The quantum threat is closer than it looks
Quantum computers are moving from theory to engineering. While they aren't breaking codes yet, they will eventually crack the math protecting our bank accounts and private messages. We have a deadline because the transition to new security takes years, not weeks.
The core of this threat lies in Shor’s algorithm, a quantum algorithm capable of efficiently factoring large numbers and solving the discrete logarithm problem. These are the mathematical foundations of widely used public-key cryptography systems like RSA and Elliptic Curve Cryptography (ECC). A sufficiently powerful quantum computer running Shor’s algorithm could render these systems obsolete, exposing sensitive data to decryption.
We’re talking about the security of everything from online banking and e-commerce to government communications and critical infrastructure. The concern isn't just that these algorithms could be broken, but that an adversary could harvest encrypted data today and decrypt it later when quantum computers become powerful enough. That’s why the year 2026 is so important. The National Institute of Standards and Technology (NIST) is aiming to finalize post-quantum cryptography standards by then, giving organizations time to prepare for the transition.
Why RSA and ECC are vulnerable
RSA (Rivest–Shamir–Adleman) and ECC (Elliptic Curve Cryptography) are the workhorses of modern public-key cryptography. RSA relies on the difficulty of factoring large numbers, while ECC relies on the difficulty of solving the elliptic curve discrete logarithm problem. These algorithms are used to establish secure connections, encrypt data, and verify digital signatures.
You encounter these algorithms constantly. HTTPS, the protocol securing websites, relies on RSA or ECC to establish secure connections. Virtual Private Networks (VPNs) use them to encrypt your internet traffic. Secure Shell (SSH) uses them for secure remote access to servers. Digital signatures, used to verify the authenticity of software and documents, also depend on these algorithms.
Quantum computers, through Shor’s algorithm, directly attack the mathematical problems underpinning RSA and ECC. This means a quantum computer could break the encryption protecting your web browsing sessions, decrypt your VPN traffic, and forge digital signatures. While symmetric encryption algorithms like AES (Advanced Encryption Standard) are considered more resistant to quantum attacks, they still need to be integrated with quantum-resistant key exchange mechanisms to provide full security.
NIST’s Post-Quantum Cryptography Standardization
Recognizing the looming threat, NIST launched a Post-Quantum Cryptography (PQC) standardization process in 2016. The goal was to identify and standardize cryptographic algorithms resistant to attacks from both classical and quantum computers. This has been a multi-round process involving extensive analysis and testing of candidate algorithms.
In July 2022, NIST announced the first group of algorithms selected for standardization. These include CRYSTALS-Kyber for key encapsulation – essentially, securely exchanging encryption keys – and CRYSTALS-Dilithium, FALCON, and SPHINCS+ for digital signatures. The selection wasn’t about finding a single "silver bullet" but rather establishing a portfolio of algorithms with different strengths and weaknesses.
The new standards rely on different math problems, like lattice-based cryptography, which is the current favorite because it balances speed with security. NIST is still testing other methods like code-based and multivariate systems to ensure we have backups if one method fails.
- CRYSTALS-Kyber handles the secure exchange of encryption keys.
- CRYSTALS-Dilithium: Digital signature algorithm.
- FALCON: Digital signature algorithm.
- SPHINCS+: Digital signature algorithm.
NIST Post-Quantum Cryptography (PQC) Algorithm Comparison
| Algorithm | Algorithm Type | Key Size | Performance Impact | Known Considerations |
|---|---|---|---|---|
| CRYSTALS-Kyber | Key-Encapsulation Mechanism (KEM) | Moderate | Generally efficient; good for constrained environments | Relatively new; long-term security analysis ongoing. |
| CRYSTALS-Dilithium | Digital Signature | Moderate | Good performance for signing and verification | Security relies on the hardness of Module-LWE and Module-SIS problems. |
| Falcon | Digital Signature | Small | Fast signature generation, larger signature size | Security based on the Shortest Integer Solution (SIS) problem on lattices. |
| SPHINCS+ | Digital Signature | Large | Stateless signature scheme; resilient to side-channel attacks | Signatures are significantly larger than other schemes; slower signing. |
| Rainbow | Digital Signature | Moderate | Based on multivariate quadratic equations | Concerns about potential structural weaknesses; requires careful implementation. |
| Classic McEliece | Key-Encapsulation Mechanism (KEM) | Very Large | High computational cost; large key sizes | Long-standing security; considered conservative but less practical for some applications. |
Qualitative comparison based on the article research brief. Confirm current product details in the official docs before making implementation choices.
