The expanding attack surface
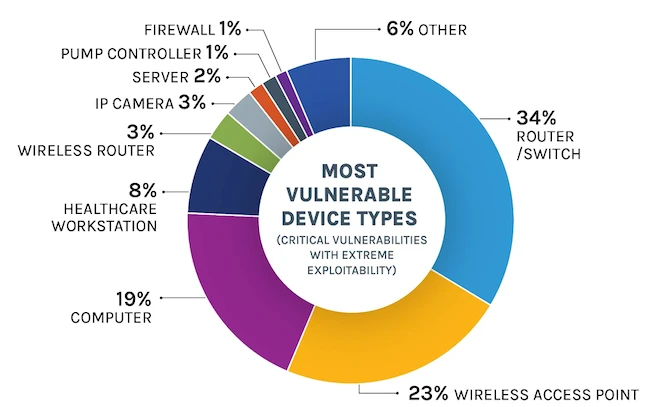
IoT is everywhere. We use smart thermostats at home and sensors in factories. Statista expects 43 billion connected devices by 2027. This growth gives hackers more ways to get into private networks.
Most of these gadgets weren't built with security in mind. Because they are so common, one weak camera or sensor is often enough for a hacker to reach an entire corporate network.
The economic consequences of IoT breaches are substantial. A report by IBM’s Cost of a Data Breach Report 2023 found the average cost of a data breach reached $4.45 million. Given the increasing reliance on IoT, these costs are only expected to rise. Addressing IoT security vulnerabilities is therefore not just a technical imperative, but a critical business necessity, especially as we move into 2026 and beyond.

Default passwords and weak authentication
One of the most persistent and easily exploited IoT security vulnerabilities is the use of default passwords. Many devices ship with well-known credentials like 'admin' and 'password,' or easily guessable combinations. Attackers routinely scan networks for devices using these default settings, gaining unauthorized access in a matter of minutes.
The issue is that many devices don't force you to change the password or use multi-factor authentication (MFA). Cheap hardware often lacks the memory to run modern security tools, so manufacturers skip them to keep costs down.
NIST Special Publication 800-213, IoT Device Cybersecurity Guidance for the Federal Government, emphasizes the importance of secure authentication protocols. It recommends using strong cryptographic algorithms and implementing MFA wherever feasible. Real-world examples abound: the 2018 Mirai botnet attack exploited default credentials on thousands of IoT devices, demonstrating the devastating consequences of this simple oversight.
Supply chain risks and firmware flaws
IoT security vulnerabilities often originate before a device is even deployed, during the manufacturing and supply chain process. Compromised components, insecure firmware, and backdoors intentionally inserted by malicious actors can all create significant risks. This makes it difficult for organizations to ensure the security of the devices they purchase.
Updating firmware on a massive scale presents another challenge. Many IoT devices lack automatic update mechanisms, leaving them vulnerable to known exploits for extended periods. Even when updates are available, users often fail to install them promptly, either due to lack of awareness or technical difficulties. This creates a window of opportunity for attackers.
CISA’s IoT Acquisition Guidance stresses the importance of vendor risk management. Organizations should carefully vet their IoT vendors, assess their security practices, and demand transparency into the supply chain. This includes understanding where components are sourced and how firmware is developed and tested. A checklist of security questions for vendors is a good starting point.
- Check if the vendor has a vulnerability disclosure program.
- What is the vendor’s process for patching security vulnerabilities?
- Does the vendor provide end-of-life support for devices?
