Understanding the Basics of Web Application Security
Before we dive into the nitty-gritty of cybersecurity penetration testing, it's crucial to grasp the basics of web application security. Web applications, the heart of your online presence, are often the prime target for cyber threats. Understanding their security is the first step towards a robust defense.
Web application security revolves around a set of measures and protocols designed to protect web applications from threats that exploit vulnerabilities in the application's code. Common threats include Cross-Site Scripting (XSS), SQL Injection, and Cross-Site Request Forgery (CSRF). These threats can lead to data breaches, identity theft, and other serious consequences.
At the core of web application security is the principle of defense in depth. This principle suggests that multiple layers of security controls (defense) should be placed throughout an IT system. Its intent is to provide redundancy in the event a security control fails or a vulnerability is exploited. This can include applying security patches and network security updates regularly, using firewalls, and employing intrusion detection systems.
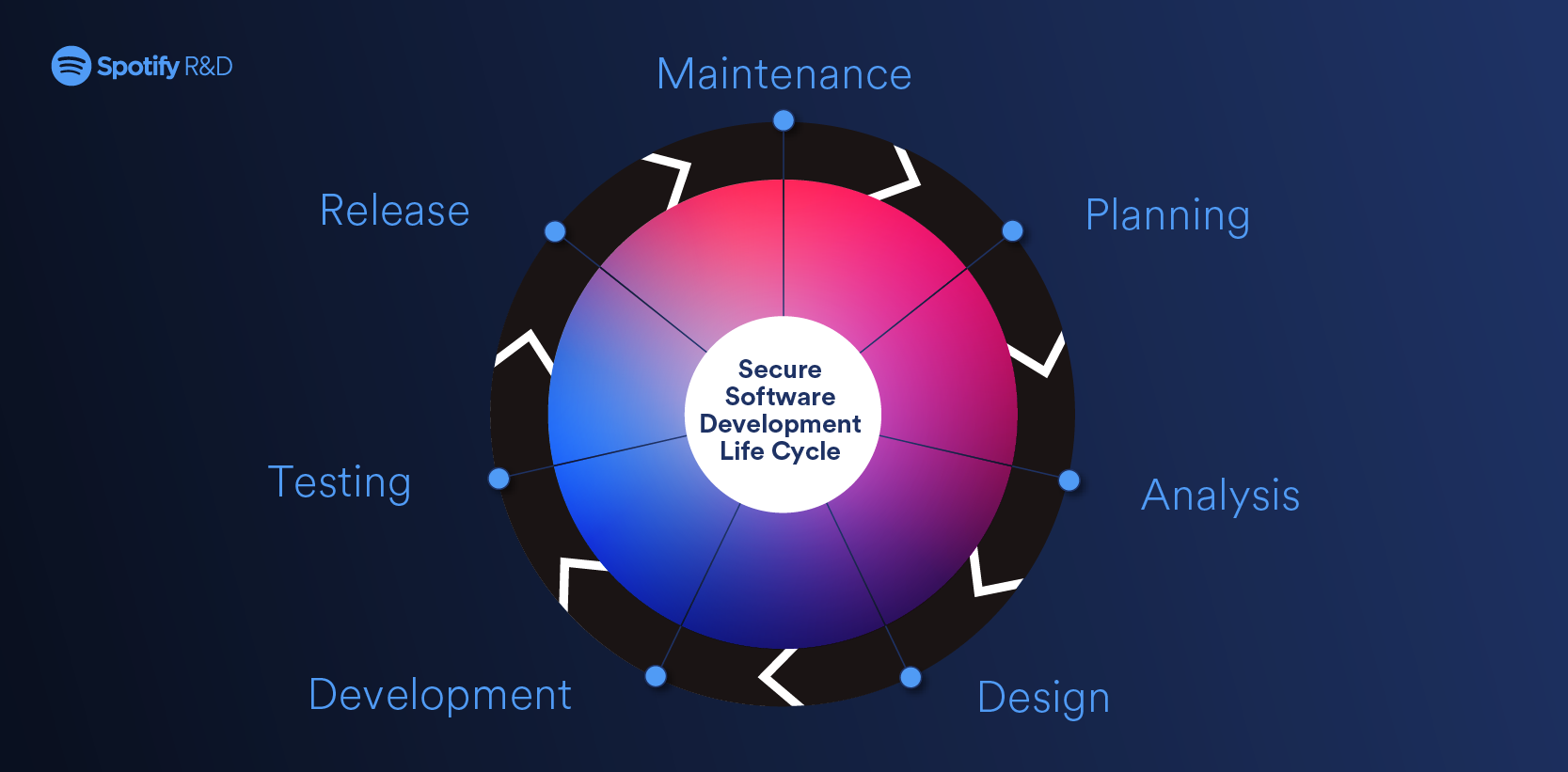
Another key aspect is the secure development lifecycle, which integrates security considerations into every phase of software development. This approach helps to identify and fix security vulnerabilities early, reducing the risk of exploitation.
Understanding these basics provides a foundation for exploring more advanced topics like penetration testing methods and cybersecurity protection techniques. Remember, in the digital world, security measures are not a one-time task but a continuous process of learning, implementing, and updating.
Common Penetration Testing Methods
Now that we've established a solid understanding of web application security, let's delve into the realm of penetration testing methods. Penetration testing, often referred to as 'pen testing', is a simulated cyber attack against your system to check for exploitable vulnerabilities. It's a crucial component of cybersecurity protection techniques, providing a real-world perspective on how secure your web applications truly are.
