Zero Trust: Beyond the Hype
The term 'Zero Trust' gets thrown around a lot these days. It’s easy to dismiss it as just another cybersecurity buzzword, but that would be a mistake. The fundamental problem is that traditional network security – built around the idea of a secure perimeter – is simply no longer effective. We’ve seen a massive shift toward remote work, widespread cloud adoption, and increasingly sophisticated attacks that easily bypass these outdated defenses.
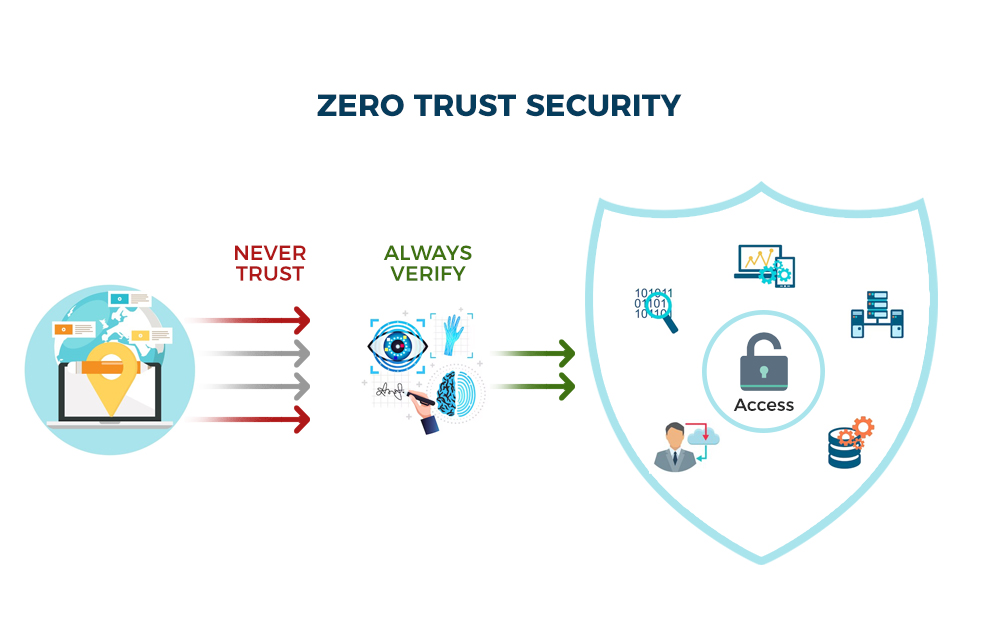
The old model assumes everything inside the network is trustworthy. That assumption is demonstrably false. A single compromised device or user account can give attackers free rein. Zero Trust turns that model on its head. It operates on the principle of 'never trust, always verify,' regardless of whether a user or device is inside or outside the network perimeter.
The National Institute of Standards and Technology (NIST) Special Publication 800-207 provides the foundational documentation for understanding Zero Trust Architecture. It doesn’t prescribe a specific product or solution, but rather a set of guiding principles. Understanding these principles is the first step toward building a more resilient security posture. This isn't about replacing everything you have; it's about layering a new approach on top of your existing infrastructure.
I believe that the shift to Zero Trust isn’t optional anymore. It's a necessary evolution in network security, driven by the changing threat landscape and the realities of modern IT environments. It’s a complex undertaking, but the potential benefits – reduced risk, improved compliance, and greater agility – are well worth the effort.

Core Principles: Verify Everything
At its heart, Zero Trust is built on three core principles: never trust, always verify, and assume breach. 'Never trust' means that no user, device, or application should be automatically trusted, even if they are already authenticated. 'Always verify' requires strict identity verification for every access request. And 'assume breach' acknowledges that attackers will eventually find a way in, so security controls must be designed to minimize the impact of a successful attack.
Microsegmentation is a critical component of Zero Trust. Instead of treating the network as a single, monolithic entity, it divides the network into smaller, isolated segments. This limits the blast radius of a potential breach, preventing attackers from moving laterally across the network. Think of it like watertight compartments on a ship – if one compartment is breached, the damage is contained.
Least privilege access is another key principle. Users and applications should only be granted the minimum level of access necessary to perform their tasks. This reduces the potential damage that can be caused by a compromised account. Continuous monitoring is also essential. Security teams need to constantly monitor network traffic and user activity for suspicious behavior. This requires robust logging, alerting, and analytics capabilities.
These principles aren't just abstract concepts. They have practical implications for how you design and manage your network. For example, implementing microsegmentation might involve using software-defined networking (SDN) to create virtual network segments. Enforcing least privilege access might require implementing role-based access control (RBAC) and regularly reviewing user permissions.
