Moving past the perimeter
The old model of trusting everything inside a network perimeter is dead. When apps lived in a basement server room, a firewall was enough. Now, with remote teams and cloud services, there is no perimeter to defend.
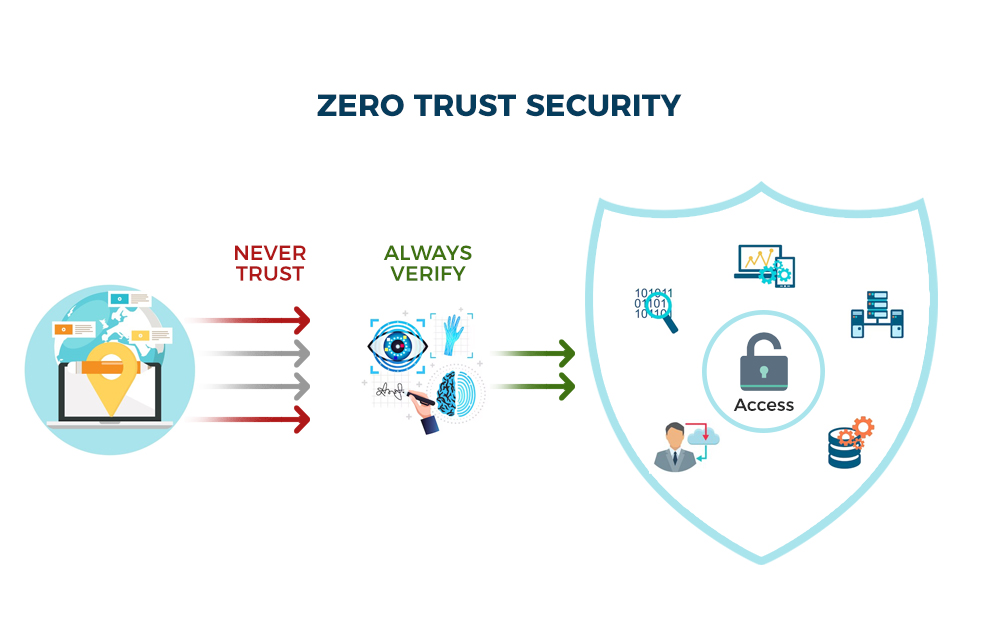
The result? Breaches are increasingly originating inside networks, exploiting the implicit trust placed in users and devices. Zero Trust is a response to this reality. It’s not a single product or technology, but a fundamental shift in security philosophy. The core idea is simple: trust nothing, verify everything. Every user, every device, every application—regardless of location—must be authenticated, authorized, and continuously validated before being granted access.
There’s a lot of marketing noise around Zero Trust, and it's easy to get lost in the buzzwords. Some vendors try to sell it as a quick fix, but that’s a misunderstanding. It’s a strategic approach that requires a holistic overhaul of security practices. It’s about minimizing the attack surface and limiting the blast radius of any potential breach. This isn’t about making security more complex, it’s about making it more precise.
The move to Zero Trust isn’t just driven by technological changes. Regulatory pressures, like those stemming from increasing data privacy regulations, also play a role. Organizations are facing greater scrutiny and potential penalties for data breaches, making a stronger security posture a business imperative. This isn’t just about avoiding headlines; it’s about protecting sensitive data and maintaining customer trust.
Practical advice from the DoD
The Department of Defense (DoD) has been a strong advocate for Zero Trust, and their Zero Trust Implementation Guideline Primer offers a surprisingly detailed and practical guide. Developed by the NSA, it’s geared towards federal agencies, but the principles are broadly applicable to any enterprise environment. It’s a much more granular document than the NIST framework, offering specific recommendations.
