The failure of the castle-and-moat model
Digital security used to be simple: build a high wall and keep the bad guys out. That 'castle-and-moat' logic doesn't work anymore. Between remote teams and cloud apps, there is no single perimeter left to defend. The 2020 SolarWinds breach and the 2023 MOVEit attacks proved that once someone is inside, the old defenses just watch them walk away with the data.
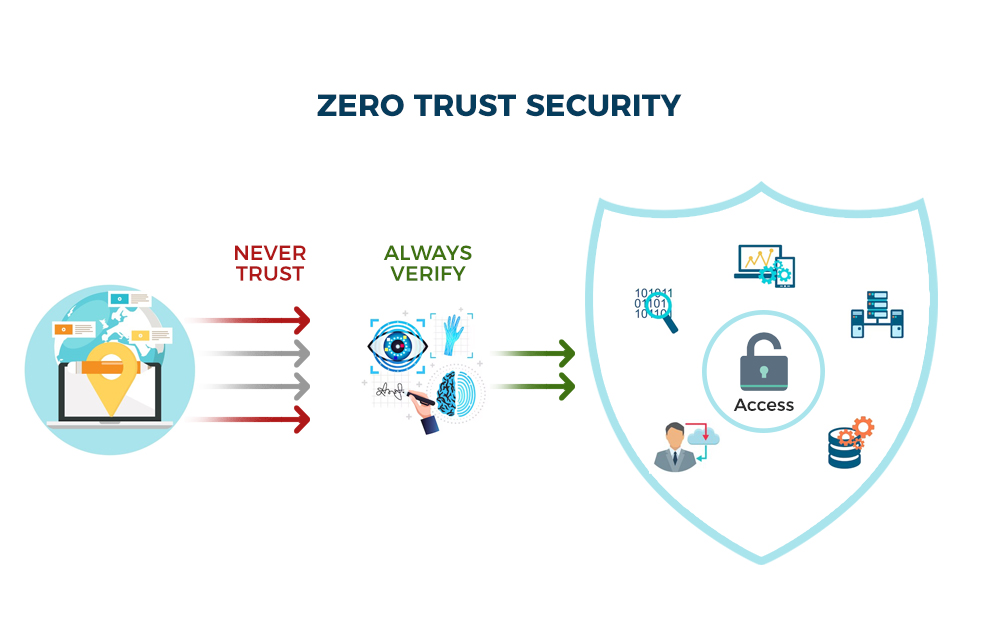
These attacks weren't about breaking into the network; they were about operating within it. Once attackers gained a foothold, they moved laterally, exploiting trust relationships to access sensitive data. This is where Zero Trust comes in. It’s a fundamental shift in thinking, moving away from "trust but verify’ to ‘never trust, always verify."
Zero Trust isn't a single product you can buy, though many vendors will try to sell you that idea. It’s a strategic approach to security, a philosophy that assumes breach and verifies every user, device, and application before granting access to resources. It’s about minimizing the blast radius of an attack and making it significantly harder for attackers to move around your network, even if they manage to get inside. It’s a more realistic model for the current threat environment.
Implementing Zero Trust isn’t easy, and it’s not a quick fix. It requires a comprehensive assessment of your existing security posture, a clear understanding of your critical assets, and a willingness to embrace a new way of thinking about security. But the alternative – continuing to rely on outdated perimeter-based defenses – is increasingly risky.
NIST’s seven pillars
The National Institute of Standards and Technology (NIST) has outlined seven core pillars that form the foundation of a Zero Trust Architecture, detailed in their Special Publication 800-207. These pillars aren’t necessarily sequential steps, but rather interconnected areas that must be addressed to achieve a robust Zero Trust posture. Understanding these pillars is essential for any organization embarking on a Zero Trust journey.
Let's break them down: Data Security focuses on classifying data, understanding its sensitivity, and implementing appropriate controls to protect it, both in transit and at rest. Workforce Security emphasizes verifying the identity of every user and ensuring they only have access to the resources they need to perform their job. Device Security ensures that all devices accessing your network – company-owned or personal – meet specific security requirements.
Application Security involves securing the applications themselves, from development to deployment, and continuously monitoring them for vulnerabilities. Network Security moves beyond traditional perimeter defenses to microsegment the network, limiting the lateral movement of attackers. Automation & Orchestration is about leveraging automation to streamline security processes and respond to threats more effectively. Finally, Visibility & Analytics are crucial for detecting and responding to malicious activity. You can't protect what you can’t see.
These pillars aren’t independent silos. They work together to create a layered defense that makes it significantly harder for attackers to compromise your systems. Implementing Zero Trust requires a holistic approach that addresses all seven pillars, tailored to your organization’s specific needs and risk profile.
- Data security: Classifying and encrypting sensitive files.
- Workforce Security
- Device Security
- Application Security
- Network Security
- Automation & Orchestration
- Visibility & Analytics
NIST Zero Trust Pillars Assessment
- Identity - Do you currently verify the identity of every user and device attempting to access network resources?