- Never trust: No user, device, or application is inherently trustworthy.
- Always verify: Strict identity verification for every access request.
- Assume breach: Design security controls to minimize breach impact.
Identity as the New Perimeter
In a Zero Trust architecture, identity becomes the new perimeter. If you can’t reliably verify the identity of a user or device, you shouldn’t grant access to any resources. This is why Identity and Access Management (IAM) is so crucial. A strong IAM system is the foundation of a Zero Trust security strategy.
Multi-Factor Authentication (MFA) is a fundamental requirement. Requiring users to provide multiple forms of authentication – something they know (password), something they have (security token), and something they are (biometrics) – significantly reduces the risk of unauthorized access. Passwordless authentication methods, such as FIDO2 security keys, are gaining traction as a more secure and user-friendly alternative to traditional passwords.
Privileged Access Management (PAM) is another critical component. PAM controls and monitors access to privileged accounts – accounts with elevated permissions that can be used to make significant changes to the system. The Department of Defense (DoD) Zero Trust Implementation Guideline Phase One places a heavy emphasis on PAM, recognizing the risk posed by compromised privileged accounts.
Integrating IAM with other security tools is essential. For example, IAM can be integrated with SIEM systems to provide a more comprehensive view of security events. It can also be integrated with endpoint detection and response (EDR) solutions to provide real-time threat detection and response capabilities. The goal is to create a cohesive security ecosystem where all components work together to protect the organization.
- MFA: Multi-Factor Authentication is a core IAM component.
- Passwordless Authentication: FIDO2 security keys offer enhanced security and usability.
- PAM: Privileged Access Management controls access to sensitive accounts.
Multi-Factor Authentication (MFA) Method Comparison for Zero Trust Environments
| Method | Security Strength | User Experience | Implementation Complexity | Cost Considerations |
|---|---|---|---|---|
| SMS-Based MFA | Lowest | Generally High - widely understood | Low | Lower upfront cost, potential per-message fees |
| Authenticator App (TOTP) | Better | Good - requires app installation | Medium | Low to moderate - app development/integration or third-party service |
| Hardware Security Keys (FIDO2/WebAuthn) | Highest | Moderate - requires physical key | Medium to High - requires key distribution & management | Moderate - cost of hardware tokens |
| Biometric Authentication (Fingerprint, Facial Recognition) | High | Very Good - convenient for users | High - integration with identity provider, privacy concerns | Moderate to Higher - depends on technology and integration |
| Push Notifications (via Authenticator App) | Better | High - user confirms on trusted device | Medium | Moderate - relies on app and network connectivity |
| Passwordless Authentication (FIDO2/WebAuthn) | Highest | Good - relies on device biometrics or PIN | High - requires platform support and user enrollment | Moderate - cost of compatible devices and integration |
Qualitative comparison based on the article research brief. Confirm current product details in the official docs before making implementation choices.
Microsegmentation: Containing the Blast Radius
Microsegmentation takes network segmentation to a much finer granularity. Traditional network segmentation typically divides the network into broad zones, such as a DMZ for public-facing servers and an internal network for critical systems. Microsegmentation, on the other hand, creates granular segments around individual workloads or applications.
The key difference is the level of isolation. Traditional segmentation relies on perimeter firewalls to control traffic between zones. Microsegmentation uses a combination of technologies, such as software-defined networking (SDN), host-based firewalls, and network virtualization, to isolate workloads at the application level. This significantly limits lateral movement, making it much harder for attackers to compromise multiple systems.
One approach to microsegmentation is to use software-defined networking (SDN) to create virtual network segments. SDN allows you to centrally manage and control network traffic, making it easier to create and enforce granular security policies. Another approach is to use host-based firewalls, which are installed on individual servers or endpoints to control network traffic in and out of those systems.
While microsegmentation can be complex to implement, the benefits are significant. By containing the blast radius of a potential breach, it can prevent attackers from gaining access to critical data and systems. This is particularly important in today’s threat landscape, where attackers are increasingly targeting sensitive data.
Data Security in a Zero Trust World
Zero Trust isn’t just about controlling access to networks and applications; it’s also about protecting data. Data-centric security is a critical component of a Zero Trust architecture. This means focusing on protecting the data itself, rather than just the infrastructure around it.
Data Loss Prevention (DLP) is a key technology for preventing sensitive data from leaving the organization. DLP systems can monitor network traffic, endpoint activity, and cloud storage to detect and block unauthorized data transfers. Encryption is also essential, both at rest and in transit. Encrypting data makes it unreadable to unauthorized users, even if they gain access to the storage media.