Insecure network services
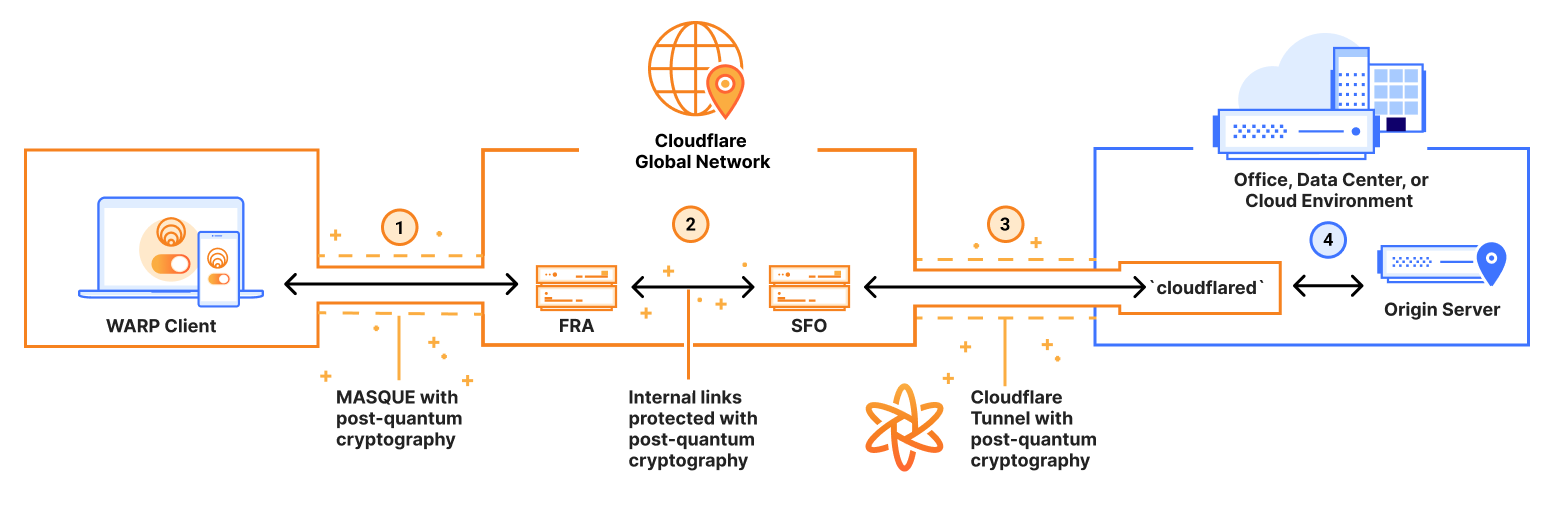
Many IoT devices rely on insecure network protocols like Telnet, FTP, and HTTP, which transmit data in plain text and lack robust security features. These protocols expose devices to man-in-the-middle attacks, data breaches, and other malicious activities. Using these protocols is akin to shouting sensitive information across a crowded room.
Secure alternatives like SSH, HTTPS, and TLS provide encryption and authentication, protecting data in transit. However, many IoT devices continue to use older, less secure protocols due to compatibility issues or cost constraints. The Universal Plug and Play (UPnP) protocol, while intended to simplify network configuration, has been repeatedly exploited to gain unauthorized access to IoT devices.
I'm not sure which protocols will be most common by 2026, but the rule is simple: use secure channels. Turn off services you don't use and scan for open ports regularly.
Data privacy and encryption failures
The proliferation of IoT devices raises significant data privacy concerns. These devices collect vast amounts of personal information – from location data and usage patterns to sensitive health information. The lack of adequate data protection measures can lead to unauthorized access, misuse, and even identity theft.
Many IoT devices fail to implement end-to-end encryption, meaning that data is often transmitted and stored in plain text. This makes it vulnerable to interception by attackers. Even when encryption is used, it may be weak or outdated, providing little real protection. The lack of transparency about data collection practices further exacerbates the problem.
Regulations like the General Data Protection Regulation (GDPR) in Europe and the California Consumer Privacy Act (CCPA) impose strict requirements on how personal data is collected, used, and protected. Organizations that fail to comply with these regulations face hefty fines. Implementing robust data encryption, minimizing data collection, and providing users with control over their data are essential steps towards ensuring data privacy.
Botnets and DDoS attacks
IoT devices are increasingly targeted by botnet operators due to their inherent vulnerabilities and widespread availability. These devices are often easy to compromise and can be recruited into botnets without the knowledge of their owners. The resulting botnets can be used to launch devastating Distributed Denial-of-Service (DDoS) attacks.
DDoS attacks overwhelm target servers with traffic, making them unavailable to legitimate users. Large-scale IoT botnets have the capacity to generate massive amounts of traffic, capable of taking down entire websites and online services. The 2016 Dyn DDoS attack, powered by the Mirai botnet, is a prime example of the destructive potential of IoT-based botnets.
Weak security measures – default passwords, unpatched vulnerabilities, and insecure network protocols – make IoT devices easy targets for botnet operators. Regularly patching devices, strengthening authentication, and implementing network segmentation can help mitigate the risk of botnet infections. Monitoring network traffic for suspicious activity is also crucial.