- Device - Do you currently assess the security posture of every device before granting access to resources?
- Network - Do you currently microsegment your network to limit the blast radius of potential breaches?
- Application Workloads - Do you currently implement least privilege access controls for all application workloads?
- Data - Do you currently classify and protect your data based on its sensitivity?
- Automation & Orchestration - Do you currently leverage automation to enforce Zero Trust policies and respond to security events?
- Visibility & Analytics - Do you currently continuously monitor and analyze network traffic and user behavior for anomalies?
Identity is the new perimeter
At the heart of any Zero Trust architecture lies robust Identity and Access Management (IAM). Zero Trust fundamentally challenges the idea of implicit trust based on network location. Instead, every access request is treated as if it originates from an untrusted source. This means verifying the identity of the user every time they attempt to access a resource.
Strong authentication is paramount. Multi-Factor Authentication (MFA) is no longer optional; it's a necessity. Requiring users to provide multiple forms of verification – something they know (password), something they have (security token), and something they are (biometric scan) – significantly reduces the risk of unauthorized access. Beyond authentication, least privilege access is essential. Users should only be granted the minimum level of access required to perform their duties.
Access shouldn't be a one-time hall pass. It needs constant re-evaluation based on what the user is doing and which device they're holding. Identity Providers (IdPs) are the engine here, managing credentials and enforcing rules in real-time. You'll need tight integration between your IdP and the rest of your stack for this to actually work.
Microsegmentation: Containment is Key
Microsegmentation is a network security technique that divides a network into small, isolated segments. Unlike traditional network segmentation, which often creates broad zones of trust, microsegmentation creates granular policies that control traffic between individual workloads. This significantly limits the blast radius of a potential breach. If an attacker compromises one segment, they won't be able to easily move laterally to other parts of the network.
Think of it like building internal firewalls around every application and workload. Each segment has its own security policies, defining exactly which traffic is allowed in and out. This is a departure from the traditional "trust but verify" approach where internal traffic was often implicitly trusted. Microsegmentation forces you to explicitly define trust relationships.
Implementing microsegmentation can be challenging, particularly in complex environments with many interconnected systems. It requires a deep understanding of application dependencies and network traffic patterns. However, the benefits – improved security and reduced risk – are well worth the effort. VMware's NSX is often cited as a platform for achieving microsegmentation, but other solutions are available.
A good example of successful microsegmentation comes from a large financial institution that implemented it to protect its sensitive customer data. By segmenting its network and enforcing strict access controls, the institution was able to contain a ransomware attack and prevent it from spreading to critical systems, saving them potentially millions in damages.
- Identify critical assets and applications.
- Map application dependencies.
- Define granular security policies.
- Implement microsegmentation technology.
- Continuously monitor and refine policies.
Continuous Monitoring and Analytics
Zero Trust isn’t a "set it and forget it" security model. Continuous monitoring and analytics are essential for detecting and responding to threats in real-time. You need to constantly monitor your network for suspicious activity, analyze security logs, and identify potential vulnerabilities. This requires a combination of technology and expertise.
Security Information and Event Management (SIEM) systems collect and analyze security logs from various sources, providing a centralized view of your security posture. User and Entity Behavior Analytics (UEBA) tools go a step further, using machine learning to detect anomalous behavior that may indicate a security threat. These tools can identify patterns that would be difficult for human analysts to spot.
However, the sheer volume of data generated by these tools can be overwhelming. Automation is key. You need to automate threat detection, incident response, and vulnerability management to reduce the workload on your security team and improve your response time. This might involve using Security Orchestration, Automation and Response (SOAR) platforms to automate repetitive tasks.
The goal is to move from reactive security – responding to incidents after they occur – to proactive security – identifying and mitigating threats before they cause damage. Continuous monitoring and analytics are the foundation of this proactive approach.
Common roadblocks and how to bypass them
Implementing Zero Trust isn’t without its challenges. Legacy systems that weren’t designed with Zero Trust in mind can be difficult to integrate. The complexity of implementing microsegmentation and enforcing granular access controls can be daunting. And perhaps the biggest challenge is cultural resistance – convincing users and IT staff to embrace a new way of thinking about security.