Data classification is another important practice. Categorizing data based on its sensitivity level allows you to apply appropriate security controls. For example, highly sensitive data might require stronger encryption and access controls than less sensitive data. Data governance plays a vital role here, establishing policies and procedures for managing and protecting data throughout its lifecycle.
I often see organizations overlook the importance of data security when implementing Zero Trust. They focus on controlling access to systems, but they don’t pay enough attention to protecting the data itself. But securing the data is ultimately the most important goal.
Featured Products

Comprehensive data loss prevention policies · Integration with Microsoft 365 ecosystem · Real-time monitoring and reporting
This guide provides essential insights into leveraging Microsoft Purview for robust data loss prevention within your Microsoft 365 environment, a critical component for Zero Trust.

Technical and organizational security measures · Protection against data loss and computer crime · Best practices for data security management
This book offers a foundational understanding of technical and organizational measures necessary to protect data from loss and cybercrime, aligning with Zero Trust principles.
Centralized data loss prevention · Automated data discovery and classification · Real-time monitoring and alerting
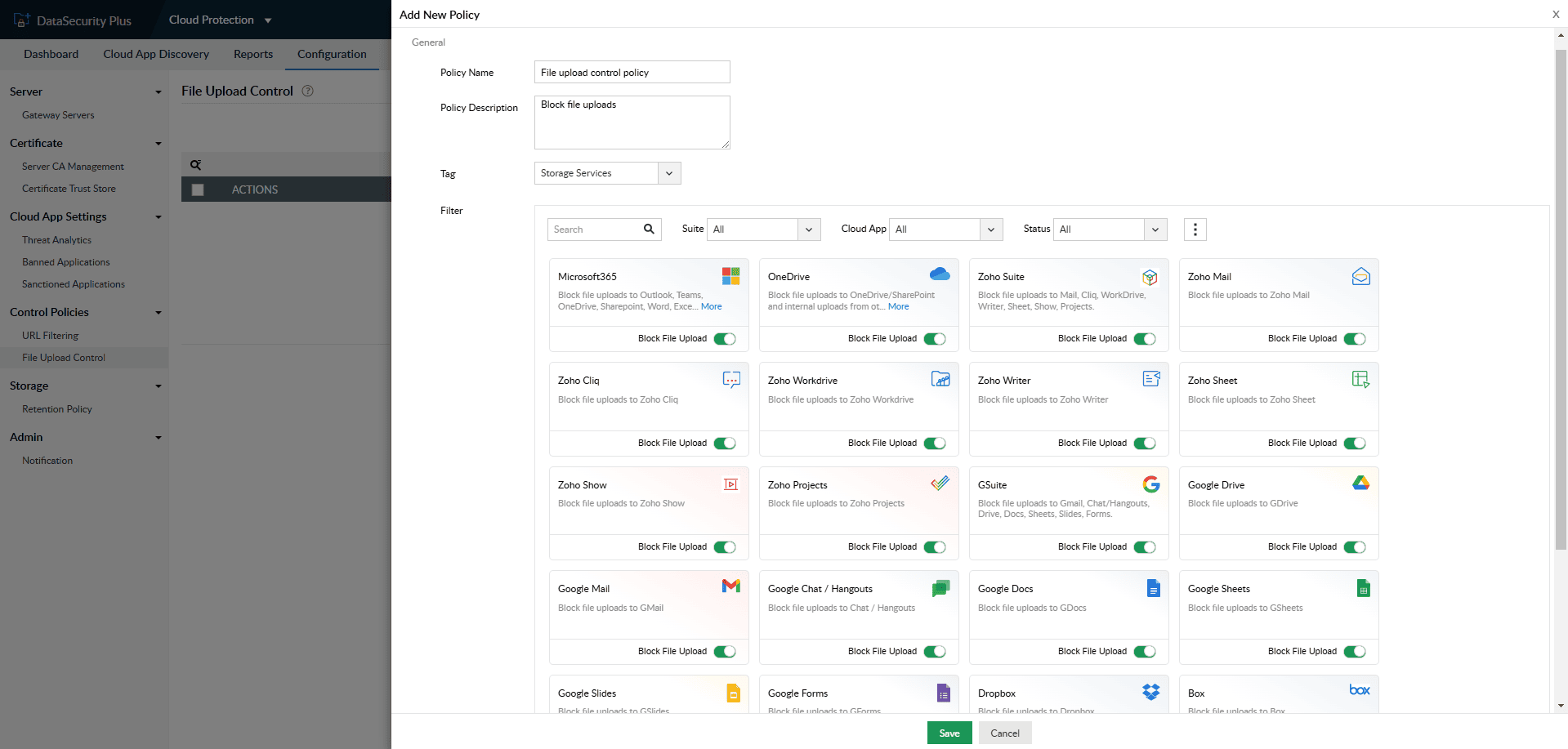
ManageEngine DataSecurity Plus provides a comprehensive solution for data loss prevention, offering automated discovery and classification to help secure sensitive information in line with Zero Trust.