How to protect your network
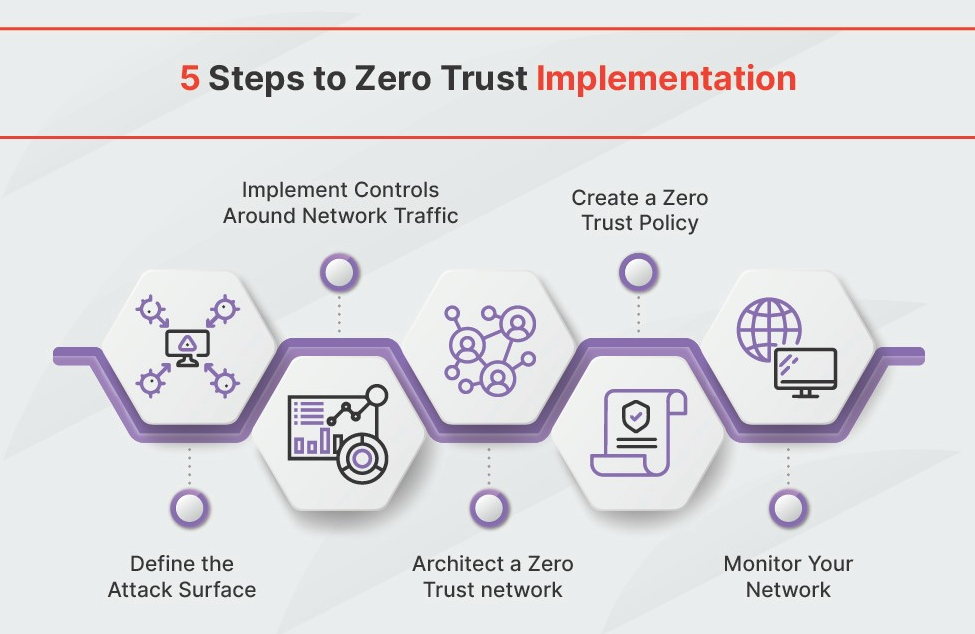
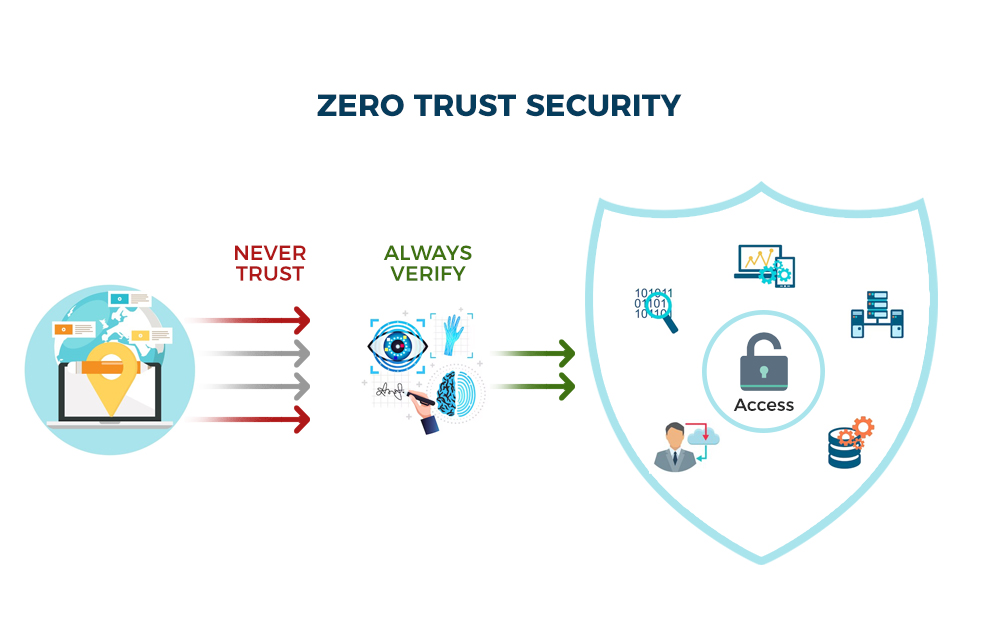
Addressing IoT security vulnerabilities requires a multi-layered approach. Secure device configuration is paramount: change default passwords, disable unnecessary services, and enable automatic updates. Network segmentation can isolate IoT devices from critical systems, limiting the impact of a potential breach. Intrusion detection systems can identify and block malicious traffic.
Vulnerability management is an ongoing process. Regularly scan for vulnerabilities, apply security patches promptly, and stay informed about emerging threats. Conducting regular security audits can help identify weaknesses in your IoT infrastructure. Employee training is also essential: educate users about the risks of IoT devices and best practices for security.
NIST and CISA provide valuable guidance on IoT security. NIST SP 800-213 offers a comprehensive framework for securing IoT devices. CISA’s IoT Acquisition Guidance provides recommendations for selecting and deploying secure IoT devices. A layered security approach, combined with proactive vulnerability management and employee awareness, is the best defense against IoT cyber threats.


No comments yet. Be the first to share your thoughts!