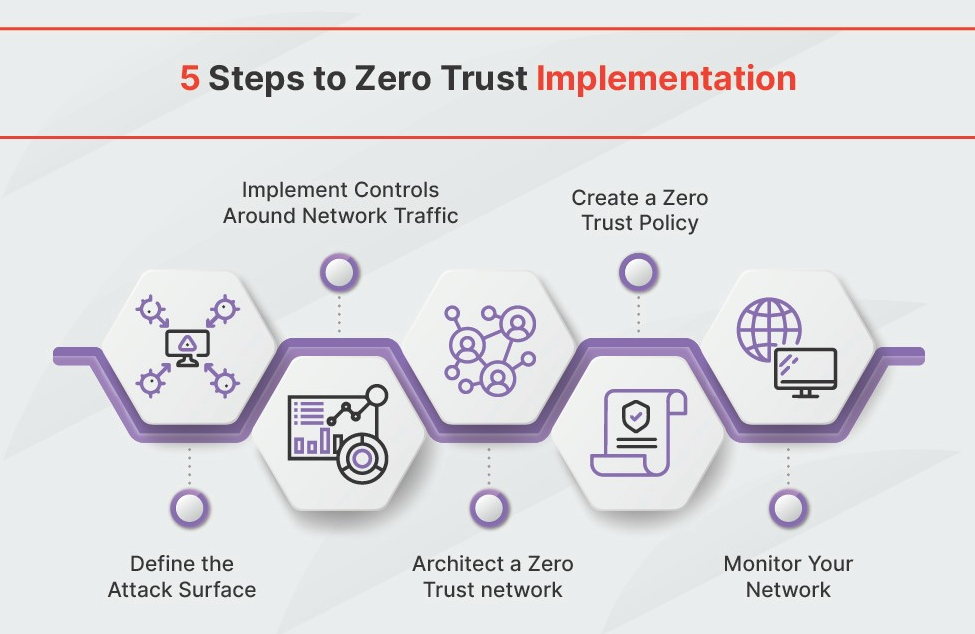
Before you can migrate to PQC, you need to know what cryptography you're already using. This is surprisingly difficult. Most organizations don't have a comprehensive inventory of their cryptographic assets. You need to identify every place where encryption, digital signatures, or key exchange protocols are employed within your network.
This includes examining TLS/SSL configurations on web servers and other network devices, VPN connections, SSH keys used for remote access, digital signatures used to verify software updates, and key exchange protocols used in various applications. Don’t forget about internal systems – databases, file servers, and application-level encryption all need to be accounted for.
A complete inventory is crucial for prioritizing your migration efforts and ensuring that no critical systems are left vulnerable. It allows you to understand your exposure and develop a targeted plan for adopting PQC. Ignoring this step is like fighting a fire blindfolded.
Tools like OpenSSL can help you inspect the cryptographic configurations of your systems. Network scanners can identify devices using outdated or vulnerable protocols. Specialized crypto inventory tools are also emerging, though they may require significant configuration and customization to fit your specific environment. Regular scans are also vital – your crypto inventory isn’t a one-time project.
Where to start migrating
You can’t migrate everything at once. Prioritization is key. Focus on systems that handle long-lived secrets or data that needs to remain confidential for many years into the future. Think about data with a long shelf life – financial records, intellectual property, sensitive customer data, and national security information.
The concept of crypto-agility is paramount here. This refers to the ability to quickly and easily switch cryptographic algorithms without requiring major changes to your systems. Systems designed with crypto-agility in mind will be much easier to migrate to PQC when the time comes. Avoid hardcoding specific algorithms into your applications.
The risk associated with different types of data varies. A breach of financial records could have immediate and severe consequences, while a compromise of less sensitive data might be less critical. Assess the potential impact of a cryptographic failure on each system and prioritize accordingly. Consider the regulatory requirements that apply to your data.