High-performance 802.11ac Wave 2 wireless · Outdoor deployment capabilities · Internal antennas for broad coverage
This Cisco outdoor access point enhances network security by providing reliable and secure wireless connectivity, essential for extending Zero Trust principles to the network edge.
As an Amazon Associate I earn from qualifying purchases. Prices may vary.
Continuous Monitoring and Analytics
Zero Trust isn’t a 'set it and forget it' security model. It requires continuous monitoring and analysis to detect and respond to threats. This is where Security Information and Event Management (SIEM) systems come into play. SIEM systems collect and analyze security logs from various sources, providing a centralized view of security events.
User and Entity Behavior Analytics (UEBA) is another valuable tool. UEBA uses machine learning to identify anomalous behavior that might indicate a security threat. For example, it can detect a user logging in from an unusual location or accessing sensitive data they don’t normally access. Threat intelligence feeds provide information about known threats and vulnerabilities, allowing you to proactively identify and mitigate risks.
These tools aren’t just about detecting threats; they’re also about responding to them. Automated incident response capabilities can help you quickly contain and remediate security breaches. This might involve isolating compromised systems, blocking malicious traffic, or revoking user access.
The "trust but verify" aspect of Zero Trust truly comes to life through continuous monitoring and analytics. It allows you to constantly assess the security posture of your network and identify areas for improvement. It's about building a resilient security system that can adapt to evolving threats.
Zero Trust Implementation: A Phased Approach
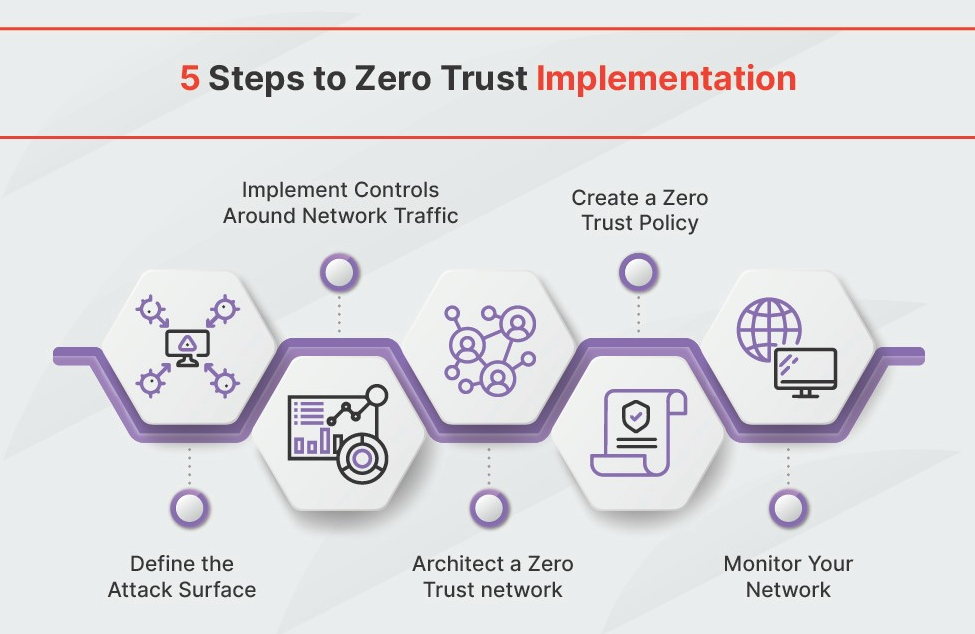
Implementing Zero Trust can seem daunting, but it doesn’t have to be an all-or-nothing proposition. A phased approach is the most practical way to get started. The Department of Defense (DoD) Zero Trust Implementation Guideline Phase One recommends a similar approach, starting with a pilot project to gain experience and demonstrate value.
Begin by identifying a critical asset or application that you want to protect. Then, implement Zero Trust controls around that asset, such as MFA, microsegmentation, and continuous monitoring. Monitor the results closely and make adjustments as needed. Once you’ve successfully implemented Zero Trust for that asset, you can gradually expand to other areas of the organization.