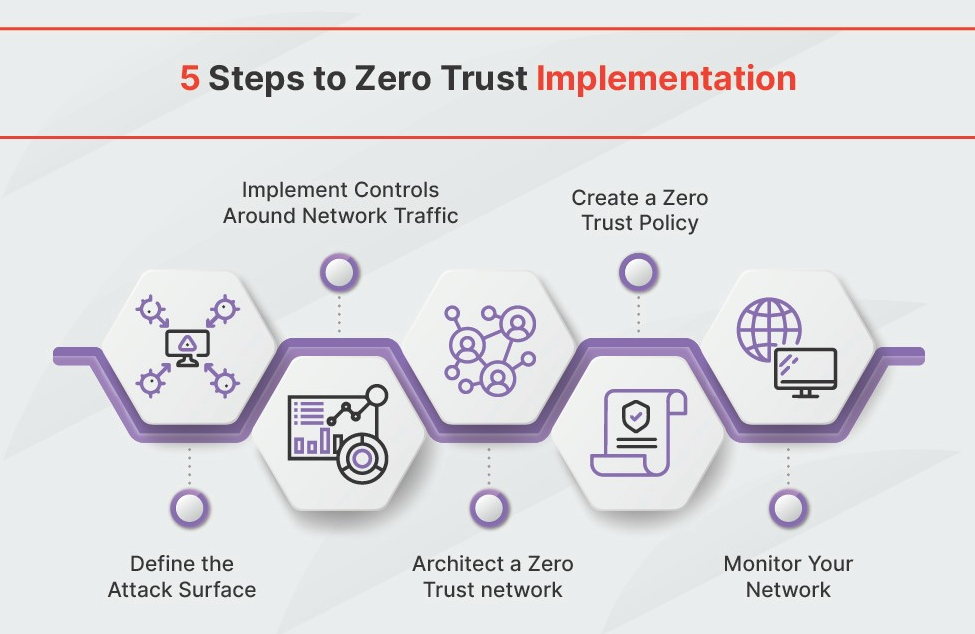
One of the most effective ways to overcome these challenges is to take a phased approach. Start with a pilot project, focusing on a critical application or workload. This will allow you to test your Zero Trust implementation and identify any potential issues before rolling it out more broadly. Prioritize the most critical assets and applications first.
Address legacy systems by isolating them and implementing compensating controls. This might involve using network segmentation or application whitelisting to limit their exposure. Invest in training and education to help users and IT staff understand the benefits of Zero Trust and how it will impact their work. Communicate clearly and frequently throughout the implementation process.
Remember that Zero Trust is a journey, not a destination. It’s an ongoing process of continuous improvement. Regularly review your security policies, monitor your network for threats, and adapt your Zero Trust implementation as your organization’s needs evolve.
Essential Zero Trust Network Access Solutions for SMBs
Explains foundational principles of Zero Trust networking. · Provides practical guidance for network segmentation. · Discusses identity and access management in a Zero Trust context.
This book offers a foundational understanding of Zero Trust networking principles and practical implementation strategies.

Focuses on securing hybrid and multi-cloud environments. · Details automated governance and compliance for Zero Trust. · Addresses the challenges of modern cloud security.
This resource provides essential insights into extending Zero Trust principles to complex cloud infrastructures, with a focus on automation and compliance.

Covers identity architecture design using Microsoft Entra ID (Azure AD). · Integrates Zero Trust principles with identity and access management (IAM). · Offers best practices for scalability and governance.
This handbook is crucial for organizations leveraging Microsoft Entra ID to build a robust Zero Trust identity foundation.
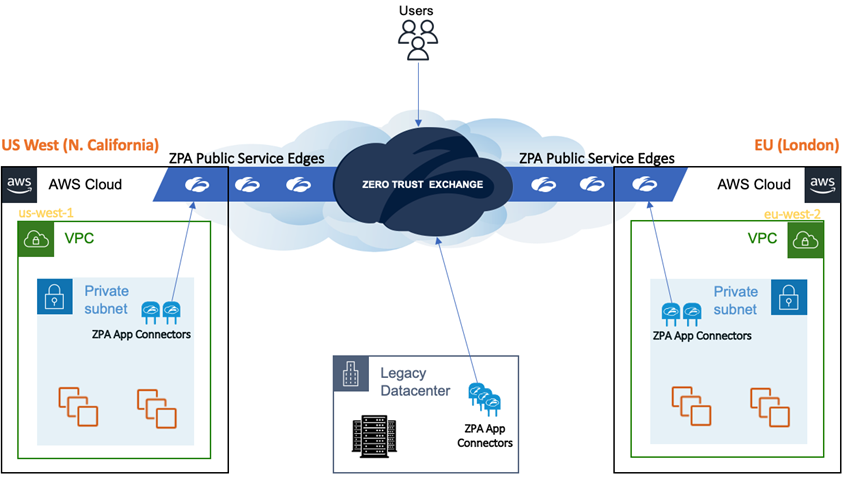
Provides secure, identity-aware access to private applications. · Eliminates network-level access, reducing attack surface. · Offers granular access policies based on user and device posture.
Zscaler Private Access is a leading Zero Trust Network Access (ZTNA) solution offering robust identity management and access control, crucial for implementing a Zero Trust Architecture in small to medium-sized businesses.
Delivers secure access to cloud, web, and private applications. · Integrates network security and SASE capabilities. · Enforces Zero Trust policies across all user and device access.
Palo Alto Networks Prisma Access is a leading Zero Trust Network Access (ZTNA) solution offering robust identity management and access control, crucial for implementing a Zero Trust Architecture in small to medium-sized businesses.
As an Amazon Associate I earn from qualifying purchases. Prices may vary.



No comments yet. Be the first to share your thoughts!