How lattice-based math works
Let’s consider two of the leading candidates: CRYSTALS-Kyber and CRYSTALS-Dilithium. CRYSTALS-Kyber is a lattice-based key encapsulation mechanism. It works by representing cryptographic keys as points in a high-dimensional lattice. The security relies on the difficulty of finding the closest point in the lattice to a given vector – a problem considered hard even for quantum computers.
CRYSTALS-Dilithium is a lattice-based digital signature algorithm. It also leverages the hardness of lattice problems, but in a different way. It allows users to digitally sign messages in a way that’s resistant to forgery, even by attackers with quantum computers. The algorithm relies on carefully constructed mathematical structures that make it incredibly difficult to break.
These algorithms aren't simply replacing existing cryptography; they’re built on fundamentally different mathematical principles. They offer a path towards long-term security in a post-quantum world, but they also come with their own trade-offs in terms of performance and implementation complexity. They tend to have larger key and signature sizes compared to traditional algorithms, which can impact bandwidth and storage requirements.
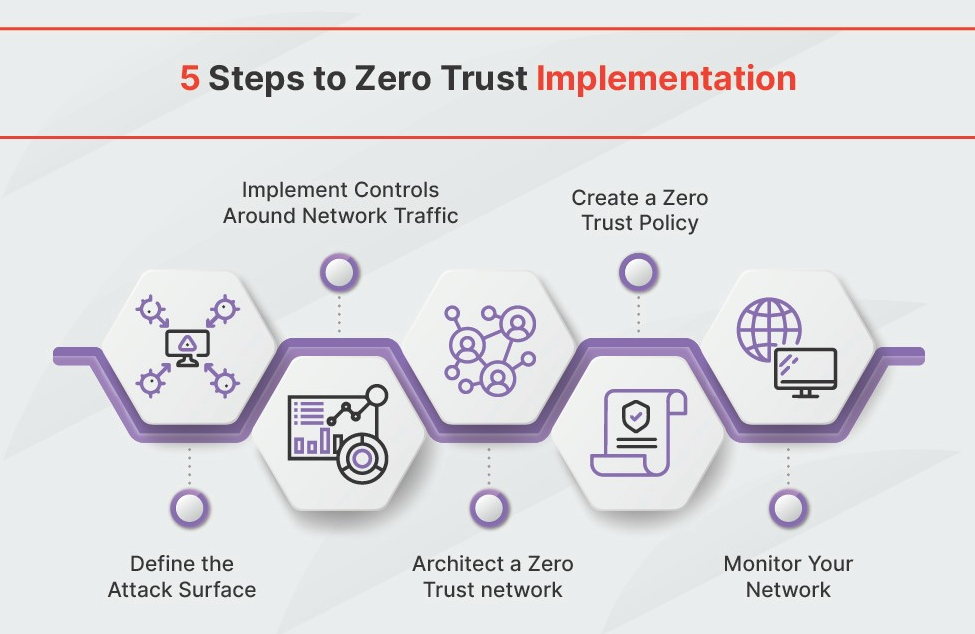
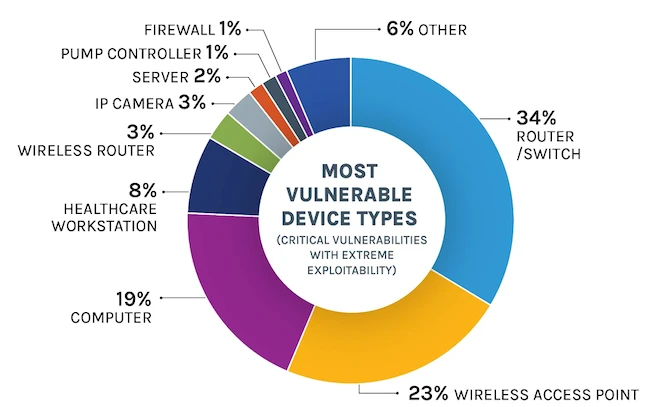
How to audit your network
Preparing for post-quantum cryptography is a multi-year undertaking. The first step is a comprehensive asset inventory. Identify all systems, applications, and data that rely on vulnerable cryptographic algorithms (RSA, ECC, etc.). This includes servers, network devices, databases, and any software using encryption.