There are several common penetration testing methods employed in the digital world:
1. Black Box Testing: In this method, the tester has no prior knowledge of the system. It's a real-world scenario where the attacker knows nothing about the target. This method is time-consuming but can reveal vulnerabilities that automated tests might miss.
2. White Box Testing: Contrary to black box testing, here the tester has complete knowledge of the system. This method is more thorough and faster, as the tester knows exactly where to look for vulnerabilities.
3. Gray Box Testing: This is a hybrid approach where the tester has partial knowledge of the system. It combines the advantages of both black and white box testing.
4. Automated Testing: This method uses software tools to perform the tests. It's faster and less labor-intensive but may not discover all vulnerabilities.
5. Manual Testing: As the name suggests, this method involves manually trying to exploit potential vulnerabilities. It's time-consuming but can uncover flaws that automated tools might overlook.
Each method has its strengths and weaknesses, and the choice depends on your specific needs and resources. A combination of these methods often provides the most comprehensive security assessment for your web applications.
Remember, penetration testing is not a one-off task. It should be a regular part of your cybersecurity routine, ensuring your online presence remains secure amidst the ever-evolving landscape of cyber threats.

Securing Your Web Applications
Stepping into the realm of Securing Your Web Applications, it's essential to understand that the safety of your online presence is not just about identifying vulnerabilities through penetration testing. It also involves implementing robust security measures to protect against potential cyber threats. Here, we'll explore some fundamental strategies to secure your web applications.
Firstly, it's crucial to keep your system updated with the latest network security updates. Cybercriminals often exploit outdated software, so regular updates can significantly reduce your vulnerability.
Secondly, consider implementing a Web Application Firewall (WAF). A WAF can help filter out malicious traffic before it reaches your application, providing an extra layer of protection.
Next, secure your data transmission with HTTPS, ensuring that the data exchanged between your server and users is encrypted and secure. This is particularly important if your web application deals with sensitive user data.
Moreover, it's vital to use secure coding practices to prevent common web application vulnerabilities such as SQL Injection and Cross-Site Scripting (XSS). Regular code reviews and using security-focused development frameworks can help achieve this.
Lastly, remember that security is a continuous process. Regular cybersecurity penetration testing and timely implementation of security measures are key to maintaining a secured web application. In the dynamic landscape of the digital world, staying proactive is the best defense against cyber threats.
By adopting these strategies, you can significantly enhance your web application security testing and protection, ensuring a secure and trustworthy online presence.
The Role of Penetration Testing in Online Security
Shifting our focus to The Role of Penetration Testing in Online Security, it's essential to comprehend the pivotal role this cybersecurity protection technique plays in fortifying your digital fortress. Penetration testing, often referred to as ethical hacking, is a proactive approach to discovering potential vulnerabilities in your web applications before malicious hackers do.
