The Rise of AI in Penetration Testing
Penetration testing, the practice of proactively identifying vulnerabilities in systems and networks, is changing. For years, it was a largely manual process, relying on the skill and experience of security professionals. But the sheer volume of attacks and the increasing complexity of modern infrastructure are straining traditional methods. Artificial intelligence is now being used to address these challenges.
Manual pen testing has limitations. It's time-consuming, expensive, and often struggles to keep pace with the speed of development and deployment. Humans can miss things, especially in large and complex environments. Attackers' tactics are constantly evolving; staying ahead requires adaptability, something AI excels at.
AI can automate many aspects of pen testing, increasing speed and scale. It can also uncover novel vulnerabilities that human testers might miss. The growing sophistication of cyberattacks—like ransomware, supply chain attacks, and targeted phishing—demands a more proactive and intelligent approach to security. AI isn't about replacing pen testers, but empowering them.
Real-world events drive this change. In 2023 alone, reported data breaches increased by 15% according to the Identity Theft Resource Center, costing businesses billions. This shows the critical need for robust security measures, and AI-powered pen testing is emerging as a component of a more resilient cybersecurity posture. This is happening now.
Core AI Techniques Used in Pen Testing
AI-powered pen testing uses several machine learning and artificial intelligence techniques. It's about applying the right techniques to specific security challenges. Natural Language Processing (NLP) analyzes source code, configuration files, and security documentation to identify potential weaknesses.
Machine Learning (ML) is used for anomaly detection. By learning a system's 'normal' behavior, ML algorithms identify deviations that might indicate an attack or a vulnerability. This is useful for detecting zero-day exploits—attacks that exploit previously unknown vulnerabilities. It's about finding what shouldn't be happening.
Reinforcement Learning is interesting in fuzzing. Fuzzing involves sending random inputs to a system to try and trigger crashes or unexpected behavior. Reinforcement Learning allows the fuzzer to learn which inputs are most likely to be effective, making the process more efficient than traditional fuzzing. It's an AI actively trying to break things and learning from its mistakes.
Genetic Algorithms are used to optimize attack paths. These algorithms mimic natural selection, evolving potential attack strategies over time to find the most effective way to compromise a system. They explore a vast search space of possible attacks, identifying the most promising avenues. The result is a more thorough and intelligent assessment of a system’s security.
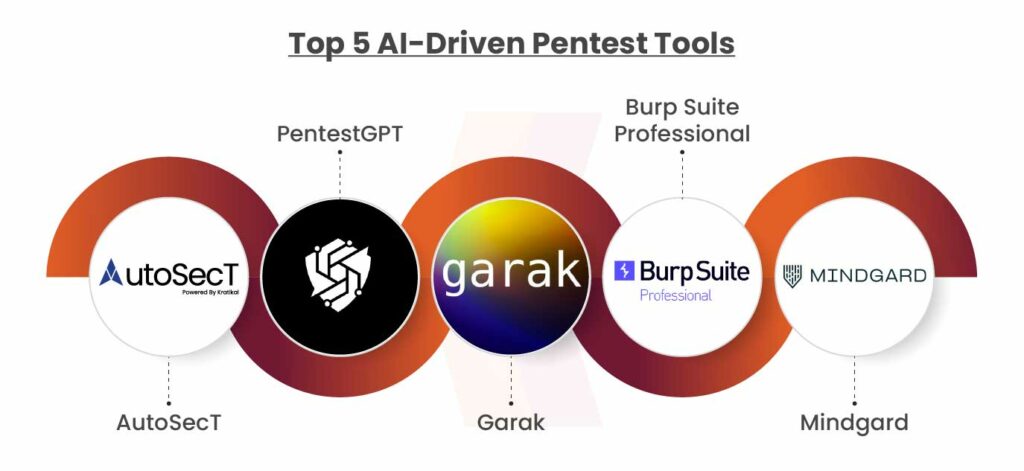
Top 10 AI-Powered Pen Testing Tools (2026)
The market for AI-powered penetration testing tools is rapidly evolving. Here are ten leading solutions as of late 2026, each offering a unique approach to automated security testing. The features and capabilities of these tools are constantly being updated, so this is a snapshot in time.