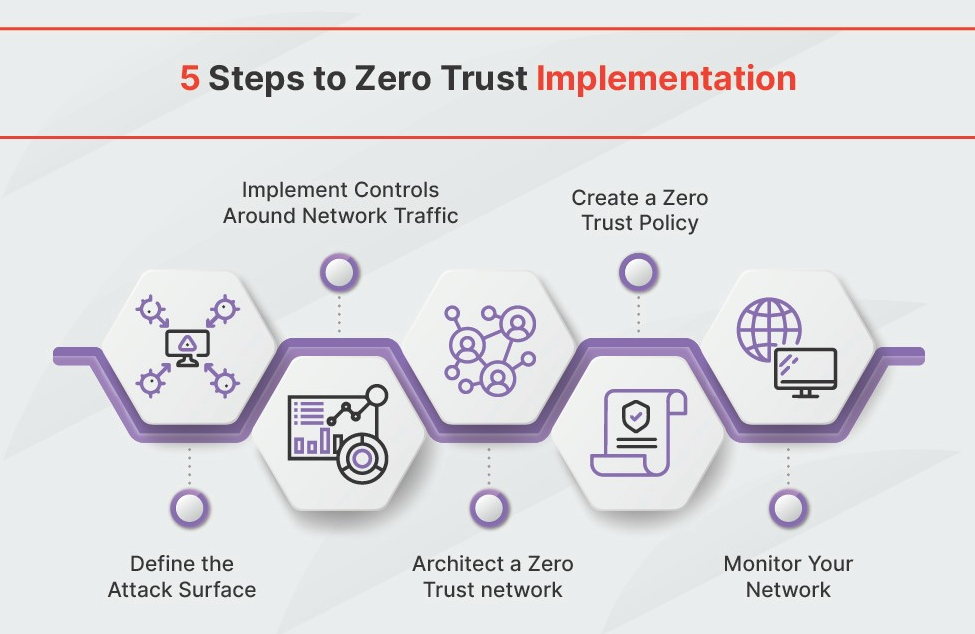
The Primer focuses on several key areas. User access management is paramount, emphasizing the need for strong authentication, least privilege access, and continuous monitoring of user behavior. Device security is also critical, requiring endpoint detection and response (EDR) solutions and robust device posture assessment. Network segmentation, achieved through microsegmentation, is heavily emphasized as a way to contain breaches.
The guidance also covers application security, advocating for secure development practices and continuous vulnerability scanning. A significant portion of the document is dedicated to data protection, outlining strategies for data encryption, data loss prevention (DLP), and data access control. It also stresses the importance of automating security processes to improve efficiency and responsiveness.
What I find particularly useful is the emphasis on phased implementation. The DoD recognizes that transitioning to Zero Trust is a complex undertaking and recommends a gradual approach, starting with critical systems and data. This is a sensible strategy for organizations with limited resources or complex IT environments. The document also acknowledges the importance of organizational change management and training.
Identity as the New Perimeter
In a Zero Trust architecture, identity becomes the new perimeter. Traditional perimeter-based security relied on trusting anyone inside the network. Zero Trust flips that on its head: no one is trusted by default. Every access request, regardless of origin, must be verified. This makes robust Identity and Access Management (IAM) absolutely essential.
Multi-Factor Authentication (MFA) is a cornerstone of Zero Trust identity management. Requiring users to provide multiple forms of verification—something they know (password), something they have (security token), and something they are (biometrics)—significantly reduces the risk of unauthorized access. Privileged Access Management (PAM) is equally important, controlling and monitoring access to sensitive systems and data.
Emerging technologies are further strengthening identity security. Passwordless authentication, using technologies like biometrics or FIDO2 security keys, eliminates the vulnerabilities associated with passwords. Continuous authentication goes a step further, continuously verifying a user’s identity based on behavioral biometrics and other factors. This provides a more dynamic and adaptive security posture.
However, implementing these technologies isn’t without challenges. User experience is a key consideration. Overly cumbersome authentication processes can frustrate users and lead to workarounds. Balancing security with usability is crucial. Organizations need to carefully evaluate their IAM solutions and choose technologies that provide strong security without sacrificing user convenience.