Common challenges include legacy systems that aren’t compatible with Zero Trust controls, lack of skilled personnel, and resistance to change. To overcome these challenges, prioritize incremental improvements, invest in training, and communicate the benefits of Zero Trust to stakeholders. It’s also important to choose the right tools and technologies.
Remember, Zero Trust is a journey, not a destination. It requires ongoing effort and commitment. But by taking a phased approach and focusing on continuous improvement, you can significantly enhance your organization’s security posture.
- Phase 1: Identify a critical asset and implement Zero Trust controls.
- Phase 2: Monitor results and make adjustments.
- Phase 3: Gradually expand Zero Trust to other areas.
Looking Ahead: Zero Trust in 2026 and Beyond
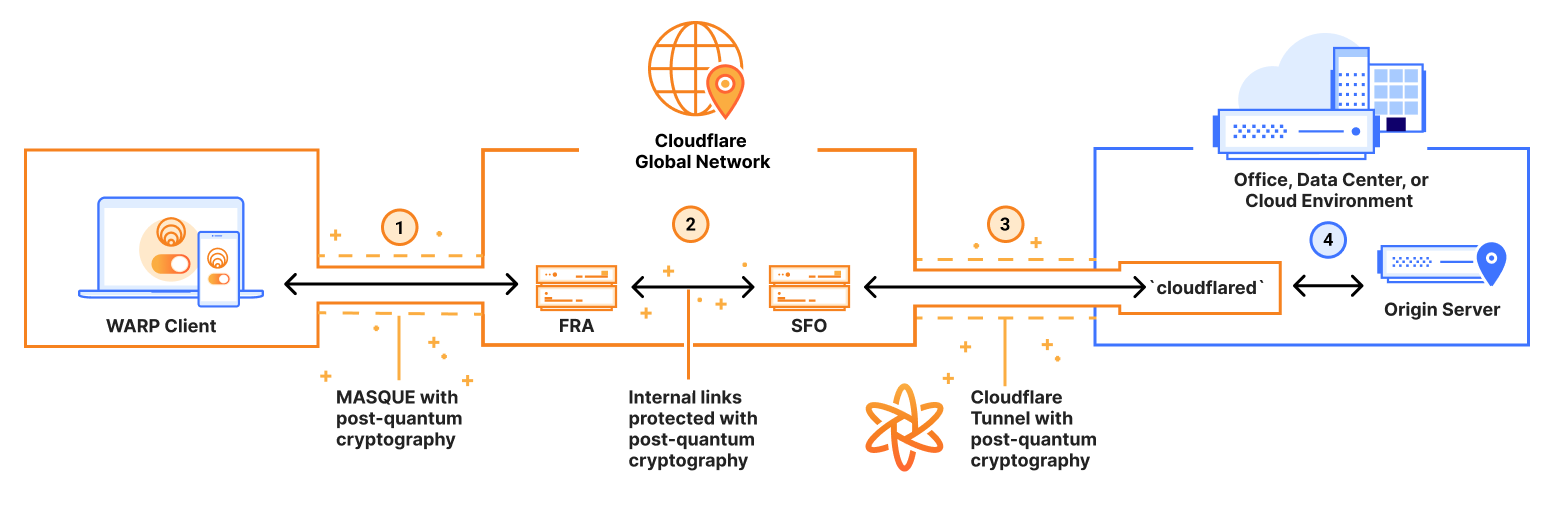
Looking ahead to 2026, I expect to see the convergence of Zero Trust with other security trends, such as Secure Access Service Edge (SASE). SASE combines network security functions, such as firewalls and intrusion detection systems, with wide area network (WAN) capabilities to provide secure access to applications and data from anywhere. Integrating Zero Trust with SASE can provide a more comprehensive and flexible security solution.
The increasing use of AI and machine learning will also play a significant role in Zero Trust. AI can be used to automate threat detection and response, improve IAM, and enhance data security. However, it’s important to remember that AI is not a silver bullet. It needs to be combined with human expertise to be truly effective.
One of the biggest challenges that still needs to be addressed is the complexity of implementing and managing Zero Trust. Many organizations lack the internal expertise and resources to do it effectively. This is where managed security service providers (MSSPs) can help. MSSPs can provide the expertise and tools needed to implement and manage Zero Trust.
Ultimately, Zero Trust is about adapting to the evolving threat landscape and building a more resilient security posture. It’s a continuous process of improvement and innovation, and I expect to see significant advancements in Zero Trust technologies and practices in the years to come.


No comments yet. Be the first to share your thoughts!