Understanding Penetration Testing
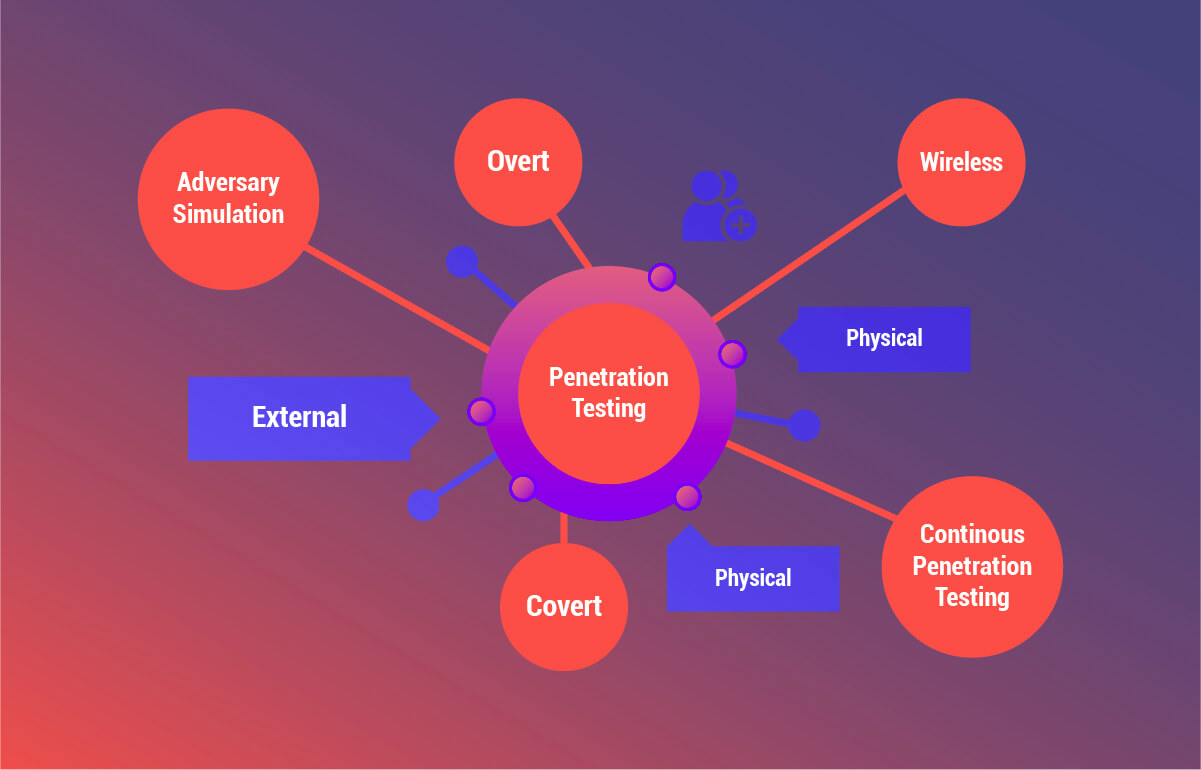
Let's dive into the world of penetration testing, a critical component of cybersecurity for businesses. In the simplest terms, penetration testing, often referred to as 'pen testing', is a simulated cyber attack against your computer system. The purpose? To check for exploitable vulnerabilities.

