The shift toward automated testing
Security teams are overwhelmed. Between cloud sprawl and the constant addition of IoT devices, there are too many targets and not enough people to test them. Manual pentesting is thorough, but it's too slow and expensive to keep up with weekly software releases.
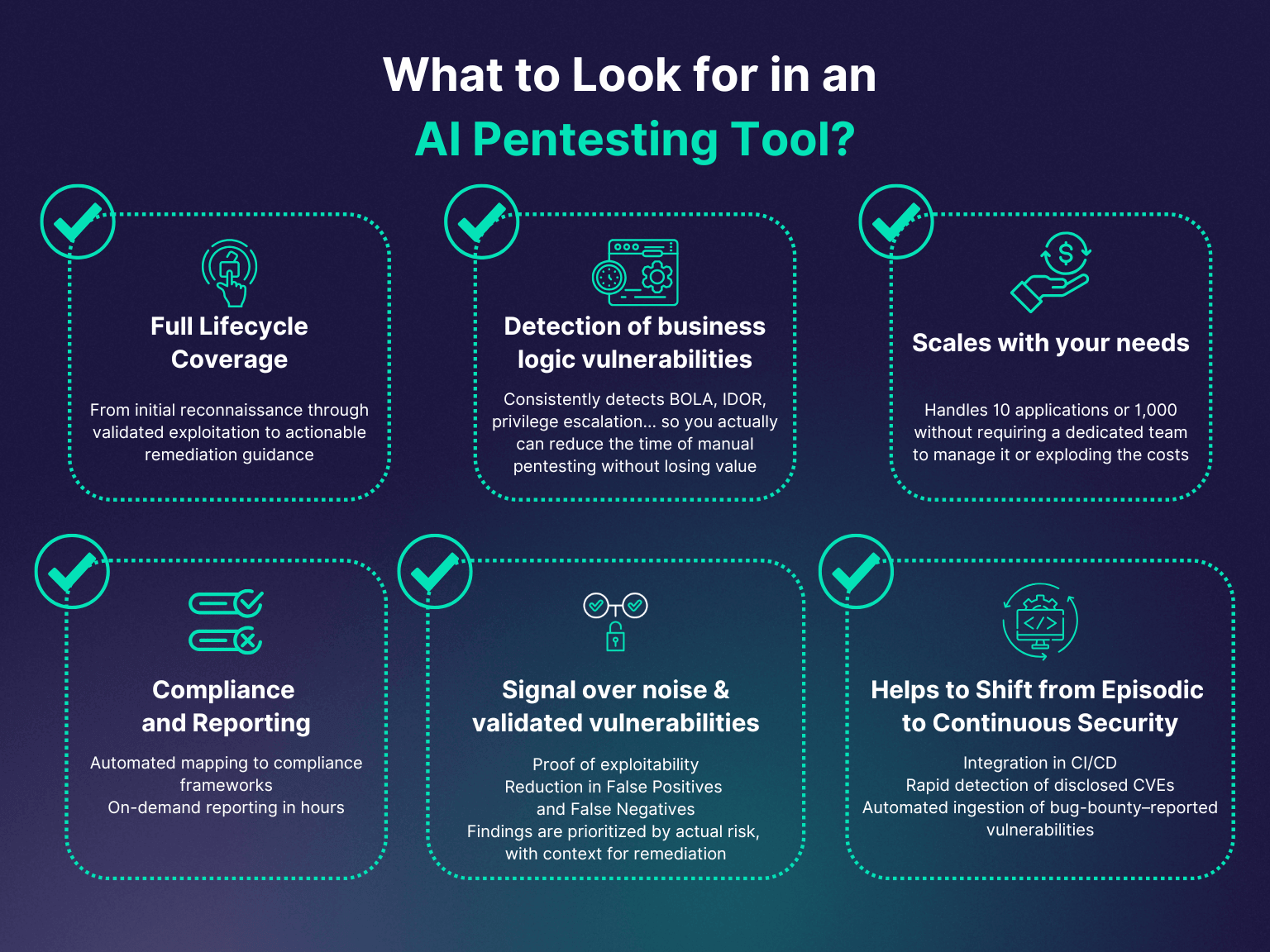
For years, pentesters have relied on a combination of established tools and their own expertise to identify vulnerabilities. But this approach has limitations. It's difficult to scale, can be prone to human error, and often struggles to keep up with the speed of modern software development. AI-powered penetration testing aims to address these challenges by automating repetitive tasks, improving accuracy, and accelerating the testing process.