Online security penetration testing dives deep into your system, simulating cyber-attacks to identify weak points. This method provides a comprehensive view of your security posture, revealing how well your network security updates and other protective measures are performing against potential threats. 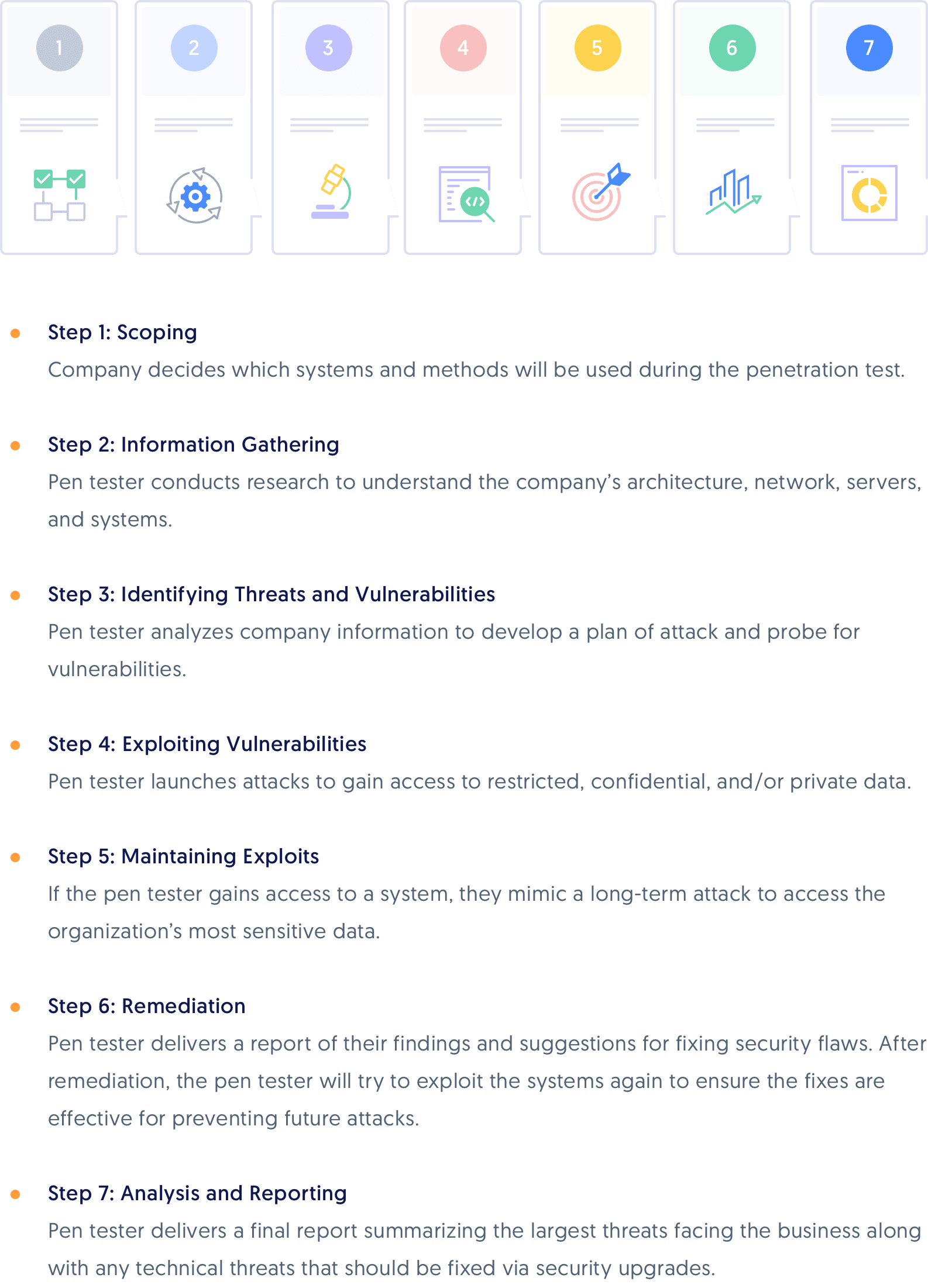
One of the significant benefits of penetration testing is its ability to provide a real-world perspective on your system's security. It doesn't merely rely on theoretical vulnerability assessments. Instead, it actively attempts to breach your defenses, just as a real attacker would. This hands-on approach allows you to understand the actual risks your web application faces, rather than theoretical ones. 
Another key advantage of penetration testing is that it helps you prioritize your security efforts. By identifying the most critical vulnerabilities that could be exploited by attackers, you can focus your resources on fixing these first, thereby maximizing your cybersecurity protection.
Moreover, penetration testing also plays a crucial role in compliance. Many regulations and standards, such as the Payment Card Industry Data Security Standard (PCI DSS), require regular penetration testing to ensure secure handling of sensitive data.
In essence, penetration testing is a critical component of online security in the digital world. It offers a proactive, real-world approach to identifying vulnerabilities, prioritizing security efforts, and maintaining regulatory compliance, thereby playing an indispensable role in securing your web applications.
Staying Ahead in the Digital World: Cybersecurity Protection Techniques
As we navigate the digital landscape, staying one step ahead is crucial. In the realm of cybersecurity, this means adopting proactive protection techniques. These techniques are not just about fixing vulnerabilities but also about anticipating potential threats. Let's delve into some key cybersecurity protection techniques that can help secure your web applications.
Regular Network Security Updates: Keeping your network security up-to-date is the first line of defense. This includes regularly updating your firewalls, antivirus software, and other security tools. 
Embracing Penetration Testing: Cybersecurity penetration testing is a proactive approach to discover vulnerabilities before they can be exploited. It involves simulating cyber-attacks on your web applications to identify weak spots. 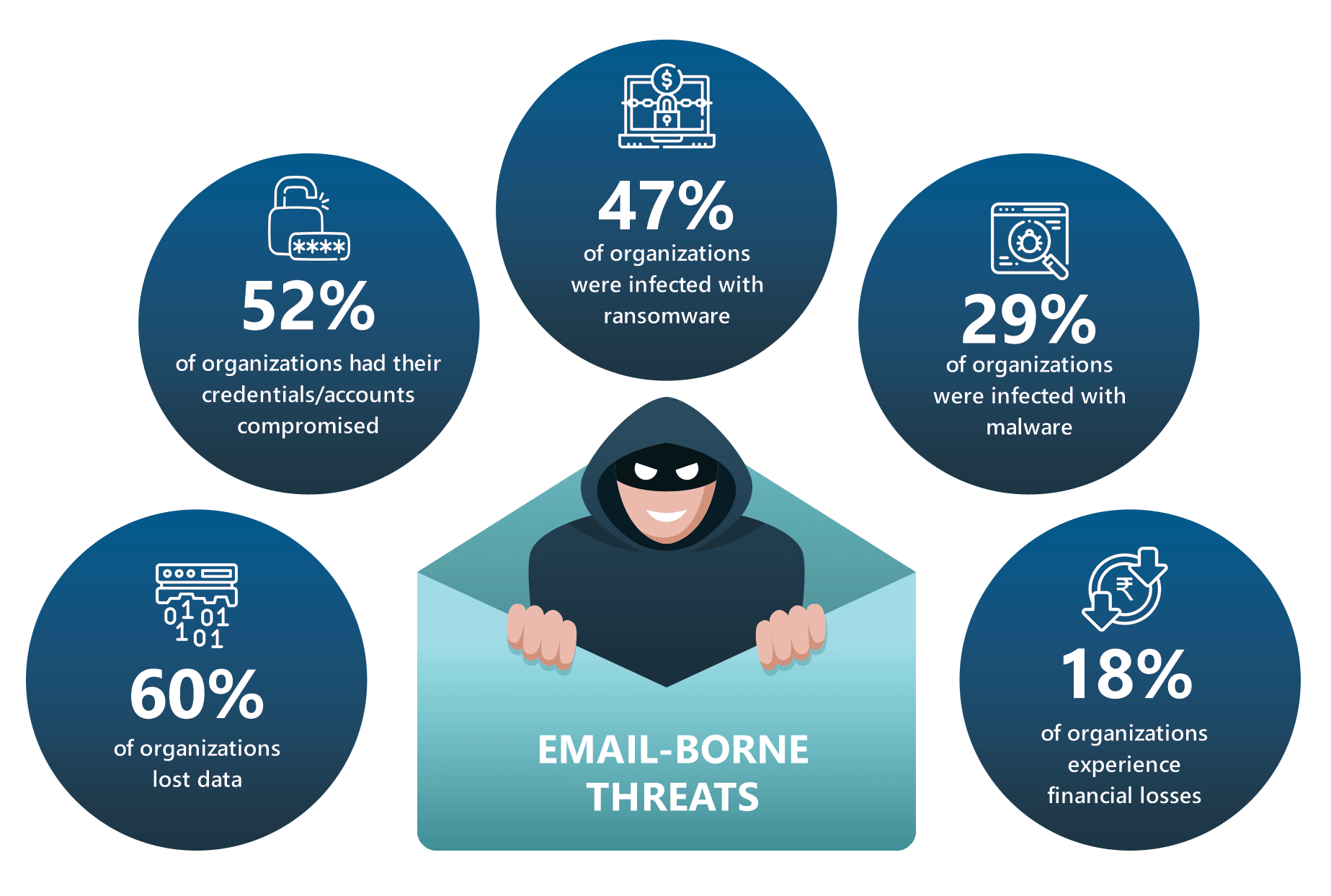
Secure Coding Practices: Secure coding is a preventive measure. It involves designing and implementing your web applications in a way that minimizes the risk of security breaches. This includes techniques like input validation, error handling, and encryption. 
Continuous Monitoring: In the digital world, threats evolve rapidly. Continuous monitoring of your web applications can help detect unusual activities and respond promptly. 
Remember, in the digital world, security is not a one-time effort but a continuous process. By embracing these cybersecurity protection techniques, you can ensure that your web applications remain secured and your online presence is protected.
Understanding Web Application Penetration Testing