Think of it as a rigorous safety drill, where a professional ethical hacker like myself, Max Stealth, mimics the actions of a malicious hacker. This is done to identify weak spots in your network security solutions before the bad guys do.
Penetration testing for businesses is not a one-size-fits-all process. It's tailored to the specific needs of your organization, taking into account your network's size, the nature of the data it holds, and the potential risks it faces. It's a proactive approach to securing your digital world.
During a pen test, the tester uses a variety of techniques to probe your system's defenses. They might send phishing emails to see if employees reveal their passwords, or they could try to exploit known software vulnerabilities. The goal is to understand how an attacker could gain unauthorized access to your system and what they could do once inside.
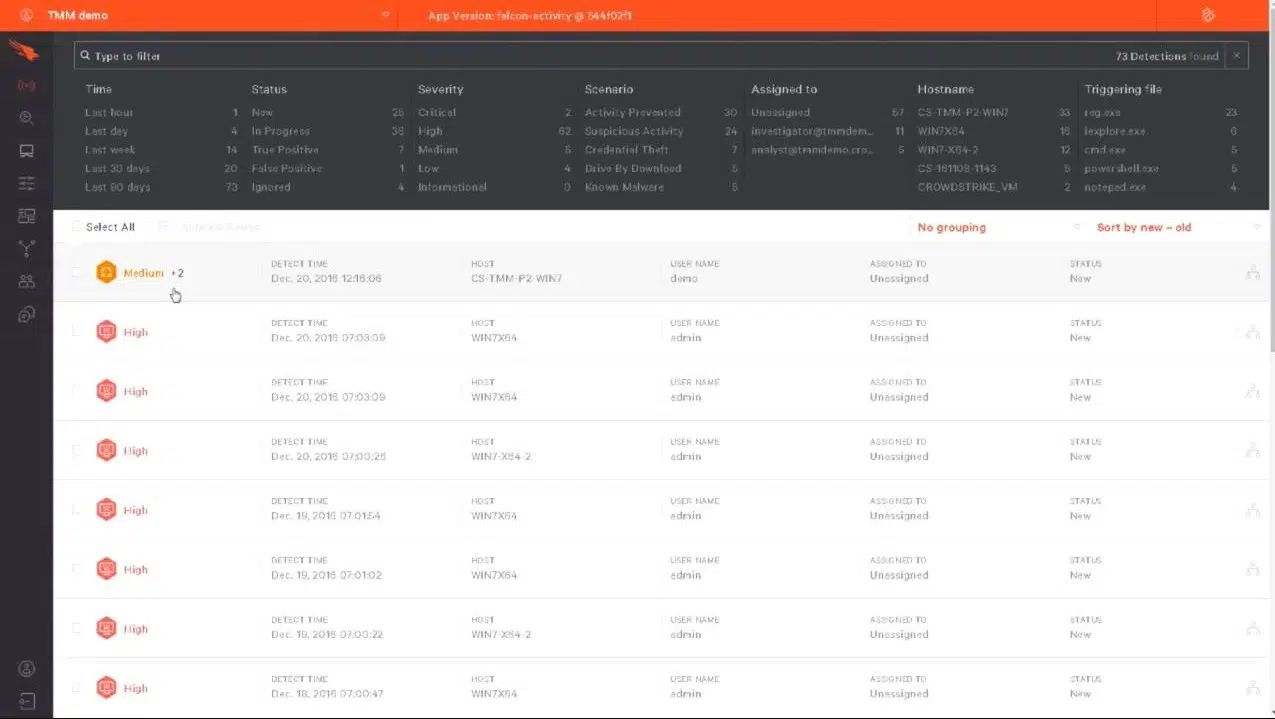
At the end of the pen test, you'll receive a detailed report outlining the vulnerabilities discovered, the severity of each, and recommendations for remediation. This valuable insight can guide your cybersecurity strategies and help you prioritize your resources effectively.
Remember, the difference between penetration testing and vulnerability scanning is that the former is a hands-on, in-depth process that not only identifies vulnerabilities but also explores their potential impact. It's a crucial step towards a robust cybersecurity posture.
Exploring Vulnerability Scanning
Now that we've delved into the realm of penetration testing, let's shift our focus to another critical aspect of cybersecurity for businesses: vulnerability scanning. While both penetration testing and vulnerability scanning aim to fortify your network security solutions, they do so in different ways.
Vulnerability scanning, as the name suggests, is a process that automatically scans your network and systems for known vulnerabilities. It's akin to a doctor's routine check-up, where they use various instruments to detect any signs of illness. In the digital world, these 'instruments' are specialized software tools that comb through your network, identifying any weaknesses that could be exploited by cybercriminals.

Unlike penetration testing, which is a hands-on, in-depth process, vulnerability scanning is largely automated. It's a broad, surface-level examination that can cover a wide range of systems quickly. This makes it an excellent tool for businesses that need to scan large networks regularly.
After a vulnerability scan, you'll receive a report listing all the vulnerabilities detected, ranked by severity. However, unlike a pen test report, it won't provide a detailed analysis of potential attack scenarios or the potential impact of each vulnerability. It's more of a 'symptom list' that tells you what's wrong, but not how it could affect you if left untreated.
So, while vulnerability scanning for businesses is an efficient way to identify known vulnerabilities, it doesn't replace the need for penetration testing. The two processes complement each other, providing a comprehensive approach to securing your digital world. Remember, in the realm of cybersecurity, knowledge is power. The more you know about your system's vulnerabilities, the better equipped you'll be to defend against cyber threats.
Key Differences Between Penetration Testing and Vulnerability Scanning
Now, let's delve into the key differences between penetration testing and vulnerability scanning. While both are crucial components of cybersecurity for businesses, they serve different purposes and offer unique insights into your network security solutions. Understanding these differences is essential for any business striving to secure its digital world.
Scope and Depth: Penetration testing is a deep-dive into your network's security. It's a hands-on, in-depth process where a professional ethical hacker, like a penetration tester, mimics the actions of a cybercriminal to identify vulnerabilities. On the other hand, vulnerability scanning is a broader, surface-level examination. It's an automated process that scans your network for known vulnerabilities, providing a 'symptom list' of potential weaknesses.
Approach: Penetration testing is a proactive approach to cybersecurity. It not only identifies vulnerabilities but also tests how they can be exploited, providing a detailed analysis of potential attack scenarios. Vulnerability scanning, however, is more reactive. It identifies known vulnerabilities but doesn't provide an in-depth analysis of how they could be exploited.