By 2026, we anticipate AI will be a mainstream component of most serious security programs. The tools discussed here aren’t meant to replace skilled pentesters, but to amplify their abilities and allow them to focus on the most complex and critical areas. We're seeing a shift from finding vulnerabilities to understanding and exploiting them, and AI is becoming essential to that evolution.
Seven tools to watch
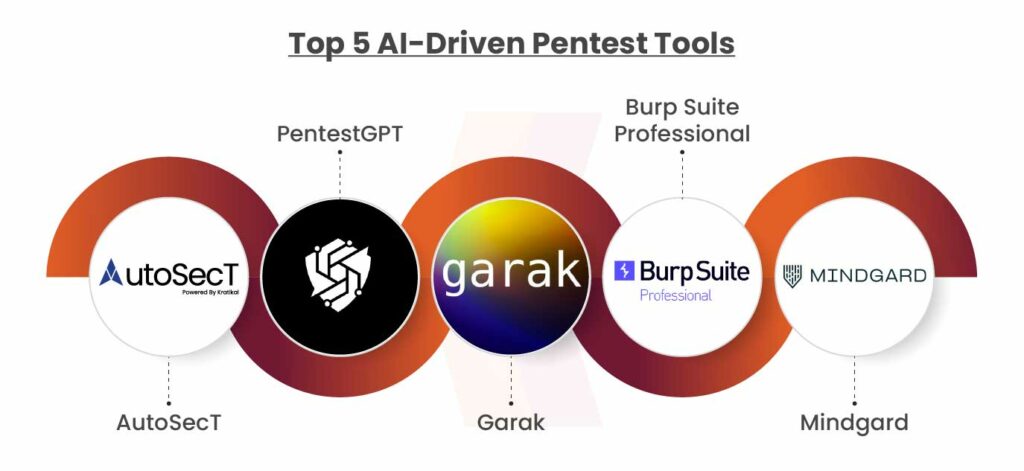
The AI-powered penetration testing market is rapidly evolving. Here are seven tools that stand out as potential game-changers by 2026, based on current trends and capabilities. Keep in mind that the specifics of these tools will likely change, but the underlying principles will remain relevant.
1. StackHawk: StackHawk focuses on developer-centric application security testing. It integrates directly into CI/CD pipelines and uses AI to prioritize vulnerabilities based on their impact and exploitability. It's particularly useful for identifying vulnerabilities in modern web applications and APIs. StackHawk's strength is its ability to find issues early in the development lifecycle.
2. Detectify: Detectify leverages crowdsourced security research and machine learning to identify vulnerabilities in web applications. Their platform continuously scans for new vulnerabilities and automatically updates its detection capabilities. Detectify excels at finding known vulnerabilities quickly, but its AI is increasingly focused on identifying zero-day exploits.
3. Intrigue: Intrigue specializes in external attack surface management (EASM) and uses AI to discover and assess internet-exposed assets. It identifies vulnerabilities across an organization’s entire digital footprint, including websites, cloud services, and email domains. Intrigue is valuable for understanding an organization’s overall risk posture.
4. Probelys: Probelys is an automated penetration testing tool for web applications. It uses a combination of static and dynamic analysis, along with machine learning, to identify a wide range of vulnerabilities. Probelys can be customized to simulate different attacker profiles and test specific attack scenarios.
5. Pentest-Tools.com (PTX): PTX is a suite of tools that includes AI-powered features for vulnerability scanning, exploitation, and reporting. While not solely AI-driven, the platform is integrating AI to automate tasks and improve the accuracy of its findings. PTX is a good option for organizations looking for a comprehensive penetration testing solution.