Let's dive into the world of Web Application Penetration Testing. In the simplest terms, it's a cybersecurity practice that tests a web application's security. It's like a mock drill where we simulate attacks on our web applications to find vulnerabilities before the bad guys do.
Imagine your web application as a fortress. The walls, gates, and guards are all part of your cybersecurity measures. Now, penetration testing is like inviting a friendly dragon to attack your fortress. The dragon doesn't mean any harm but will expose any weak spots in your defenses. That's exactly what web application penetration testing does. It's a controlled, ethical hacking attempt to identify and fix security holes in your digital fortress.

Web application penetration testing follows a systematic process. It starts with gathering information about the target system, identifying possible entry points, attempting to break in, and reporting back the findings. The goal is to improve cybersecurity protection techniques and ensure digital world security measures are up-to-date.
By understanding the ins and outs of penetration testing, you can better protect your online presence. It's a proactive approach to network security updates and a vital part of maintaining secured web applications.
So, whether you're a small business owner, a web developer, or just a tech enthusiast, understanding web application penetration testing is your first step towards a more secure digital world.
The Importance of Network Security Updates
Now that we've explored the concept of web application penetration testing, let's shift our focus to the importance of network security updates. In the ever-evolving landscape of the digital world, staying updated is not just an option, it's a necessity.
Think of network security updates as the regular health check-ups for your digital fortress. Just as you wouldn't ignore a doctor's advice to stay healthy, you shouldn't neglect these updates to maintain a robust cybersecurity posture. They are the vitamins that keep your network's immune system strong against the relentless onslaught of cyber threats.
Network security updates are crucial for several reasons. First, they patch vulnerabilities that could be exploited by malicious hackers. These vulnerabilities are like hidden trap doors in your digital fortress. If left unattended, they can provide easy access for cyber intruders.

Second, these updates often come with enhancements to improve your system's overall performance and stability. They can also add new features that enhance your cybersecurity protection techniques, making your digital fortress not just stronger, but smarter too.
Lastly, network security updates help you stay compliant with the latest industry standards and regulations. Non-compliance can lead to hefty fines and a damaged reputation.
In the realm of online security penetration testing, staying updated is a proactive defense strategy. It's like keeping your friendly dragon well-fed and ready for the next mock attack. So, remember, a well-updated system is a well-protected system. Embrace network security updates, and fortify your digital presence.
Securing Web Applications: Best Practices
When it comes to Securing Web Applications: Best Practices, there are several key measures that can significantly enhance your online security posture.
Firstly, it's crucial to keep your web applications updated with the latest network security updates. This not only patches vulnerabilities but also equips your system with the latest security features. 