1. Bright Security: Bright Security focuses on developers. It integrates directly into the CI/CD pipeline, providing real-time vulnerability feedback. Its AI engine prioritizes vulnerabilities based on exploitability and potential impact. Target users include development teams and security champions.
2. Detectify: Detectify specializes in web application security. It uses a crowdsourced vulnerability database and AI-powered scanning to identify a wide range of web vulnerabilities, including XSS, SQL injection, and CSRF. It’s a good choice for organizations with a strong web presence and is popular with bug bounty hunters.
3. Probely: Probely focuses on API security testing. APIs are increasingly targeted by attackers, and Probely provides a comprehensive solution for identifying API vulnerabilities. It uses AI to learn expected API behavior and detect anomalies. This tool is geared towards DevOps and security teams.
4. Invicti (formerly Netsparker): Invicti is a web application security scanner that has incorporated AI to improve its accuracy and efficiency. It uses Proof-Based Scanning technology, which automatically verifies vulnerabilities to reduce false positives. Invicti is favored by enterprise-level organizations.
5. Pentera: Pentera automates the entire penetration testing process, from reconnaissance to exploitation. It uses AI to mimic the behavior of real-world attackers, providing a realistic assessment of an organization’s security posture. This is an option for organizations that want a fully automated solution.
6. RunReveal: RunReveal is a cloud-native pen testing platform that uses AI to identify and prioritize vulnerabilities. It has a unique "attack path mapping’ feature, which visualizes the potential routes an attacker could take to compromise a system. It"s designed for security teams of all sizes.
7. Stealthbits Technologies: Stealthbits focuses on data security and access governance. Their AI-powered tools help organizations identify and remediate risks associated with sensitive data. They are strong in identifying misconfigurations and excessive permissions. This caters to compliance-focused organizations.
8. Synergist: Synergist combines vulnerability scanning with penetration testing. It uses AI to automate many manual tasks in pen testing, such as vulnerability validation and report generation. It targets security teams looking to streamline their workflow.
9. Horizon3.ai: Horizon3.ai specializes in breach and attack simulation (BAS). It uses AI to simulate real-world attacks, helping organizations identify and prioritize security weaknesses. This allows organizations to proactively test their defenses. It's ideal for larger enterprises.
10. Lupus Security: Lupus Security offers a distributed penetration testing platform. It allows organizations to launch large-scale pen tests from multiple locations, simulating a global attack. AI is used to optimize the scanning process and prioritize vulnerabilities. It suits organizations with complex, geographically distributed networks.
Essential Hardware for AI-Powered Penetration Testing