Next, conduct a risk assessment to prioritize your efforts. Which systems are most critical? What data is most sensitive? Which systems are most exposed to potential attacks? This will help you focus your resources on the areas that need the most immediate attention. Don’t underestimate the complexity of this process; it requires deep understanding of your infrastructure.
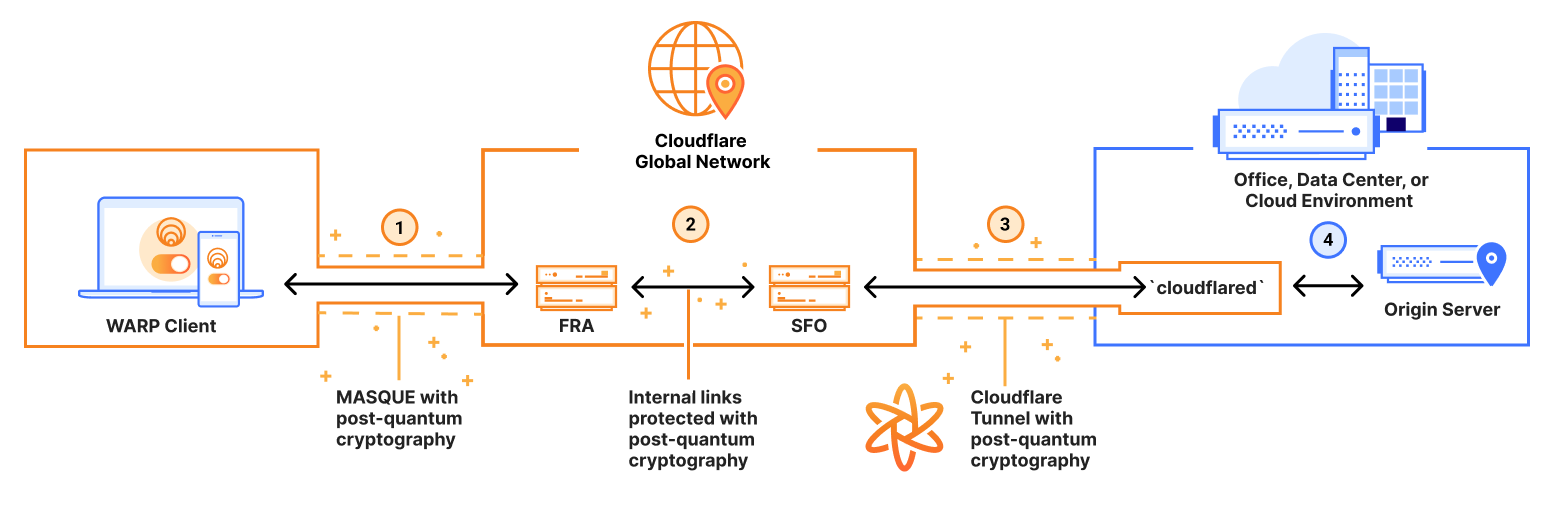
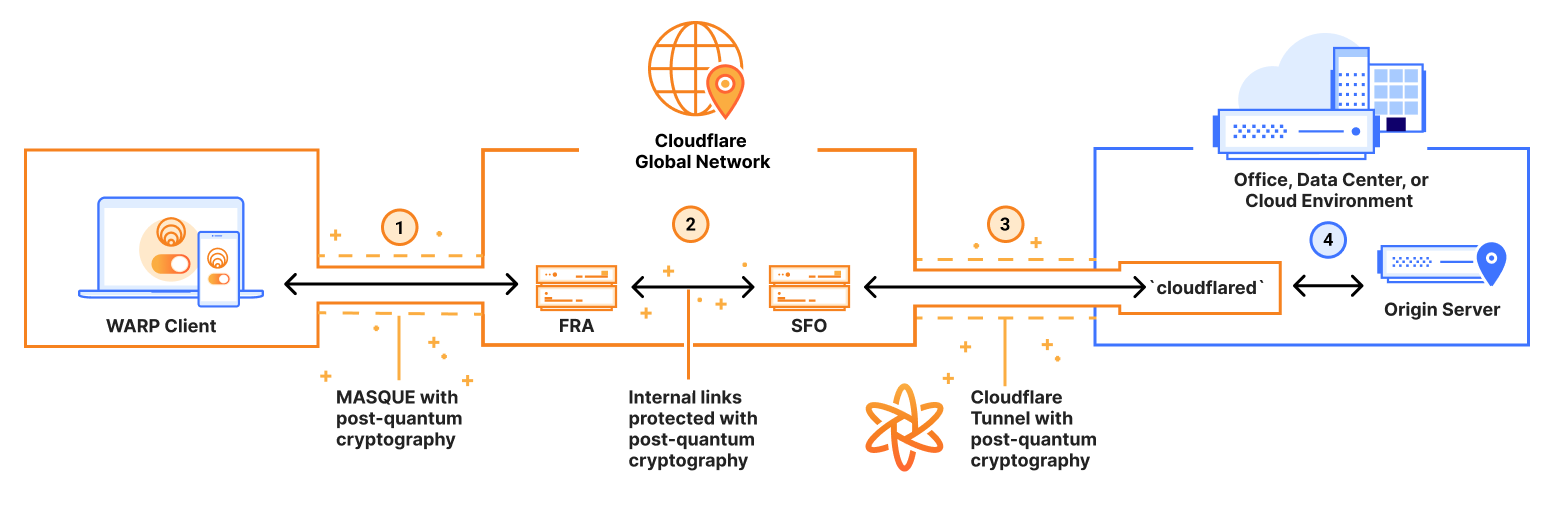
Planning for algorithm migration is crucial. This involves identifying and testing PQC implementations, developing deployment strategies, and ensuring compatibility with existing systems. A hybrid approach – combining classical and post-quantum algorithms – is often the most practical starting point. This allows you to maintain compatibility with legacy systems while gradually introducing PQC.
Testing is paramount. You need to validate that PQC implementations work correctly and don’t introduce new vulnerabilities. This includes functional testing, performance testing, and security audits. Consider engaging with cybersecurity experts to help with this process.
- Conduct a comprehensive asset inventory.
- Perform a risk assessment.
- Plan for algorithm migration.
- Use a hybrid approach that runs classical and quantum-resistant math side-by-side.
- Thoroughly test PQC implementations.
Tools and Libraries for PQC Implementation
Several open-source tools and libraries are available to help with PQC implementation. OpenSSL, a widely used cryptography library, is actively adding support for PQC algorithms. PQClean is a project providing clean, portable implementations of PQC algorithms in C. It’s designed to make it easier to integrate PQC into existing systems.
liboqs is another valuable resource, offering a collection of PQC algorithms and tools. These libraries are constantly evolving as the PQC landscape matures. It’s essential to stay updated on the latest releases and security advisories. Be mindful of version compatibility and potential security vulnerabilities.