Secondly, implementing a robust cybersecurity penetration testing routine is vital. Regular penetration testing uncovers potential weaknesses in your web applications, allowing you to fix them before they can be exploited. 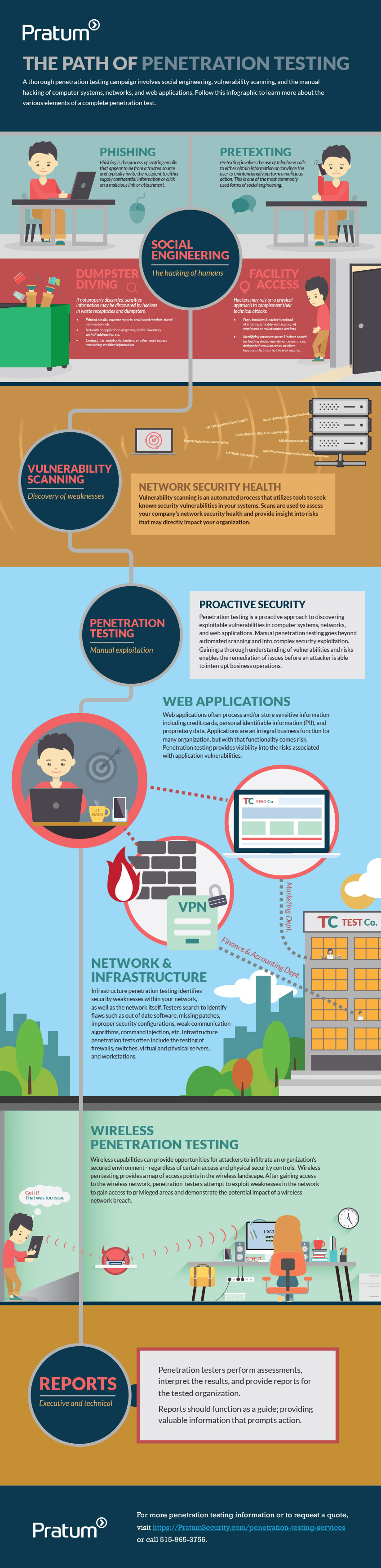
Moreover, it's essential to adopt secure coding practices. This includes input validation to prevent SQL injection attacks, using secure cookies, and implementing Cross-Site Request Forgery (CSRF) tokens. 
Another best practice is to use HTTPS for all your web applications. HTTPS encrypts the data between your web application and the user, safeguarding it from interception and tampering. 
Lastly, always ensure that your web applications have the most recent cybersecurity protection techniques. This includes using firewalls, intrusion detection systems, and regularly updating your security policies. 
By adhering to these best practices, you can significantly enhance the security of your web applications, ensuring a safer digital world for your users.
Web Application Security Testing: A Comprehensive Approach
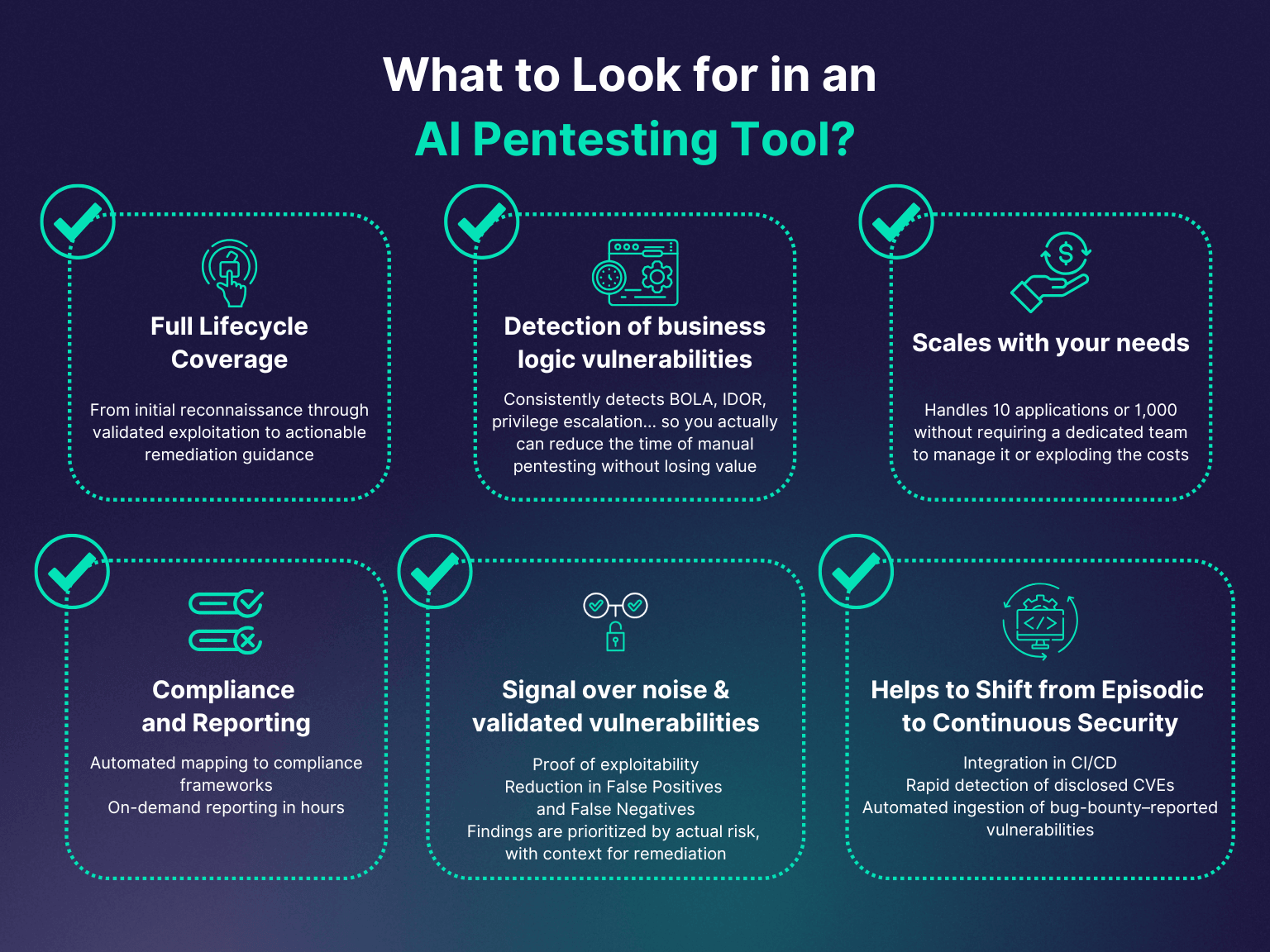
Stepping into the realm of Web Application Security Testing: A Comprehensive Approach, we delve deeper into the intricacies of securing your digital presence. This approach is a holistic one, encompassing a wide range of cybersecurity penetration testing methods and network security updates. It's about creating a secured web application that stands firm against the ever-evolving threats in the digital world.