Multi-factor authentication (MFA) security key · Connects via USB-C or NFC · FIDO Certified for strong online account protection
This hardware solution complements AI-driven penetration testing by providing secure access to systems and accounts.

Extends WiFi range up to 1750Mbps · Dual-band operation for optimal performance · PCMag Editor's Choice for reliable internet boosting
This hardware solution complements AI-driven penetration testing by providing robust network monitoring capabilities.

Quad-core 64-bit processor · Integrated WiFi and Bluetooth connectivity · Compact and versatile computing platform
This hardware solution complements AI-driven penetration testing by providing a versatile platform for custom security tool development.

Comprehensive starter kit for Raspberry Pi · Includes 223 components and 128 projects · Detailed tutorials in Python, C, Java, Scratch, and Processing
This hardware solution complements AI-driven penetration testing by providing a versatile platform for custom security tool development.
As an Amazon Associate I earn from qualifying purchases. Prices may vary.
Decoding Automation: What Can AI Truly Automate?
Have a realistic understanding of what AI can and cannot do in penetration testing. The hype often outpaces reality. AI excels at automating repetitive tasks, such as vulnerability scanning, fuzzing, and identifying common misconfigurations. It can also analyze large volumes of data to detect anomalies and prioritize potential threats. But it’s not a magic bullet.
Tasks that still require significant human expertise include complex exploit development, strategic thinking, and understanding the business context of security vulnerabilities. AI can suggest potential exploits, but it often lacks the creativity and adaptability needed to successfully exploit complex systems. Similarly, AI can identify vulnerabilities, but it can't always determine their true impact on the business.
One common misconception is that AI can fully automate the entire penetration testing process. While AI can automate many steps, it still requires human oversight to validate findings, interpret results, and develop effective remediation strategies. A human pen tester is needed to provide context and make informed decisions. Think of AI as a powerful assistant, not a replacement.
The key is to focus on using AI to augment human capabilities, not to replace them. By automating repetitive tasks, AI frees up pen testers to focus on more challenging and strategic work. This leads to more thorough and effective security assessments.
AI Pen Testing and the Skill Gap
The rise of AI-powered pen testing tools is undoubtedly impacting the demand for penetration testing skills. While some fear that AI will lead to widespread job displacement, the reality is more nuanced. The role of the pen tester is evolving, not disappearing. The demand for skilled security professionals is still high, but the required skillset is changing.
AI is automating many of the more basic tasks traditionally performed by pen testers, such as vulnerability scanning and report generation. This means that junior-level pen testers may need to develop new skills to remain competitive. The focus is shifting towards skills like data analysis, threat intelligence, and incident response.
What's becoming increasingly important is the ability to interpret AI-generated results and validate findings. Pen testers need to be able to understand why an AI tool identified a particular vulnerability and assess its true impact on the business. This requires a strong understanding of security principles and a critical thinking mindset.
There’s a growing need for security professionals who can bridge the gap between AI and human expertise. These individuals will be responsible for managing AI-powered pen testing tools, interpreting their results, and developing effective remediation strategies. It's about becoming an 'AI-augmented' pen tester, leveraging the power of AI to enhance your capabilities.
Integrating AI Tools into Existing Security Workflows
Successfully integrating AI-powered pen testing tools into existing security programs requires careful planning and execution. It’s not enough to simply purchase a tool and expect it to solve all your security problems. Compatibility with existing security infrastructure is crucial. This includes integration with Security Information and Event Management (SIEM) systems, vulnerability management platforms, and DevOps pipelines.
Data integration is a major challenge. AI-powered pen testing tools generate a lot of data, and it’s important to be able to correlate this data with other security data sources. This requires a robust data integration strategy and the use of standardized data formats. Without this, the value of the AI-generated insights is diminished.
Consider your organization's security maturity level. Organizations with mature security programs are better equipped to integrate AI-powered pen testing tools than those with less mature programs. Start small and gradually expand your use of AI as your security capabilities mature. Pilot projects can be a good way to test the waters.
Different organizational structures will require different integration approaches. A centralized security team may have more control over the integration process than a decentralized one. It’s important to involve all stakeholders in the planning process to ensure buy-in and successful implementation.
Future Trends: Beyond 2026
Looking beyond 2026, the future of AI in penetration testing is likely to be shaped by several emerging technologies. Generative AI, for example, has the potential to automate the creation of exploits, making it easier for attackers (and defenders) to exploit vulnerabilities. This will require a new generation of security tools that can detect and mitigate AI-generated attacks.
AI-powered deception technology is another promising area. This involves creating realistic decoys and traps to lure attackers and gather intelligence about their tactics. AI can be used to dynamically adjust these decoys to make them more effective. The goal is to turn the tables on attackers and gain the upper hand.
However, the rise of AI in security also presents new challenges. Adversarial AI – the use of AI to evade detection – is a growing concern. Attackers are already using AI to develop more sophisticated malware and phishing attacks. Defenders will need to stay one step ahead by developing AI-powered defenses that can detect and respond to these threats.
Ethical considerations are also becoming increasingly important. The use of AI for offensive security purposes raises questions about responsible disclosure and the potential for unintended consequences. It's essential to develop ethical guidelines and best practices for the use of AI in penetration testing.



No comments yet. Be the first to share your thoughts!