While specific SDKs are emerging, the main focus now is on integrating PQC algorithms into existing cryptographic libraries. This allows developers to leverage their existing knowledge and infrastructure. Experimentation and testing with these tools are crucial to determine the best fit for your specific needs.
The 2026 Timeline: What to Expect
By 2026, organizations should aim to have a clear understanding of their cryptographic inventory, a prioritized migration plan, and initial deployments of PQC algorithms in non-critical systems. This isn't about fully replacing all existing cryptography by 2026, but about laying the groundwork for a smooth transition.
Ongoing monitoring and adaptation are essential. The quantum computing landscape is evolving rapidly, and new breakthroughs could impact the PQC landscape. Stay informed about the latest research and NIST’s standardization efforts. Be prepared to adjust your plans as needed. This requires a long-term commitment to security.
The transition to PQC is a complex undertaking, but it’s a necessary one. Ignoring the threat posed by quantum computing is not an option. By taking proactive steps now, organizations can protect their data and ensure their long-term security in a post-quantum world. The key is to start planning, testing, and implementing PQC solutions today.
- Complete cryptographic inventory.
- Prioritized migration plan.
- Initial PQC deployments in non-critical systems.
- Ongoing monitoring and adaptation.
Essential Hardware and Software for Post-Quantum Cybersecurity Readiness

High-performance, general-purpose Hardware Security Module (HSM) · Secure key generation, storage, and lifecycle management · FIPS 140-2 Level 3 certified
The Thales Luna HSM 7 provides robust hardware-based security for cryptographic keys, essential for protecting sensitive data in a post-quantum era.