Microsegmentation: Containing the Blast Radius
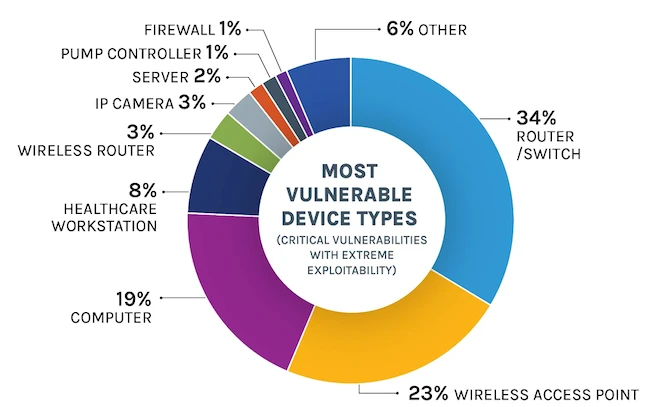
Microsegmentation is the practice of dividing a network into smaller, isolated segments. This limits the lateral movement of attackers within the network, containing the blast radius of a potential breach. If one segment is compromised, the attacker is prevented from easily accessing other sensitive systems and data.
There are several approaches to microsegmentation. Software-Defined Networking (SDN) allows you to dynamically define and enforce network policies based on application requirements. Network virtualization creates isolated virtual networks, providing a similar level of isolation. Firewalling is also a key component, using granular rules to control traffic between segments. Some security vendors, like Illumio, specialize in microsegmentation solutions.
Implementing microsegmentation in complex environments can be challenging. Legacy applications often weren’t designed with segmentation in mind, making it difficult to isolate them. Discovering application dependencies is also crucial. You need to understand how applications interact with each other to avoid disrupting business processes. It requires a thorough understanding of your network architecture.
Despite the challenges, the benefits of microsegmentation are significant. It’s one of the most effective ways to limit the impact of a breach. It also improves compliance with data privacy regulations, such as GDPR and CCPA, by reducing the risk of data exfiltration. It’s not a silver bullet, but it’s a critical component of a Zero Trust architecture.
Continuous Monitoring and Analytics
Zero Trust isn’t a "set it and forget it" security model. Continuous monitoring and security analytics are essential for detecting and responding to threats in real time. Traditional security tools, like firewalls, are reactive. They block known threats, but they often miss sophisticated attacks. Zero Trust requires a proactive approach.
Security Information and Event Management (SIEM) systems collect and analyze security logs from various sources, providing a centralized view of security events. User and Entity Behavior Analytics (UEBA) uses machine learning to detect anomalous behavior, identifying potential insider threats and compromised accounts. Threat intelligence feeds provide information about emerging threats, allowing you to proactively defend against them.
The key is automation. Manually analyzing security logs is simply not scalable. Automated threat detection and response capabilities are crucial for quickly identifying and mitigating threats. Security Orchestration, Automation and Response (SOAR) platforms automate security workflows, streamlining incident response.
Continuous monitoring creates a massive data trail. You need a team that knows how to filter out the noise, or you'll spend all day chasing false positives instead of stopping actual breaches.
What to watch for in 2026
Looking ahead to 2026, several trends are likely to shape the future of Zero Trust. Artificial intelligence (AI) and machine learning (ML) will play an increasingly important role in automating threat detection and response. AI-powered security tools will be able to identify and block sophisticated attacks with greater accuracy and speed.