Frequency: Due to its automated nature, vulnerability scanning can be performed more frequently, making it ideal for businesses with large networks that need regular checks. Penetration testing, due to its intensive nature, is typically performed less frequently, often as part of a scheduled security audit or in response to a significant change in the network infrastructure.

Reporting: After a penetration test, you receive a detailed report outlining potential attack scenarios and the potential impact of each vulnerability. This helps businesses understand the real-world implications of their vulnerabilities. In contrast, a vulnerability scan report provides a list of detected vulnerabilities, ranked by severity, but doesn't offer a detailed analysis of potential impacts or attack scenarios.

In essence, while both penetration testing and vulnerability scanning are vital tools in the cybersecurity toolkit, they offer different perspectives and insights. They complement each other, providing a comprehensive approach to network security for businesses.
Benefits of Vulnerability Scanning for Businesses
Let's dive into the world of Vulnerability Scanning and how it can be a game-changer for businesses in securing their digital world. One of the most significant advantages of vulnerability scanning for businesses is its ability to provide a comprehensive view of potential weaknesses in a system. This proactive approach to cybersecurity for businesses helps in identifying and addressing vulnerabilities before they can be exploited by malicious hackers.

Vulnerability scanning for businesses is like a regular health check-up for your network security solutions. It ensures that your systems are running optimally and are free from potential threats. This process is automated and can be scheduled at regular intervals, ensuring continuous monitoring and timely detection of any security loopholes.
Another benefit of vulnerability scanning is its cost-effectiveness. Compared to the potential financial loss from a cyberattack, the investment in regular vulnerability scanning is minimal. It's a classic case of prevention being better, and cheaper, than cure.

Lastly, vulnerability scanning helps businesses comply with various industry regulations and standards. Regular scans can provide the necessary documentation and evidence of due diligence in maintaining a secure digital environment. This not only helps in avoiding penalties but also builds trust with clients and stakeholders.
In the detailed comparison of penetration testing and vulnerability scanning, it's clear that both have their unique benefits. However, the comprehensive, cost-effective, and regulatory compliant nature of vulnerability scanning makes it an essential tool in any business's cybersecurity arsenal.
Benefits of Penetration Testing for Businesses
Now that we've explored the difference between penetration testing and vulnerability scanning, let's focus on the benefits of penetration testing for businesses. As a proactive and in-depth approach to cybersecurity, penetration testing offers several unique advantages.
Uncovering Hidden Vulnerabilities: Penetration testing goes beyond identifying known vulnerabilities. It mimics the actions of cybercriminals, uncovering hidden vulnerabilities that automated systems might miss. This deep-dive approach provides a more realistic assessment of your network's security. 
Real-world Attack Scenarios: Penetration testing doesn't just identify vulnerabilities; it tests how they can be exploited. This offers businesses a clear picture of potential attack scenarios, helping them understand the real-world implications of their vulnerabilities. 
Proactive Security: By identifying and testing vulnerabilities before they can be exploited, penetration testing allows businesses to be proactive in their cybersecurity efforts. This can save businesses from costly breaches and reputational damage. 
Compliance and Trust: Many industries require regular penetration testing for compliance purposes. Even if it's not a requirement, conducting regular penetration tests can build trust with customers and stakeholders by demonstrating your commitment to cybersecurity. 
In summary, penetration testing for businesses offers a proactive, in-depth, and realistic approach to cybersecurity. It uncovers hidden vulnerabilities, provides real-world attack scenarios, enhances proactive security measures, and builds trust through compliance. It's an essential tool for any business looking to secure its digital world.
Choosing the Right Approach for Your Business
When it comes to fortifying your digital fortress, the choice between penetration testing and vulnerability scanning can seem like a daunting task. Each approach has its unique strengths, and the decision should be based on your business's specific needs and objectives.
Penetration testing is akin to a full-scale military exercise on your defenses. It's an aggressive approach that simulates real-world attacks to test your network's resilience. If your business handles sensitive data or operates in a high-risk industry, penetration testing can provide valuable insights into your security posture. It's a hands-on, comprehensive method that can expose even the most hidden vulnerabilities. However, it requires more resources and expertise to execute effectively.
On the other hand, vulnerability scanning is like a routine patrol of your digital perimeter. It's a proactive and cost-effective way to identify potential weak spots in your defenses. If your business needs to maintain compliance with industry regulations or if you're looking for a more automated, continuous monitoring solution, vulnerability scanning might be the better choice. It's less intensive than penetration testing, but it can still provide a solid foundation for your cybersecurity strategy.
Ultimately, the choice between penetration testing and vulnerability scanning isn't a binary one. Many businesses opt for a combination of both, using vulnerability scanning for regular check-ups and penetration testing for in-depth audits. This balanced approach can provide a robust, multi-layered defense against the ever-evolving threats in the digital world.
Remember, the goal isn't to choose the 'best' method, but rather the right one for your business. By understanding the difference between penetration testing and vulnerability scanning, you can make an informed decision that aligns with your business's needs and helps secure your digital world.

