The end of the network perimeter
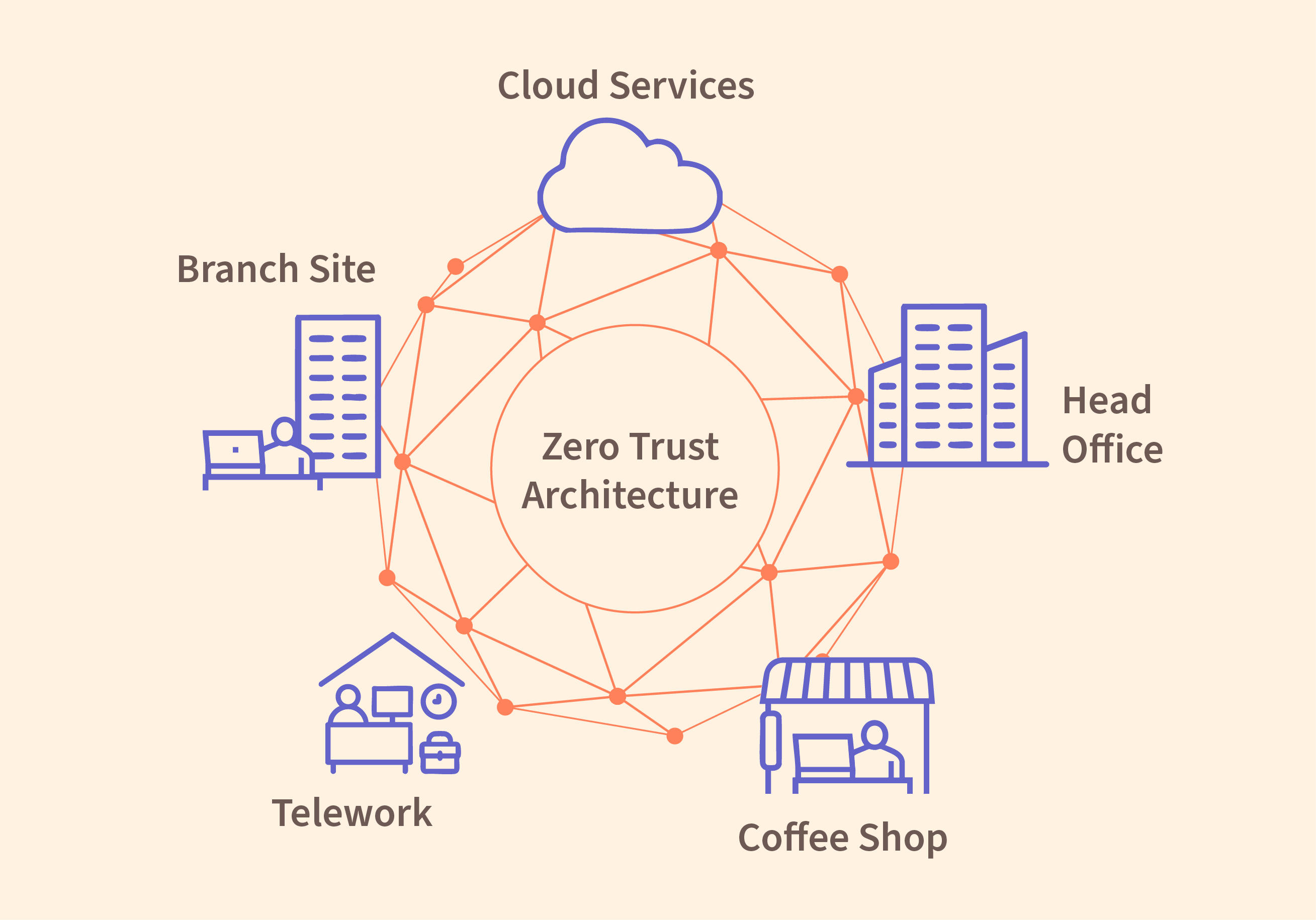
Remote work is no longer a temporary fix. Most companies now operate with a scattered workforce, which makes the old 'castle-and-moat' security model useless. You can't protect a perimeter that doesn't exist when your data lives on home Wi-Fi networks and coffee shop laptops.