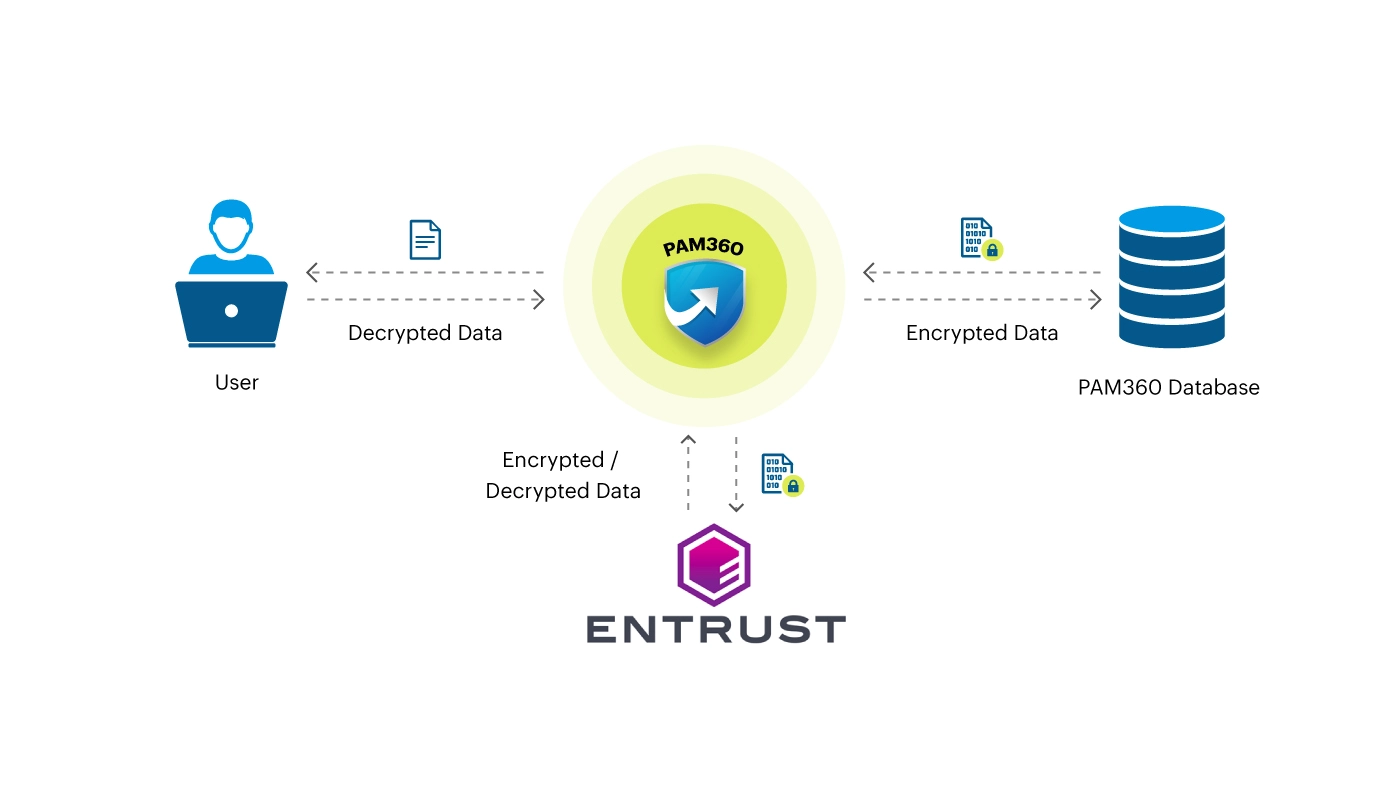
Secure key management and cryptographic operations · Tamper-resistant hardware security module · Supports a wide range of cryptographic algorithms
Entrust's nShield HSM offers a secure environment for cryptographic keys, acting as a vital component in safeguarding against future advanced cyber threats.

Identifies security vulnerabilities and misconfigurations · Analyzes network infrastructure for potential weaknesses · Provides actionable insights for remediation
This Network Vulnerability Assessment tool helps proactively discover and address security loopholes within your network's infrastructure before they can be exploited.

Secures multi-cloud environments (AWS, Azure, Google Cloud) · Automates cloud security posture management · Ensures compliance and mitigates risks
Mastering Cloud Security Posture Management is crucial for maintaining a strong security posture across complex, multi-cloud infrastructures in preparation for evolving threats.

Guides through the process of risk assessment · Covers various aspects of security risk management · Provides frameworks for identifying and evaluating risks
The Security Risk Assessment Handbook offers a structured approach to understanding and managing security risks, a fundamental step in preparing for quantum computing's impact.
As an Amazon Associate I earn from qualifying purchases. Prices may vary.


No comments yet. Be the first to share your thoughts!