Best Practices for Implementing Penetration Testing and Vulnerability Scanning
As we delve into the best practices for implementing penetration testing and vulnerability scanning, it's crucial to remember that these methods are not standalone solutions, but integral parts of a comprehensive cybersecurity strategy. Let's explore some key steps to ensure effective execution of these network security solutions.
1. Define Your Objectives: Before initiating any cybersecurity measure, it's essential to clearly outline your objectives. What are you hoping to achieve with penetration testing or vulnerability scanning? Is it compliance, risk assessment, or identifying potential vulnerabilities? Having clear objectives will guide the process and ensure that it aligns with your business's needs.
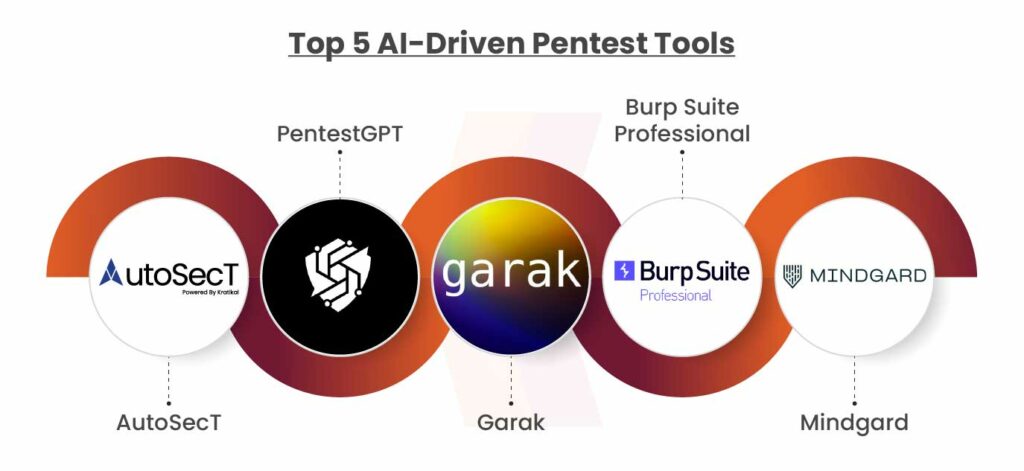
2. Choose the Right Tools: The digital world is teeming with a plethora of tools for penetration testing and vulnerability scanning. Your choice should be based on your business's specific requirements. For instance, if you're a small business with limited resources, you might opt for automated vulnerability scanning tools. Conversely, larger enterprises handling sensitive data might require more sophisticated penetration testing tools.
3. Regularly Schedule Tests and Scans: Cyber threats are not static; they evolve constantly. Therefore, your cybersecurity measures should be dynamic as well. Regularly schedule penetration tests and vulnerability scans to stay ahead of potential threats. This not only helps in identifying new vulnerabilities but also in assessing the effectiveness of your current security measures.
4. Analyze and Act: The value of penetration testing and vulnerability scanning lies not just in identifying weaknesses, but also in taking corrective action. Once vulnerabilities are identified, prioritize them based on their potential impact and act swiftly to address them. Remember, a vulnerability left unaddressed is a disaster waiting to happen.
5. Foster a Culture of Cybersecurity: Lastly, but most importantly, foster a culture of cybersecurity within your organization. Encourage employees to take an active role in maintaining security. After all, the most sophisticated security systems can be compromised by simple human error.
In the end, the key to securing your digital world lies in a balanced, proactive approach to cybersecurity. By effectively implementing penetration testing and vulnerability scanning, you can fortify your defenses and stay one step ahead of cyber threats.



No comments yet. Be the first to share your thoughts!