6. Latch: Latch is a newer platform that emphasizes AI-driven vulnerability discovery and exploitation. They focus on automating the entire penetration testing process, from reconnaissance to reporting. Latch’s approach is particularly promising for organizations that lack in-house penetration testing expertise. They are also working on integrating with open-source AI agents.
7. Immunefi: While primarily a bug bounty platform, Immunefi is increasingly utilizing AI to analyze bug reports and prioritize vulnerabilities. Their AI algorithms can help identify critical vulnerabilities more quickly and efficiently. This is a good example of how AI is being applied to post-exploitation security assessment.
Cobalt strike and automation
Cobalt Strike is a well-established red teaming tool used by penetration testers and threat actors alike. It’s known for its powerful command and control capabilities and its ability to simulate realistic attacks. While traditionally a manual tool, Cobalt Strike is seeing increased integration of AI to automate key tasks.
Currently, some integrations allow for automated beacon obfuscation, making it harder for security defenses to detect malicious activity. By 2026, we can expect to see further advancements in this area, including AI-powered lateral movement techniques and automated report generation. The goal is to allow red teams to move faster and more effectively while minimizing the risk of detection.
We're seeing developers use models to analyze traffic and pick targets. These tools can change tactics based on how a defender reacts. Of course, making Cobalt Strike more efficient also makes it a more dangerous tool for actual attackers.
Moving from scanning to exploitation
Models are moving into exploitation. They can now generate payloads and try to bypass firewalls without human input. I watched a demo from BePractical where an open-source agent handled a basic sequence from recon to shell access.
AI algorithms can analyze vulnerability data and automatically generate exploits tailored to specific targets. They can also be used to bypass security controls like firewalls and intrusion detection systems. This is particularly concerning because it lowers the barrier to entry for attackers and makes it easier to launch sophisticated attacks.
However, the use of AI in exploitation also raises significant ethical considerations. It's crucial to develop AI responsibly and ensure that it's not used for malicious purposes. This requires careful consideration of the potential risks and benefits, as well as the implementation of appropriate safeguards. There's a real need for clear guidelines and regulations surrounding the use of AI in cybersecurity.
- Build security controls that can spot automated bot behavior.
- Invest in AI-powered defenses to counter AI-powered attacks.
- Promote responsible AI development and ethical hacking practices.
Reporting and fixing bugs
Traditionally, penetration testing reports have been lengthy, technical documents that are difficult for non-technical audiences to understand. AI is changing this by automating the report generation process and improving the clarity and conciseness of the findings. AI can analyze vulnerability data and automatically generate reports that highlight the most critical risks.
AI can also prioritize vulnerabilities based on their risk score, taking into account factors like exploitability, impact, and business criticality. This helps organizations focus their remediation efforts on the most important issues first. Furthermore, AI can suggest specific remediation steps, such as patching vulnerabilities or implementing security controls.
Some AI-powered tools can even automate some patching processes, reducing the time and effort required to fix vulnerabilities. This is particularly valuable for organizations with limited security resources. The ability to generate clear, concise reports and automate remediation steps will make penetration testing more accessible and effective for a wider range of organizations.
Featured Products
Automated security scanning techniques · DevSecOps integration · Practical testing methodologies
This book provides practical techniques for automating security scanning and testing, crucial for efficient DevSecOps pipelines.
AI-driven threat detection · Automated incident response · Network-wide visibility
Cynet 360 leverages AI to provide comprehensive extended detection and response, automating the identification and neutralization of cyber threats.

Self-learning AI · Behavioral threat analysis · Real-time threat detection
The Darktrace Enterprise Immune System uses AI to learn and adapt to an organization's unique digital environment, detecting novel and sophisticated threats.

Reads 1D and 2D barcodes · Wired USB connection · Automatic scanning
While not an AI penetration testing tool, this scanner is essential for inventory management and data entry in warehouses and retail environments, streamlining operations.

Exploitation framework · Penetration testing techniques · Vulnerability research
Metasploit is a foundational tool for penetration testers, offering a robust framework for developing and executing exploits against vulnerabilities.
As an Amazon Associate I earn from qualifying purchases. Prices may vary.



No comments yet. Be the first to share your thoughts!