At the heart of this approach is a thorough understanding of your web application's architecture. This includes recognizing the data flow, identifying potential weak points, and understanding the functionalities of each component. 
Once you've mapped out your application, the next step is to perform a comprehensive risk assessment. This involves identifying potential threats, assessing their impact, and prioritizing them based on their severity. This risk-based approach ensures that you focus your efforts where they're needed most.
Following the risk assessment, it's time to put your application to the test. Employ a variety of penetration testing methods, such as static and dynamic analysis, to uncover any hidden vulnerabilities. Remember, the goal is not just to find vulnerabilities but also to understand their root cause. This understanding is crucial in developing effective countermeasures.
Finally, it's essential to remember that security is not a one-time event but an ongoing process. Regularly update your web applications with the latest network security updates and continually monitor your system for any unusual activity. 
By adopting this comprehensive approach to web application security testing, you're not just protecting your online presence but also contributing to a safer digital world. Remember, in the realm of cybersecurity, vigilance is your best defense.
Importance of Network Security Updates
Now that we've explored the concept of web application penetration testing, let's shift our focus to the Importance of Network Security Updates. In the ever-evolving digital landscape, staying updated is not just an option, it's a necessity.
Think of network security updates as the regular health check-ups for your digital fortress. Just as we need regular health screenings to catch any potential issues early, our digital systems also need regular updates to stay healthy and secure. 
These updates are vital for several reasons. Firstly, they patch up any known vulnerabilities in your system. Cybercriminals are always on the lookout for these vulnerabilities, and they won't hesitate to exploit them. By regularly updating your network security, you're closing these loopholes before they can be used against you.
Secondly, network security updates often come with enhancements to your system's existing security features. These enhancements can range from improved encryption algorithms to more robust firewalls. They serve to strengthen your digital fortress against the ever-growing arsenal of cyber threats.
Lastly, network security updates help you stay compliant with the latest cybersecurity regulations and standards. Non-compliance can lead to hefty fines and a damaged reputation. By staying updated, you're not just protecting your digital assets, but also your brand's integrity. 
In conclusion, network security updates are an integral part of cybersecurity penetration testing and maintaining secured web applications. They are the lifeblood that keeps your digital fortress strong and resilient against cyber threats. So, make sure to keep them at the top of your cybersecurity checklist.
Effective Penetration Testing Methods
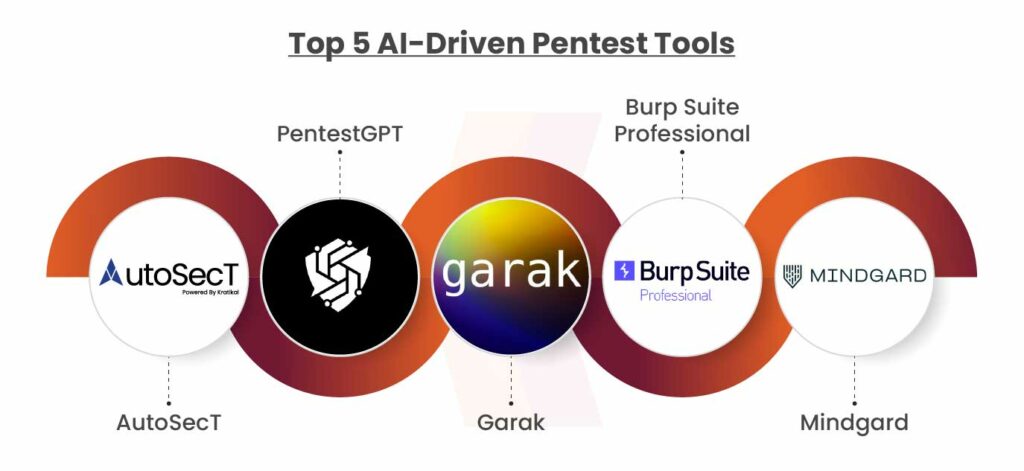
Transitioning from the importance of network security updates, let's delve into the realm of Effective Penetration Testing Methods. Penetration testing, or 'pen testing', is a proactive approach to cybersecurity. It involves simulating cyber-attacks on your own systems to identify vulnerabilities before they're exploited by malicious hackers.