Historically, network security relied on establishing a secure boundary. Once inside that perimeter, users were often implicitly trusted. This model is deeply flawed in a remote-first world where that perimeter has dissolved. Attackers now target remote workers directly, exploiting vulnerabilities in home networks and personal devices.
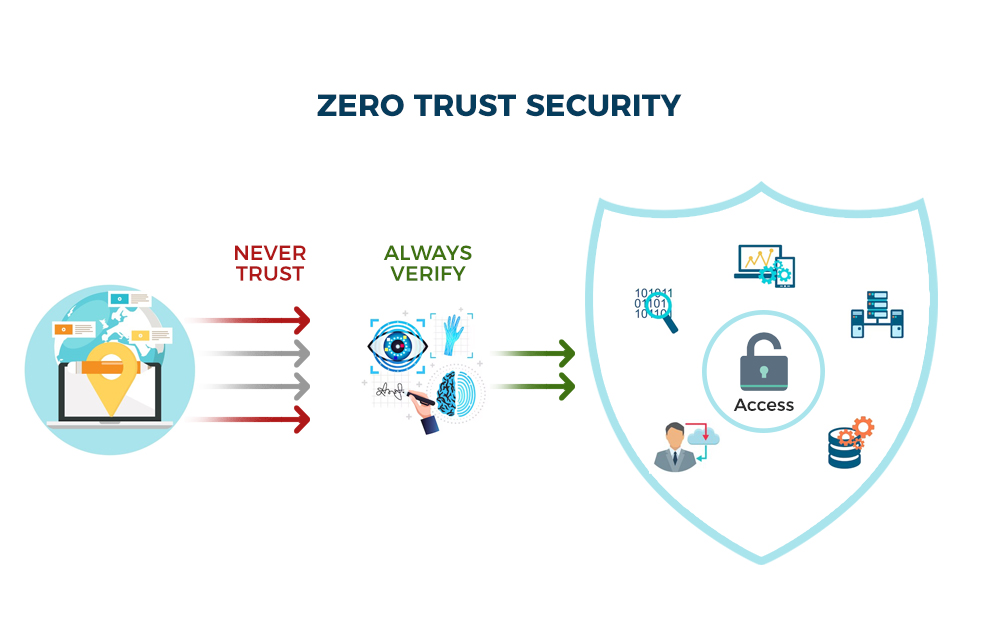
Zero Trust is a security framework built on the principle of 'never trust, always verify.' It assumes that no user or device, whether inside or outside the network, is inherently trustworthy. Every access request is rigorously authenticated, authorized, and continuously validated. This is a direct response to the failures of perimeter-based security in a world where the perimeter is increasingly irrelevant.
Verizon’s 2023 Data Breach Investigations Report shows that 74% of breaches involve people making mistakes or being targeted directly. Ransomware attacks on remote staff jumped 49% in a single year. These aren't just abstract risks; they are the primary way hackers get in now.
Content is being updated. Check back soon.
NIST framework components
The National Institute of Standards and Technology (NIST) Special Publication 800-207 provides a comprehensive framework for Zero Trust Architecture. It outlines seven key pillars that organizations should address when implementing a Zero Trust approach. These pillars aren’t isolated components, but rather interconnected elements working together to create a more secure environment.
First, Data Security is paramount. This means classifying data based on sensitivity and implementing appropriate encryption and access controls. It’s not enough to simply protect the network; you must protect the data itself, wherever it resides. Then there's Command Plane Security, which focuses on protecting the infrastructure used to manage and control the network. Compromise here could allow an attacker to control the entire system.
The Programming Plane Security pillar concerns itself with the development and deployment of secure code. This focuses on preventing vulnerabilities from being introduced during the software development lifecycle. Infrastructure Security ensures the underlying network infrastructure – servers, routers, switches – is hardened and protected. This involves regular patching, vulnerability scanning, and intrusion detection.