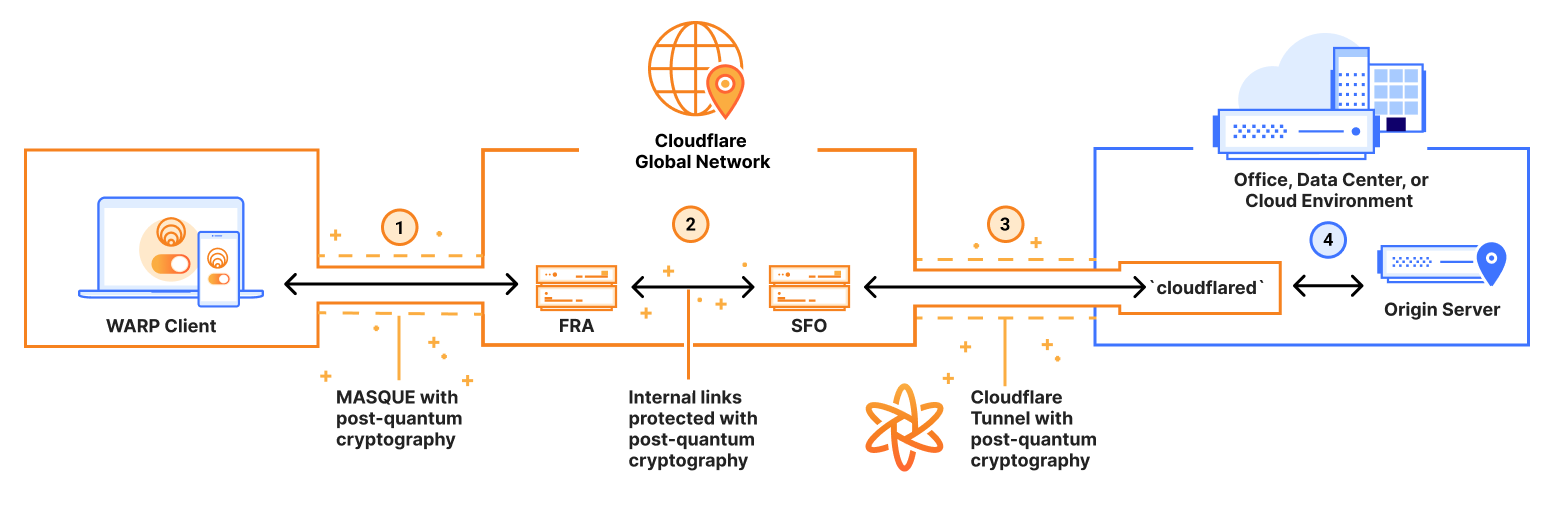
Cloud security will become even more critical. As more organizations migrate to the cloud, securing cloud environments will be a top priority. Zero Trust principles need to be extended to the cloud, ensuring that access to cloud resources is strictly controlled and continuously monitored. The complexity of multi-cloud environments will drive demand for unified security solutions.
The rise of remote work is another significant trend. Securing remote access to corporate resources is a major challenge. Zero Trust architectures, with their emphasis on identity verification and least privilege access, are well-suited to address this challenge. We’ll likely see increased adoption of technologies like Zero Trust Network Access (ZTNA).
I'm not sure about specific product predictions, but I expect to see more integration of Zero Trust principles into existing security tools. Security vendors will increasingly offer Zero Trust-enabled versions of their products. The focus will be on simplifying implementation and reducing complexity. The goal is to make Zero Trust accessible to organizations of all sizes.
Zero Trust Tool Selection: Qualitative Decision Matrix
| Security Need | Cloud-Native | On-Premise | Managed Service |
|---|---|---|---|
| Identity and Access Management (IAM) | Strong suitability; offers scalability and integration with cloud applications. | Suitable, but requires significant infrastructure management. | Good option for organizations lacking internal IAM expertise. |
| Microsegmentation | Generally well-suited due to dynamic policy enforcement capabilities. | Can be complex to implement and maintain, particularly in large environments. | Provides simplified deployment and management of microsegmentation policies. |
| Threat Detection & Response | Leverages cloud-based threat intelligence and analytics. | Requires robust internal security operations (SecOps) capabilities. | Offers 24/7 monitoring and incident response services. |
| Data Security | Data Loss Prevention (DLP) tools integrate effectively with cloud storage. | Provides greater control over data residing within the organization's network. | Can offer comprehensive data security solutions, including encryption and access control. |
| Endpoint Security | Mobile Device Management (MDM) and Endpoint Detection and Response (EDR) solutions are commonly cloud-delivered. | Allows for strict control over endpoint configurations and security policies. | Provides centralized management and threat protection for endpoints. |
| Network Visibility & Analytics | Offers broad network visibility through cloud-based dashboards and reporting. | Requires investment in network monitoring tools and skilled analysts. | Provides proactive network monitoring and threat hunting services. |
Illustrative comparison based on the article research brief. Verify current pricing, limits, and product details in the official docs before relying on it.



No comments yet. Be the first to share your thoughts!