One of the most effective methods is the Black Box Testing. Here, the tester has no prior knowledge of the system architecture. This method simulates an external attack, much like a real-world cyber assault where the attacker knows nothing about the target. It's a comprehensive way to test the security of your web applications from an outsider's perspective. 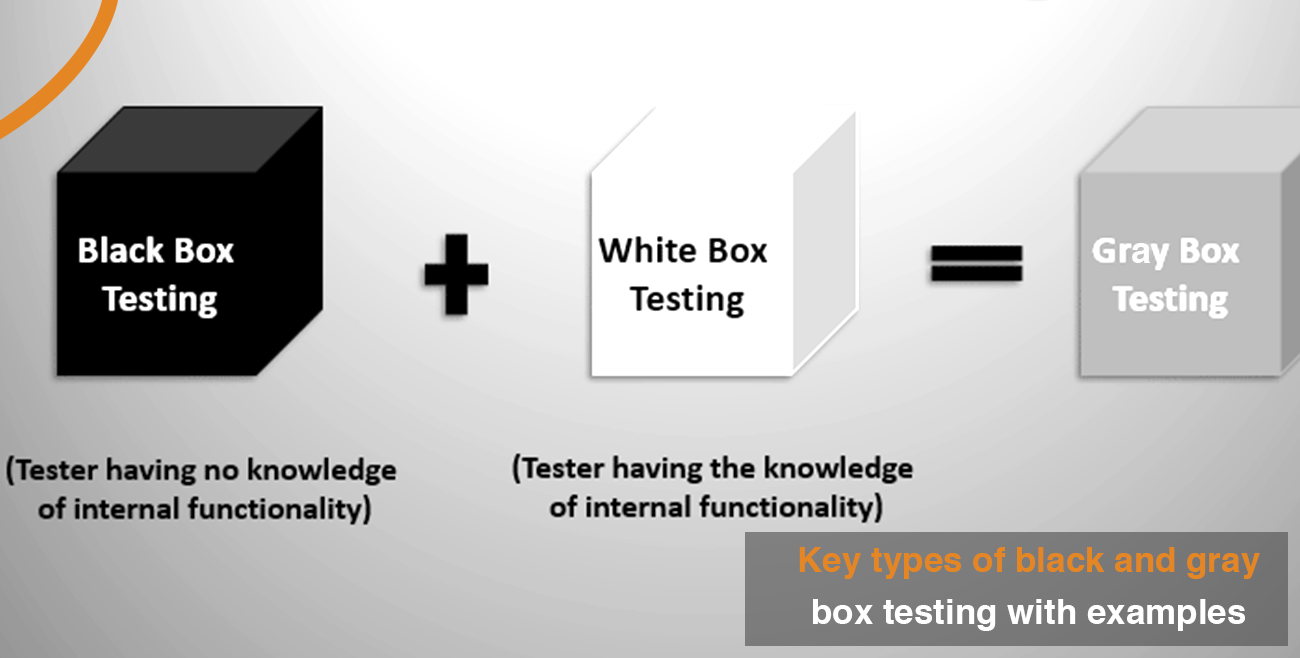
Next, we have White Box Testing. Unlike Black Box Testing, here the tester has complete knowledge of the system's architecture. This method is akin to an internal attack, where the attacker has intimate knowledge of the system. It's an excellent way to identify vulnerabilities that may be overlooked in Black Box Testing. 
Finally, there's Grey Box Testing, a hybrid of the two. The tester has partial knowledge of the system, simulating an attack from someone with limited inside information. This method offers a balanced approach, combining the strengths of both Black and White Box Testing. 
These methods, when used in conjunction, provide a robust penetration testing strategy. They help ensure your web applications are secure, offering you peace of mind in the ever-evolving digital world. Remember, the goal isn't just to identify vulnerabilities but also to fix them, making your online presence a secured fortress against cyber threats.
Securing Web Applications
After understanding the various penetration testing methods, we now turn our attention to Securing Web Applications. In the digital world, where cyber threats are constantly evolving, securing your web applications is not just a necessity, it's an imperative.
Web applications are a common target for hackers due to their widespread use and the valuable data they often hold. Therefore, implementing robust cybersecurity measures is crucial. The first step towards securing your web applications is understanding the potential threats. This includes everything from SQL injection and Cross-Site Scripting (XSS) to Cross-Site Request Forgery (CSRF) and Distributed Denial of Service (DDoS) attacks.
Once you've identified the threats, the next step is to implement a multi-layered security strategy. This involves using a combination of security measures such as firewalls, intrusion detection systems, and secure coding practices. 
A key aspect of this strategy is secure coding. This involves writing code in a way that minimizes the potential for security vulnerabilities. It includes practices such as input validation, output encoding, and proper error handling.
Another important aspect is keeping your software and systems up-to-date with the latest network security updates. These updates often contain patches for known vulnerabilities, helping to protect your web applications from known threats.
Finally, regular cybersecurity penetration testing is essential. This involves simulating cyber-attacks on your web applications to identify and fix vulnerabilities before they can be exploited by hackers.
In conclusion, securing your web applications is a continuous process that involves understanding the threats, implementing a multi-layered security strategy, and regularly testing your defenses. By doing so, you can help ensure your online presence is a secured fortress in the digital world.
Web Application Security Testing
As we delve deeper into the realm of cybersecurity, let's cast the spotlight on Web Application Security Testing. This process is a cornerstone in the fortress of online security, serving as a proactive approach to uncover potential vulnerabilities and fix them before they become a gateway for hackers.