Endpoint Security is crucial in a remote work environment. It involves securing all devices that access the network, including laptops, smartphones, and tablets. This includes implementing endpoint detection and response (EDR) solutions and enforcing device compliance policies. Application Security focuses on securing the applications themselves, ensuring they are free from vulnerabilities and adhere to secure coding practices. Finally, Identity and Access Management (IAM), which we’ll explore in more detail later, is the cornerstone of Zero Trust, verifying every user and device attempting to access resources.
Identity as the boundary
In a Zero Trust model, identity becomes the new perimeter. Traditional network boundaries are dissolving, so verifying who is accessing resources is more important than where they are located. This places Identity and Access Management (IAM) at the heart of the security strategy.
Multi-Factor Authentication (MFA) is a non-negotiable component of any Zero Trust implementation. Requiring users to provide multiple forms of verification – something they know, something they have, and something they are – significantly reduces the risk of unauthorized access. Even if an attacker compromises a password, they'll still need access to a second factor to gain entry.
The principle of Least Privilege Access dictates that users should only be granted the minimum level of access necessary to perform their job duties. This limits the potential damage an attacker can cause if they compromise an account. A well-implemented Identity Governance and Administration (IGA) solution can help automate the process of provisioning and managing user access rights.
Managing identities across a diverse remote environment presents unique challenges. Organizations must account for personal devices, varying network connections, and the potential for shadow IT. Robust IGA solutions and strong MFA policies are essential for maintaining control.
- Require MFA for every user and every application without exception.
- Enforce Least Privilege Access.
- Use IGA tools to handle identity management automatically.
- Regularly review and update user access rights.
Content is being updated. Check back soon.
Microsegmentation and Network Access Control
Microsegmentation involves dividing the network into small, isolated segments. This limits the blast radius of a potential breach, preventing an attacker from moving laterally across the network. If one segment is compromised, the attacker's access is contained, minimizing the impact.
Traditional network segmentation often relies on broad subnet divisions, which can still allow for significant lateral movement. Microsegmentation, on the other hand, uses granular policies based on application, user identity, and device posture to create highly isolated environments. It’s about creating a "zero trust zone" for every application and resource.
Network Access Control (NAC) solutions play a vital role in enforcing these policies. NAC solutions verify the identity and security posture of devices before granting them access to the network. This ensures that only compliant devices are allowed to connect, reducing the risk of introducing malware or other threats.
Imagine a scenario where an attacker compromises a remote worker’s laptop. With traditional segmentation, they might have access to a large portion of the network. With microsegmentation, their access would be limited to the specific segment associated with that user and their authorized applications, greatly reducing the potential damage.
Continuous Monitoring and Analytics
Zero Trust isn’t a one-time implementation; it’s an ongoing process. Continuous monitoring and threat detection are essential for identifying and responding to potential security incidents. Traditional reactive security approaches – waiting for an alert to trigger a response – are no longer sufficient.
Security Information and Event Management (SIEM) systems collect and analyze security logs from various sources, providing a centralized view of security events. Extended Detection and Response (XDR) solutions go a step further, integrating data from multiple security tools to provide a more comprehensive threat detection and response capability.
However, simply collecting data isn’t enough. Behavioral analytics play a crucial role in identifying anomalous activity that might indicate a security breach. By establishing a baseline of normal behavior, organizations can detect deviations that warrant further investigation. This is where machine learning can be particularly valuable.
Automation is key to responding to threats quickly and effectively. Automated response actions, such as isolating compromised devices or blocking malicious traffic, can significantly reduce the impact of a breach. This requires integrating monitoring and analytics tools with security orchestration, automation, and response (SOAR) platforms.
Content is being updated. Check back soon.