Systems that communicate with external parties are also high-priority targets. If you exchange sensitive data with partners or customers, you need to ensure that your cryptographic protocols are compatible with theirs. Coordination with your partners will be essential for a smooth transition to PQC. Don't assume they're already prepared.
How to use post-quantum algorithms
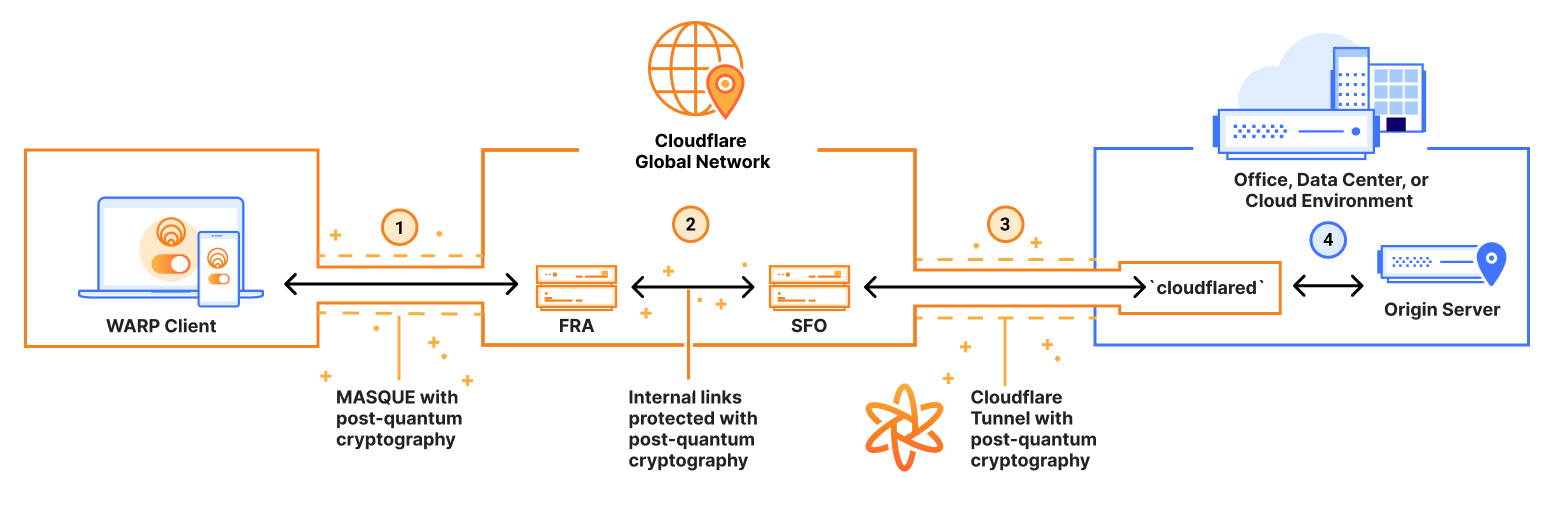
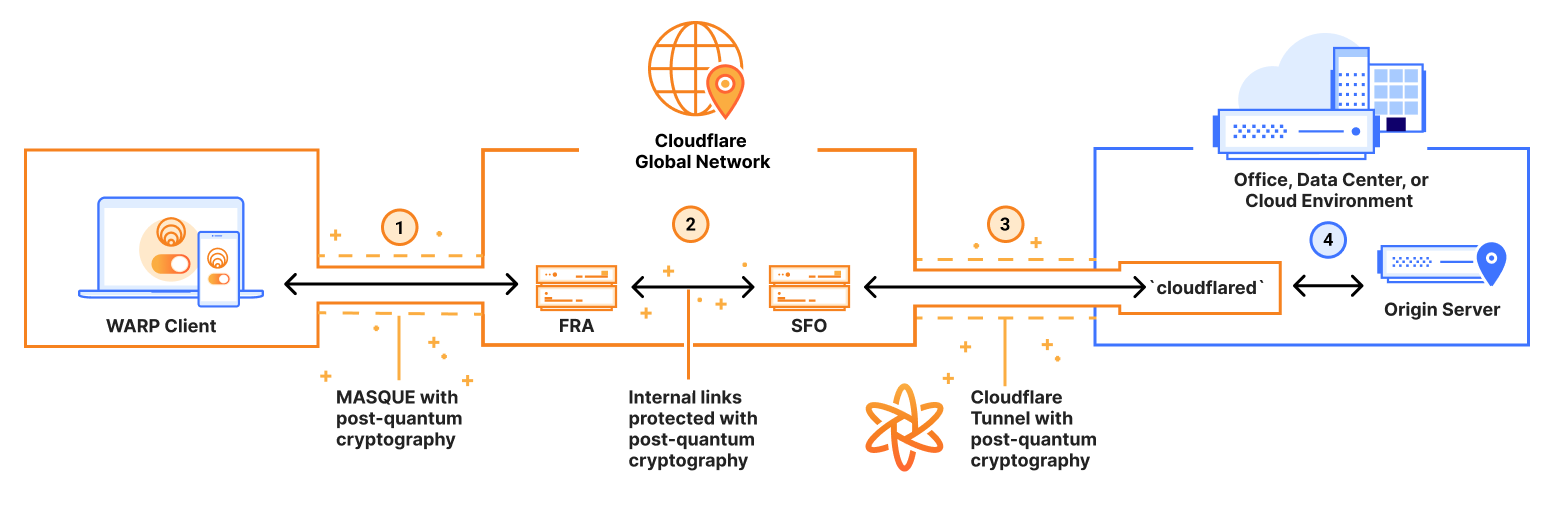
Implementing PQC algorithms isn’t a simple drop-in replacement for existing cryptography. It requires careful planning and testing. One of the most promising approaches is to use TLS 1.3 with post-quantum key exchange. TLS 1.3 is designed to be more flexible and extensible than previous versions, making it easier to integrate new cryptographic algorithms.
Hybrid approaches – combining classical and post-quantum algorithms – are often recommended as a first step. This provides a degree of protection against both classical and quantum attacks, while also ensuring compatibility with systems that don’t yet support PQC. For example, you might use a hybrid key exchange that combines ECDHE with CRYSTALS-Kyber.
Integrating PQC into existing systems can be challenging, particularly for legacy applications. Many systems were not designed with crypto-agility in mind, making it difficult to switch algorithms without significant code changes. Thorough testing is essential to ensure that PQC integration doesn’t introduce new vulnerabilities or performance issues.
Fortunately, a growing number of tools and libraries now support PQC. OpenSSL 3.0 and later versions include support for several of the NIST-selected algorithms. Programming languages like Python and Java also have libraries that provide PQC implementations. However, these libraries are still under development and may not be suitable for all applications.
Be aware of potential performance overhead. PQC algorithms can be computationally more expensive than classical algorithms, which could impact the performance of your systems. Careful benchmarking and optimization are crucial.
- Identify systems using vulnerable cryptography.
- Prioritize based on data sensitivity and lifespan.
- Implement hybrid key exchange mechanisms.
- Test thoroughly and monitor performance.