Web Application Security Testing is a specialized form of cybersecurity penetration testing, specifically tailored to secure web applications. It involves a comprehensive examination of your web application's code, functionalities, and the environment in which it operates. The objective? To identify any weak spots that could be exploited by cybercriminals.

One of the primary techniques used in this process is dynamic testing. This involves interacting with the web application in real-time, mimicking the actions of a potential attacker to uncover vulnerabilities that might not be visible in the static code. This hands-on approach allows for a more realistic assessment of your application's security posture.
Another crucial technique is static testing. This involves a thorough review of your application's source code to identify potential security flaws. It's akin to proofreading a document for errors, but instead of grammar and punctuation, we're looking for insecure coding practices and potential security loopholes.

Web Application Security Testing is not a one-time event, but rather a continuous process that should be integrated into the development lifecycle of your application. Regular testing ensures that any new changes or updates to your application do not introduce new vulnerabilities. In the ever-evolving landscape of the digital world, staying one step ahead of potential threats is key to maintaining a secured web application.
Protecting Your Online Presence with Penetration Testing
Now that we've explored the intricacies of Web Application Security Testing, let's shift our focus to the broader perspective of Protecting Your Online Presence with Penetration Testing. Penetration testing, or 'pen testing', is a crucial component of cybersecurity protection techniques. It's a simulated cyber attack against your system to check for exploitable vulnerabilities. In the context of web applications, it's like a full-scale rehearsal to ensure your defenses are up to the task.
Imagine your online presence as a fortress. The walls are your network security updates, the guards are your secure web applications, and the gate is your web application security testing. But how do you know if they can withstand a real attack? That's where penetration testing comes in. It's like having a friendly knight test your defenses before the real battle. 
There are several penetration testing methods that can be employed to safeguard your digital world. These include external testing (testing the security of the network's perimeter), internal testing (simulating an attack from a rogue insider), and blind testing (simulating an attack from a hacker with minimal information about the system).
Online security penetration testing is a proactive approach. Instead of waiting for an attack to happen, you're taking the initiative to find and fix vulnerabilities. It's an essential step in securing your online presence, and it's a step that should never be skipped. Remember, in the digital world, security is not a product, but a process. And penetration testing is a vital part of that process. 
So, whether you're a small business owner, a manager at a large corporation, or just an individual concerned about your online security, penetration testing should be a part of your cybersecurity strategy. It's not just about protecting your data - it's about protecting your reputation, your customers, and ultimately, your future in the digital world.
Cybersecurity Protection Techniques for Web Applications
Delving deeper into the realm of cybersecurity protection techniques for web applications, it's essential to understand that the digital world is a battlefield. Each day, new threats emerge, and old ones evolve, making it imperative to stay ahead of the curve. Web applications, being the gateways to vast amounts of sensitive data, are often prime targets for cybercriminals. Therefore, implementing robust cybersecurity measures is not just an option, but a necessity.
One of the most effective techniques is the use of secured web applications. This involves the application of stringent security measures right from the development stage. Coding practices that prioritize security, such as input validation, can help prevent common attacks like SQL injection and cross-site scripting. 
Another crucial technique is the regular deployment of network security updates. These updates often contain patches for known vulnerabilities that could be exploited by attackers. Staying updated is akin to reinforcing the walls of your fortress, ensuring that no weak spots are left exposed. 
Furthermore, the use of firewalls and intrusion detection systems (IDS) can add an extra layer of protection. Firewalls control the traffic entering and leaving the network, blocking any suspicious activity. On the other hand, IDS monitor the network for any signs of a breach, allowing for quick detection and response. 
Finally, regular cybersecurity penetration testing is a must. This technique simulates real-world attacks on the system, identifying any potential vulnerabilities. It's like a regular health check-up for your web applications, ensuring they are in the best shape to fend off any attacks. 
In the ever-evolving digital world, staying secure is a continuous journey. By implementing these cybersecurity protection techniques, you can ensure that your web applications are not just surviving, but thriving in this battlefield.
Digital World Security Measures
Stepping into the realm of Digital World Security Measures, we find ourselves in a dynamic landscape where vigilance and proactive measures are key. The digital world is akin to a vast ocean, teeming with potential threats lurking beneath the surface. As such, the security of your online presence is akin to a sturdy ship, designed to weather any storm.
One of the most fundamental measures in this digital world is the use of secure web applications. These are akin to fortified castles, built with robust walls to keep out unwanted intruders. They are designed with security at their core, incorporating secure coding practices and stringent validation checks to ward off common cyber threats.

Another vital measure is the consistent application of network security updates. Think of these as regular maintenance checks for your ship, ensuring that it remains seaworthy and ready to face any potential threats. These updates often contain patches for known vulnerabilities, effectively sealing any cracks that could be exploited by cybercriminals.
Adding to this, the deployment of firewalls and intrusion detection systems (IDS) serve as your ship's watchful crew, constantly on the lookout for potential threats. Firewalls control the flow of traffic, blocking any suspicious activity, while IDS monitor the network for signs of a breach, enabling swift detection and response.

Lastly, cybersecurity penetration testing is a crucial measure. This method simulates real-world attacks, identifying potential vulnerabilities in your system. It's like a drill for your crew, ensuring they are prepared to fend off any attacks.
In the vast ocean of the digital world, these security measures are your compass and map, guiding you safely through potential dangers. By implementing these measures, you can ensure that your online presence remains secure, regardless of the challenges that the digital world may present.



No comments yet. Be the first to share your thoughts!