How to start the transition
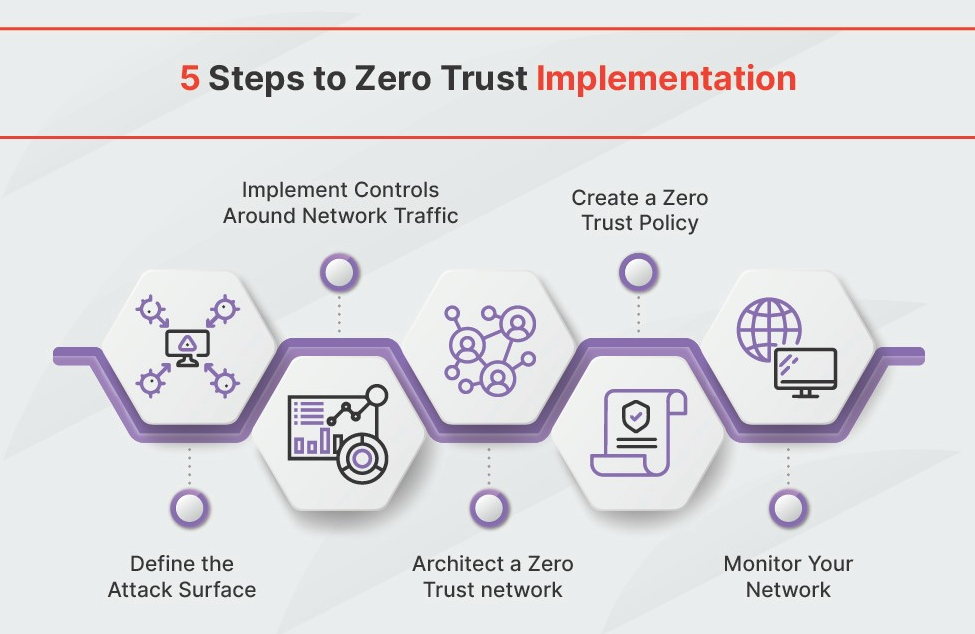
Implementing Zero Trust is a journey, not a destination. It requires a phased approach, starting with assessment and planning. Organizations need to understand their current security posture, identify critical assets, and define clear goals for their Zero Trust implementation. The Department of Defense's Zero Trust Implementation Guideline Primer is a valuable resource in this process:
The next step is identity management. This involves implementing MFA, enforcing Least Privilege Access, and deploying an IGA solution. Simultaneously, organizations should focus on device security, ensuring all devices accessing the network are compliant with security policies. This includes endpoint detection and response (EDR) solutions and mobile device management (MDM) tools.
Network segmentation is a critical component. Start by segmenting critical assets and gradually expand segmentation across the network. Finally, continuous monitoring should be implemented from the outset, providing visibility into network activity and enabling rapid threat detection and response. This involves deploying SIEM and XDR solutions and establishing robust security analytics capabilities.
Remember that a full Zero Trust implementation can take time and resources. It’s important to prioritize based on risk and focus on delivering incremental value. Don't try to boil the ocean. Start with a pilot project and gradually expand the scope of the implementation.
Where implementations fail
Implementing Zero Trust isn’t without its challenges. One of the most common obstacles is lack of executive buy-in. If leadership doesn’t understand the benefits of Zero Trust, it will be difficult to secure the necessary funding and resources. Clearly articulating the risks of the current security model and the potential benefits of Zero Trust is crucial.
The complexity of implementation can also be a significant hurdle. Zero Trust requires integrating multiple security tools and technologies, which can be challenging. Start small, focus on delivering incremental value, and leverage automation wherever possible. Integration issues with existing systems are also common. Carefully assess compatibility and plan for potential integration challenges.
Finally, user resistance can derail a Zero Trust implementation. Users may resist changes to their workflows or perceive MFA as inconvenient. Thorough training and clear communication are essential for addressing these concerns. Emphasize the benefits of Zero Trust – enhanced security and protection of sensitive data – and address user concerns proactively.


No comments yet. Be the first to share your thoughts!