NIST Post-Quantum Cryptography Standard Algorithms: A Comparative Overview
| Algorithm | Primary Use Case | Key Size & Signature Characteristics | Security Foundation | Implementation Considerations |
|---|---|---|---|---|
| Kyber | Key Encapsulation Mechanism (KEM) - for establishing shared secrets | Generally smaller key and ciphertext sizes compared to signature schemes. Designed for efficient performance. | Based on the hardness of solving the Module Learning With Errors (MLWE) problem over structured lattices. | Considered relatively straightforward to implement, with optimizations available for various platforms. |
| Dilithium | Digital Signature Scheme | Offers a balance between signature size and performance. Multiple security levels are defined. | Relies on the Short Integer Solution (SIS) problem over lattices. | Implementation complexity is moderate, requiring careful attention to lattice-based cryptography best practices. |
| Falcon | Digital Signature Scheme | Characterized by very small signature sizes, making it suitable for bandwidth-constrained environments. | Based on the Shortest Integer Solution (SIS) problem, utilizing a NTRU lattice structure. | Implementation can be more complex than Dilithium due to the NTRU lattice structure and requires specific optimizations for performance. |
| SPHINCS+ | Digital Signature Scheme | Provides strong security assurances, even in the face of potential lattice-based cryptanalysis. Signature sizes are larger than other schemes. | Based on hash functions, offering resilience against attacks targeting lattice structures. Security relies on the collision resistance of the underlying hash function. | Implementation is generally more resource-intensive than other algorithms due to the hash-based approach, but does not rely on complex mathematical structures. |
| Kyber | Key Exchange | Designed for efficient key exchange with relatively low computational overhead. | Security is predicated on the presumed difficulty of solving the Module-LWE problem. | Offers a good balance between performance and security for key exchange applications. |
| Dilithium | Digital Signatures | Provides a robust signature scheme suitable for a wide range of applications. | Its security foundation is built on the hardness of lattice problems, specifically variants of SIS. | Requires careful implementation to avoid side-channel vulnerabilities common in lattice-based cryptography. |
| Falcon | Digital Signatures (bandwidth-constrained scenarios) | Excels in scenarios where minimizing signature size is paramount. | Leverages the hardness of solving the SIS problem on NTRU lattices. | Implementation demands expertise in NTRU lattice cryptography and requires optimization for practical performance. |
Illustrative comparison based on the article research brief. Verify current pricing, limits, and product details in the official docs before relying on it.
CISA Guidance and Resources
The Cybersecurity and Infrastructure Security Agency (CISA) is actively working to promote the adoption of PQC across the federal government and the private sector. They've published guidance on migrating to PQC and have developed a list of Product Categories for Technologies That Use Post-Quantum Cryptography Standards.
This list categorizes technologies based on their risk level and provides recommendations for when to begin migrating to PQC. For example, systems that handle highly sensitive data should prioritize PQC migration sooner than systems that handle less sensitive data. CISA's guidance is a valuable resource for organizations of all sizes.
Vendor support is crucial for successful PQC adoption. You need to work with your software and hardware vendors to ensure that their products support PQC algorithms. Demand PQC support from your vendors and ask about their plans for transitioning to PQC. The more pressure vendors face, the faster they will respond.
CISA provides implementation guides and risk categories on their site. They are currently the main driver for PQC adoption in the US, especially for those of us working with federal data.
Beyond 2026: Ongoing Vigilance
Migrating to PQC isn’t a one-time fix. It’s an ongoing process. The field of quantum computing is rapidly evolving, and new algorithms and attacks could emerge in the future. Continuous monitoring and adaptation are essential to maintain your security posture.
Even after you’ve implemented PQC algorithms, you need to stay informed about the latest research in the field. Researchers are constantly exploring new ways to break cryptographic systems, both classical and quantum. Be prepared to update your algorithms and protocols as needed.
The potential for new quantum algorithms to emerge is a real threat. The algorithms that are considered secure today might be vulnerable tomorrow. That’s why it’s so important to maintain crypto-agility and be prepared to switch algorithms quickly.
Collaboration between researchers, industry, and government is vital for ensuring the long-term security of our digital infrastructure. Sharing information and working together is the best way to stay ahead of the curve. The threat is evolving, and our defenses must evolve with it.
- FAQ: What if a new quantum algorithm breaks the current PQC standards?
- Answer: Crypto-agility is key. Having the ability to quickly switch algorithms allows you to respond to new threats.
- FAQ: How often should I reassess my PQC implementation?
- Answer: At least annually, or more frequently if there are significant developments in the field.


No comments yet. Be the first to share your thoughts!